Tcpdump
Posted ethtool
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Tcpdump相关的知识,希望对你有一定的参考价值。
相比wireshark,tcpdump是基于命令行(无图形化界面)的抓包分析工具,并且是linux系统默认安装的。

root@kali:~# tcpdump -h tcpdump version 4.9.2 libpcap version 1.8.1 OpenSSL 1.1.1b 26 Feb 2019 Usage: tcpdump [-aAbdDefhHIJKlLnNOpqStuUvxX#] [ -B size ] [ -c count ] [ -C file_size ] [ -E algo:secret ] [ -F file ] [ -G seconds ] [ -i interface ] [ -j tstamptype ] [ -M secret ] [ --number ] [ -Q in|out|inout ] [ -r file ] [ -s snaplen ] [ --time-stamp-precision precision ] [ --immediate-mode ] [ -T type ] [ --version ] [ -V file ] [ -w file ] [ -W filecount ] [ -y datalinktype ] [ -z postrotate-command ] [ -Z user ] [ expression ]
1.抓包
#默认只抓68个字节(来源目的ip等简单包头);-s 0 就可以全抓
tcpdump -i eth0 -s 0 -w file.pcap tcpdump -i eth0 port 22
tcpdump -i eth0 tcp port 22
2.读包
tcpdump -r file.pcap
3.筛选
tcpdump -n -r http.cap | awk ‘{print $3}‘| sort –u //awk 取第N行; sort -u 取出不重复的 tcpdump -n src host 145.254.160.237 -r http.cap tcpdump -n dst host 145.254.160.237 -r http.cap tcpdump -n port 53 -r http.cap tcpdump -nX port 80 -r http.cap //X 以16进制的新式显示

root@kali:~# tcpdump -n -r file1 | awk ‘{print $3}‘| sort -u reading from file file1, link-type EN10MB (Ethernet) 192.168.56.134 192.168.56.134.39181 192.168.56.134.46488 192.168.56.1.63012 192.168.56.2.53 39.156.69.79 Reply Request root@kali:~# tcpdump -n src host 192.168.56.134 -r file1 reading from file file1, link-type EN10MB (Ethernet) 02:38:09.331046 IP 192.168.56.134.39181 > 192.168.56.2.53: 6241+ A? baidu.com. (27) 02:38:09.331254 IP 192.168.56.134.39181 > 192.168.56.2.53: 44146+ AAAA? baidu.com. (27) 02:38:09.362449 IP 192.168.56.134 > 39.156.69.79: ICMP echo request, id 5416, seq 1, length 64 02:38:09.376782 IP 192.168.56.134.46488 > 192.168.56.2.53: 20304+ PTR? 79.69.156.39.in-addr.arpa. (43) 02:38:14.379995 IP 192.168.56.134.46488 > 192.168.56.2.53: 20304+ PTR? 79.69.156.39.in-addr.arpa. (43) 02:38:14.499939 ARP, Request who-has 192.168.56.2 tell 192.168.56.134, length 28 02:38:14.776485 IP 192.168.56.134 > 39.156.69.79: ICMP echo request, id 5416, seq 2, length 64 02:38:15.778747 IP 192.168.56.134 > 39.156.69.79: ICMP echo request, id 5416, seq 3, length 64 02:38:16.729831 IP 192.168.56.134 > 192.168.56.2: ICMP 192.168.56.134 udp port 46488 unreachable, length 167 02:38:16.781104 IP 192.168.56.134 > 39.156.69.79: ICMP echo request, id 5416, seq 4, length 64 02:38:17.783008 IP 192.168.56.134 > 39.156.69.79: ICMP echo request, id 5416, seq 5, length 64 root@kali:~# tcpdump -n dst host 192.168.56.134 -r file1 reading from file file1, link-type EN10MB (Ethernet) 02:38:09.346873 IP 192.168.56.2.53 > 192.168.56.134.39181: 6241 2/0/0 A 39.156.69.79, A 220.181.38.148 (59) 02:38:09.346951 IP 192.168.56.2.53 > 192.168.56.134.39181: 44146 0/1/0 (70) 02:38:09.375634 IP 39.156.69.79 > 192.168.56.134: ICMP echo reply, id 5416, seq 1, length 64 02:38:14.500212 ARP, Reply 192.168.56.2 is-at 00:50:56:f1:b5:70, length 46 02:38:14.775958 IP 192.168.56.2.53 > 192.168.56.134.46488: 20304 0/0/0 (43) 02:38:14.815867 IP 39.156.69.79 > 192.168.56.134: ICMP echo reply, id 5416, seq 2, length 64 02:38:15.788414 IP 39.156.69.79 > 192.168.56.134: ICMP echo reply, id 5416, seq 3, length 64 02:38:16.729748 IP 192.168.56.2.53 > 192.168.56.134.46488: 20304 NXDomain 0/1/0 (131) 02:38:16.793435 IP 39.156.69.79 > 192.168.56.134: ICMP echo reply, id 5416, seq 4, length 64 02:38:17.793048 IP 39.156.69.79 > 192.168.56.134: ICMP echo reply, id 5416, seq 5, length 64 root@kali:~# tcpdump -n port 53 -r file1 reading from file file1, link-type EN10MB (Ethernet) 02:38:09.331046 IP 192.168.56.134.39181 > 192.168.56.2.53: 6241+ A? baidu.com. (27) 02:38:09.331254 IP 192.168.56.134.39181 > 192.168.56.2.53: 44146+ AAAA? baidu.com. (27) 02:38:09.346873 IP 192.168.56.2.53 > 192.168.56.134.39181: 6241 2/0/0 A 39.156.69.79, A 220.181.38.148 (59) 02:38:09.346951 IP 192.168.56.2.53 > 192.168.56.134.39181: 44146 0/1/0 (70) 02:38:09.376782 IP 192.168.56.134.46488 > 192.168.56.2.53: 20304+ PTR? 79.69.156.39.in-addr.arpa. (43) 02:38:14.379995 IP 192.168.56.134.46488 > 192.168.56.2.53: 20304+ PTR? 79.69.156.39.in-addr.arpa. (43) 02:38:14.775958 IP 192.168.56.2.53 > 192.168.56.134.46488: 20304 0/0/0 (43) 02:38:16.729748 IP 192.168.56.2.53 > 192.168.56.134.46488: 20304 NXDomain 0/1/0 (131) root@kali:~# tcpdump -nX port 53 -r file1 reading from file file1, link-type EN10MB (Ethernet) 02:38:09.331046 IP 192.168.56.134.39181 > 192.168.56.2.53: 6241+ A? baidu.com. (27) 0x0000: 4500 0037 563e 4000 4011 f29e c0a8 3886 E..7V>@.@.....8. 0x0010: c0a8 3802 990d 0035 0023 f20d 1861 0100 ..8....5.#...a.. 0x0020: 0001 0000 0000 0000 0562 6169 6475 0363 .........baidu.c 0x0030: 6f6d 0000 0100 01 om..... 02:38:09.331254 IP 192.168.56.134.39181 > 192.168.56.2.53: 44146+ AAAA? baidu.com. (27) 0x0000: 4500 0037 563f 4000 4011 f29d c0a8 3886 E..7V?@.@.....8. 0x0010: c0a8 3802 990d 0035 0023 f20d ac72 0100 ..8....5.#...r.. 0x0020: 0001 0000 0000 0000 0562 6169 6475 0363 .........baidu.c 0x0030: 6f6d 0000 1c00 01 om..... 02:38:09.346873 IP 192.168.56.2.53 > 192.168.56.134.39181: 6241 2/0/0 A 39.156.69.79, A 220.181.38.148 (59) 0x0000: 4500 0057 1b00 0000 8011 2dbd c0a8 3802 E..W......-...8. 0x0010: c0a8 3886 0035 990d 0043 3566 1861 8180 ..8..5...C5f.a.. 0x0020: 0001 0002 0000 0000 0562 6169 6475 0363 .........baidu.c 0x0030: 6f6d 0000 0100 01c0 0c00 0100 0100 0000 om.............. 0x0040: 0500 0427 9c45 4fc0 0c00 0100 0100 0000 ...‘.EO......... 0x0050: 0500 04dc b526 94 .....&. 02:38:09.346951 IP 192.168.56.2.53 > 192.168.56.134.39181: 44146 0/1/0 (70) 0x0000: 4500 0062 1b01 0000 8011 2db1 c0a8 3802 E..b......-...8. 0x0010: c0a8 3886 0035 990d 004e 9e44 ac72 8180 ..8..5...N.D.r.. 0x0020: 0001 0000 0001 0000 0562 6169 6475 0363 .........baidu.c 0x0030: 6f6d 0000 1c00 01c0 0c00 0600 0100 0000 om.............. 0x0040: 0500 1f03 646e 73c0 0c02 7361 c00c 77ee ....dns...sa..w. 0x0050: d9fa 0000 012c 0000 012c 0027 8d00 0000 .....,...,.‘.... 0x0060: 1c20 .. 02:38:09.376782 IP 192.168.56.134.46488 > 192.168.56.2.53: 20304+ PTR? 79.69.156.39.in-addr.arpa. (43) 0x0000: 4500 0047 5646 4000 4011 f286 c0a8 3886 E..GVF@.@.....8. 0x0010: c0a8 3802 b598 0035 0033 f21d 4f50 0100 ..8....5.3..OP.. 0x0020: 0001 0000 0000 0000 0237 3902 3639 0331 .........79.69.1 0x0030: 3536 0233 3907 696e 2d61 6464 7204 6172 56.39.in-addr.ar 0x0040: 7061 0000 0c00 01 pa..... 02:38:14.379995 IP 192.168.56.134.46488 > 192.168.56.2.53: 20304+ PTR? 79.69.156.39.in-addr.arpa. (43) 0x0000: 4500 0047 5a58 4000 4011 ee74 c0a8 3886 E..GZX@.@..t..8. 0x0010: c0a8 3802 b598 0035 0033 f21d 4f50 0100 ..8....5.3..OP.. 0x0020: 0001 0000 0000 0000 0237 3902 3639 0331 .........79.69.1 0x0030: 3536 0233 3907 696e 2d61 6464 7204 6172 56.39.in-addr.ar 0x0040: 7061 0000 0c00 01 pa..... 02:38:14.775958 IP 192.168.56.2.53 > 192.168.56.134.46488: 20304 0/0/0 (43) 0x0000: 4500 0047 1b03 0000 8011 2dca c0a8 3802 E..G......-...8. 0x0010: c0a8 3886 0035 b598 0033 55ef 4f50 8180 ..8..5...3U.OP.. 0x0020: 0001 0000 0000 0000 0237 3902 3639 0331 .........79.69.1 0x0030: 3536 0233 3907 696e 2d61 6464 7204 6172 56.39.in-addr.ar 0x0040: 7061 0000 0c00 01 pa..... 02:38:16.729748 IP 192.168.56.2.53 > 192.168.56.134.46488: 20304 NXDomain 0/1/0 (131) 0x0000: 4500 009f 1b06 0000 8011 2d6f c0a8 3802 E.........-o..8. 0x0010: c0a8 3886 0035 b598 008b 1572 4f50 8183 ..8..5.....rOP.. 0x0020: 0001 0000 0001 0000 0237 3902 3639 0331 .........79.69.1 0x0030: 3536 0233 3907 696e 2d61 6464 7204 6172 56.39.in-addr.ar 0x0040: 7061 0000 0c00 01c0 1600 0600 0100 0000 pa.............. 0x0050: 0500 4c02 6e73 0561 706e 6963 036e 6574 ..L.ns.apnic.net 0x0060: 0027 7265 6164 2d74 7874 2d72 6563 6f72 .‘read-txt-recor 0x0070: 642d 6f66 2d7a 6f6e 652d 6669 7273 742d d-of-zone-first- 0x0080: 646e 732d 6164 6d69 6ec0 3a00 0012 6b00 dns-admin.:...k. 0x0090: 001c 2000 0007 0800 093a 8000 000e 10 .........:..... root@kali:~#
高级筛选:
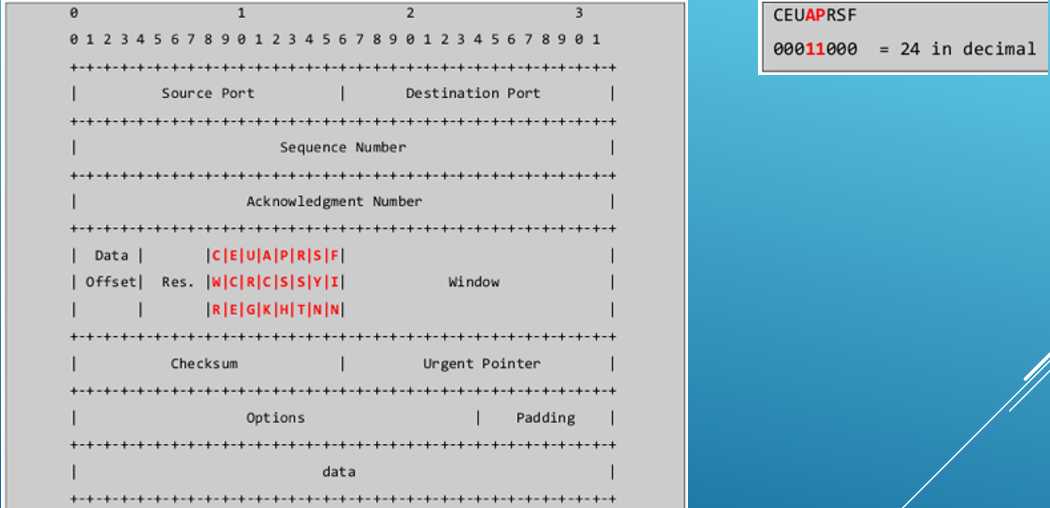
凡是第十四个字节是psh+ack就筛选,可得tcp数据流:
tcpdump -A -n ‘tcp[13] = 24‘ -r http.cap
ethtool
以上是关于Tcpdump的主要内容,如果未能解决你的问题,请参考以下文章
