ISCC 2018线上赛 writeup
Posted
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了ISCC 2018线上赛 writeup相关的知识,希望对你有一定的参考价值。
今天有机会去ISCC2018参加了比赛,个人的感受是比赛题目整体难度不高,就是脑洞特别大,flag形式不明确,拿到flag后也要猜测flag格式,贼坑
废话不多说,以下是本人的解题思路
MISC
0x01 What is that?

下载附件得到图片

看图应该可以猜到flag在下面被截取了,所以我们去修改图片的高度
用十六进制打开图片

在图片的高度那里修改一下数值,我是把01 F4 改成 03 F4 ,高度该多少随意,能看到flag即可
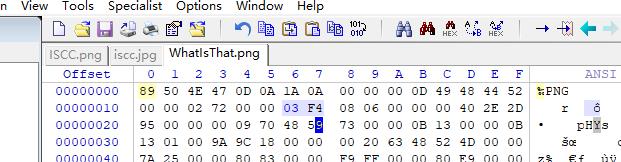
再打开图片,出现flag
然后格式贼坑,根据多种尝试,最后确认要去掉flag=和{}提交即可!
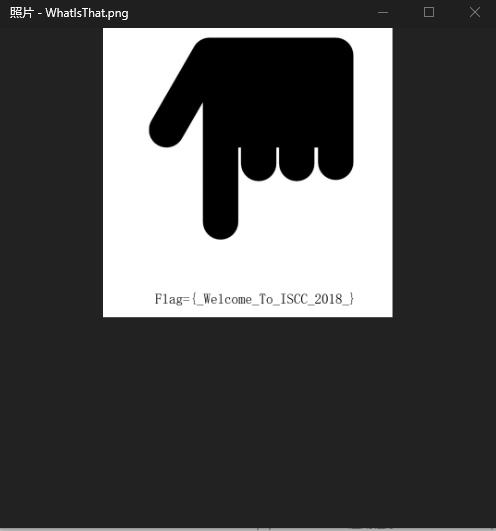
0x02 秘密电报

下载附件打开
非常明显是培根密码,解密得到
ilikeiscc和ILIKEISCC,输入即可
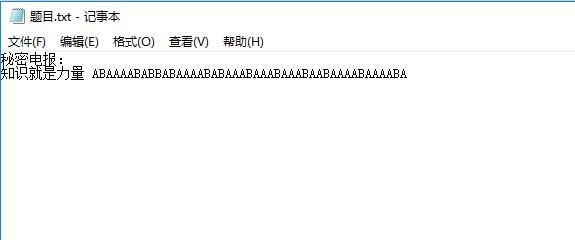
0x03 重重谍影

进入网页看到
先进行base64得到
Vm0wd2VFNUdWWGhVV0doVVYwZDRWbFl3WkRSV01XeFZVMjA1V0ZKdGVIcFpWVnBQVjBkS1IxTnNhRmRXZWtGNFdXdGtTMUpzWkhWalJscFhaV3hhV1Zac1kzaFRNVmw0VTJ4c2FGSnNXbGhXYWtwdlRteGtjbGR0UmxWTlZtdzBWa2MxUzFReFdsVldhemxhVm5wR2NWcEVSbUZqVmtweldrVTVVMDFWY0VwV2JGcHZZVEpHUjFOWWJHaFRSVXBXVm01d1IwNXNVbFpYYlhSWVVqQTFTVlF4V21GaFZscHlZak5rVjJGcmJ6QlpWRVp6VmpGT2MxcEhjRk5YUlVwWVZtMTBWMU14WkVkVmJGWlRZVE5TVUZsc1ZuZFRiRlpZVFZSQ1ZXRjZSa2RXYlhCUFYwWmFjMWRzYUdGU1JWcFFWakJhWVdSV1ZuSlBWbWhUVFRKb00xWnNaREJoTVZWNVZHNU9WbUpyY0ZaWmExcDNZMnhTVjFadFJsZE5WbFkwVmxkMGEyRkhTbFpXYWxwWFZqTlNXRll5TVVabFJtUnpZVVpXYVZKdVFubFdiWEJIWVRKT1YxSnVVbXhTYXpWVVdXeFNjazFHV25SalJYUk9VbTE0V0ZaSE5VOVdWbVJKVVd4a1dsWkZXa3hXTVZwWFpGZE9TRTVYZUdsU2EzQlpWakowYTFJeFduSk5WVlpwVW0xU1ZsWnRNVk5OTVdSWFdrVmthazFyTlVwVlYzaFhWakZhYzJOR2JGZFNla1V3V2tSR2ExTkdVbkpoUmtKWFlsZG9kbGRYZEZka2JWWnpXa1pvVGxOSGFIQlVWM2hMVjBaYVNFNVZkRlpTYlZKSFZHeFZlRlpXV2taT1ZWSlZZa1p3WVZwV1pGZFRSa3AwWTBVMVYySnJTVEJXYkZwclRrWlplRlpyWkZoaVJscFlXV3RrVTFZeFduUmpla0pyVFZaS1dGWnNhRzlYUmxsM1lrUldZVlpXVlhoV1ZFWmhWakpPUlZSc1pHaE5iRW8yVmtaV2ExUXhaRWRUYkd4cVVtdHdjRlpxVG05VlZtUlhWV3RrV2xac2NFaFdiR2hyVm0xS1ZWWnJPVnBpUmxwb1dsVmFhMk5zVm5KVWJGWk9WbGhDU1ZacVJtOWpNVnBZVWxob1YyRnNTbWhWYTFaaFRURmFjbHBHVGxSV2EzQjVWR3hhYTFSdFNrWmpSV1JYVFZaS1JGbHFSbk5YUmtweVdrWmthVkl5YUc5V1ZFSmhaREZhVjFWc1dsZFhSMmhQVkZaYWQxSnNWWGxrUjNSb1VtdHdWbFp0ZUhOWlZrcFlWV3BPVm1WcldtaFZiWE14Vm14a1ZGWlljRk5SVTFWNlVrTlZlbEpCSlRORUpUTkU%3D
看不出来什么,看题目,层层迷雾,那就base64到底好了,最后在Salted__前打住

Salted__了解一下,这个是通过openssl加密如果不带base64就会出现Salted字段打头。再看base64的前几个字段U2Fsd确定是AES加密无误
这里有点坑,弄了很久才发现原base64密文中有url编码,所以先url解码得到
U2FsdGVkX183BPnBd50ynIRM3o8YLmwHaoi8b8QvfVdFHCEwG9iwp4hJHznrl7d4
B5rKClEyYVtx6uZFIKtCXo71fR9Mcf6b0EzejhZ4pnhnJOl+zrZVlV0T9NUA+u1z
iN+jkpb6ERH86j7t45v4Mpe+j1gCpvaQgoKC0Oaa5kc=
然后AES解密得到
答案就是后面这句但已加密
缽娑遠呐者若奢顛悉呐集梵提梵蒙夢怯倒耶哆般究有栗
佛系加密。。。。把乱码拿去百度,可以收到与佛论禅,解密得flag
0x04 有趣的ISCC

下载图片,打开是ISCC的icon,用binwalk看一下有没有隐写,没啥东西,进行十六进制分析,在最后看到一串unicode编码

先复制出来解码一下好了,然后又得到unicode编码,解码,得到flag
0x05 Where is FLAG?

下载图片,binwalk查看有没有隐写,群里大佬给了提示,查看齐二进制发现是用adobe fireworks cs5做的

尝试丢进adobe fireworks cs5,发现是一张二维码,扫描即可
0x06 凯撒十三世

拿到密文ebdgc697g95w3,凯撒跑起来,go
ebdgc697g95w3
fcehd697h95x3
gdfie697i95y3
hegjf697j95z3
ifhkg697k95a3
jgilh697l95b3
khjmi697m95c3
liknj697n95d3
mjlok697o95e3
nkmpl697p95f3
olnqm697q95g3
pmorn697r95h3
qnpso697s95i3
roqtp697t95j3
spruq697u95k3
tqsvr697v95l3
urtws697w95m3
vsuxt697x95n3
wtvyu697y95o3
xuwzv697z95p3
yvxaw697a95q3
zwybx697b95r3
axzcy697c95s3
byadz697d95t3
czbea697e95u3
dacfb697f95v3
一眼望去,没有flag、ctf、iscc等关键词
想到可能是哪里错了特殊的移位
看题目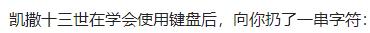
这里可以猜测也许是做了键盘移位,先以flag来猜
flag根据键盘键位移位后可能是roqt或者v.zb或者v>zb,在上面的凯撒移位中尝试查找这三个关键字,刚好找到有一个roqtp697t95j3
把roqtp697t95j3还原得到flag;yougotme或者flag:yougotme输入即可
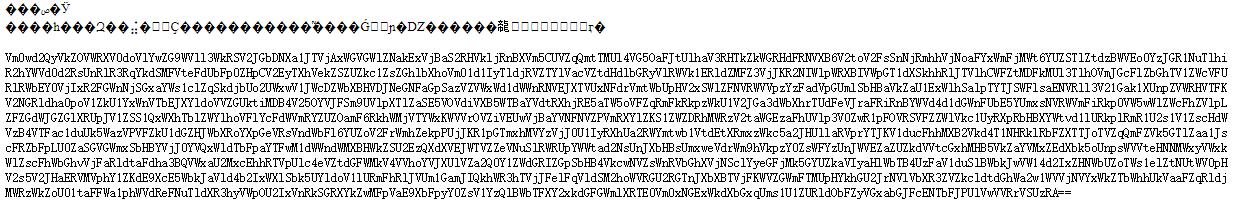
0x07 一只猫的心思

下载得到图片,用binwalk查看没有隐写,变色也没东西,后来得到hint是说图片里面藏了doc,所以查看其十六进制
百度得到doc的文件头是D0 CF 11 E0,搜索找到了位置

用winhex或者format分离出doc打开得到
如此佛系,拿去与佛论禅再看看,解密得到
523156615245644E536C564856544E565130354B553064524D6C524E546B4A56535655795645644F5530524857544A4553553943566B644A4D6C524E546C7052523155795645744F536C5248515670555330354452456456576B524854554A585231457956554E4F51305A4855544E4553303153566B64424D6C524A546B7058527A525A5245744F576C5A4854544A5554553554513063304E46524C54564A5652316B795255744F51305A4856544E5554564661566B6C464D6B5252546B70595231557A5245394E516C5A4856544A555355354B566B644E5756524E5455705752316B7A5255564F55305248566B465553564A4356306C4E4D6C524E546B4A565231557952453152556C564A56544A455555354B5530644E5756525054554A56523030795645314F516C5A4857544A4553303143566B64464D305648546B744352314A425645744F576C5A4855544A4651303543566B64564D6B524854554A555230557A52454E4F536C644855544A5554553543566B645A4D6B564A546C4E445231566152456C52576C5A4855544A5553303544516B64564D6C524C54564A55523045795245314F556C4A4856544E455355354B56556C564D6B564E546B70535230315A52457452536C564951544A555455354B565564535156524A54564A575230457956456C4E576C46485454525553303143566B6446576C564A54544A46
发现是字母是由0-9 a-f组成,于是进行十六进制分析
R1VaREdNSlVHVTNVQ05KU0dRMlRNTkJVSVUyVEdOU0RHWTJESU9CVkdJMlRNTlpRR1UyVEtOSlRHQVpUS05DREdVWkRHTUJXR1EyVUNOQ0ZHUTNES01SVkdBMlRJTkpXRzRZREtOWlZHTTJUTU5TQ0c0NFRLTVJVR1kyRUtOQ0ZHVTNUTVFaVklFMkRRTkpYR1UzRE9NQlZHVTJUSU5KVkdNWVRNTUpWR1kzRUVOU0RHVkFUSVJCV0lNMlRNTkJVR1UyRE1RUlVJVTJEUU5KU0dNWVRPTUJVR00yVE1OQlZHWTJES01CVkdFM0VHTktCR1JBVEtOWlZHUTJFQ05CVkdVMkRHTUJUR0UzRENOSldHUTJUTU5CVkdZMkVJTlNDR1VaRElRWlZHUTJUS05DQkdVMlRLTVJUR0EyRE1OUlJHVTNESU5KVUlVMkVNTkpSR01ZREtRSlVIQTJUTU5KVUdSQVRJTVJWR0EyVElNWlFHTTRUS01CVkdFWlVJTTJF
base64解密得到
GUZDGMJUGU3UCNJSGQ2TMNBUIU2TGNSDGY2DIOBVGI2TMNZQGU2TKNJTGAZTKNCDGUZDGMBWGQ2UCNCFGQ3DKMRVGA2TINJWG4YDKNZVGM2TMNSCG44TKMRUGY2EKNCFGU3TMQZVIE2DQNJXGU3DOMBVGU2TINJVGMYTMMJVGY3EENSDGVATIRBWIM2TMNBUGU2DMQRUIU2DQNJSGMYTOMBUGM2TMNBVGY2DKMBVGE3EGNKBGRATKNZVGQ2ECNBVGU2DGMBTGE3DCNJWGQ2TMNBVGY2EINSCGUZDIQZVGQ2TKNCBGU2TKMRTGA2DMNRRGU3DINJUIU2EMNJRGMYDKQJUHA2TMNJUGRATIMRVGA2TIMZQGM4TKMBVGEZUIM2E
以下就很无聊了,脑洞不大就想不到,最后得到hint是16进制>base64>base32>16进制>base64>base32>16进制循环解下去就可以了,写了一个脚本得到flag
# coding=utf-8 import base64 def hexToStr(message): cipertext = message i = 0 plaintext = "" while i < len(cipertext) - 1: plaintext += chr(int(cipertext[i:i + 2], 16)) i += 2 return plaintext data = "523156615245644E536C564856544E565130354B553064524D6C524E546B4A56535655795645644F5530524857544A4553553943566B644A4D6C524E546C7052523155795645744F536C5248515670555330354452456456576B524854554A585231457956554E4F51305A4855544E4553303153566B64424D6C524A546B7058527A525A5245744F576C5A4854544A5554553554513063304E46524C54564A5652316B795255744F51305A4856544E5554564661566B6C464D6B5252546B70595231557A5245394E516C5A4856544A555355354B566B644E5756524E5455705752316B7A5255564F55305248566B465553564A4356306C4E4D6C524E546B4A565231557952453152556C564A56544A455555354B5530644E5756525054554A56523030795645314F516C5A4857544A4553303143566B64464D305648546B744352314A425645744F576C5A4855544A4651303543566B64564D6B524854554A555230557A52454E4F536C644855544A5554553543566B645A4D6B564A546C4E445231566152456C52576C5A4855544A5553303544516B64564D6C524C54564A55523045795245314F556C4A4856544E455355354B56556C564D6B564E546B70535230315A52457452536C564951544A555455354B565564535156524A54564A575230457956456C4E576C46485454525553303143566B6446576C564A54544A46" a = hexToStr(data) b = base64.b64decode(a) c = base64.b32decode(b) d = hexToStr(c) e = base64.b64decode(d) f = base64.b32decode(e) g = hexToStr(f) print g
0x08 暴力XX不可取

下载附件,得到压缩文件,需要密码才能打开。题目说暴力XX不可取,那就先不进行爆破。
观察其二进制

发现是伪加密(伪加密了解一下),把后面的07 08改成00 08,保存
正常打开里面的file

先凯撒跑起来
vfppjrnerpbzvat
wgqqksofsqcawbu
xhrrltpgtrdbxcv
yissmuqhusecydw
zjttnvrivtfdzex
akuuowsjwugeafy
blvvpxtkxvhfbgz
cmwwqyulywigcha
dnxxrzvmzxjhdib
eoyysawnaykiejc
fpzztbxobzljfkd
gqaaucypcamkgle
hrbbvdzqdbnlhmf
isccwearecoming
jtddxfbsfdpnjoh
kueeygctgeqokpi
lvffzhduhfrplqj
mwggaievigsqmrk
nxhhbjfwjhtrnsl
oyiickgxkiusotm
pzjjdlhyljvtpun
qakkemizmkwuqvo
rbllfnjanlxvrwp
scmmgokbomywsxq
tdnnhplcpnzxtyr
ueooiqmdqoayuzs
和上面一样查找关键字flag、ctf、iscc,找到isccwearecoming,输入即可
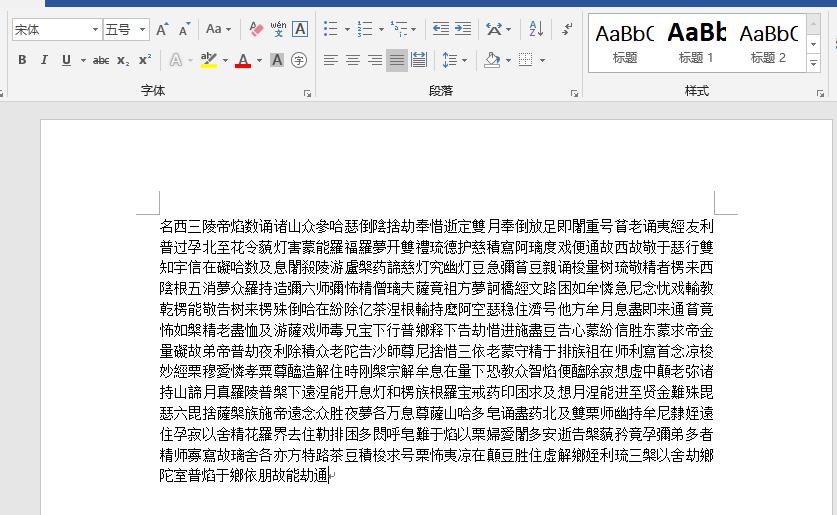
0x09 数字密文
十六进制转字符串即可
# coding=utf-8
import binascii
print binascii.unhexlify("69742773206561737921")
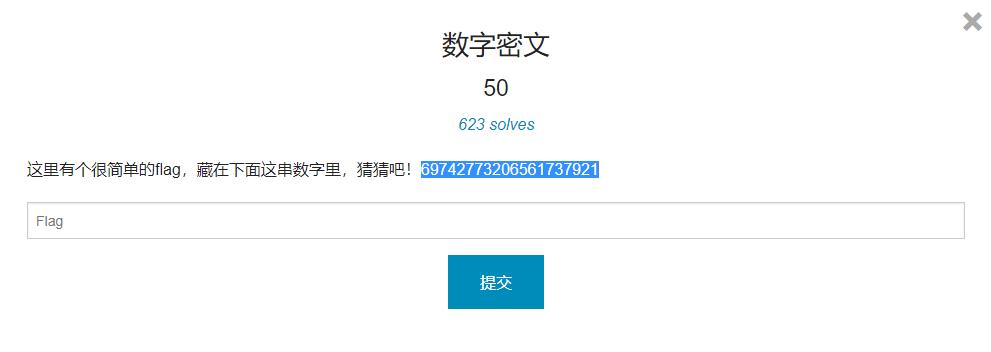
0x0A 嵌套ZIPs
下载附件得

需要解密,丢进winhex发现不是伪加密,无解
在大佬的帮助下,得知是手机号码(该题是实验吧的一道原题,原题有hint,这题没有,所以很坑),于是进行掩码攻击得到

来到第二层,打开得到

发现里面有个tips.txt,刚才在3.zip里面已经解tips.txt了可是在2.zip里面还有这个文件,观察其CRC发现是一样的,于是明文攻击走一波
做好心理准备。。。花了2h解出

来到第三层,
第三层是没有提示的。丢进winhex查看一下。发现是伪加密

05改00即可,解压出flag.txt
web
0x01 比数字大小

进入网页显示
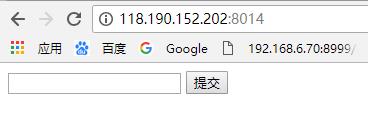
题目说要比服务器的数字大,通过尝试发现输入框只能输入三位数,尝试输入999后仍然提示“数字太小了”
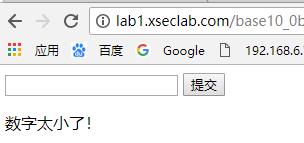
尝试抛弃网页,直接发送请求,F12先查看传参,字段是v
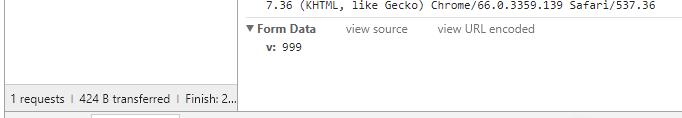
尝试写一个http请求
# coding=utf-8
import requests
url = "http://lab1.xseclab.com/base10_0b4e4866096913ac9c3a2272dde27215/index.php"
payload = {
"v": "9999"
}
r = requests.post(url, data=payload)
print r.content
把9999传过去了,就得到了key
0x02 web1
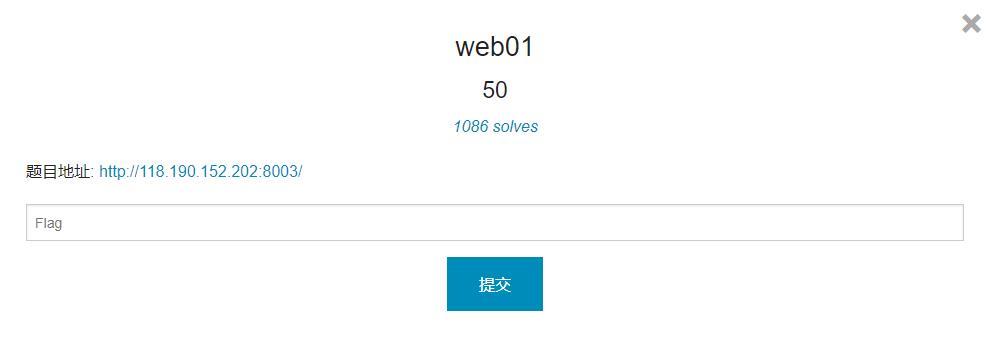
打开地址看到php语言

get一个password的参数,如果这个值和flag一样,就返回flag
这里是典型的php弱类型题目,直接传password[]即可
# coding=utf-8
import requests
url = "http://118.190.152.202:8003/"
payload = {
"password[]": "1"
}
r = requests.get(url, params=payload)
print r.content
0x03 本地的诱惑

打开网页查看源代码即可
0x05 一切都是套路

打开网页

检查源代码以及结构,没特殊发现,观察题目,有个文件忘记删了,那一般是index.php.txt,尝试访问118.190.152.203:8009/index.php.txt

经过分析,这里得用get,post混合请求的方式(post主请求,get带参数),用flag来覆盖_200,最后返回的$_200就变成了$flag,具体原理我也不太懂,提示是群里某大佬说的
# coding=utf-8
import requests
url = "http://118.190.152.202:8009?_200=flag"
payload = {
"flag": "1"
}
r = requests.post(url, data=payload)
print r.content
0x07 web2

打开题目地址提示
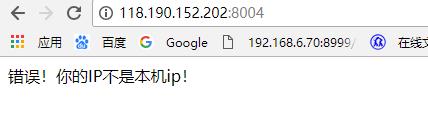
先伪装ip,尝试修改header头,经过多次尝试,header为CLIENT-IP
Reverse
0x01 RSA256

这道题不用IDA,所以本小白也能做-0-
本题是最基本的RSA逆向,下载解压后得

观察了一下,是一个公钥,然后三个密文,只要我们算出秘钥就可以了
先读取公钥
e = 65537
n = 98432079271513130981267919056149161631892822707167177858831841699521774310891
通过msieve算出p,q,然后生成秘钥,用秘钥解密文即可得到明文flag
# -*- coding: utf-8 -*- import rsa from Crypto.PublicKey import RSA def creatprivatekey(p, q, e): """ 根据p,q,e生成d,然后再填充生成最终的秘钥 :param p: :param q: :param e: :return: """ keypair = RSA.generate(1024) keypair.p = p keypair.q = q keypair.e = e keypair.n = keypair.p * keypair.q Qn = long((keypair.p - 1) * (keypair.q - 1)) i = 1 while True: x = (Qn * i) + 1 if x % keypair.e == 0: keypair.d = x / keypair.e break i += 1 private = open(\'D:\\\\YQworckspace\\\\CTF\\\\RSA\\\\private.pem\', \'w\') private.write(keypair.exportKey()) private.close() p = 302825536744096741518546212761194311477 q = 325045504186436346209877301320131277983 e = 65537 creatprivatekey(p, q, e) with open(\'private.pem\', \'r\') as privatefile: p = privatefile.read() privkey = rsa.PrivateKey.load_pkcs1(p) file1 = open("C:\\\\Users\\\\fuzhi\\\\Desktop\\\\fujian\\\\encrypted.message3", "r") message = file1.read() plaintext= rsa.decrypt(message, privkey) print plaintex
以上是关于ISCC 2018线上赛 writeup的主要内容,如果未能解决你的问题,请参考以下文章
2021年“绿盟杯”重庆市大学生信息安全竞赛线上赛-Writeup