IPSEC over GRE
Posted 害怕网络暴力
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了IPSEC over GRE相关的知识,希望对你有一定的参考价值。
顾名思义,就是对数据包先进行ipsec的封装,然后再外面加上一层GRE的封装,但是这种封装方式缺点很多,ipsec无法支持组播,所以tunnel口的两端不能运行关于组播的一些路由协议,比如ospf,如果运行,那么私网数据在公网上依然能被看到,那么vpn就没意义了。华三的官方配置手册上面也说了这种方式不能充分利用二者的优势,一般不推荐使用,但是它可以不好,我们不能不会。
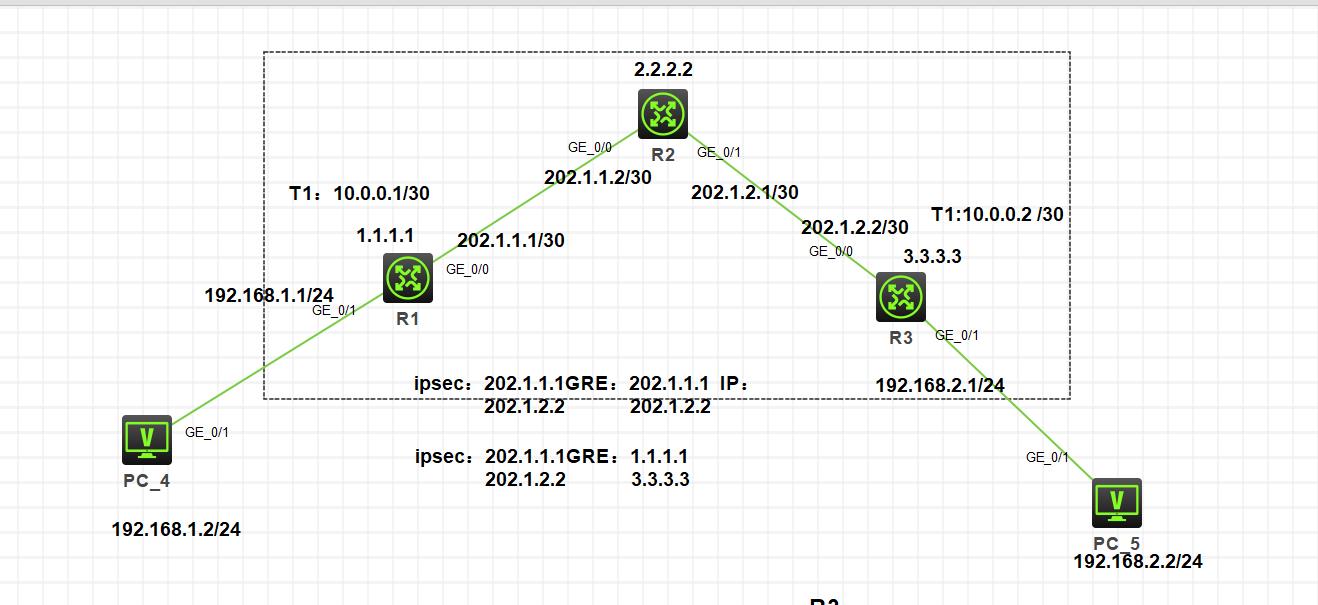
实验组网
需求:
三台路由器模拟公网,公网运行ospf保证两端公网可达,在R1和R3上运行ipsec over gre保证两端私网可达。
地址配置和ospf不做过多赘述
R1:配置gre
[H3C]interface Tunnel1 mode gre
[H3C-Tunnel1]ip address 10.0.0.1 255.255.255.252
[H3C-Tunnel1]source 202.1.1.1
[H3C-Tunnel1]destination 202.1.2.2
R3:配置gre
[H3C]interface Tunnel1 mode gre
[H3C-Tunnel1]ip address 10.0.0.2 255.255.255.252
[H3C-Tunnel1]source 202.1.2.2
[H3C-Tunnel1]destination 202.1.1.1
引流
R1
[H3C]ip route-static 192.168.2.0 24 Tunnel 1
R3
[H3C]ip route-static 192.168.1.0 24 Tunnel 1
这时候两端私网已经通了,但是只是一个gre的隧道
这时通过抓包可以很明显的发现私网数据包被gre进行封装了

配置ipsec感兴趣流
R1
[H3C-acl-ipv4-adv-3000] rule 0 permit ip source 192.168.1.2 0 destination 192.16
8.2.2 0
R3
[H3C-acl-ipv4-adv-3000] rule 0 permit ip source 192.168.2.2 0 destination 192.16
8.1.2 0
配置ike和ipsec
R1
[H3C]ike keychain 1
[H3C-ike-keychain-1] pre-shared-key address 10.0.0.2 255.255.255.255 key simple
123
[H3C-ike-keychain-1]qu
[H3C]ike proposal 1
[H3C-ike-proposal-1]qu
[H3C]ike profile 1
[H3C-ike-profile-1] keychain 1
[H3C-ike-profile-1] local-identity address 10.0.0.1
[H3C-ike-profile-1] match remote identity address 10.0.0.2 255.255.255.255
[H3C-ike-profile-1] proposal 1
[H3C-ike-profile-1]qu
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1] esp encryption-algorithm des-cbc
[H3C-ipsec-transform-set-1] esp authentication-algorithm md5
[H3C-ipsec-transform-set-1]qu
[H3C]ipsec policy zx 1 isakmp
[H3C-ipsec-policy-isakmp-zx-1] transform-set 1
[H3C-ipsec-policy-isakmp-zx-1] security acl 3000
[H3C-ipsec-policy-isakmp-zx-1] remote-address 10.0.0.2
[H3C-ipsec-policy-isakmp-zx-1] ike-profile 1
[H3C-ipsec-policy-isakmp-zx-1]qu
R3
[H3C]ike keychain 1
[H3C-ike-keychain-1]pre-shared-key address 10.0.0.1 255.255.255.255 key simple 1
23
[H3C-ike-keychain-1]qu
[H3C]ike profile 1
[H3C-ike-profile-1]keychain 1
[H3C-ike-profile-1]local-identity address 10.0.0.2
[H3C-ike-profile-1]match remote identity address 10.0.0.1 255.255.255.255
[H3C-ike-profile-1]proposal 1
[H3C-ike-profile-1]qu
[H3C]ike proposal 1
[H3C-ike-proposal-1]qu
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1]esp encryption-algorithm des-cbc
[H3C-ipsec-transform-set-1]esp authentication-algorithm md5
[H3C-ipsec-transform-set-1]qu
[H3C]ipsec policy zx 1 isakmp
[H3C-ipsec-policy-isakmp-zx-1]transform-set 1
[H3C-ipsec-policy-isakmp-zx-1]security acl 3000
[H3C-ipsec-policy-isakmp-zx-1]remote-address 10.0.0.1 #这个一定要配 不然ike起不来
[H3C-ipsec-policy-isakmp-zx-1]ike-profile 1
[H3C-ipsec-policy-isakmp-zx-1]qu
这里需要注意ipsec策略的应用接口,私网数据到达出口设备上会查找路由表,发现去往对端私网要走tunnel 1接口,那么数据到达tunnel口里面就会进行gre的封装,但是我们的需求是先封装ipsec,ipsec是应用在哪个接口,就会使用哪个接口的ip,所以这里把ipsec应用在tunnel口里面,让数据包先去出发ipsec,进行ipsec封装,在匹配直连路由到达对面,为什么匹配直连,因为ipsec使用tunnel口ip进行封装,tunnel口的ip和对端就相当于直连!
R1 R3
[H3C]interface Tunnel 1
[H3C-Tunnel1]ipsec apply policy zx
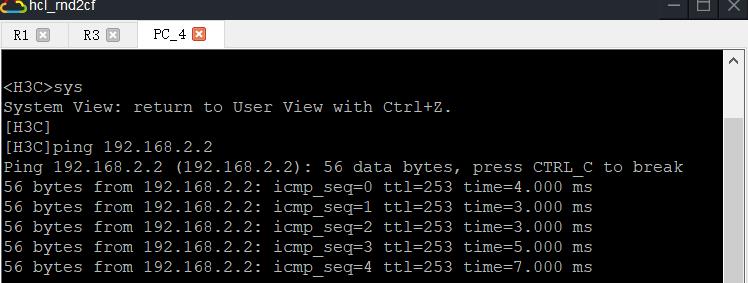
这时随便哪端先触发,都会先进行ipsec封装,在进行gre的封装
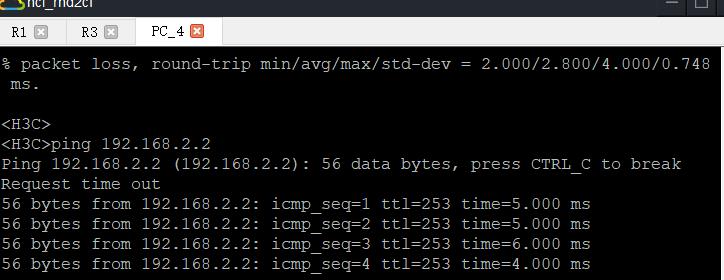
抓包看一下封装,这时再去ping就不能看icmp包了,因为内层的数据包头和icmp协议已经被ipsec加密了,可以过滤只看gre,或者esp协议!

可以看到依然有两个ip头部,但是内层的却是gre隧道的ip地址,也就是ipsec的封装,并不是发起连接的内网地址,外层依旧是gre头部,使用公网进行封装!
以上是关于IPSEC over GRE的主要内容,如果未能解决你的问题,请参考以下文章