[EXP]CVE-2019-0803 Win32k漏洞提权工具
Posted k8gege
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了[EXP]CVE-2019-0803 Win32k漏洞提权工具相关的知识,希望对你有一定的参考价值。
0x000 漏洞信息
CVE-2019-0803 | Win32k 特权提升漏洞
发布时间: 2019-04-09
当 Win32k 组件无法正确处理内存中的对象时,Windows 中存在特权提升漏洞。成功利用此漏洞的攻击者可以在内核模式中运行任意代码。攻击者可随后安装程序;查看、更改或删除数据;或者创建拥有完全用户权限的新帐户。
若要利用此漏洞,攻击者首先必须登录到系统。然后,攻击者可以运行一个为利用此漏洞而经特殊设计的应用程序,从而控制受影响的系统。
0x001 影响版本
Microsoft Windows Server 2019 0 Microsoft Windows Server 2016 0 Microsoft Windows Server 2012 R2 0 Microsoft Windows Server 2012 0 Microsoft Windows Server 2008 R2 for x64-based Systems SP1 Microsoft Windows Server 2008 R2 for Itanium-based Systems SP1 Microsoft Windows Server 2008 for x64-based Systems SP2 Microsoft Windows Server 2008 for Itanium-based Systems SP2 Microsoft Windows Server 2008 for 32-bit Systems SP2 Microsoft Windows Server 1803 0 Microsoft Windows Server 1709 0 Microsoft Windows RT 8.1 Microsoft Windows 8.1 for x64-based Systems 0 Microsoft Windows 8.1 for 32-bit Systems 0 Microsoft Windows 7 for x64-based Systems SP1 Microsoft Windows 7 for 32-bit Systems SP1 Microsoft Windows 10 Version 1809 for x64-based Systems 0 Microsoft Windows 10 Version 1809 for ARM64-based Systems 0 Microsoft Windows 10 Version 1809 for 32-bit Systems 0 Microsoft Windows 10 Version 1803 for x64-based Systems 0 Microsoft Windows 10 Version 1803 for ARM64-based Systems 0 Microsoft Windows 10 Version 1803 for 32-bit Systems 0 Microsoft Windows 10 version 1709 for x64-based Systems 0 Microsoft Windows 10 Version 1709 for ARM64-based Systems 0 Microsoft Windows 10 version 1709 for 32-bit Systems 0 Microsoft Windows 10 version 1703 for x64-based Systems 0 Microsoft Windows 10 version 1703 for 32-bit Systems 0 Microsoft Windows 10 Version 1607 for x64-based Systems 0 Microsoft Windows 10 Version 1607 for 32-bit Systems 0 Microsoft Windows 10 for x64-based Systems 0 Microsoft Windows 10 for 32-bit Systems 0
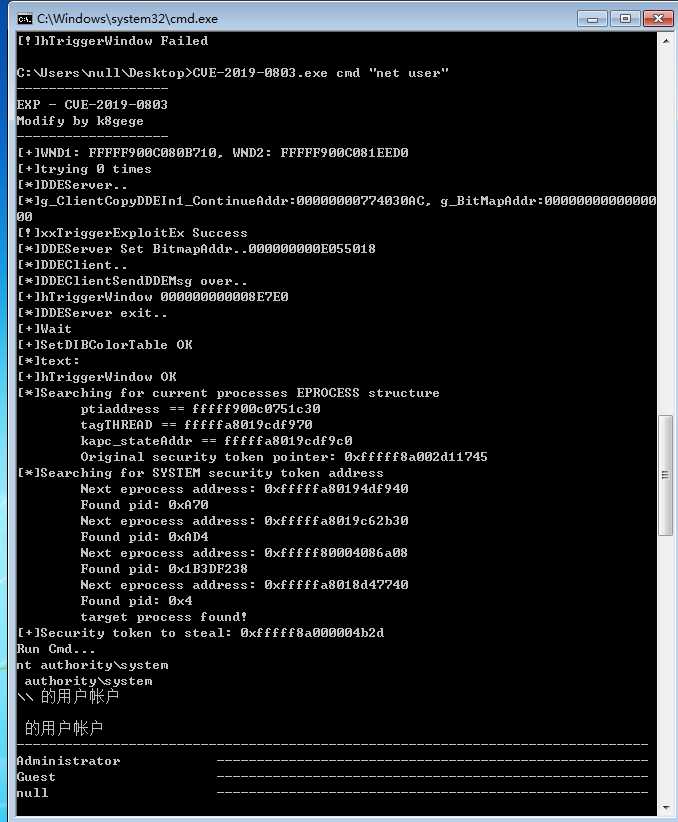
0x002 EXP用法
Usage: CVE-2019-0803.exe cmd cmdline
如图:可能需执行3-4次左右才能提权成功,测试系统为Win7 X64,其它未测。
0x003 下载
https://github.com/k8gege/K8tools/raw/master/CVE-2019-0803.exe
0x004 补丁
补丁号有很多个,不同的系统补丁号不一样,有时新的补丁包含旧洞补丁
旧的补丁号会被替换掉,所以每次提权都应该先到官方查看下对应补丁号
不要老是查询有没旧的补丁号,然后再去提权,没有旧的补丁号不代表没补
https://portal.msrc.microsoft.com/zh-cn/security-guidance/advisory/CVE-2019-0803
0x005 链接
https://www.exploit-db.com/exploits/46920
(steal Security token) https://github.com/mwrlabs/CVE-2016-7255
EDB Note: Download ~ https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/46920.zip
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0803
http://packetstormsecurity.com/files/153034/Microsoft-Windows-Win32k-Privilege-Escalation.html
以上是关于[EXP]CVE-2019-0803 Win32k漏洞提权工具的主要内容,如果未能解决你的问题,请参考以下文章
Win10蓝屏win32k power watchdog timeout 蓝屏代码0x0000019C
CVE-2018-8120 Microsoft Windows提权漏洞 Exp
win7 安装Oracle10g,使用exp工具导出Oracle11g用户所有数据,报错信息提示EXP-00056: ORACLE-12154