Openssl CA证书生成以及双向认证,及windows系统证书批量导出,android cer转bks
Posted 冰翔不败传说
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Openssl CA证书生成以及双向认证,及windows系统证书批量导出,android cer转bks相关的知识,希望对你有一定的参考价值。
Openssl CA证书生成以及双向认证
首先本文主要参照这篇文章写的
http://h2appy.blog.51cto.com/609721/1181234
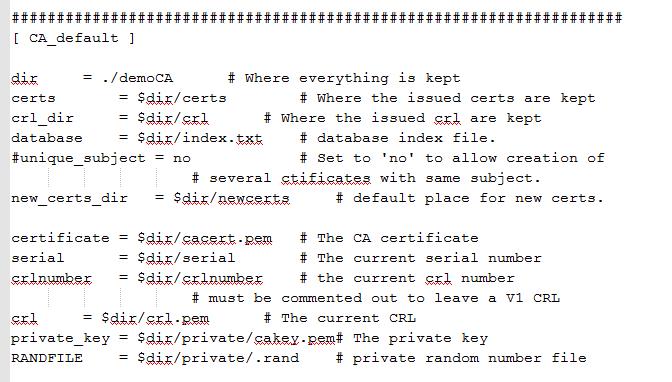
只是途中有些问题折腾了一下,比如openssl.cnf如何来的,这个文件在编译完openssl后,应该openssl根目录下/apps/demoCA有个,可以把他拷贝到openssl.exe同一级目录
里面有些目录配置,自己可以修改下,但是我没有修改,所以最后生成的文件路径必须按openssl.cnf里面来,至于如何编译openssl 请参考我的另一篇文章
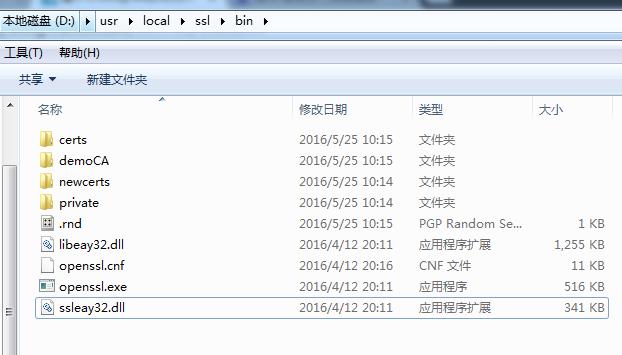
开始生成证书,需要提前做一些准备,生成一些特定目录,这些目录和openssl.cnf里面配置要求一致,在demoCA目录下,还需要建立一个index.txt,index.txt.attr空文件,以及serial文件,serial文件里面写00
注意每次输入下一步命令前,如果index.txt serial文件内容发生改变,请把index.txt中的内容清空,serial重置为00,否则后续命令中会报错(比如报数据库更新错误,此时依然会产生证书,但是c++代码加载证书时却会报错)
打开openssl.cnf文件,可以看到其中的一些目录结构要求
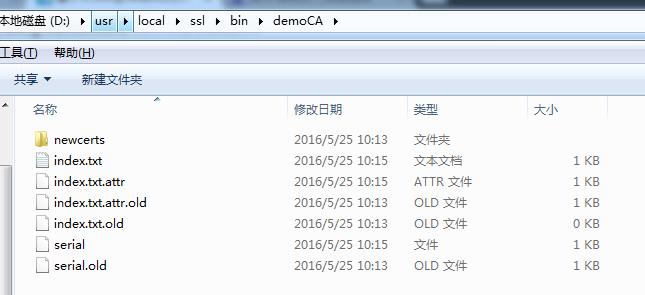
serial文件内容图

cmd进入openssl.exe所在目录下,依次输入以下命令(证书名字可以自己调整,输入过程中需要输入一些信息,如国家,省,市,主机名,邮件,密码等,请尽量保持一致) 例如我的主机名就写127.0.0.1 可以检验证书域名,代码在客户端给出
https://www.cnblogs.com/littleatp/p/5878763.html
产生CA自签名证书
openssl.exe genrsa -out ca.key -des 2048
openssl.exe req -new -x509 -days 3650 -key ca.key -out ca.crt -subj “/C=US/ST=JS/L=NJ/O=wjr/OU=dev/CN=wjr.com”
openssl.exe x509 -in ca.crt -noout -text
//测试/C=US/ST=Mars/L=iTranswarp/O=iTranswarp/OU=iTranswarp/CN=wjr.com
产生server的证书过程
openssl.exe genrsa -out server.key 1024
openssl.exe req -new -key server.key -out server.csr -subj “/C=US/ST=JS/L=NJ/O=wjr/OU=dev/CN=wjr.com”
openssl x509 -req -days 3650 -in server.csr -CA ca.crt -CAkey ca.key -passin pass:123456 -CAcreateserial -out server.crt
openssl.exe x509 -in server.crt -noout -text
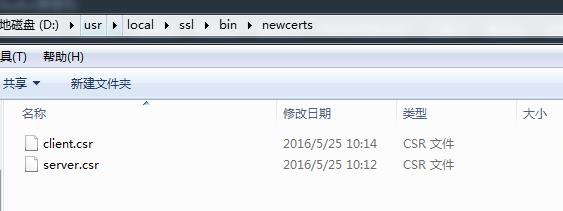
产生proxy的证书过程
openssl.exe genrsa -out private\\proxy.key 1024
openssl.exe req -new -key private\\proxy.key -out newcerts\\proxy.csr -config openssl.cnf
openssl.exe ca -in newcerts\\proxy.csr -cert private\\ca.crt -keyfile private\\ca.key -config openssl.cnf -policy policy_anything -out certs\\proxy.crt
openssl.exe x509 -in certs\\proxy.crt -noout -text
产生client的证书过程
openssl.exe genrsa -out private\\client.key 1024
openssl.exe req -new -key private\\client.key -out newcerts\\client.csr -config openssl.cnf
openssl.exe ca -in newcerts\\client.csr -cert private\\ca.crt -keyfile private\\ca.key -config openssl.cnf -policy policy_anything -out certs\\client.crt
openssl.exe x509 -in certs\\client.crt -noout -text
整个过程结束后
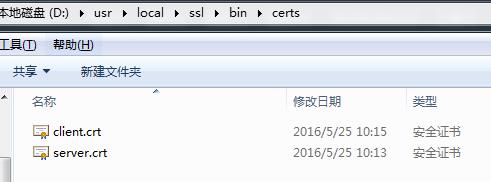
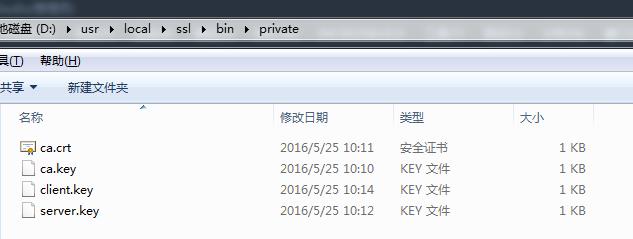
ca.crt为自签名证书;
server.crt,server.key为服务器端的证书和私钥文件;
proxy.crt,proxy.key为代理服务器端的证书和私钥文件;
client.crt,client.key为客户端的证书和私钥文件。
代码块
服务端测试代码,我做了点修改
//server
#include <winsock2.h>
#include <conio.h>
#include <stdio.h>
#include <winsock.h>
#include "openssl/x509.h"
#include "openssl/ssl.h"
#include "openssl/err.h"
#define MSGLENGTH 1024
#define PORT 8443
#define CACERT "ca.crt"
#define SVRCERTF "server.crt"
#define SVRKEYF "server.key"
int main()
{
WSADATA wsaData;
WSAStartup(MAKEWORD(2,2), &wsaData);
SOCKET sock;
SSL_METHOD *meth;
SSL_CTX* ctx;
SSL* ssl;
//SSL初始化
OpenSSL_add_ssl_algorithms();
//SSL错误信息初始化
SSL_load_error_strings();
//创建本次会话所使用的协议
meth = TLSv1_server_method();
//申请SSL会话的环境
ctx = SSL_CTX_new(meth);
if (NULL == ctx)
exit(1);
//设置会话的握手方式并加载CA证书
SSL_CTX_set_verify(ctx, SSL_VERIFY_PEER, NULL);
SSL_CTX_load_verify_locations(ctx, "D:\\\\usr\\\\local\\\\ssl\\\\bin\\\\private\\\\ca.crt", NULL);
//加载服务器端的证书
if (0 == SSL_CTX_use_certificate_file(ctx, "D:\\\\usr\\\\local\\\\ssl\\\\bin\\\\certs\\\\server.crt", SSL_FILETYPE_PEM))
{
ERR_print_errors_fp(stderr);
exit(1);
}
//加载服务器端的私钥
if (0 == SSL_CTX_use_PrivateKey_file(ctx, "D:\\\\usr\\\\local\\\\ssl\\\\bin\\\\private\\\\server.key", SSL_FILETYPE_PEM))
{
ERR_print_errors_fp(stderr);
exit(1);
}
//检查服务器端的证书和私钥是否匹配
if (!SSL_CTX_check_private_key(ctx)) {
printf("Private key does not match the certificate public key\\n");
exit(1);
}
//加密方式
SSL_CTX_set_cipher_list(ctx, "RC4-MD5");
//处理握手多次
SSL_CTX_set_mode(ctx, SSL_MODE_AUTO_RETRY);
/*以下是正常的TCP socket建立过程 .............................. */
printf("Begin tcp socket...\\n");
sock = socket(AF_INET, SOCK_STREAM, 0);
if (sock == INVALID_SOCKET) {
printf("SOCKET有问题. \\n");
return 0;
}
sockaddr_in addr;
memset(&addr, '\\0', sizeof(addr));
addr.sin_family = AF_INET;
addr.sin_port = htons(PORT); /* Server Port number */
addr.sin_addr.s_addr = INADDR_ANY;
//绑定sock
int nResult = bind(sock, (sockaddr *)&addr, sizeof(addr));
if (nResult == SOCKET_ERROR) {
printf("绑定SOCKET有问题. \\n");
return 0;
}
printf("服务器启动成功,端口:%d\\n正在等待连接\\n", PORT);
/*接受TCP链接*/
sockaddr_in sa_cli;
int err = listen(sock, 5);
if (-1 == err)
exit(1);
int client_len = sizeof(sa_cli);
int ss = accept(sock, (struct sockaddr *) &sa_cli, &client_len);
if (ss == -1) {
exit(1);
}
closesocket(sock);
printf("Connection from %d, port %d\\n", sa_cli.sin_addr.s_addr, sa_cli.sin_port);
/* TCP 链接已建立.开始 SSL 握手过程.......................... */
//绑定套接字
ssl = SSL_new(ctx);
if (NULL == ssl)
exit(1);
if (0 == SSL_set_fd(ssl, ss)) {
printf("Attach to Line fail!\\n");
exit(1);
}
//SSL握手
//SSL_accept(ssl);
int k = SSL_accept(ssl);
if (0 == k) {
printf("%d\\n", k);
printf("SSL connect fail!\\n");
exit(1);
}
//进行信息验证
X509 *client_cert;
client_cert = SSL_get_peer_certificate(ssl);
printf("发现客户端尝试连接\\n");
if (client_cert != NULL) {
printf ("Client certificate:\\n");
int rv = SSL_get_verify_result(ssl);
if (rv != X509_V_OK)
{
printf("认证出错!\\n");
exit(1);
}
//读取证书subject名并显示
char *str = X509_NAME_oneline(X509_get_subject_name(client_cert), 0, 0);
if (NULL == str) {
printf("认证出错!\\n");
exit(1);
}
printf("subject: %s\\n", str);
//读取证书的issuer名并显示
str = X509_NAME_oneline(X509_get_issuer_name(client_cert), 0, 0);
if (NULL == str) {
printf("证书名为空\\n");
exit(1);
}
printf("issuer: %s\\n", str);
printf("连接成功\\n");
X509_free (client_cert);/*如不再需要,需将证书释放 */
OPENSSL_free(str);
}
else {
printf("找不到客户端的认证证书\\n");
exit(1);
}
char buf[MSGLENGTH];
SSL_write(ssl, "Server is connect to you!\\n", strlen("Server is connect to you!\\n"));
printf("Listen to the client: \\n");
while (1) {
err = SSL_read(ssl, buf, sizeof(buf));
if(err == -1)
break;
buf[err] = '\\0';
printf("%s\\n", buf);
}
//关闭套接字
SSL_shutdown(ssl);
SSL_free(ssl);
SSL_CTX_free(ctx);
WSACleanup();
getch();
return 0;
}
客户端测试代码,我做了点修改
//client
#include <winsock2.h>
#include <conio.h>
#include <stdio.h>
#include "openssl/x509.h"
#include "openssl/ssl.h"
#include "openssl/err.h"
#include "openssl/rand.h"
#define PORT 8443
#define SERVER "127.0.0.1"
#define CACERT "D:\\\\usr\\\\local\\\\ssl\\\\bin\\\\private\\\\ca.crt"
#define MYCERTF "D:\\\\usr\\\\local\\\\ssl\\\\bin\\\\certs\\\\client.crt"
#define MYKEYF "D:\\\\usr\\\\local\\\\ssl\\\\bin\\\\private\\\\client.key"
#define MSGLENGTH 1024
int GetSrvCert(SSL * ssl, X509 ** pCert)
{
int rv = -1;
if (ssl == NULL)
{
return rv;
}
rv = SSL_get_verify_result(ssl);
*pCert = SSL_get_peer_certificate(ssl);
return rv;
}
//验证证书的合法性
int VerifyCert(X509 * pCert, const char * hostname)
{
char commonName[512] = { 0 };
X509_name_st * name = NULL;
if (pCert == NULL || hostname == NULL)
{
return -1;
}
//获取commonName
name = X509_get_subject_name(pCert);
X509_NAME_get_text_by_NID(name, NID_commonName, commonName, 512);
fprintf(stderr, "VerifyCert - Common Name on certificate: %s\\n", commonName);
if (strcmp(commonName, hostname) == 0)
{
printf("证书主机名%s\\n", commonName);
return 1;
}
else
{
return 0;
}
}
int main()
{
WSADATA wsadata;
WSAStartup(MAKEWORD(2, 2), &wsadata);
sockaddr_in sin;
int seed_int[100]; /*存放随机序列*/
SSL*ssl;
const SSL_METHOD *meth;
SSL_CTX *ctx;
//SSL初始化
OpenSSL_add_ssl_algorithms();
//SSL错误信息初始化
SSL_load_error_strings();
//创建本次会话所使用的协议
meth = TLSv1_client_method();
//申请SSL会话的环境
ctx = SSL_CTX_new(meth);
if (NULL == ctx)
exit(1);
SSL_CTX_set_default_passwd_cb(ctx, pem_password_cb1);
//SSL_CTX_set_default_passwd_cb_userdata(ctx, (void*)"555555");
//设置会话的握手方式并加载CA证书
SSL_CTX_set_verify(ctx, SSL_VERIFY_PEER, NULL);
SSL_CTX_load_verify_locations(ctx, CACERT, NULL);
//加载自己的证书
if (0 == SSL_CTX_use_certificate_file(ctx, MYCERTF, SSL_FILETYPE_PEM)) {
ERR_print_errors_fp(stderr);
exit(1);
}
//加载自己的私钥
if (0 == SSL_CTX_use_PrivateKey_file(ctx, MYKEYF, SSL_FILETYPE_PEM)) {
ERR_print_errors_fp(stderr);
exit(1);
}
//检查自己的证书和私钥是否匹配
if (!SSL_CTX_check_private_key(ctx)) {
printf("Private key does not match the certificate public key\\n");
exit(1);
}
/*构建随机数生成机制,WIN32平台必需*/
srand((unsigned)time(NULL));
for (int i = 0; i < 100; i++)
seed_int[i] = rand();
RAND_seed(seed_int, sizeof(seed_int));
//加密方式
SSL_CTX_set_cipher_list(ctx, "RC4-MD5");
//处理握手多次
SSL_CTX_set_mode(ctx, SSL_MODE_AUTO_RETRY);
/*以下是正常的TCP socket建立过程 .............................. */
SOCKET sock;
printf("Begin tcp socket...\\n");
sock = socket(AF_INET, SOCK_STREAM, 0);
if (sock == INVALID_SOCKET) {
printf("SOCKET有问题. \\n");
}
memset(&sin, '\\0', sizeof(sin));
sin.sin_family = AF_INET;
sin.sin_addr.s_addr = inet_addr(SERVER); /* Server IP */
sin.sin_port = htons(PORT); /* Server Port number */
int icnn = connect(sock, (sockaddr *)&sin, sizeof(sin));
if (icnn == SOCKET_ERROR) {
printf("连不上服务器\\n", GetLastError());
exit(1);
}
/* TCP 链接已建立.开始 SSL 握手过程.......................... */
//绑定套接字
ssl = SSL_new(ctx);
if (NULL == ssl)
exit(1);
if (0 >= SSL_set_fd(ssl, sock)) {
printf("Attach to Line fail!\\n");
exit(1);
}
//SSL握手
//SSL_connect(ssl);
int k = SSL_connect(ssl);
if (0 == k) {
printf("%d\\n", k);
printf("SSL connect fail!\\n");
exit(1);
}
printf("连接服务器成功\\n");
fprintf(stderr, "Retrieving peer certificate\\n");
//获取服务器证书
X509* pCert = NULL;
if (GetSrvCert(ssl, &pCert) != X509_V_OK)
{
if (SSL_get_verify_result(ssl) != X509_V_ERR_UNABLE_TO_GET_ISSUER_CERT_LOCALLY)
{
fprintf(stderr, "Certificate verification error: %i\\n", SSL_get_verify_result(ssl));
SSL_CTX_free(ctx);
return 0;
}
else
{
fprintf(stderr, "X509_V_ERR_UNABLE_TO_GET_ISSUER_CERT_LOCALLY\\n");
}
}
//校验服务器证书
fprintf(stderr, "Validating peer certificate\\n");
if (!VerifyCert(pCert, "127.0.0.1"))
{
fprintf(stderr, "Hostname and Common Name do not match\\n");
SSL_CTX_free(ctx);
return 0;
}
char sendmsg[MSGLENGTH] = "\\0";
char revmsg[MSGLENGTH] = "\\0";
int err = SSL_read(ssl, revmsg, sizeof(revmsg));
revmsg[err] = '\\0';
printf("%s\\n", revmsg);
while (1) {
printf("请输入所要发送的数据:\\n");
scanf("%s", sendmsg);
SSL_write(ssl, sendmsg, strlen(sendmsg));
printf("发送消息“ %s ”成功!\\n", sendmsg);
}
//关闭套接字
SSL_shutdown(ssl);
SSL_free(ssl);
SSL_CTX_free(ctx);
closesocket(sock);
WSACleanup();
return 0;
}
#系统内置证书问题
现在有个问题,当访问百度,支付宝,银联的时候,浏览器是内置证书,怎么获取批量获取这些证书呢?
在cmd中输入certmgr.msc
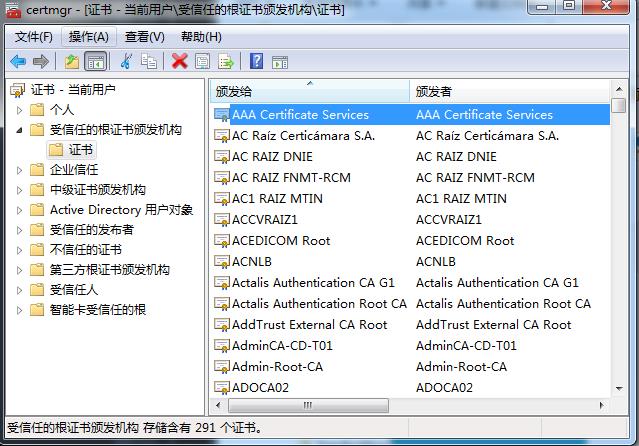
选择受信任的根证书颁发机构,全选,点邮件,所有任务,导出
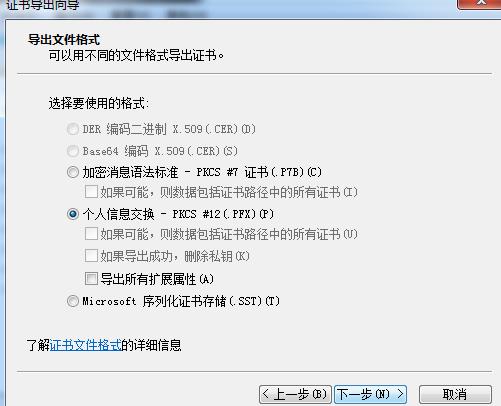
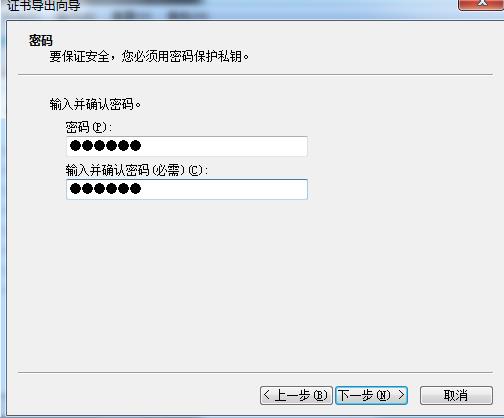
输入密码
就生成一个pfx文件,现在只要用openssl转成cer文件就可以了,命令
openssl pkcs12 -nodes -nokeys -in 11.pfx -out 1.cer -passin pass:123456
在程序中使用SSL_CTX_load_verify_locations 预先加载这个1.cer文件就可以了
#android BKS证书
Android加载bks格式证书,ios/Pc加载cer格式证书,一般而言,生成cer格式比较常见,因此需要进行cer转bks操作,操作步
以上是关于Openssl CA证书生成以及双向认证,及windows系统证书批量导出,android cer转bks的主要内容,如果未能解决你的问题,请参考以下文章