Docke官方提供了Docker Hub网站来作为一个公开的集中仓库。然而,本地访问Docker Hub速度往往很慢,并且很多时候我们需要一个本地的私有仓库只供网内使用。
Docker仓库实际上提供两方面的功能,一个是镜像管理,一个是认证。前者主要由docker-registry项目来实现,通过http服务来上传下载;后者可以通过docker-index(闭源)项目或者利用现成认证方案(如nginx)实现http请求管理。
系统环境:CentOS 7.2
主机IP:192.168.116.148
1、安装docker-registry
1 | docker run -d -p 5000:5000 --restart=always --name registry -v /opt/registry:/var/lib/registry registry:2 |
2、上传镜像
查看系统已有的镜像:
1 2 3 4 | # docker imagesREPOSITORY TAG IMAGE ID CREATED SIZEcentos latest 8140d0c64310 7 days ago 193MBregistry 2 9d0c4eabab4d 8 days ago 33.2MB |
使用docker tag将centos镜像打个标记
1 | # docker tag centos 192.168.116.148:5000/centos |
1 | # docker push 192.168.116.148:5000/centos |
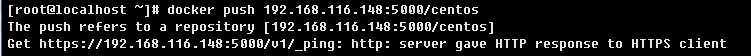
在/etc/docker/目录下,创建daemon.json文件。在文件中写入:
1 | { "insecure-registries":["192.168.116.148:5000"] } |
1 | # systemctl restart docker |
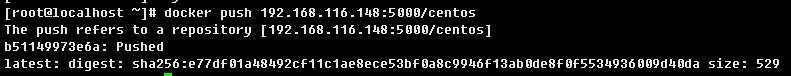
重新上传:
接下来开始配置https
3、配置SSL证书及nginx反向代理docker registry
搭建私有CA,初始化CA环境,在/etc/pki/CA/下建立证书索引数据库文件index.txt和序列号文件serial,并为证书序列号文件提供初始值。
1 2 | # touch /etc/pki/CA/{index.txt,serial}# echo 01 > /etc/pki/CA/serial |
生成密钥并保存到/etc/pki/CA/private/cakey.pem
1 | # (umask 077;openssl genrsa -out /etc/pki/CA/private/cakey.pem 2048) |
生成根证书
1 | # openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -out /etc/pki/CA/cacert.pem -days 3650 |
需要填写的信息:
1 2 3 4 5 6 7 | Country Name (2 letter code) [XX]:CNState or Province Name (full name) []:ChinaLocality Name (eg, city) [Default City]:BeijingOrganization Name (eg, company) [Default Company Ltd]:wtsOrganizational Unit Name (eg, section) []:sysopsCommon Name (eg, your name or your server‘s hostname) []:hub.wts.comEmail Address []:[email protected] |
使系统信任根证书
1 | # cat /etc/pki/CA/cacert.pem >> /etc/pki/tls/certs/ca-bundle.crt |
1 | # mkdir /app/nginx/conf/ssl |
创建密钥文件和证书申请文件
1 2 | # (umask 077;openssl genrsa -out /app/nginx/conf/ssl/docker.key 2048)# openssl req -new -key /app/nginx/conf/ssl/docker.key -out /app/nginx/conf/ssl/docker.csr |
填写的申请信息前四项要和私有CA的信息一致
1 2 3 4 5 6 7 8 9 10 11 12 | Country Name (2 letter code) [XX]:CNState or Province Name (full name) []:ChinaLocality Name (eg, city) [Default City]:BeijingOrganization Name (eg, company) [Default Company Ltd]:wtsOrganizational Unit Name (eg, section) []:sysopsCommon Name (eg, your name or your server‘s hostname) []:hub.wts.comEmail Address []:[email protected]Please enter the following ‘extra‘ attributesto be sent with your certificate requestA challenge password []: #直接回车An optional company name []: #直接回车 |
签署,证书
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 | # openssl ca -in /app/nginx/conf/ssl/docker.csr -out /app/nginx/conf/ssl/docker.crt -days 3650Using configuration from /etc/pki/tls/openssl.cnfCheck that the request matches the signatureSignature okCertificate Details: Serial Number: 1 (0x1) Validity Not Before: May 19 19:03:55 2017 GMT Not After : May 17 19:03:55 2027 GMT Subject: countryName = CN stateOrProvinceName = Beijing organizationName = wts organizationalUnitName = sysops commonName = hub.wts.com emailAddress = [email protected] X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 69:F0:D7:BF:B2:CE:6D:53:AA:1A:CD:E8:73:47:A7:9F:30:EA:17:F7 X509v3 Authority Key Identifier: keyid:AF:E5:48:44:A3:18:59:38:D5:17:07:1B:1D:6F:32:F4:EC:1E:E0:E2Certificate is to be certified until May 17 19:03:55 2027 GMT (3650 days)Sign the certificate? [y/n]:y1 out of 1 certificate requests certified, commit? [y/n]yWrite out database with 1 new entriesData Base Updated |
配置nginx反向代理docker registry
添加认证
1 2 | # yum -y install httpd-tools# htpasswd -cb /app/nginx/conf/docker-registry.htpasswd admin admin |
nginx相关配置:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 | upstream docker-registry { server 127.0.0.1:5000; } server { listen 443; server_name localhost; #charset koi8-r; #access_log logs/host.access.log main; ssl on; ssl_certificate /app/nginx/conf/ssl/docker.crt; ssl_certificate_key /app/nginx/conf/ssl/docker.key; client_max_body_size 0; chunked_transfer_encoding on; proxy_set_header Host $host; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; add_header ‘Docker-Distribution-Api-Version‘ ‘registry/2.0‘ always; location / { auth_basic "Docker registry"; auth_basic_user_file /app/nginx/conf/docker-registry.htpasswd; proxy_pass http://docker-registry; } location /_ping{ auth_basic off; proxy_pass http://docker-registry; } location /v2/_ping{ auth_basic off; proxy_pass http://docker-registry; }} |
重启nginx
1 | # /app/nginx/sbin/nginx -s reload |
1 2 3 | # cat >>/etc/hosts <<EOF192.168.116.148 hub.wts.comEOF |
1 2 | # systemctl daemon-reload# systemctl restart docker |
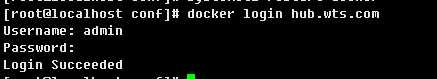
登录
上传镜像
1 2 3 | # docker pull nginx# docker tag nginx 192.168.116.148:5000/nginx# docker push 192.168.116.148:5000/nginx |
查看
1 2 | # curl --user admin:admin https://hub.wts.com/v2/_catalog{"repositories":["centos","nginx"]} |
局域网内其他机器认证(192.168.116.147 系统版本:CentOS6.5)
1 2 3 | # cat >>/etc/hosts <<EOF192.168.116.148 hub.wts.comEOF |
把CA的密钥发送到客户机,并添加到ca-bundle.crt
1 2 3 | # scp -p /etc/pki/tls/certs/ca-bundle.crt [email protected]:/etc/pki/tls/certs/ca-bundle.crt# scp -p /etc/pki/CA/cacert.pem [email protected]:/etc/pki/CA/cacert.pem# cat /etc/pki/CA/cacert.pem >> /etc/pki/tls/certs/ca-bundle.crt |
1 | # /etc/init.d/docker restart |
登录
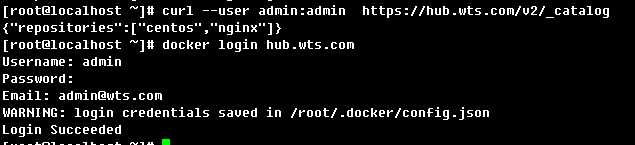
下载镜像

至此,私服基本上可以使用了。