LitCTF crypto wp
Posted Cryglz
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了LitCTF crypto wp相关的知识,希望对你有一定的参考价值。
Hex?Hex!(初级)
文件下载下来后得到:
4c69744354467b746169313131636f6f6c6c616161217d
直接16进制解码:
s =\'4c69744354467b746169313131636f6f6c6c616161217d\'
print(bytes.fromhex(s))
得到flag:LitCTFtai111coollaaa!,换成NSSCTF,下同
梦想是红色的 (初级)
txt:
自由友善公正公正敬业法治自由自由和谐平等自由自由公正法治诚信民主诚信自由自由诚信民主爱国友善平等诚信富强友善爱国自由诚信民主敬业爱国诚信民主友善爱国平等爱国爱国敬业敬业友善爱国公正敬业爱国敬业和谐文明诚信文明友善爱国自由诚信民主爱国爱国诚信和谐友善爱国自由友善平等爱国友善平等友善自由诚信自由平等爱国爱国敬业敬业友善爱国敬业敬业友善自由友善平等诚信自由法治诚信和谐
核心价值观编码
直接在线解码

原来你也玩原神 (初级)
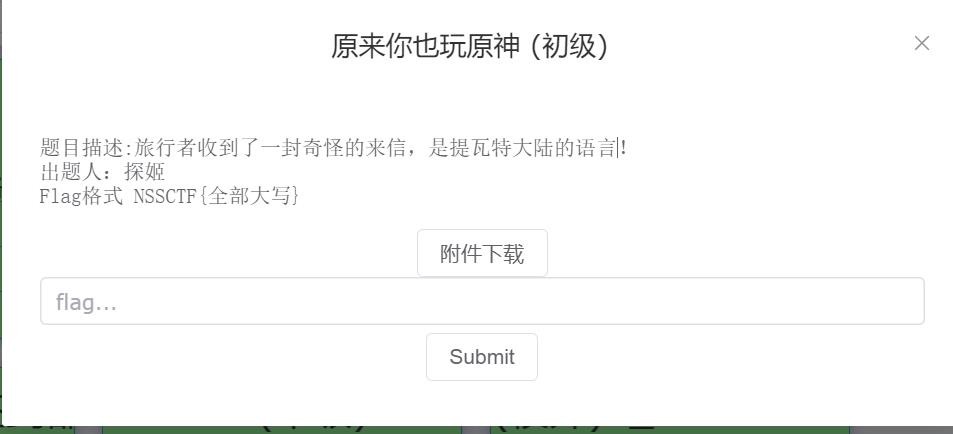
我靠!!。。。。咳咳咳,直接搜提瓦特大陆文字:
![(https://img2023.cnblogs.com/blog/2698491/202305/2698491-20230514014343632-2137279192.png)]
对照着下来就是flag:LitCTFYUANLAINIYEWANYUANSHENWWW
家人们!谁懂啊,RSA签到都不会 (初级)
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
p = getPrime(512)
q = getPrime(512)
e = 65537
n = p*q
c = pow(m,e,n)
print(f\'p = p\')
print(f\'q = q\')
print(f\'c = c\')
\'\'\'
p = 12567387145159119014524309071236701639759988903138784984758783651292440613056150667165602473478042486784826835732833001151645545259394365039352263846276073
q = 12716692565364681652614824033831497167911028027478195947187437474380470205859949692107216740030921664273595734808349540612759651241456765149114895216695451
c = 108691165922055382844520116328228845767222921196922506468663428855093343772017986225285637996980678749662049989519029385165514816621011058462841314243727826941569954125384522233795629521155389745713798246071907492365062512521474965012924607857440577856404307124237116387085337087671914959900909379028727767057
\'\'\'
import libnum
import gmpy2
p = 12567387145159119014524309071236701639759988903138784984758783651292440613056150667165602473478042486784826835732833001151645545259394365039352263846276073
q = 12716692565364681652614824033831497167911028027478195947187437474380470205859949692107216740030921664273595734808349540612759651241456765149114895216695451
c = 108691165922055382844520116328228845767222921196922506468663428855093343772017986225285637996980678749662049989519029385165514816621011058462841314243727826941569954125384522233795629521155389745713798246071907492365062512521474965012924607857440577856404307124237116387085337087671914959900909379028727767057
e = 65537
n = p*q
phi = (p-1)*(q-1)
d = gmpy2.invert(e,phi)
flag = pow(c,d,n)
print(libnum.n2s(int(flag)))
yafu (中级)
题目代码:
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
n = 1
for i in range(15):
n *=getPrime(32)
e = 65537
c = pow(m,e,n)
print(f\'n = n\')
print(f\'c = c\')
\'\'\'
n = 15241208217768849887180010139590210767831431018204645415681695749294131435566140166245881287131522331092026252879324931622292179726764214435307
c = 12608550100856399369399391849907846147170257754920996952259023159548789970041433744454761458030776176806265496305629236559551086998780836655717
\'\'\'
说了用yafu,然后如图
其实也可以不用,factordb库挺好用的,直接生成列表:
from factordb.factordb import FactorDB
f = FactorDB(15241208217768849887180010139590210767831431018204645415681695749294131435566140166245881287131522331092026252879324931622292179726764214435307)
f.get_factor_list()
f.connect()
prime = f.get_factor_list()
print(prime)
e = 65537
n = 15241208217768849887180010139590210767831431018204645415681695749294131435566140166245881287131522331092026252879324931622292179726764214435307
c = 12608550100856399369399391849907846147170257754920996952259023159548789970041433744454761458030776176806265496305629236559551086998780836655717
from functools import *
a = 1
phi = reduce(lambda a,b:a*(b-1),[1]+prime)
d = pow(e,-1,phi)
flag = pow(c,d,n)
print(bytes.fromhex(hex(flag)[2:]))
factordb(中级)
e = 65537
n = 87924348264132406875276140514499937145050893665602592992418171647042491658461
c = 87677652386897749300638591365341016390128692783949277305987828177045932576708
额,和上道题一样,可以在线factordb.com分解,也可以用上道题代码,把值改一下即可,这里不多赘述
(校外)P_Leak
很简单的一道dp泄露,直接上代码:
e = 65537
n = 50612159190225619689404794427464916374543237300894011803225784470008992781409447214236779975896311093686413491163221778479739252804271270231391599602217675895446538524670610623369953168412236472302812808639218392319634397138871387898452935081756580084070333246950840091192420542761507705395568904875746222477
dp =5892502924236878675675338970704766304539618343869489297045857272605067962848952532606770917225218534430490745895652561015493032055636004130931491316020329
c =39257649468514605476432946851710016346016992413796229928386230062780829495844059368939749930876895443279723032641876662714088329296631207594999580050131450251288839714711436117326769029649419789323982613380617840218087161435260837263996287628129307328857086987521821533565738409794866606381789730458247531619
for i in range(1, e): # 在范围(1,e)之间进行遍历
if (dp * e - 1) % i == 0:
if n % (((dp * e - 1) // i) + 1) == 0: # 存在p,使得n能被p整除
p = ((dp * e - 1) // i) + 1
q = n // (((dp * e - 1) // i) + 1)
phi = (q - 1) * (p - 1) # 欧拉定理
d = int(gp.invert(e, phi)) # 求模逆
m = pow(c, d, n) # 快速求幂取模运算
print(m) # 10进制明文
print(\'------------\')
print(hex(m)[2:]) # 16进制明文
print(\'------------\')
print(bytes.fromhex(hex(m)[2:])) # 16进制转文本
print(\'------------\')
print(libnum.n2s(m))
md5的破解
from Crypto.Util.number import *
from hashlib import md5
from secret import flag
#flag全是由小写字母及数字组成
m=md5(flag).hexdigest()
print(flag[:13]+flag[15:18]+flag[19:34]+flag[35:38])
print(m)
# b\'LitCTFmd5can3derypt213thoughcrsh\'
# 496603d6953a15846cd7cc476f146771
根据代码内容,爆破md5
import string
import hashlib
a=\'LitCTFmd5can??3de?rypt213thoughcr?sh\'
b=\'496603d6953a15846cd7cc476f146771\'
dic1=string.digits+string.ascii_lowercase+string.ascii_uppercase
for i1 in dic1:
for i2 in dic1:
for i3 in dic1:
for i4 in dic1:
bb = \'LitCTFmd5can\' + i1 + i2 + \'3de\' + i3+ \'rypt213thoughcr\' + i4 +\'sh\'
aa = hashlib.md5(bb.encode(\'utf-8\'))
bbb = aa.hexdigest()
if bbb == b:
print(i1, i2, i3,i4)
print(\'LitCTFmd5can\' + i1 + i2 + \'3de\' + i3+ \'rypt213thoughcr\' + i4 +\'sh\')
e的学问
题目代码
from Crypto.Util.number import *
m=bytes_to_long(b\'xxxxxx\')
p=getPrime(256)
q=getPrime(256)
e=74
n=p*q
c=pow(m,e,n)
print("p=",p)
print("q=",q)
print("c=",c)
#p= 86053582917386343422567174764040471033234388106968488834872953625339458483149
#q= 72031998384560188060716696553519973198388628004850270102102972862328770104493
#c= 3939634105073614197573473825268995321781553470182462454724181094897309933627076266632153551522332244941496491385911139566998817961371516587764621395810123
代码如下:
#sage环境运行
p= 86053582917386343422567174764040471033234388106968488834872953625339458483149
q= 72031998384560188060716696553519973198388628004850270102102972862328770104493
c=3939634105073614197573473825268995321781553470182462454724181094897309933627076266632153551522332244941496491385911139566998817961371516587764621395810123
N=p*q
e=74
phi=(p-1)*(q-1)
d = pow(e//2,-1,phi)
C = pow(c,d,N)
P.<a>=PolynomialRing(Zmod(p),implementation=\'NTL\')
f=a^2-C
mps=f.monic().roots()
P.<a>=PolynomialRing(Zmod(q),implementation=\'NTL\')
g=a^2-C
mqs=g.monic().roots()
for mpp in mps:
x=mpp[0]
for mqq in mqs:
y=mqq[0]
solution = hex(CRT_list([int(x), int(y)], [p, q]))[2:]
if len(solution) % 2 == 0:
print(bytes.fromhex(solution))
我测你vva
题目java代码如下:
public class Encrypto
public static void main(String[] args)
String flag="";
int cipher;
char[] arr;
arr=flag.toCharArray();
for(int i=0; i<flag.length(); i++)
if(i%2==0)
cipher=Integer.valueOf(arr[i]);
cipher=cipher+i;
System.out.print((char)cipher);
if(i%2!=0)
cipher=Integer.valueOf(arr[i]);
cipher=cipher-i;
System.out.print((char)cipher);
//cipher=HYEQJvPZ~X@+Bp
上面的程序是一个简单加密算法的 Java 实现。该程序接受一个字符串输入,标志,并根据字符串中字符的索引是奇数还是偶数通过添加或减去一个值来加密它。然后将加密的字符串打印到控制台。
加密后的字符串存储在变量cipher中,其值为HYEQJvPZ~X@+Bp。要解密字符串,您可以根据每个字符在字符串中的索引,通过减去或添加相同的值来反转加密过程。以下是解密函数的示例实现:
def decrypt(cipher):
result = []
for i in range(len(cipher)):
shift = i if i % 2 == 0 else -i
result.append(chr(ord(cipher[i]) - shift))
return \'\'.join(result)
encrypted = "HYEQJvPZ~X@+Bp"
decrypted = decrypt(encrypted)
print(decrypted)
The same common divisor (高级)
from Crypto.Util.number import *
m=bytes_to_long(b\'xxxxxx\')
e=65537
p=getPrime(1024)
q1=getPrime(1024)
q2=getPrime(1024)
n1=p*q1
n2=p*q2
c1=pow(m,e,n1)
c2=pow(m,e,n2)
n3=n1^n2
print(\'n1=\',n1)
print(\'n3=\',n3)
print(\'c1=\',c1)
print(\'c2=\',c2)
#n1= 9852079772293301283705208653824307027320071498525390578148444258198605733768947108049676831872672654449631852459503049139275329796717506126689710613873813880735666507857022786447784753088176997374711523987152412069255685005264853118880922539048290400078105858759506186417678959028622484823376958194324034590514104266608644398160457382895380141070373685334979803658172378382884352616985632157233900719194944197689860219335238499593658894630966428723660931647038577670614850305719449893199713589368780231046895222526070730152875112477675102652862254926169713030701937231206405968412044029177246460558028793385980934233
#n3= 4940268030889181135441311597961813780480775970170156650560367030148383674257975796516865571557828263935532335958510269356443566533284856608454193676600884849913964971291145182724888816164723930966472329604608512023988191536173112847915884014445539739070437180314205284883149421228744714989392788108329929896637182055266508625177260492776962915873036873839946591259443753924970795669864031580632650140641456386202636466624658715315856453572441182758855085077441336516178544978457053552156714181607801760605521338788424464551796638531143900048375037218585999440622490119344971822707261432953755569507740550277088437182
#c1= 7066425618980522033304943700150361912772559890076173881522840300333719222157667104461410726444725540513601550570478331917063911791020088865705346188662290524599499769112250751103647749860198318955619903728724860941709527724500004142950768744200491448875522031555564384426372047270359602780292587644737898593450148108629904854675417943165292922990980758572264063039172969633878015560735737699147707712154627358077477591293746136250207139049702201052305840453700782016480965369600667516646007546442708862429431724013679189842300429421340122052682391471347471758814138218632022564279296594279507382548264409296929401260
#c2= 854668035897095127498890630660344701894030345838998465420605524714323454298819946231147930930739944351187708040037822108105697983018529921300277486094149269105712677374751164879455815185393395371001495146490416978221501351569800028842842393448555836910486037183218754013655794027528039329299851644787006463456162952383099752894635657833907958930587328480492546831654755627949756658554724024525108575961076341962292900510328611128404001877137799465932130220386963518903892403159969133882215092783063943679288192557384595152566356483424061922742307738886179947575613661171671781544283180451958232826666741028590085269
一道简单的广播攻击:给了一个e,和多组的n,c。这些nc还都是一个明文m,通过对不同的n进行gcd()算法,求出最大公约数,(即p)
求出P了,就能求出q,进而求出d, 解出明文m
import gmpy2
import binascii
e = 65537
n1 = 9852079772293301283705208653824307027320071498525390578148444258198605733768947108049676831872672654449631852459503049139275329796717506126689710613873813880735666507857022786447784753088176997374711523987152412069255685005264853118880922539048290400078105858759506186417678959028622484823376958194324034590514104266608644398160457382895380141070373685334979803658172378382884352616985632157233900719194944197689860219335238499593658894630966428723660931647038577670614850305719449893199713589368780231046895222526070730152875112477675102652862254926169713030701937231206405968412044029177246460558028793385980934233
c1 = 7066425618980522033304943700150361912772559890076173881522840300333719222157667104461410726444725540513601550570478331917063911791020088865705346188662290524599499769112250751103647749860198318955619903728724860941709527724500004142950768744200491448875522031555564384426372047270359602780292587644737898593450148108629904854675417943165292922990980758572264063039172969633878015560735737699147707712154627358077477591293746136250207139049702201052305840453700782016480965369600667516646007546442708862429431724013679189842300429421340122052682391471347471758814138218632022564279296594279507382548264409296929401260
n2 = 13275392358603749049507302824073643158313511157306042129424622043169404438475070367199888792522735816696831092853554043588044629442339762181808939836068784930395387656511731023773900700005021564847480224798180592959510217158765133918150651706674329603149481255390797032771700235015269257730220757739489147426447858665350504461218790022992177725157756735193197648927044824616697206813752794351736481372892433605669363455272775767270738838271685683788851792503697508906872616175734362549442203442409947760416740297996886756365560632301306250478012961270642177511142736084877917270911656025730517314096773424314000497639
c2 = 854668035897095127498890630660344701894030345838998465420605524714323454298819946231147930930739944351187708040037822108105697983018529921300277486094149269105712677374751164879455815185393395371001495146490416978221501351569800028842842393448555836910486037183218754013655794027528039329299851644787006463456162952383099752894635657833907958930587328480492546831654755627949756658554724024525108575961076341962292900510328611128404001877137799465932130220386963518903892403159969133882215092783063943679288192557384595152566356483424061922742307738886179947575613661171671781544283180451958232826666741028590085269
p = gmpy2.gcd(n1,n2) # 欧几里得算法,p为两者的最大公约数
q = n1 // p
phi = (p-1)*(q-1)
d = gmpy2.invert(e,phi)
m = gmpy2.powmod(c1,d,n1)
print(binascii.unhexlify(hex(m)[2:]))
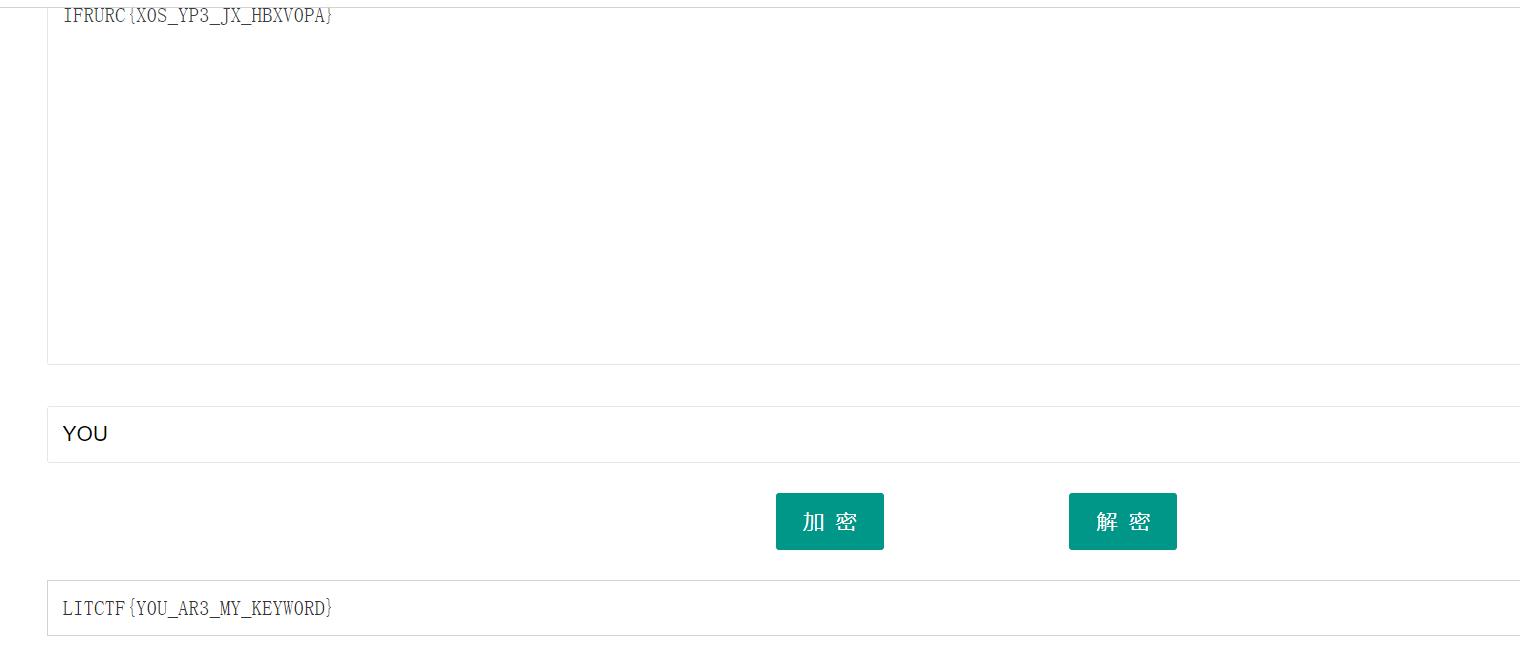
你是我的关键词(Keyworld) (初级),
txtx:IFRURCX0S_YP3_JX_HBXV0PA
根据题目提示,为关键字密码,直接在现网站解密:密钥为大写:YOU
(校外)Is this only base?
SWZxWl=F=DQef0hlEiSUIVh9ESCcMFS9NF2NXFzM
先栅栏数23解密,在base64解码,在凯撒密码解码
(校外)Virginia
下载下来是这:
Ysexj lrk rzmkses os wilj hhks joa rtsy xzmktye yt xuim ehgy joa ofsz blnz yz pohv tnjx fxtx yuzc dxjlmy fyd nzr tnjx fuw cegq! Orkfx wnfe yuz haty eo jwpas;lz wnjce etf wgse tu lz;bk bsaz dzu cfyt zt me,hjnaaxp yuz sabj znrd znk qtfk fyd usp cnfyck yz du fwl zmp tnnygy dzu cfyt zt oo.Sfj yuz sabj pnuzrh nfapospsy yz mgpp yuz dwkje,ettfgn ycigqd tu rlkk dzu yycotl,pnuzrh ytcrub eo qjpp etf harln,kszumm sovj eo sfve etf hguay? Gqhaex auz dzuxxpll ny ozmpry’xsokx.Tf etf fkjw tnfe iz mfrzx joa,ne pxtmahqj hawes zmp ozmpr vjcsus, eou.Yse nfapojdt uk aeuuwe jty’t tjneyxlroqj hgap tnj meyy zf kapreysitl;ehkd uuyy xaqj ehk rzsz tq ebjcyzmtnm ysaz hzmkx llusr tnjtr cfj.Hguaitjds rnps ltc tntde cmz cxd,ehuxp wnt suxy, ehuxp wnt sabj degwnhki,lnj ysoyj hhu mlvk yciki,qox tyle ysee hln guarkhtazj ehk nxpuweathp ol upovqp,wnt sabj eoahsej yseow wibjd.Luap bkltny bttn f dmoqp,gxths cneh g ptsy fyd ksos cneh g ypax.Yse hwtgnypsz kftawp woqw arblyy gp bgxpd us l fuwrozypn vfdt, etf cgs’e gu ty wkqw it qtfkzytoq joa qpt mt zf etfr vfdt lftlawps gso hkfctghsey.Bset dzu cjce htcn,etf wkwp cxdtnm fyd kapretye gwzuti joa bls yrtlosr.Loap yuzc lokp su ysaz bset dzu jnp,yuz\'ce zmp otj hhu nd ssnwitl lnj jgexdznk fcoaso yuz ts iwjitl.
Uwegxp skso tnnd mkxdamj eo zmzsk upovqp wnt xegs dosjehosr tu dzu,zt ehuxp wnt sabj eoahsej dzux qtfk ny otj hae tc attehkw,eo zmzsk bso sfve etf ssnwe cmpn etf rkfwle spej ne,tu ysoyj ehgy xaqj joa xpe zmp bxnrhzjc soip ol ysitld wnjy yuz lrk wparqj duby,tu ysoyj hhu dzu cfyt zt wez yses pyoc ysaz dzu guarkhtazj ehknc fxnpnjxsiv.Fyd ok joa izn’z, izn’z bzrxd,yozmtnm gld cnwl nfapks eo etf,yuz hirq uuyy xiyx zuz ty tnj zpvtctastte yz bxnrhzjy surpotj’d dgd hizm ehox xeyxlgk.Rj pgxdwuwo iy szt g wpgaqlr Ifpsgw aayxhoxi,lnj yse ksn frfr=[86, 116, 128, 80, 98, 85, 139, 122, 134, 114, 125, 136, 117, 123, 129, 127, 128, 128, 142, 130, 140, 147, 127, 132, 131, 136, 151, 134, 152, 164] -Cgjdax
维吉尼亚解码:
Please send this message to those people who mean something to you,to those who have touched your life in one way or another,to those who make you smile when you really need it,to those that make you see the brighter side of things when you are really down,to those who you want to let them know that you appreciate their friendship.And if you don’t, don’t worry,nothing bad will happen to you,you will just miss out on the opportunity to brighten someone’s day with this message.My password is not a regular Caesar password,and the enc flag=[86, 116, 128, 80, 98, 85, 139, 122, 134, 114, 125, 136, 117, 123, 129, 127, 128, 128, 142, 130, 140, 147, 127, 132, 131, 136, 151, 134, 152, 164] -Caesar
知道是凯撒:
flag=[86, 116, 128, 80, 98, 85, 139, 122, 134, 114, 125, 136, 117, 123, 129, 127, 128, 128, 142, 130, 140, 147, 127, 132, 131, 136, 151, 134, 152, 164],与“LitCTF”的ascii码作比较
密文与明文之间,比如前六个数值与明文LitCTF的差距分别是-10,-11,-12.。。。代码如下:
flag=[86, 116, 128, 80, 98, 85, 139, 122, 134, 114, 125, 136, 117, 123, 129, 127, 128, 128, 142, 130, 140, 147, 127, 132, 131, 136, 151, 134, 152, 164]
j=-10
for i in flag:
print(chr(i + j), end=\'\')
j -= 1
babyLCG
题目:
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
bit_len = m.bit_length()
a = getPrime(bit_len)
b = getPrime(bit_len)
p = getPrime(bit_len+1)
seed = m
result = []
for i in range(10):
seed = (a*seed+b)%p
result.append(seed)
print(result)
"""
result = [699175025435513913222265085178805479192132631113784770123757454808149151697608216361550466652878, 193316257467202036043918706856603526262215679149886976392930192639917920593706895122296071643390, 1624937780477561769577140419364339298985292198464188802403816662221142156714021229977403603922943, 659236391930254891621938248429619132720452597526316230221895367798170380093631947248925278766506, 111407194162820942281872438978366964960570302720229611594374532025973998885554449685055172110829, 1415787594624585063605356859393351333923892058922987749824214311091742328340293435914830175796909, 655057648553921580727111809001898496375489870757705297406250204329094679858718932270475755075698, 1683427135823894785654993254138434580152093609545092045940376086714124324274044014654085676620851, 492953986125248558013838257810313149490245209968714980288031443714890115686764222999717055064509, 70048773361068060773257074705619791938224397526269544533030294499007242937089146507674570192265]
"""
简单的一道lcg,解题代码:
from Crypto.Util.number import *
def gcd(a,b):
if(b==0):
return a
else:
return gcd(b,a%b)
s = [699175025435513913222265085178805479192132631113784770123757454808149151697608216361550466652878, 193316257467202036043918706856603526262215679149886976392930192639917920593706895122296071643390, 1624937780477561769577140419364339298985292198464188802403816662221142156714021229977403603922943, 659236391930254891621938248429619132720452597526316230221895367798170380093631947248925278766506, 111407194162820942281872438978366964960570302720229611594374532025973998885554449685055172110829, 1415787594624585063605356859393351333923892058922987749824214311091742328340293435914830175796909, 655057648553921580727111809001898496375489870757705297406250204329094679858718932270475755075698, 1683427135823894785654993254138434580152093609545092045940376086714124324274044014654085676620851, 492953986125248558013838257810313149490245209968714980288031443714890115686764222999717055064509, 70048773361068060773257074705619791938224397526269544533030294499007242937089146507674570192265]
t = []
for i in range(9):
t.append(s[i]-s[i-1])
all_n = []
for i in range(7):
all_n.append(gcd((t[i+1]*t[i-1]-t[i]*t[i]), (t[i+2]*t[i]-t[i+1]*t[i+1])))
MMI = lambda A, n,s=1,t=0,N=0: (n < 2 and t%N or MMI(n, A%n, t, s-A//n*t, N or n),-1)[n<1] #逆元计算
for n in all_n:
n=abs(n)
if n==1:
continue
a=(s[2]-s[1])*MMI((s[1]-s[0]),n)%n
ani=MMI(a,n)
b=(s[1]-a*s[0])%n
seed = (ani*(s[0]-b))%n
plaintext=seed
print(long_to_bytes(plaintext))
easy_math (中级)
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
e = 65537
p = getPrime(512)
q = getPrime(128)
n = p*q
hint = p**3-q**5
c = pow(m,e,n)
print(f\'n = n\')
print(f\'c = c\')
print(f\'hint = hint\')
\'\'\'
n = 2230791374046346835775433548641067593691369485828070649075162141394476183565187654365131822111419512477883295758461313983481545182887415447403634720326639070667688614534290859200753589300443797
c = 2168563038335029902089976057856861885635845445863841607485310134441400500612435296818745930370268060353437465666224400129105788787423156958336380480503762222278722770240792709450637433509537280
hint = 392490868359411675557103683163021977774935163924606169241731307258226973701652855448542714274348304997416149742779376023311152228735117186027560227613656229190807480010615064372521942836446425717660375242197759811804760170129768647414717571386950790115746414735411766002368288743086845078803312201707960465419405926186622999423245762570917629351110970429987377475979058821154568001902541710817731089463915930932142007312230897818177067675996751110894377356758932
\'\'\'
运sympy库解方程:
n = 2230791374046346835775433548641067593691369485828070649075162141394476183565187654365131822111419512477883295758461313983481545182887415447403634720326639070667688614534290859200753589300443797
c = 2168563038335029902089976057856861885635845445863841607485310134441400500612435296818745930370268060353437465666224400129105788787423156958336380480503762222278722770240792709450637433509537280
hint = 392490868359411675557103683163021977774935163924606169241731307258226973701652855448542714274348304997416149742779376023311152228735117186027560227613656229190807480010615064372521942836446425717660375242197759811804760170129768647414717571386950790115746414735411766002368288743086845078803312201707960465419405926186622999423245762570917629351110970429987377475979058821154568001902541710817731089463915930932142007312230897818177067675996751110894377356758932
e = 65537
import sympy
import libnum
from Crypto.Util.number import *
p,q = sympy.symbols("x,y")
eq1 = p*q - 2230791374046346835775433548641067593691369485828070649075162141394476183565187654365131822111419512477883295758461313983481545182887415447403634720326639070667688614534290859200753589300443797
eq2 = p**3-q**5-392490868359411675557103683163021977774935163924606169241731307258226973701652855448542714274348304997416149742779376023311152228735117186027560227613656229190807480010615064372521942836446425717660375242197759811804760170129768647414717571386950790115746414735411766002368288743086845078803312201707960465419405926186622999423245762570917629351110970429987377475979058821154568001902541710817731089463915930932142007312230897818177067675996751110894377356758932
s = sympy.solve([eq1,eq2],[p,q])
p = s[0][0]
q = s[0][1]
n=p*q
fn=(p-1)*(q-1)
d=inverse(e,fn)
flag=pow(c,d,n)
print(\'flag=\',flag)
print(libnum.n2s(int(flag)))
隐晦的聊天记录
出题人:6c73d5240a948c86981bc294814d
某不知名收件人:收到消息attack at dawn
出题人:xxxxxxxxxxxxxxxxxxxxxxxxxxxx
某不知名收件人:收到消息Monday or Thur
已知出题人和收件人手中的密钥相同,请解出出题人第二次发送的密文呢(16进制,字母小写,解得的结果记得要加上LitCTF哦。)
opt加密,直接异或:代码如下:
s = \'6c73d5240a948c86981bc294814d\'
m1 = \'attack at dawn\'
m2 = \'Monday or Thur\'
# 将s和m1转换为二进制序列
s_bin = bin(int(s, 16))[2:].zfill(len(s) * 4)
m1_bin = \'\'.join(format(ord(c), \'08b\') for c in m1)
# 对二进制序列进行异或操作
key_bin = \'\'
for i in range(len(s_bin)):
key_bin += str(int(s_bin[i]) ^ int(m1_bin[i]))
# 将“Monday or Thur”转换为二进制序列
m2_bin = \'\'.join(format(ord(c), \'08b\') for c in m2)
# 对二进制序列进行异或操作
final_bin = \'\'
for i in range(len(key_bin)):
final_bin += str(int(key_bin[i]) ^ int(m2_bin[i]))
# 将异或结果转换为字符串
result = []
for i in range(0, len(final_bin), 8):
result.append (int(final_bin[i:i+8], 2))
print(result)
m = [64, 104, 207, 33, 8, 134, 140, 136, 158, 27, 242, 157, 131, 81]
s = \'\'
for i in m:
s +=hex(int(i))[2:]
print(s)
#4068cf2108868c889e1bf29d8351
Euler
题目如下:
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
p = getPrime(512)
q = getPrime(512)
n = p*q
c = pow(m,n-p-q+3,n)
print(f\'n = n\')
print(f\'c = c\')
"""
n = 115140122725890943990475192890188343698762004010330526468754961357872096040956340092062274481843042907652320664917728267982409212988849109825729150839069369465433531269728824368749655421846730162477193420534803525810831025762500375845466064264837531992986534097821734242082950392892529951104643690838773406549
c = 406480424882876909664869928877322864482740577681292497936198951316587691545267772748204383995815523935005725558478033908575228532559165174398668885819826720515607326399097899572022020453298441
"""
c= m^(phi+2) mod n =m^2 * m^phi mod n
又因为m^phi =1 mod n
c = m^2 mod n
解题代码:
import gmpy2
from libnum import*
n = 115140122725890943990475192890188343698762004010330526468754961357872096040956340092062274481843042907652320664917728267982409212988849109825729150839069369465433531269728824368749655421846730162477193420534803525810831025762500375845466064264837531992986534097821734242082950392892529951104643690838773406549
c= 406480424882876909664869928877322864482740577681292497936198951316587691545267772748204383995815523935005725558478033908575228532559165174398668885819826720515607326399097899572022020453298441
i = 0
while 1:
if(gmpy2.iroot(c+i*n,2)[1]==1): #开根号
print(gmpy2.iroot(c+i*n,2))
m = gmpy2.iroot(c+i*n,2)[0]
break
i=i+1
print(n2s(int(m)))
Where is P
题目:
from Crypto.Util.number import *
m=bytes_to_long(b\'XXXX\')
e=65537
p=getPrime(1024)
q=getPrime(1024)
n=p*q
print(p)
c=pow(m,e,n)
P=p>>340
print(P)
a=pow(P,3,n)
print("n=",n)
print("c=",c)
print("a=",a)
#n= 24479907029118467064460793139240403258697681144532146836881997837526487637306591893357774423547391867013441147680031968367449693796015901951120514250935018725570026327610524687128709707340727799633444550317834481416507364804274266363478822257132586592232042108076935945436358397787891169163821061005102693505011197453089873909085170776511350713452580692963748763166981047023704528272230392479728897831538235554137129584665886878574314566549330671483636900134584707867654841021494106881794644469229030140144595938886437242375435914268001721437309283611088568191856208951867342004280893021653793820874747638264412653721
#c= 6566517934961780069851397787369134601399136324586682773286046135297104713708615112015588908759927424841719937322574766875308296258325687730658550956691921018605724308665345526807393669538103819281108643141723589363068859617542807984954436567078438099854340705208503317269397632214274507740533638883597409138972287275965697689862321166613821995226000320597560745749780942467497435742492468670016480112957715214640939272457886646483560443432985954141177463448896521810457886108311082101521263110578485768091003174683555938678346359150123350656418123918738868598042533211541966786594006129134087145798672161268647536724
#a= 22184346235325197613876257964606959796734210361241668065837491428527234174610482874427139453643569493268653377061231169173874401139203757698022691973395609028489121048788465356158531144787135876251872262389742175830840373281181905217510352227396545981674450409488394636498629147806808635157820030290630290808150235068140864601098322473572121965126109735529553247807211711005936042322910065304489093415276688746634951081501428768318098925390576594162098506572668709475140964400043947851427774550253257759990959997691631511262768785787474750441024242552456956598974533625095249106992723798354594261566983135394923063605
rsa很典型的p高位泄露:
代码如下:
import gmpy2 #先求P
from libnum import*
n = 24479907029118467064460793139240403258697681144532146836881997837526487637306591893357774423547391867013441147680031968367449693796015901951120514250935018725570026327610524687128709707340727799633444550317834481416507364804274266363478822257132586592232042108076935945436358397787891169163821061005102693505011197453089873909085170776511350713452580692963748763166981047023704528272230392479728897831538235554137129584665886878574314566549330671483636900134584707867654841021494106881794644469229030140144595938886437242375435914268001721437309283611088568191856208951867342004280893021653793820874747638264412653721
c= 22184346235325197613876257964606959796734210361241668065837491428527234174610482874427139453643569493268653377061231169173874401139203757698022691973395609028489121048788465356158531144787135876251872262389742175830840373281181905217510352227396545981674450409488394636498629147806808635157820030290630290808150235068140864601098322473572121965126109735529553247807211711005936042322910065304489093415276688746634951081501428768318098925390576594162098506572668709475140964400043947851427774550253257759990959997691631511262768785787474750441024242552456956598974533625095249106992723798354594261566983135394923063605
i = 0
while 1:
if(gmpy2.iroot(c+i*n,3)[1]==1): #开根号
print(gmpy2.iroot(c+i*n,3))
break
i=i+1
#sage
from sage.all import *
n=24479907029118467064460793139240403258697681144532146836881997837526487637306591893357774423547391867013441147680031968367449693796015901951120514250935018725570026327610524687128709707340727799633444550317834481416507364804274266363478822257132586592232042108076935945436358397787891169163821061005102693505011197453089873909085170776511350713452580692963748763166981047023704528272230392479728897831538235554137129584665886878574314566549330671483636900134584707867654841021494106881794644469229030140144595938886437242375435914268001721437309283611088568191856208951867342004280893021653793820874747638264412653721
P= 66302204855869216148926460265779698576660998574555407124043768605865908069722142097621926304390549253688814246272903647124801382742681337653915017783954290069842646020090511605930590064443141710086879668946
#P为p去除0的剩余位e = 0x10001
pbits = 1024
kbits = pbits - P.nbits()
print(P.nbits())
P = P << kbits
PR.<x> = PolynomialRing(Zmod(n))
f = x + P
roots = f.small_roots(X=2^kbits, beta=0.4)
if roots:
p = P+int(roots[0])
print("n= "+str(n))
print("p= "+str(p))
print("q= "+str(n//p))
baby_xor
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
assert len(flag)==32
p = getPrime(512)
q = getPrime(512)
n = p*q
e = 65537
c1 = p^m
c2 = pow(m,e,n)
print(f\'n = n\')
print(f\'c1 = c1\')
print(f\'c2 = c2\')
"""
n = 139167681803392690594490403105432649693546256181767408269202101512534988406137879788255103631885736461742577594980136624933914700779445704490217419248411578290305101891222576080645870988658334799437317221565839991979543660824098367011942169305111105129234902517835649895908656770416774539906212596072334423407
c1 = 11201139662236758800406931253538295757259990870588609533820056210585752522925690049252488581929717556881067021381940083808024384402885422258545946243513996
c2 = 112016152270171196606652761990170033221036025260883289104273504703557624964071464062375228351458191745141525003775876044271210498526920529385038130932141551598616579917681815276713386113932345056134302042399379895915706991873687943357627747262597883603999621939794450743982662393955266685255577026078256473601
"""
flag头已经知道了,异或一下能得到50bit,这样coppersmith就很好解了
#sage环境
import gmpy2
from Crypto.Util.number import *
n = 139167681803392690594490403105432649693546256181767408269202101512534988406137879788255103631885736461742577594980136624933914700779445704490217419248411578290305101891222576080645870988658334799437317221565839991979543660824098367011942169305111105129234902517835649895908656770416774539906212596072334423407
c1 = 11201139662236758800406931253538295757259990870588609533820056210585752522925690049252488581929717556881067021381940083808024384402885422258545946243513996
c2 = 112016152270171196606652761990170033221036025260883289104273504703557624964071464062375228351458191745141525003775876044271210498526920529385038130932141551598616579917681815276713386113932345056134302042399379895915706991873687943357627747262597883603999621939794450743982662393955266685255577026078256473601
m=0b1001100011010010111010001000011010101000100011001111011
m=m<<200
p=m^^c1
p4=p>>220
pbits = 512
kbits = pbits - p4.nbits()
p4 = p4 <<kbits
PR.<x> = PolynomialRing(Zmod(n))
f = x + p4
x0 = f.small_roots(X=2^kbits, beta=0.4)[0]
p = p4+x0
assert n % p == 0
q = n//int(p)
assert p*q==n
e = 65537
phi = (q-1) * (p-1)
d = inverse(e,-1,phi)
m = pow(c2,d,n)
print(m)
print(long_to_bytes(m))
Crypto-RSA-1
i春秋第二届春秋欢乐赛RSA256 WP
题目链接:RSA256
0x00 查看题目内容
下载文件并解压,发现压缩包里有三段密文以及一个公钥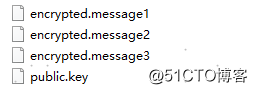
0x01 使用openssl查看公钥
看到public.key以后用kali linux里的openssl查看
查看一下openssl 中rsa的相关命令
[email protected]:~/Desktop# openssl rsa -help
Usage: rsa [options]
Valid options are:
-help Display this summary
-inform format Input format, one of DER NET PEM
-outform format Output format, one of DER NET PEM PVK
-in val Input file
-out outfile Output file
-pubin Expect a public key in input file
-pubout Output a public key
-passout val Output file pass phrase source
-passin val Input file pass phrase source
-RSAPublicKey_in Input is an RSAPublicKey
-RSAPublicKey_out Output is an RSAPublicKey
-noout Don‘t print key out
-text Print the key in text
-modulus Print the RSA key modulus
-check Verify key consistency
-* Any supported cipher
-pvk-strong Enable ‘Strong‘ PVK encoding level (default)
-pvk-weak Enable ‘Weak‘ PVK encoding level
-pvk-none Don‘t enforce PVK encoding
-engine val Use engine, possibly a hardware device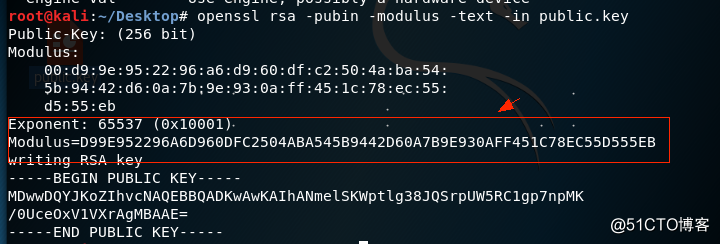
0x02 把N转成十进制
因为N是十六进制数 所以得把N转换成十进制才能用在线分解网站将其分解
[email protected]:~/Desktop# python
Python 2.7.15 (default, Jul 28 2018, 11:29:29)
[GCC 8.1.0] on linux2
Type "help", "copyright", "credits" or "license" for more information.
>>> Modulus=0xD99E952296A6D960DFC2504ABA545B9442D60A7B9E930AFF451C78EC55D555EB
>>> Modulus
98432079271513130981267919056149161631892822707167177858831841699521774310891L
0x03因式分解
将n进行因式分解来得到我们的p和q (推荐使用http://factordb.com/)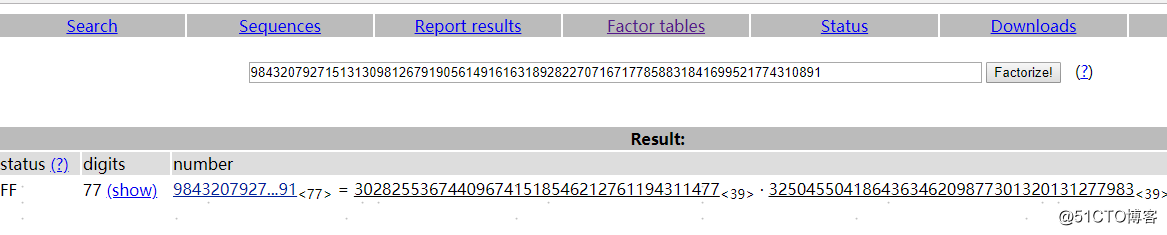
0x04 生成私钥解密
import gmpy2
import rsa
p = 302825536744096741518546212761194311477
q = 325045504186436346209877301320131277983
n = p * q
e = 65537
d = int(gmpy2.invert(e , (p-1) * (q-1)))
privatekey = rsa.PrivateKey(n , e , d , p , q)
with open("encrypted.message1" , "rb") as f:
print(rsa.decrypt(f.read(), privatekey).decode())
with open("encrypted.message2" , "rb") as f:
print(rsa.decrypt(f.read(), privatekey).decode())
with open("encrypted.message3" , "rb") as f:
print(rsa.decrypt(f.read(), privatekey).decode())以上是关于LitCTF crypto wp的主要内容,如果未能解决你的问题,请参考以下文章