httpd服务之虚拟主机访问控制https配置
Posted
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了httpd服务之虚拟主机访问控制https配置相关的知识,希望对你有一定的参考价值。
实验要求:
建立httpd服务器,要求提供两个基于名称的虚拟主机:
(1)www.X.com,页面文件目录为/web/vhosts/x;错误日志为/var/log/httpd/x.err,访问日志为/var/log/httpd/x.access
(2)www.Y.com,页面文件目录为/web/vhosts/y;错误日志为/var/log/httpd/www2.err,访问日志为/var/log/httpd/y.access
(3)为两个虚拟主机建立各自的主页文件index.html,内容分别为其对应的主机名
(4)通过www.X.com/server-status输出httpd工作状态相关信息
2、为上面的第2个虚拟主机提供https服务,使得用户可以通过https安全的访问此web站点
(1)要求使用证书认证,证书中要求使用的国家(CN)、州(Beijing)、城市(Beijing)和组织(MageEdu)
(2)设置部门为Ops,主机名为www.Y.com,邮件为[email protected]
实验环境:
centos6
httpd2.2
httpd服务器---172.18.252.80
DNS服务器---172.18.253.55
根CA===172.18.252.36
实验前准备:
在各个主机上关闭防火墙、SELinux
vim /etc/selinux/config
修改
SELINUX=enforcing
改成
SELINUX=disabled
防火墙设置
iptables -F
httpd服务器(172.18.252.80)
安装httpd
[[email protected] httpd]# yuminstallhttpd -y
禁用默认的主机模式
[[email protected] ~]# vim /etc/httpd/conf/httpd.conf
注释下面这行内容
#DocumentRoot "/var/www/html"
为主机添加IP
[[email protected] ~]# ip addr show dev eth0 #查看原有ip
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdiscpfifo_fast state UP qlen 1000
link/ether00:0c:29:66:45:e9 brd ff:ff:ff:ff:ff:ff
inet 172.18.252.80/16brd 172.18.255.255 scope global eth0
inet6fe80::20c:29ff:fe66:45e9/64 scope link
valid_lft foreverpreferred_lft forever
[[email protected] ~]# ip addr add 172.18.252.90/16 dev eth0 #添加一个ip
[[email protected] ~]# ip addr show dev eth0 #查看添加后的IP信息,此时有2个IP地址了。 80,90
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdiscpfifo_fast state UP qlen 1000
link/ether00:0c:29:66:45:e9 brd ff:ff:ff:ff:ff:ff
inet 172.18.252.80/16brd 172.18.255.255 scope global eth0
inet 172.18.252.90/16scope global secondary eth0
inet6fe80::20c:29ff:fe66:45e9/64 scope link
valid_lft foreverpreferred_lft forever
添加虚拟主机配置文件
[[email protected] ~]# mkdir -p /web/vhosts/{x,y} #创建页面文件目录
[[email protected] ~]# echo "www.X.com">/web/vhosts/x/index.html #创建域名为www.X.com主页文件
[[email protected] ~]# echo "www.Y.com">/web/vhosts/y/index.html #创建域名为www.Y.com主页文件
[[email protected] ~]# touch/var/log/httpd/{x.err,x.access,www2.err,y.access} #创建日志文件
[[email protected] ~]# cd /etc/httpd/conf.d/ #进入配置目录
[[email protected] conf.d]# vim test.conf #创建一个配置文件,编辑内容如下
[[email protected] conf.d]# cat test.conf
namevirtualhost 172.18.252.80:80 namevirtualhost 172.18.252.90:80 <virtualhost 172.18.252.80:80> documentroot "/web/vhosts/x" servername "www.X.com" ErrorLog "/var/log/httpd/x.err" CustomLog "/var/log/httpd/x.access" common <Directory "/web/vhosts/x"> Options Indexes FollowSymLinks AllowOverride None Order allow,deny Allow from all </Directory> </VirtualHost>
<virtualhost 172.18.252.90:80> documentroot "/web/vhosts/y" servername "www.Y.com" # 主机名(域名) ErrorLog "/var/log/httpd/www2.err" CustomLog "/var/log/httpd/y.access" common <Directory "/web/vhosts/y"> Options Indexes FollowSymLinks AllowOverride None Order allow,deny Allow from all </Directory> </VirtualHost> |
实现status页面
在主配置文件/etc/httpd/conf/httpd.conf
取消注释
LoadModule status_module modules/mod_status.so
这项,加载此模块
添加如下内容
<Location /Server-status> SetHandler Server-status Order deny,allow Deny from all Allow from 172.18.252.80:80 </Location> |
[[email protected] conf.d]# httpd -t #检查语法
[[email protected] conf.d]# service httpd reload #重启服务
设置dns服务器地址
[[email protected] conf.d]# vim /etc/resolv.conf
nameserver 172.18.253.55
注:网卡eth0 配置文件中设置 PEERDNS=no
DNS服务器(172.18.253.55)
安装named服务
[[email protected] ~]# yum -y install bind
启动named服务
[[email protected] ~]# service named start
设置dns服务器地址
search X.com # 本机所在域dns服务器解析区域,包含X.com Y.com
search Y.com
nameserver 172.18.253.55 #本机ip为dns解析地址
注意:dns所在ip网卡配置文件设置PEERDNS=no
修改配置文件定义options
vim /etc/named.conf
options {*OPTIONS选项用来定义一些影响整个DNS服务器的环境
listen-on port 53 { any;}; ---any指监听本机的所有ip,端口为53
directory "/var/named"; 指定的域名解析文件的路径,如这里的是将其指定到/var/named 下
allow-query { any; }; ---允许所有主机查询本机的dns,也可以额指定某个ip
recursion yes; ---表示允许递归迭代,改为no就是不到根上去查找了
dnssec-enable no;
dnssec-validation no;
};
修改区域解析库的配置文件
vim /etc/named.rfc1912.zone或者
vim /etc/named.conf
[[email protected] ~]# cat /etc/named.rfc1912.zones
zone "X.com" IN { type master; file "X.com.zone"; };
zone "Y.com" IN { type master; file "Y.com.zone"; }; |
[[email protected] ~]# named-checkconf #检查语法错误
配置解析域文件
[[email protected] ~]# vim /var/named/Y.com.zone
[[email protected] ~]# cat /var/named/Y.com.zone
$TTL 1D @ IN SOA dns admin ( 2017092111 1D 1H 1W 3H) NS dns.Y.com. dns A 172.18.253.55 www A 172.18.252.90 |
[[email protected] ~]# vim /var/named/X.com.zone
[[email protected] ~]# cat /var/named/X.com.zone
$TTL 1D
@ IN SOA dns admin ( 2017092918 1D 1H 1W 3H) NS dns.X.com. dns A 172.18.253.55 www A 172.18.252.80 |
检查语法错误
[[email protected] ~]# named-checkzone "Y.com"/var/named/Y.com.zone
zone Y.com/IN: loaded serial 2017092111
OK
[[email protected] ~]# named-checkzone "X.com"/var/named/X.com.zone
zone X.com/IN: loaded serial 2017092918
OK
测试
[[email protected] ~]# elinks -source http://www.X.com
[[email protected] ~]# elinks -source http://www.Y.com
在httpd服务器(172.18.252.80)上查看日志
[[email protected] ~]# cat /var/log/httpd/x.access
172.18.252.90 - - [27/Sep/2017:01:42:36 +0800] "GET /HTTP/1.1" 200 10
172.18.253.55 - - [27/Sep/2017:01:45:25 +0800] "GET /HTTP/1.1" 200 10
CA根证书搭建(172.18.252.36)
安装openssl包
[[email protected] ~]# yum -y install openssl
生成证书索引文件,指定第一个颁发证书的序列号
[[email protected] ~]# touch /etc/pki/CA/index.txt
[[email protected] ~]# echo 01 >/etc/pki/CA/serial
[[email protected] ~]# cat /etc/pki/CA/serial
01
生成私钥
[[email protected] CA]# (umask 066;openssl genrsa -outprivate/cakey.pem 2048)
生成自签名证书
[[email protected] CA]# openssl req -new -x509 -key private/cakey.pem-out cacert.pem -days 7300
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:beijing
Locality Name (eg, city) [Default City]:beijing
Organization Name (eg, company) [Default Company Ltd]:magedu.com
查看证书信息
[[email protected] CA]# openssl x509 -in cacert.pem -noout -subject
subject= /C=CN/ST=beijing/L=beijing/O=magedu.com/OU=ops
httpd服务器(172.18.252.80)上为虚拟主机(172.18.252.90)www.Y.com配置支持https
安装httpd支持ssl模块
[[email protected] ~]#yum install mod_ssl -y
安装openssl包
[[email protected] ~]# yum install openssl
生成私钥
[[email protected] ~]# cd /etc/httpd/conf
[[email protected] conf]# mkdir ssl
[[email protected] conf]# cd ssl
[[email protected] ssl]# (umask 077;openssl genrsa -out httpd.key 1024)
生成证书申请
[[email protected] ssl]# openssl req -new -key httpd.key -out httpd.csr
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:beijing
Locality Name (eg, city) [Default City]:beijing
Organization Name (eg, company) [Default Company Ltd]:magedu.com
Organizational Unit Name (eg, section) []:opt
Common Name (eg, your name or your server‘s hostname) []:www.Y.com
Email Address []:[email protected]
向根CA证书(172.18.252.36)发起签证请求
[[email protected] ssl]# scp httpd.csr 172.18.252.36:/etc/pki/CA
在根CA所在主机上(172.18.252.36)完成签证
[[email protected] CA]# ls
cacert.pem certs crl httpd.csr index.txt newcerts private serial
[[email protected] CA]# openssl ca -in httpd.csr -out certs/httpd.crt-days 720
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
[[email protected] CA]# scp certs/httpd.crt172.18.252.80:/etc/httpd/conf/ssl
在httpd服务器(172.18.252.80)上
[[email protected] ssl]# ls
httpd.crt httpd.csr httpd.key #证书
修改httpd的ssl配置文件
vim /etc/httpd/conf.d/ssl.conf
DocumentRoot "/web/vhosts/y/"
ServerName www.Y.com
SSLCertificateFile /etc/httpd/conf/ssl/httpd.crt
SSLCertificateKeyFile /etc/httpd/conf/ssl/httpd.key
[[email protected] ssl]# httpd -t
Syntax OK
[[email protected] ssl]# service httpd restart
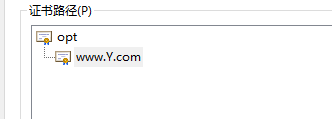
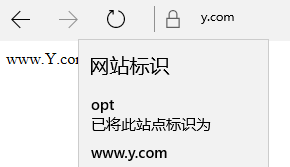
将ca证书导入到客户端可信任证书服务器,并验证
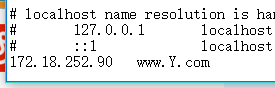
在windows的c:/windows/system32/drivers/etc/hosts文件中加入
测试
本文出自 “13147015” 博客,请务必保留此出处http://13157015.blog.51cto.com/13147015/1970049
以上是关于httpd服务之虚拟主机访问控制https配置的主要内容,如果未能解决你的问题,请参考以下文章