Puppet安装部署篇
Posted
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Puppet安装部署篇相关的知识,希望对你有一定的参考价值。
前言:上篇写了结合svn钩子做版本控制puppet master代码,后续的操作都要在windows客户端使用svn完成操作,如果直接在服务器端操作,svn的钩子就会出现同步失败和不同步的问题.
解决:pkill svn && svnserve -d -r /data/puppet_co/ #重启操作
1、安装完puppet查看puppet的主配置文件目录:
#puppet agent --configprint confdir /etc/puppet
2、设置puppet/puppet server 服务开机自启动:
# chkconfig puppetmaster on # chkconfig puppet on
3、puppet master 的启动:
/etc/init.d/puppetmaster start
4、查看puppet master是否启动成功.
/etc/init.d/puppetmaster status
5、puppet.conf的原先配置文件做备份,使用下面的命令生成Master资源追加到puppet.conf文件(各agent端就不需要了).
#puppet master --genconfig >> /etc/puppet/puppet.conf
注意:下面这块我使用命令将注释行去掉了,并不是生成的就没有注释,下面有些参数注释掉,是因为下面报警告,我做了优化贴出来的最新的.
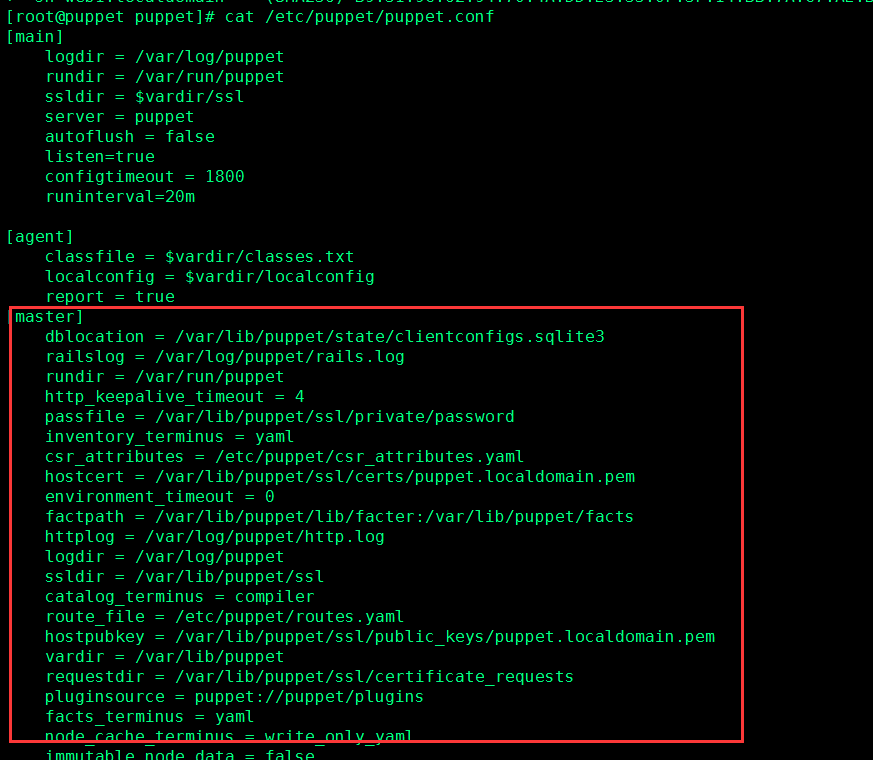
[[email protected] puppet]# cat /etc/puppet/puppet.conf
[main] logdir = /var/log/puppet rundir = /var/run/puppet ssldir = $vardir/ssl server = puppet autoflush = false listen=true configtimeout = 1800 runinterval=20m
[agent] classfile = $vardir/classes.txt localconfig = $vardir/localconfig report = true
[master] dblocation = /var/lib/puppet/state/clientconfigs.sqlite3 railslog = /var/log/puppet/rails.log rundir = /var/run/puppet http_keepalive_timeout = 4 passfile = /var/lib/puppet/ssl/private/password inventory_terminus = yaml csr_attributes = /etc/puppet/csr_attributes.yaml hostcert = /var/lib/puppet/ssl/certs/puppet.localdomain.pem environment_timeout = 0 factpath = /var/lib/puppet/lib/facter:/var/lib/puppet/facts httplog = /var/log/puppet/http.log logdir = /var/log/puppet ssldir = /var/lib/puppet/ssl catalog_terminus = compiler route_file = /etc/puppet/routes.yaml hostpubkey = /var/lib/puppet/ssl/public_keys/puppet.localdomain.pem vardir = /var/lib/puppet requestdir = /var/lib/puppet/ssl/certificate_requests pluginsource = puppet://puppet/plugins facts_terminus = yaml node_cache_terminus = write_only_yaml immutable_node_data = false privatedir = /var/lib/puppet/ssl/private pluginfactsource = puppet://puppet/pluginfacts libdir = /var/lib/puppet/lib hiera_config = /etc/puppet/hiera.yaml hostcrl = /var/lib/puppet/ssl/crl.pem hostcsr = /var/lib/puppet/ssl/csr_puppet.localdomain.pem default_file_terminus = rest certdir = /var/lib/puppet/ssl/certs certname = puppet certificate_expire_warning = 5184000 hostprivkey = /var/lib/puppet/ssl/private_keys/puppet.localdomain.pem confdir = /etc/puppet publickeydir = /var/lib/puppet/ssl/public_keys plugindest = /var/lib/puppet/lib node_terminus = plain statedir = /var/lib/puppet/state filetimeout = 15 localcacert = /var/lib/puppet/ssl/certs/ca.pem name = master privatekeydir = /var/lib/puppet/ssl/private_keys pluginfactdest = /var/lib/puppet/facts.d data_binding_terminus = hiera preview_outputdir = /var/lib/puppet/preview yamldir = /var/lib/puppet/yaml #masterlog = /var/log/puppet/puppetmaster.log masterport = 8140 rest_authconfig = /etc/puppet/auth.conf #manifestdir = /etc/puppet/manifests server_datadir = /var/lib/puppet/server_data masterhttplog = /var/log/puppet/masterhttp.log #modulepath = /etc/puppet/modules:/usr/share/puppet/modules reportdir = /var/lib/puppet/reports storeconfigs_backend = active_record bucketdir = /var/lib/puppet/bucket fileserverconfig = /etc/puppet/fileserver.conf #manifest = /etc/puppet/manifests/site.pp basemodulepath = /etc/puppet/modules:/usr/share/puppet/modules #templatedir = /var/lib/puppet/templates waitforcert = 120 statefile = /var/lib/puppet/state/state.yaml inventory_server = puppet puppetdlog = /var/log/puppet/puppetd.log client_datadir = /var/lib/puppet/client_data lastrunfile = /var/lib/puppet/state/last_run_summary.yaml agent_disabled_lockfile = /var/lib/puppet/state/agent_disabled.lock runinterval = 1800 resourcefile = /var/lib/puppet/state/resources.txt node_name_value = puppet.localdomain configtimeout = 120 ca_port = 8140 localconfig = /var/lib/puppet/state/localconfig report_port = 8140 clientyamldir = /var/lib/puppet/client_yaml inventory_port = 8140 splaylimit = 1800 agent_catalog_run_lockfile = /var/lib/puppet/state/agent_catalog_run.lock classfile = /var/lib/puppet/state/classes.txt lastrunreport = /var/lib/puppet/state/last_run_report.yaml clientbucketdir = /var/lib/puppet/clientbucket ca_server = puppet graphdir = /var/lib/puppet/state/graphs report_server = puppet tagmap = /etc/puppet/tagmail.conf config = /etc/puppet/puppet.conf bindaddress = 0.0.0.0 pidfile = /var/run/puppet/master.pid ca_ttl = 157680000 capub = /var/lib/puppet/ssl/ca/ca_pub.pem serial = /var/lib/puppet/ssl/ca/serial caprivatedir = /var/lib/puppet/ssl/ca/private signeddir = /var/lib/puppet/ssl/ca/signed cadir = /var/lib/puppet/ssl/ca autosign = /etc/puppet/autosign.conf cakey = /var/lib/puppet/ssl/ca/ca_key.pem cacrl = /var/lib/puppet/ssl/ca/ca_crl.pem cert_inventory = /var/lib/puppet/ssl/ca/inventory.txt csrdir = /var/lib/puppet/ssl/ca/requests ca_name = Puppet CA: puppet.localdomain capass = /var/lib/puppet/ssl/ca/private/ca.pass cacert = /var/lib/puppet/ssl/ca/ca_crt.pem module_skeleton_dir = /var/lib/puppet/puppet-module/skeleton module_working_dir = /var/lib/puppet/puppet-module rrdinterval = 1800 rrddir = /var/lib/puppet/rrd archive_file_server = puppet devicedir = /var/lib/puppet/devices deviceconfig = /etc/puppet/device.conf reports = store, http reporturl = http://192.168.30.134:3000/reports/upload
注意:并不是生成的所有参数都会用到,只保留启动Master守护进程的基本参数也是可以的,这块偷个懒直接用生成的.
6、Master配置puppet.conf文件.(下面的参数有则修改,无则增加)
vim /etc/puppet/puppet.conf
[main] #指定了puppet端的服务地址. server = puppet #客户端获取配置超时时间. configtimeout = 1800 #客户端执行时间间隔,如果不设置默认为30分钟. runinterval=20m #是否实时刷新日志到磁盘. autoflush = false listen=true
[agent] #生成报告 report = true
[master] 修改项: certname = puppet #报告存放的目录,客户端每次执行会生成一份以日期+时间命名的yaml文件报告. reportdir = /var/lib/puppet/reports #自动授权签名配置文件. autosign = /etc/puppet/autosign.conf #puppet master服务端监听的地址. bindaddress = 0.0.0.0 #puppetmaster服务端监听端口. masterport = 8140 #通过此参数看到执行中的过程与变化 evaltrace = false #上传方式 reports = store, http #http上传时的地址 reporturl = http://192.168.30.134:3000/reports/upload
配置完成后重启puppet 服务.
/etc/init.d/puppetmaster restart
7、puppet auth.conf配置文件:
旧版本中文件为authconfig文件,使用XMLRPC协议,XMLRPC是使用http协议作为传输协议的RPC机制,使用XML文本的方式,效率底下.
Master本身是由Web Server提供Agent访问,如果没有权限控制,Agent就可以遍历Master上的资源.
auth.conf文件主要负责Agent访问Master服务器上一些目录和配置文件的权限和认证,它的官方名称时http network api,为了使用安全,Agent访问master过程中,使用https协议进行通讯交互.
https://{server}:{port}/{environment}/{resource}/{key}
auth.conf配置文件共7个参数:
参数:path、environment、method、auth、allow、allow_ip、deny的组合形成了Agent访问Master目录权限控制的ACL(权限控制列表).
path参数:指定acl的路径,path后接系统路径、正则表达式、路径前缀和资源等信息.
environment参数:可以包含一个环境或者多个环境列表,不设置默认为所有环境.puppet环境主要用于灰度.
method参数:包含find(查找)、search(搜索)、save(保存)和destroy(销毁),可以在method后设置任意一个参数或用逗号做分割设置多个参数,默认为所有参数.
auth参数:auth参数包含yes和on、any和no或off,不同的参数可以匹配不同的请求,默认值为yes或on.
auth设置为yes或on均表示匹配那些已经通过认证的agent请求.
auth设置为any意味着只匹配认证进行中和没有被认证的请求.
auth设置on或off,均表示匹配未认证过的agrnt请求,认证过的请求将会跳过此ACL。
allow参数:值为hostname和certname,puppet2.7.1以后支持perl或ruby正则表达式.
allow_ip参数:后接一个ip或ip的网段,表示允许指定ip范围通过.
deny参数:后接一个ip、多个ip、网段或域名等,表示禁止这些范围访问master的目录权限.
举例一:
允许lisi.example.com域访问/facts
path /facts
method find,search
auth yes
allow lisi.example.com
举例二:
匹配192.168.30.0/24段ip地址认证中或没有被认证的情况下访问catalog。
path ~ ^/catalog
auth any
allow_ip 192.168.30.0/24
举例三:
进制guest.puppet.com访问/
path /
deny guest.puppet.com
提示:puppet源码安装auth.conf文件放在源码安装目录里,RPM方式安装auth.conf文件安装到/etc/puppet目录里.
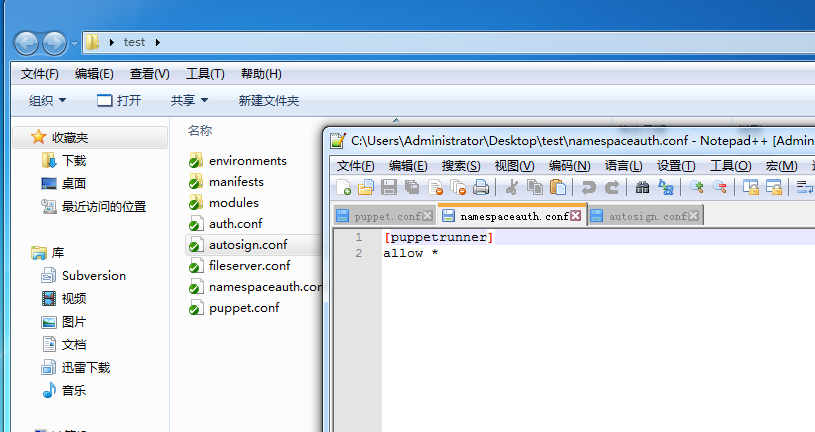
8、namespaceauth.conf文件:
/etc/puppet/namespaceauth.conf配置文件,RPM安装默认/etc/puppet是没有这个文件的,这个文件用于指定访问puppet的名称空间.namespaceauth.conf文件并不是puppet配置中必要的文件,只有当/etc/puppet.conf文件中listen=true时才会配置此文件,否则会报will not start without authorization file namespaceauth.conf 这样的错误,文件配置参考如下:
大概就下面这几项,但是不会全用到,/etc/puppet.conf文件不设置listen=true,这个文件根本不需要,设置了listen=true下面常用puppetrunner这项.
[fileserver] allow *.example.com [puppetmaster] allow *.example.com [puppetrunner] allow * [puppetbucket] allow *.example.com [puppetreports] allow * [resource] allow server.examplc.om
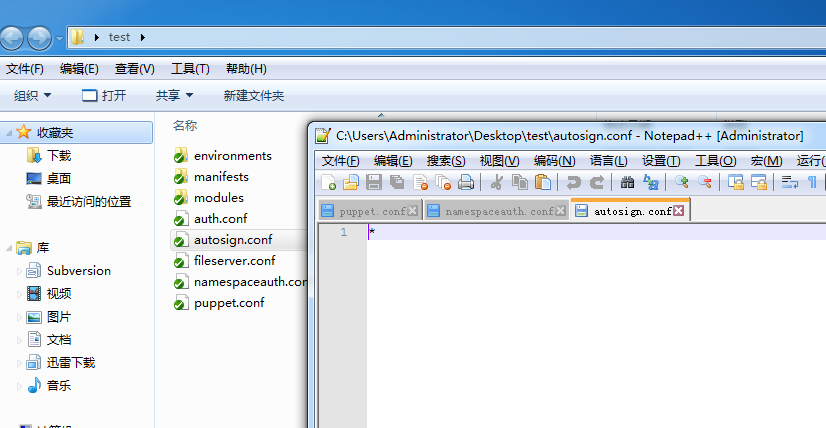
9、autosign.conf文件参数:
/etc/puppet/aotusign.conf配置文件主要用于自动签名证书功能,默认没有需要手动创建添加.通常Agent访问Master需要手动授权认证,通过在master上增加autosign.conf文件,实现对某一来源或所有来源的Agent做自动授权证书签名.
大概有两种方式的授权:
第一种:
cat /etc/puppet/autosign.conf *
第二种:
cat /etc/puppet/autosign.conf *.example.com
10、fileserver.conf文件参数:
/etc/puppet/fileserver.conf文件master目录的挂载配置文件,它包含了Master的挂载目录位置和挂载目录授权信息等.fileserver.conf并非puppet必要文件,默认安装完puppet软件包含此文件,只有agent从master获取一个文件或文件列表时才会用到它 .
fileserver.conf文件里面注释写的很详细,怎么使用挂载也有官网默认的例子:
如果你需要服务器文件来自一个目录而不是从模块中获取,你必须为这个文件创建一个挂载点.
# If you need to serve files from a directory that is NOT in a module,
# you must create a static mount point in this file:
#
# [extra_files]
# path /etc/puppet/files
# allow *
# In the example above, anything in /etc/puppet/files/<file name> would be
# available to authenticated nodes at puppet:///extra_files/<file name>.
在上面例子中,任何在/etc/puppet/files/<file name> 都可以有效的被认证的节点puppet:///extra_files/<file name>.引用.
下面是说结合挂载点auth.conf文件怎么写.
# Every static mount point should have an `allow *` line; setting more
# granular permissions in this file is deprecated. Instead, you can
# control file access in auth.conf by controlling the
# /file_metadata/<mount point> and /file_content/<mount point> paths:
#
# path ~ ^/file_(metadata|content)/extra_files/
# auth yes
# allow /^(.+)\.example\.com$/
# allow_ip 192.168.100.0/24
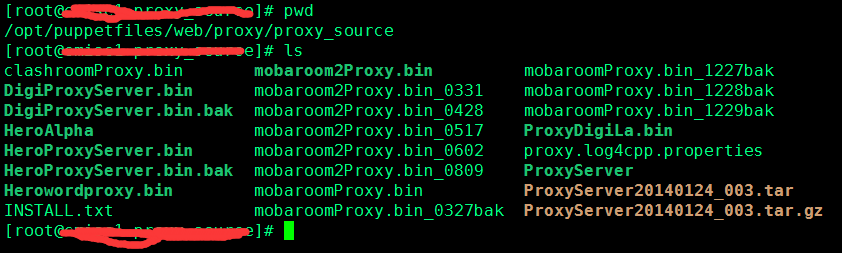
举例实例参考:(fileserver.conf结合auth.conf文件)
cat fileserver.conf
[bin] #挂载点叫bin
path /opt/puppetfiles #挂载根路径为系统上/opt/puppetfiles
allow *#允许所有主机访问
结合auth.conf文件做ACL权限认证,
cat auth.conf
path ~ ^/file_(metadata|content)/bin/
auth yes
allow_ip 192.168.30.0/24
随便一个modules模块引用:
file { "/usr/local/${folder_name}/${bin_name}":
owner => "root",
group => "root",
mode => "755",
ensure => "file",
source => "puppet:///bin/web/proxy/proxy_source/clashroomProxy.bin" #同步挂载点下的文件到Agent客户端.
}
服务器上的路径如下:
注意:目前同步文件puppet只支持puppet文件服务协议,并不支持rsync和http等专业的文件同步工具,如果server上的文件过大,多个agent一起同步,肯定会超时,同步失败.
忽略:puppet master端还有一个邮件功能配置功能,用的不多,文件名为tagmail.conf文件,不做介绍了.
做完上面的配置,reload下puppetmaster服务:
[[email protected] puppet]# /etc/init.d/puppetmaster reload Stopping puppetmaster: [ OK ] Starting puppetmaster: [ OK ]
11、Agent端的配置
配置另外2台puppet agent配置,指明puppet server可以在全局配置中指定,也可以在agent中指定:
参考如下(配置二选一配置):
[main]#可以在全局配置中指定
server = puppet
[agent]#也可以在agent配置中指定
server = puppet
举例:
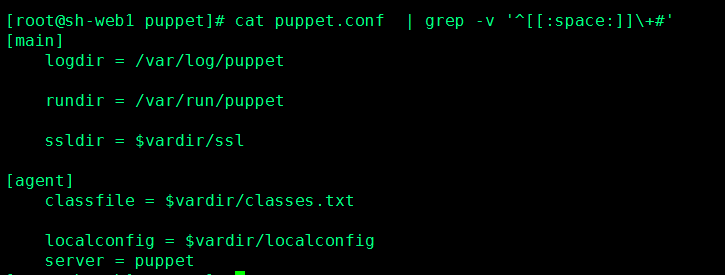
192.168.30.131 sh-web1这台puppet agent配置:(server在agent段指定)
[[email protected] puppet]# cat puppet.conf | grep -v ‘^[[:space:]]\+#‘ [main] logdir = /var/log/puppet rundir = /var/run/puppet ssldir = $vardir/ssl [agent] classfile = $vardir/classes.txt localconfig = $vardir/localconfig server = puppet
如图:
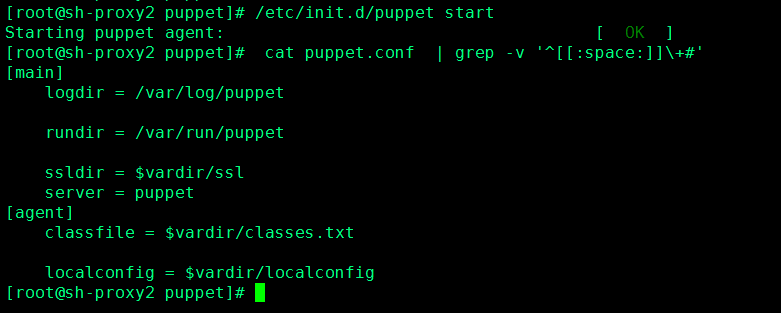
192.168.30.132 sh-proxy2这台puppet agent配置:(server在main段指定)
# cat puppet.conf | grep -v ‘^[[:space:]]\+#‘ [main] logdir = /var/log/puppet rundir = /var/run/puppet ssldir = $vardir/ssl server = puppet [agent] classfile = $vardir/classes.txt localconfig = $vardir/localconfig
agent 端/etc/puppet.conf文件配置完,分别启动服务:
[[email protected] puppet]# /etc/init.d/puppet start Starting puppet agent: [ OK ]
12、添加/etc/hosts中添加三台机器的解析(三台机器都需要相互解析,都加上),为了简单快捷就不做dns了.
192.168.30.134puppet 192.168.30.131sh-web1 192.168.30.132sh-proxy2
扩展:目前比较火的ip-域名映射关系的dns服务器除了bind外,还有dnsmasq,之前文章写过了,也支持dhcp和dns功能,软件极小,配置起来非常方便,dnsmasq的诞生本来时为了解决嵌入式系统问题的(我大学专业就是嵌入式的),所以可以想象到它小的程度.
做完上面的,puppet master上立即就签署了agent证书,自动完成立即生效,不需要人工干预.
#puppet cert list --all
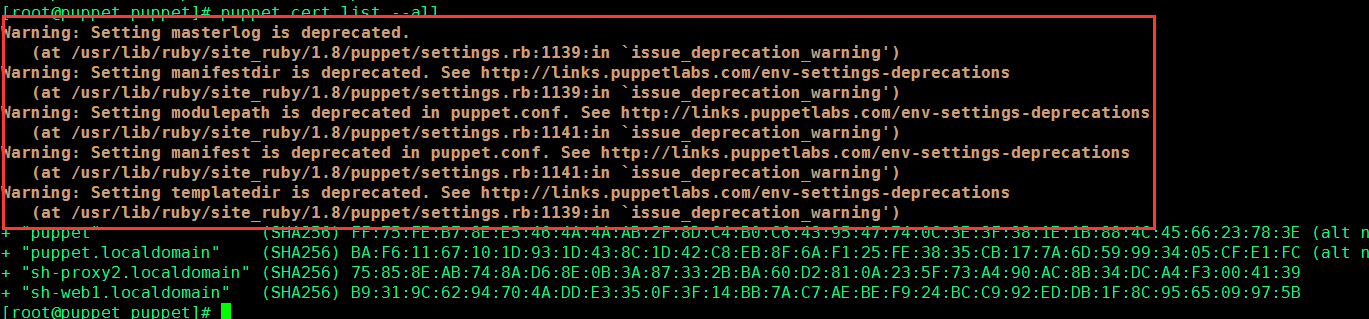
13、报警告(不是报错):
[[email protected] puppet]# puppet cert list --all Warning: Setting masterlog is deprecated. (at /usr/lib/ruby/site_ruby/1.8/puppet/settings.rb:1139:in `issue_deprecation_warning‘) Warning: Setting manifestdir is deprecated. See http://links.puppetlabs.com/env-settings-deprecations (at /usr/lib/ruby/site_ruby/1.8/puppet/settings.rb:1139:in `issue_deprecation_warning‘) Warning: Setting modulepath is deprecated in puppet.conf. See http://links.puppetlabs.com/env-settings-deprecations (at /usr/lib/ruby/site_ruby/1.8/puppet/settings.rb:1141:in `issue_deprecation_warning‘) Warning: Setting manifest is deprecated in puppet.conf. See http://links.puppetlabs.com/env-settings-deprecations (at /usr/lib/ruby/site_ruby/1.8/puppet/settings.rb:1141:in `issue_deprecation_warning‘) Warning: Setting templatedir is deprecated. See http://links.puppetlabs.com/env-settings-deprecations (at /usr/lib/ruby/site_ruby/1.8/puppet/settings.rb:1139:in `issue_deprecation_warning‘) + "puppet" (SHA256) FF:75:FE:B7:8E:E5:46:4A:4A:AB:2F:8D:C4:B0:C6:43:95:47:74:0C:3E:3F:38:1E:1B:88:4C:45:66:23:78:3E (alt names: "DNS:puppet", "DNS:puppet.localdomain") + "puppet.localdomain" (SHA256) BA:F6:11:67:10:1D:93:1D:43:8C:1D:42:C8:EB:8F:6A:F1:25:FE:38:35:CB:17:7A:6D:59:99:34:05:CF:E1:FC (alt names: "DNS:puppet", "DNS:puppet.localdomain") + "sh-proxy2.localdomain" (SHA256) 75:85:8E:AB:74:8A:D6:8E:0B:3A:87:33:2B:BA:60:D2:81:0A:23:5F:73:A4:90:AC:8B:34:DC:A4:F3:00:41:39 + "sh-web1.localdomain" (SHA256) B9:31:9C:62:94:70:4A:DD:E3:35:0F:3F:14:BB:7A:C7:AE:BE:F9:24:BC:C9:92:ED:DB:1F:8C:95:65:09:97:5B
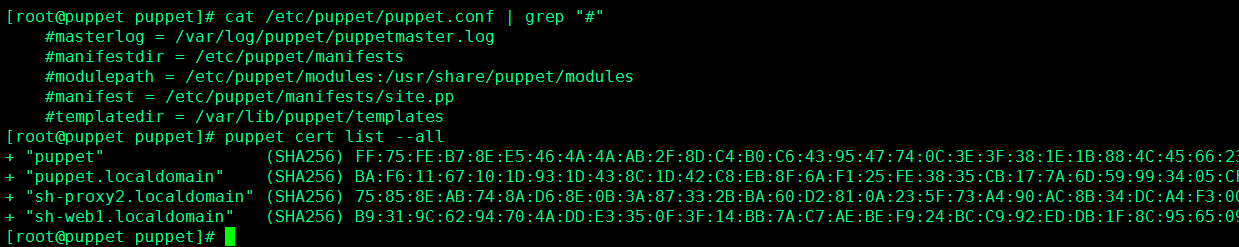
处理办法,注释掉这些:
[[email protected] puppet]# cat /etc/puppet/puppet.conf | grep "#" #masterlog = /var/log/puppet/puppetmaster.log #manifestdir = /etc/puppet/manifests #modulepath = /etc/puppet/modules:/usr/share/puppet/modules #manifest = /etc/puppet/manifests/site.pp #templatedir = /var/lib/puppet/templates
再次查看证书:
[[email protected] puppet]# puppet cert list --all + "puppet" (SHA256) FF:75:FE:B7:8E:E5:46:4A:4A:AB:2F:8D:C4:B0:C6:43:95:47:74:0C:3E:3F:38:1E:1B:88:4C:45:66:23:78:3E (alt names: "DNS:puppet", "DNS:puppet.localdomain") + "puppet.localdomain" (SHA256) BA:F6:11:67:10:1D:93:1D:43:8C:1D:42:C8:EB:8F:6A:F1:25:FE:38:35:CB:17:7A:6D:59:99:34:05:CF:E1:FC (alt names: "DNS:puppet", "DNS:puppet.localdomain") + "sh-proxy2.localdomain" (SHA256) 75:85:8E:AB:74:8A:D6:8E:0B:3A:87:33:2B:BA:60:D2:81:0A:23:5F:73:A4:90:AC:8B:34:DC:A4:F3:00:41:39 + "sh-web1.localdomain" (SHA256) B9:31:9C:62:94:70:4A:DD:E3:35:0F:3F:14:BB:7A:C7:AE:BE:F9:24:BC:C9:92:ED:DB:1F:8C:95:65:09:97:5B
结果如图:
14、总结:
到此puppet c/s 配置完成,修改的内容不多,主要在svn客户端操作:
1)、新增namespaceauth.conf配置文件:
3)、修改puppet master端puppet.conf文件.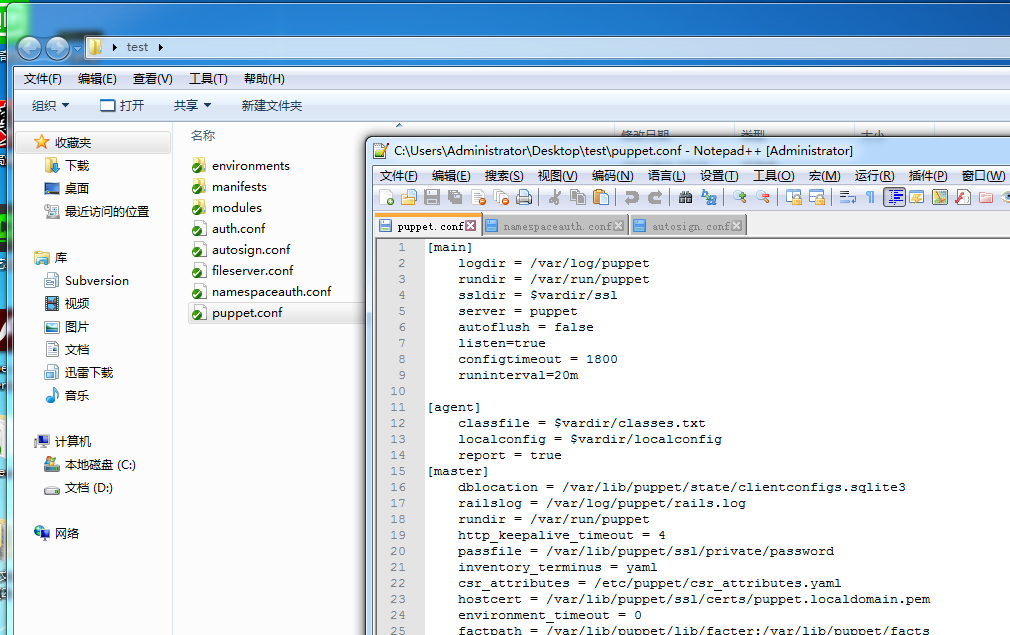 4)、Agent 端puppet.conf文件配置上面已经有就不截图了.
4)、Agent 端puppet.conf文件配置上面已经有就不截图了.
本文出自 “蚂蚁” 博客,请务必保留此出处http://215687833.blog.51cto.com/6724358/1962872
以上是关于Puppet安装部署篇的主要内容,如果未能解决你的问题,请参考以下文章