80分求DES加密解密算法实现的PHP源代码
Posted
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了80分求DES加密解密算法实现的PHP源代码相关的知识,希望对你有一定的参考价值。
运行以下php文件
<?php
function idtag_des_decode($key,$encrypted)
$encrypted = base64_decode($encrypted);
$td = mcrypt_module_open(MCRYPT_DES,'',MCRYPT_MODE_CBC,''); //使用MCRYPT_DES算法,cbc模式
$iv = mcrypt_create_iv(mcrypt_enc_get_iv_size($td), MCRYPT_RAND);
$ks = mcrypt_enc_get_key_size($td);
mcrypt_generic_init($td, $key, $key); //初始处理
$decrypted = mdecrypt_generic($td, $encrypted); //解密
mcrypt_generic_deinit($td); //结束
mcrypt_module_close($td);
$y=pkcs5_unpad($decrypted);
return $y;
function idtag_des_encode($key,$text)
$y=pkcs5_pad($text);
$td = mcrypt_module_open(MCRYPT_DES,'',MCRYPT_MODE_CBC,''); //使用MCRYPT_DES算法,cbc模式
/// $iv = mcrypt_create_iv(mcrypt_enc_get_iv_size($td), MCRYPT_RAND);
$ks = mcrypt_enc_get_key_size($td);
mcrypt_generic_init($td, $key, $key); //初始处理
$encrypted = mcrypt_generic($td, $y); //解密
mcrypt_generic_deinit($td); //结束
mcrypt_module_close($td);
return base64_encode($encrypted);
function pkcs5_pad($text,$block=8)
$pad = $block - (strlen($text) % $block);
return $text . str_repeat(chr($pad), $pad);
function pkcs5_unpad($text)
$pad = ord($textstrlen($text)-1);
if ($pad > strlen($text)) return $text;
if (strspn($text, chr($pad), strlen($text) - $pad) != $pad) return $text;
return substr($text, 0, -1 * $pad);
$key = '12345678';
$str = 'str';
echo "encode:".idtag_des_encode($key,$str);
?>
打印出的结果是:encode:fwSjSc4VKyQ=
现在求一个不依赖于mcrypt扩展库的DES算法实现PHP源代码。如果答案满意,追加30分。
<?php
function des ($key, $message, $encrypt, $mode, $iv, $padding)
$message0 = $message;
//declaring this locally speeds things up a bit
$spfunction1 = array (0x1010400,0,0x10000,0x1010404,0x1010004,0x10404,0x4,0x10000,0x400,0x1010400,0x1010404,0x400,0x1000404,0x1010004,0x1000000,0x4,0x404,0x1000400,0x1000400,0x10400,0x10400,0x1010000,0x1010000,0x1000404,0x10004,0x1000004,0x1000004,0x10004,0,0x404,0x10404,0x1000000,0x10000,0x1010404,0x4,0x1010000,0x1010400,0x1000000,0x1000000,0x400,0x1010004,0x10000,0x10400,0x1000004,0x400,0x4,0x1000404,0x10404,0x1010404,0x10004,0x1010000,0x1000404,0x1000004,0x404,0x10404,0x1010400,0x404,0x1000400,0x1000400,0,0x10004,0x10400,0,0x1010004);
$spfunction2 = array (-0x7fef7fe0,-0x7fff8000,0x8000,0x108020,0x100000,0x20,-0x7fefffe0,-0x7fff7fe0,-0x7fffffe0,-0x7fef7fe0,-0x7fef8000,-0x80000000,-0x7fff8000,0x100000,0x20,-0x7fefffe0,0x108000,0x100020,-0x7fff7fe0,0,-0x80000000,0x8000,0x108020,-0x7ff00000,0x100020,-0x7fffffe0,0,0x108000,0x8020,-0x7fef8000,-0x7ff00000,0x8020,0,0x108020,-0x7fefffe0,0x100000,-0x7fff7fe0,-0x7ff00000,-0x7fef8000,0x8000,-0x7ff00000,-0x7fff8000,0x20,-0x7fef7fe0,0x108020,0x20,0x8000,-0x80000000,0x8020,-0x7fef8000,0x100000,-0x7fffffe0,0x100020,-0x7fff7fe0,-0x7fffffe0,0x100020,0x108000,0,-0x7fff8000,0x8020,-0x80000000,-0x7fefffe0,-0x7fef7fe0,0x108000);
$spfunction3 = array (0x208,0x8020200,0,0x8020008,0x8000200,0,0x20208,0x8000200,0x20008,0x8000008,0x8000008,0x20000,0x8020208,0x20008,0x8020000,0x208,0x8000000,0x8,0x8020200,0x200,0x20200,0x8020000,0x8020008,0x20208,0x8000208,0x20200,0x20000,0x8000208,0x8,0x8020208,0x200,0x8000000,0x8020200,0x8000000,0x20008,0x208,0x20000,0x8020200,0x8000200,0,0x200,0x20008,0x8020208,0x8000200,0x8000008,0x200,0,0x8020008,0x8000208,0x20000,0x8000000,0x8020208,0x8,0x20208,0x20200,0x8000008,0x8020000,0x8000208,0x208,0x8020000,0x20208,0x8,0x8020008,0x20200);
$spfunction4 = array (0x802001,0x2081,0x2081,0x80,0x802080,0x800081,0x800001,0x2001,0,0x802000,0x802000,0x802081,0x81,0,0x800080,0x800001,0x1,0x2000,0x800000,0x802001,0x80,0x800000,0x2001,0x2080,0x800081,0x1,0x2080,0x800080,0x2000,0x802080,0x802081,0x81,0x800080,0x800001,0x802000,0x802081,0x81,0,0,0x802000,0x2080,0x800080,0x800081,0x1,0x802001,0x2081,0x2081,0x80,0x802081,0x81,0x1,0x2000,0x800001,0x2001,0x802080,0x800081,0x2001,0x2080,0x800000,0x802001,0x80,0x800000,0x2000,0x802080);
$spfunction5 = array (0x100,0x2080100,0x2080000,0x42000100,0x80000,0x100,0x40000000,0x2080000,0x40080100,0x80000,0x2000100,0x40080100,0x42000100,0x42080000,0x80100,0x40000000,0x2000000,0x40080000,0x40080000,0,0x40000100,0x42080100,0x42080100,0x2000100,0x42080000,0x40000100,0,0x42000000,0x2080100,0x2000000,0x42000000,0x80100,0x80000,0x42000100,0x100,0x2000000,0x40000000,0x2080000,0x42000100,0x40080100,0x2000100,0x40000000,0x42080000,0x2080100,0x40080100,0x100,0x2000000,0x42080000,0x42080100,0x80100,0x42000000,0x42080100,0x2080000,0,0x40080000,0x42000000,0x80100,0x2000100,0x40000100,0x80000,0,0x40080000,0x2080100,0x40000100);
$spfunction6 = array (0x20000010,0x20400000,0x4000,0x20404010,0x20400000,0x10,0x20404010,0x400000,0x20004000,0x404010,0x400000,0x20000010,0x400010,0x20004000,0x20000000,0x4010,0,0x400010,0x20004010,0x4000,0x404000,0x20004010,0x10,0x20400010,0x20400010,0,0x404010,0x20404000,0x4010,0x404000,0x20404000,0x20000000,0x20004000,0x10,0x20400010,0x404000,0x20404010,0x400000,0x4010,0x20000010,0x400000,0x20004000,0x20000000,0x4010,0x20000010,0x20404010,0x404000,0x20400000,0x404010,0x20404000,0,0x20400010,0x10,0x4000,0x20400000,0x404010,0x4000,0x400010,0x20004010,0,0x20404000,0x20000000,0x400010,0x20004010);
$spfunction7 = array (0x200000,0x4200002,0x4000802,0,0x800,0x4000802,0x200802,0x4200800,0x4200802,0x200000,0,0x4000002,0x2,0x4000000,0x4200002,0x802,0x4000800,0x200802,0x200002,0x4000800,0x4000002,0x4200000,0x4200800,0x200002,0x4200000,0x800,0x802,0x4200802,0x200800,0x2,0x4000000,0x200800,0x4000000,0x200800,0x200000,0x4000802,0x4000802,0x4200002,0x4200002,0x2,0x200002,0x4000000,0x4000800,0x200000,0x4200800,0x802,0x200802,0x4200800,0x802,0x4000002,0x4200802,0x4200000,0x200800,0,0x2,0x4200802,0,0x200802,0x4200000,0x800,0x4000002,0x4000800,0x800,0x200002);
$spfunction8 = array (0x10001040,0x1000,0x40000,0x10041040,0x10000000,0x10001040,0x40,0x10000000,0x40040,0x10040000,0x10041040,0x41000,0x10041000,0x41040,0x1000,0x40,0x10040000,0x10000040,0x10001000,0x1040,0x41000,0x40040,0x10040040,0x10041000,0x1040,0,0,0x10040040,0x10000040,0x10001000,0x41040,0x40000,0x41040,0x40000,0x10041000,0x1000,0x40,0x10040040,0x1000,0x41040,0x10001000,0x40,0x10000040,0x10040000,0x10040040,0x10000000,0x40000,0x10001040,0,0x10041040,0x40040,0x10000040,0x10040000,0x10001000,0x10001040,0,0x10041040,0x41000,0x41000,0x1040,0x1040,0x40040,0x10000000,0x10041000);
$masks = array (4294967295,2147483647,1073741823,536870911,268435455,134217727,67108863,33554431,16777215,8388607,4194303,2097151,1048575,524287,262143,131071,65535,32767,16383,8191,4095,2047,1023,511,255,127,63,31,15,7,3,1,0);
//create the 16 or 48 subkeys we will need
$keys = des_createKeys ($key);
$m=0;
$len = strlen($message);
//如果加密,则需要填充
if($encrypt==1)
if($len%8==1)
for($i=0;$i<7;$i++)
$message.=chr(7);
if($len%8==2)
for($i=0;$i<6;$i++)
$message.=chr(6);
if($len%8==3)
for($i=0;$i<5;$i++)
$message.=chr(5);
if($len%8==4)
for($i=0;$i<4;$i++)
$message.=chr(4);
if($len%8==5)
for($i=0;$i<3;$i++)
$message.=chr(3);
if($len%8==6)
for($i=0;$i<2;$i++)
$message.=chr(2);
if($len%8==7)
for($i=0;$i<1;$i++)
$message.=chr(1);
if($len%8==0)
for($i=0;$i<8;$i++)
$message.=chr(8);
$len = $len + 8;
echo "message:".$message;
echo "<br>";
$chunk = 0;
//set up the loops for single and triple des
$iterations = ((count($keys) == 32) ? 3 : 9); //single or triple des
if ($iterations == 3) $looping = (($encrypt) ? array (0, 32, 2) : array (30, -2, -2));
else $looping = (($encrypt) ? array (0, 32, 2, 62, 30, -2, 64, 96, 2) : array (94, 62, -2, 32, 64, 2, 30, -2, -2));
echo "3.iterations".$iterations;
echo "<br> 4.looping:";
for($ii = 0; $ii < count($looping); $ii++)
echo ",".$looping[$ii];
echo "<br>";
//pad the message depending on the padding parameter
// if ($padding == 2) $message .= " "; //pad the message with spaces
// else if ($padding == 1) $temp = chr (8-($len%8)); $message .= $temp . $temp . $temp . $temp . $temp . $temp . $temp . $temp; if ($temp==8) $len+=8; //PKCS7 padding
// else if (!$padding) $message .= (chr(0) . chr(0) . chr(0) . chr(0) . chr(0) . chr(0) . chr(0) . chr(0)); //pad the message out with null bytes
//store the result here
$result = "";
$tempresult = "";
if ($mode == 1) //CBC mode
$cbcleft = (ord($iv$m++) << 24) | (ord($iv$m++) << 16) | (ord($iv$m++) << 8) | ord($iv$m++);
$cbcright = (ord($iv$m++) << 24) | (ord($iv$m++) << 16) | (ord($iv$m++) << 8) | ord($iv$m++);
$m=0;
echo "mode:".$mode;
echo "<br>";
echo "5.cbcleft:".$cbcleft;
echo "<br>";
echo "6.cbcright:".$cbcright;
echo "<br>";
//loop through each 64 bit chunk of the message
while ($m < $len)
$left = (ord($message$m++) << 24) | (ord($message$m++) << 16) | (ord($message$m++) << 8) | ord($message$m++);
$right = (ord($message$m++) << 24) | (ord($message$m++) << 16) | (ord($message$m++) << 8) | ord($message$m++);
//for Cipher Block Chaining mode, xor the message with the previous result
if ($mode == 1) if ($encrypt) $left ^= $cbcleft; $right ^= $cbcright; else $cbcleft2 = $cbcleft; $cbcright2 = $cbcright; $cbcleft = $left; $cbcright = $right;
//first each 64 but chunk of the message must be permuted according to IP
$temp = (($left >> 4 & $masks[4]) ^ $right) & 0x0f0f0f0f; $right ^= $temp; $left ^= ($temp << 4);
$temp = (($left >> 16 & $masks[16]) ^ $right) & 0x0000ffff; $right ^= $temp; $left ^= ($temp << 16);
$temp = (($right >> 2 & $masks[2]) ^ $left) & 0x33333333; $left ^= $temp; $right ^= ($temp << 2);
$temp = (($right >> 8 & $masks[8]) ^ $left) & 0x00ff00ff; $left ^= $temp; $right ^= ($temp << 8);
$temp = (($left >> 1 & $masks[1]) ^ $right) & 0x55555555; $right ^= $temp; $left ^= ($temp << 1);
$left = (($left << 1) | ($left >> 31 & $masks[31]));
$right = (($right << 1) | ($right >> 31 & $masks[31]));
//do this either 1 or 3 times for each chunk of the message
for ($j=0; $j<$iterations; $j+=3)
$endloop = $looping[$j+1];
$loopinc = $looping[$j+2];
//now go through and perform the encryption or decryption
for ($i=$looping[$j]; $i!=$endloop; $i+=$loopinc) //for efficiency
$right1 = $right ^ $keys[$i];
$right2 = (($right >> 4 & $masks[4]) | ($right << 28 & 0xffffffff)) ^ $keys[$i+1];
//the result is attained by passing these bytes through the S selection functions
$temp = $left;
$left = $right;
$right = $temp ^ ($spfunction2[($right1 >> 24 & $masks[24]) & 0x3f] | $spfunction4[($right1 >> 16 & $masks[16]) & 0x3f]
| $spfunction6[($right1 >> 8 & $masks[8]) & 0x3f] | $spfunction8[$right1 & 0x3f]
| $spfunction1[($right2 >> 24 & $masks[24]) & 0x3f] | $spfunction3[($right2 >> 16 & $masks[16]) & 0x3f]
| $spfunction5[($right2 >> 8 & $masks[8]) & 0x3f] | $spfunction7[$right2 & 0x3f]);
$temp = $left; $left = $right; $right = $temp; //unreverse left and right
//for either 1 or 3 iterations
//move then each one bit to the right
$left = (($left >> 1 & $masks[1]) | ($left << 31));
$right = (($right >> 1 & $masks[1]) | ($right << 31));
//now perform IP-1, which is IP in the opposite direction
$temp = (($left >> 1 & $masks[1]) ^ $right) & 0x55555555; $right ^= $temp; $left ^= ($temp << 1);
$temp = (($right >> 8 & $masks[8]) ^ $left) & 0x00ff00ff; $left ^= $temp; $right ^= ($temp << 8);
$temp = (($right >> 2 & $masks[2]) ^ $left) & 0x33333333; $left ^= $temp; $right ^= ($temp << 2);
$temp = (($left >> 16 & $masks[16]) ^ $right) & 0x0000ffff; $right ^= $temp; $left ^= ($temp << 16);
$temp = (($left >> 4 & $masks[4]) ^ $right) & 0x0f0f0f0f; $right ^= $temp; $left ^= ($temp << 4);
//for Cipher Block Chaining mode, xor the message with the previous result
if ($mode == 1) if ($encrypt) $cbcleft = $left; $cbcright = $right; else $left ^= $cbcleft2; $right ^= $cbcright2;
$tempresult .= (chr($left>>24 & $masks[24]) . chr(($left>>16 & $masks[16]) & 0xff) . chr(($left>>8 & $masks[8]) & 0xff) . chr($left & 0xff) . chr($right>>24 & $masks[24]) . chr(($right>>16 & $masks[16]) & 0xff) . chr(($right>>8 & $masks[8]) & 0xff) . chr($right & 0xff));
$chunk += 8;
if ($chunk == 512) $result .= $tempresult; $tempresult = ""; $chunk = 0;
//for every 8 characters, or 64 bits in the message
//return the result as an array
return ($result . $tempresult);
//end of des
//des_createKeys
//this takes as input a 64 bit key (even though only 56 bits are used)
//as an array of 2 integers, and returns 16 48 bit keys
function des_createKeys ($key)
//declaring this locally speeds things up a bit
$pc2bytes0 = array (0,0x4,0x20000000,0x20000004,0x10000,0x10004,0x20010000,0x20010004,0x200,0x204,0x20000200,0x20000204,0x10200,0x10204,0x20010200,0x20010204);
$pc2bytes1 = array (0,0x1,0x100000,0x100001,0x4000000,0x4000001,0x4100000,0x4100001,0x100,0x101,0x100100,0x100101,0x4000100,0x4000101,0x4100100,0x4100101);
$pc2bytes2 = array (0,0x8,0x800,0x808,0x1000000,0x1000008,0x1000800,0x1000808,0,0x8,0x800,0x808,0x1000000,0x1000008,0x1000800,0x1000808);
$pc2bytes3 = array (0,0x200000,0x8000000,0x8200000,0x2000,0x202000,0x8002000,0x8202000,0x20000,0x220000,0x8020000,0x8220000,0x22000,0x222000,0x8022000,0x8222000);
$pc2bytes4 = array (0,0x40000,0x10,0x40010,0,0x40000,0x10,0x40010,0x1000,0x41000,0x1010,0x41010,0x1000,0x41000,0x1010,0x41010);
$pc2bytes5 = array (0,0x400,0x20,0x420,0,0x400,0x20,0x420,0x2000000,0x2000400,0x2000020,0x2000420,0x2000000,0x2000400,0x2000020,0x2000420);
$pc2bytes6 = array (0,0x10000000,0x80000,0x10080000,0x2,0x10000002,0x80002,0x10080002,0,0x10000000,0x80000,0x10080000,0x2,0x10000002,0x80002,0x10080002);
$pc2bytes7 = array (0,0x10000,0x800,0x10800,0x20000000,0x20010000,0x20000800,0x20010800,0x20000,0x30000,0x20800,0x30800,0x20020000,0x20030000,0x20020800,0x20030800);
$pc2bytes8 = array (0,0x40000,0,0x40000,0x2,0x40002,0x2,0x40002,0x2000000,0x2040000,0x2000000,0x2040000,0x2000002,0x2040002,0x2000002,0x2040002);
$pc2bytes9 = array (0,0x10000000,0x8,0x10000008,0,0x10000000,0x8,0x10000008,0x400,0x10000400,0x408,0x10000408,0x400,0x10000400,0x408,0x10000408);
$pc2bytes10 = array (0,0x20,0,0x20,0x100000,0x100020,0x100000,0x100020,0x2000,0x2020,0x2000,0x2020,0x102000,0x102020,0x102000,0x102020);
$pc2bytes11 = array (0,0x1000000,0x200,0x1000200,0x200000,0x1200000,0x200200,0x1200200,0x4000000,0x5000000,0x4000200,0x5000200,0x4200000,0x5200000,0x4200200,0x5200200);
$pc2bytes12 = array (0,0x1000,0x8000000,0x8001000,0x80000,0x81000,0x8080000,0x8081000,0x10,0x1010,0x8000010,0x8001010,0x80010,0x81010,0x8080010,0x8081010);
$pc2bytes13 = array (0,0x4,0x100,0x104,0,0x4,0x100,0x104,0x1,0x5,0x101,0x105,0x1,0x5,0x101,0x105);
$masks = array (4294967295,2147483647,1073741823,536870911,268435455,134217727,67108863,33554431,16777215,8388607,4194303,2097151,1048575,524287,262143,131071,65535,32767,16383,8191,4095,2047,1023,511,255,127,63,31,15,7,3,1,0);
//how many iterations (1 for des, 3 for triple des)
// $iterations = ((strlen($key) > 8) ? 3 : 1); //changed by Paul 16/6/2007 to use Triple DES for 9+ byte keys
$iterations = ((strlen($key) > 24) ? 3 : 1); //changed by Paul 16/6/2007 to use Triple DES for 9+ byte keys
//stores the return keys
$keys = array (); // size = 32 * iterations but you don't specify this in php
//now define the left shifts which need to be done
$shifts = array (0, 0, 1, 1, 1, 1, 1, 1, 0, 1, 1, 1, 1, 1, 1, 0);
//other variables
$m=0;
$n=0;
for ($j=0; $j<$iterations; $j++) //either 1 or 3 iterations
$left = (ord($key$m++) << 24) | (ord($key$m++) << 16) | (ord($key$m++) << 8) | ord($key$m++);
$right = (ord($key$m++) << 24) | (ord($key$m++) << 16) | (ord($key$m++) << 8) | ord($key$m++);
$temp = (($left >> 4 & $masks[4]) ^ $right) & 0x0f0f0f0f; $right ^= $temp; $left ^= ($temp << 4);
$temp = (($right >> 16 & $masks[16]) ^ $left) & 0x0000ffff; $left ^= $temp; $right ^= ($temp << 16);
$temp = (($left >> 2 & $masks[2]) ^ $right) & 0x33333333; $right ^= $temp; $left ^= ($temp << 2);
$temp = (($right >> 16 & $masks[16]) ^ $left) & 0x0000ffff; $left ^= $temp; $right ^= ($temp << 16);
$temp = (($left >> 1 & $masks[1]) ^ $right) & 0x55555555; $right ^= $temp; $left ^= ($temp << 1);
$temp = (($right >> 8 & $masks[8]) ^ $left) & 0x00ff00ff; $left ^= $temp; $right ^= ($temp << 8);
$temp = (($left >> 1 & $masks[1]) ^ $right) & 0x55555555; $right ^= $temp; $left ^= ($temp << 1);
//the right side needs to be shifted and to get the last four bits of the left side
$temp = ($left << 8) | (($right >> 20 & $masks[20]) & 0x000000f0);
//left needs to be put upside down
$left = ($right << 24) | (($right << 8) & 0xff0000) | (($right >> 8 & $masks[8]) & 0xff00) | (($right >> 24 & $masks[24]) & 0xf0);
$right = $temp;
//now go through and perform these shifts on the left and right keys
for ($i=0; $i < count($shifts); $i++)
//shift the keys either one or two bits to the left
if ($shifts[$i] > 0)
$left = (($left << 2) | ($left >> 26 & $masks[26]));
$right = (($right << 2) | ($right >> 26 & $masks[26]));
else
$left = (($left << 1) | ($left >> 27 & $masks[27]));
$right = (($right << 1) | ($right >> 27 & $masks[27]));
$left = $left & -0xf;
$right = $right & -0xf;
//now apply PC-2, in such a way that E is easier when encrypting or decrypting
//this conversion will look like PC-2 except only the last 6 bits of each byte are used
//rather than 48 consecutive bits and the order of lines will be according to
//how the S selection functions will be applied: S2, S4, S6, S8, S1, S3, S5, S7
$lefttemp = $pc2bytes0[$left >> 28 & $masks[28]] | $pc2bytes1[($left >> 24 & $masks[24]) & 0xf]
| $pc2bytes2[($left >> 20 & $masks[20]) & 0xf] | $pc2bytes3[($left >> 16 & $masks[16]) & 0xf]
| $pc2bytes4[($left >> 12 & $masks[12]) & 0xf] | $pc2bytes5[($left >> 8 & $masks[8]) & 0xf]
| $pc2bytes6[($left >> 4 & $masks[4]) & 0xf];
$righttemp = $pc2bytes7[$right >> 28 & $masks[28]] | $pc2bytes8[($right >> 24 & $masks[24]) & 0xf]
| $pc2bytes9[($right >> 20 & $masks[20]) & 0xf] | $pc2bytes10[($right >> 16 & $masks[16]) & 0xf]
| $pc2bytes11[($right >> 12 & $masks[12]) & 0xf] | $pc2bytes12[($right >> 8 & $masks[8]) & 0xf]
| $pc2bytes13[($right >> 4 & $masks[4]) & 0xf];
$temp = (($righttemp >> 16 & $masks[16]) ^ $lefttemp) & 0x0000ffff;
$keys[$n++] = $lefttemp ^ $temp; $keys[$n++] = $righttemp ^ ($temp << 16);
//for each iterations
//return the keys we've created
for($ii = 0; $ii < count($keys); $ii++)
echo ",".$keys[$ii];
echo "<br>";
return $keys;
//end of des_createKeys
////////////////////////////// TEST //////////////////////////////
function stringToHex ($s)
$r = "0x";
$hexes = array ("0","1","2","3","4","5","6","7","8","9","a","b","c","d","e","f");
for ($i=0; $i<strlen($s); $i++) $r .= ($hexes [(ord($s$i) >> 4)] . $hexes [(ord($s$i) & 0xf)]);
return $r;
function hexToString ($h)
$r = "";
for ($i= (substr($h, 0, 2)=="0x")?2:0; $i<strlen($h); $i+=2) $r .= chr (base_convert (substr ($h, $i, 2), 16, 10));
return $r;
function idtag_des_encode($text)
$key = '12345678';
$y=pkcs5_pad($text);
echo "y:".$y;
echo "<br />";
$td = mcrypt_module_open(MCRYPT_DES,'',MCRYPT_MODE_CBC,''); //使用MCRYPT_DES算法,cbc模式
$iv = mcrypt_create_iv(mcrypt_enc_get_iv_size($td), MCRYPT_RAND);
$ks = mcrypt_enc_get_key_size($td);
mcrypt_generic_init($td, $key, $key); //初始处理
$encrypted = mcrypt_generic($td, $y); //解密
mcrypt_generic_deinit($td); //结束
mcrypt_module_close($td);
return $encrypted;
// return base64_encode($encrypted);
function pkcs5_pad($text,$block=8)
$pad = $block - (strlen($text) % $block);
return $text . str_repeat(chr($pad), $pad);
$key = "12345678";
$message = "str4";
$ciphertext = des ($key, $message, 1, 1, $key,null);
//echo "stringToHex (ciphertext): " . stringToHex ($ciphertext);
//echo "<br />";
echo "base64_encode(ciphertext): " . base64_encode($ciphertext);
//echo "<br />";
//echo "encode64(ciphertext): " . encode64($ciphertext);
//echo "<br />";
//echo "base64_encode(stringToHex (ciphertext)): " . base64_encode(stringToHex ($ciphertext));
//echo "<br />";
//echo "stringToHex (base64_encode(ciphertext)): " . stringToHex (idtag_des_encode($message));
echo "<br />";
echo "idtag_des_encode: " .base64_encode(idtag_des_encode($message));
//$recovered_message = des ($key, $ciphertext, 0, 0, null,null);
//echo "\n";
//echo "DES Test Decrypted: " . $recovered_message;
?>
参考资料:http://www.fyyk.com
本回答被提问者采纳DES加密算法详细原理以及Java代码实现
本周的密码学实验要求使用任意编程语言来实现des加密算法,于是我在查阅了相关资料后有了以下成果。
首先,DES算法作为经典的分块密码(block cipher),其主要的实现过程由两部分组成,分别是密钥的生成以及明文的处理。
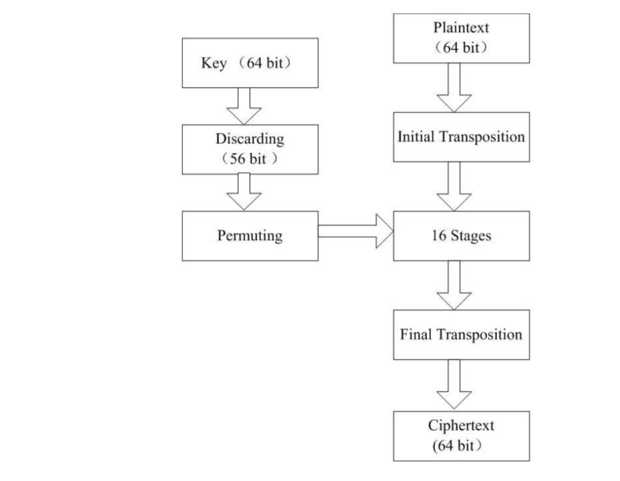
加密的大致流程如图所示
作为分块密码,密钥的输入以及明文的输入均为64位2进制数。
下面首先来说密钥的生成过程。
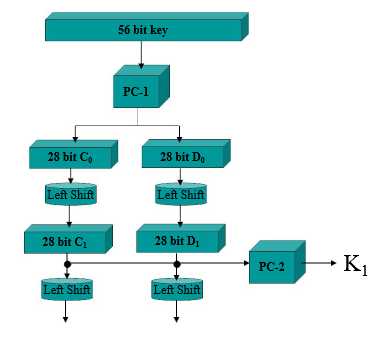
密钥处理部分如图所示
密钥的输入为64位,例如00010011 00110100 01010111 01111001 10011011 10111100 11011111 11110001,然后经过pc-1盒置换,会去除每一个8的倍数位(奇偶校验位)并打乱次序,将密钥变为56位。pc-1的置换表如下(框中的数字代表的是原密钥的位置,而不是数据)
1 57,49,41,33,25,17,9,1, 2 58,50,42,34,26,18,10,2, 3 59,51,43,35,27,19,11,3, 4 60,52,44,36,63,55,47,39, 5 31,23,15,7,62,54,46,38, 6 30,22,14,6,61,53,45,37, 7 29,21,13,5,28,20,12,4
也就是说,经过pc-1盒的置换原来第57位的1将会到第1位,原来49位的数据会到第2位,以此类推。在DES密钥加密的过程中,这种置换方式经常出现。
在经过了pc-1盒的置换后,原来56位的密钥会被均分为两组成为c0,d0。然后l0和d0会经过循环左移(left shift)的处理。
例如一串密钥为1010101,在经过一位的循环左移后会变成0101011,即循环左移几位,最左边的几位数据会紧接在后面,达到一种左移的效果。左移后的密钥块分别称为c1,d1。这时候,将c1以及d1组合起来,经过pc-2的置换(类似于pc-1)。
1 14,17,11,24,1,5, 2 3,28,15,6,21,10, 3 23,19,12,4,26,8, 4 16,7,27,20,13,2, 5 41,52,31,37,47,55, 6 30,40,51,45,33,48, 7 44,49,39,56,34,53, 8 46,42,50,36,29,32
经过了pc-2盒的置换后,原本56位的密钥会变为48位。这个时候,第一个能够用于加密的子密钥k1就生成好了。在des算法密钥生成的过程中,一个主密钥会经过16轮的循环左移和pc-2置换,生成16个子密钥。循环左移的位数和轮次的关系如下表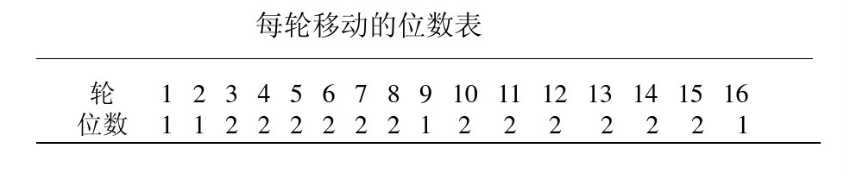
后续子密钥的生成过程就是重复上面的过程,c1和d1再进行循环左移得到c2和d2,再经过pc-2盒置换得到k2,c2和d2再经过左移得到c3和d3经过pc-2盒得到k3.....经过这样的操作16轮,得到16个子密钥。密钥的生成过程大致如上,接下来来阐述明文的处理过程。
 明文的处理流程大致如图所示。
明文的处理流程大致如图所示。
首先,64位明文的输入需要经过初始置换,并把输出块分为L0,R0两部分,每部分32位。(有点类似于密钥初始化时的pc-1)置换规则如下:
1 58,50,42,34,26,18,10,2, 2 60,52,44,36,28,20,12,4, 3 62,54,46,38,30,22,14,6, 4 64,56,48,40,32,24,16,8, 5 57,49,41,33,25,17, 9,1, 6 59,51,43,35,27,19,11,3, 7 61,53,45,37,29,21,13,5, 8 63,55,47,39,31,23,15,7
这个过程与pc-1阶段类似,置换后的第1位是原来的第58位,第2位是原来的第50位,以此类推。L0是置换后数据的前32位,R0是置换后的后32位。
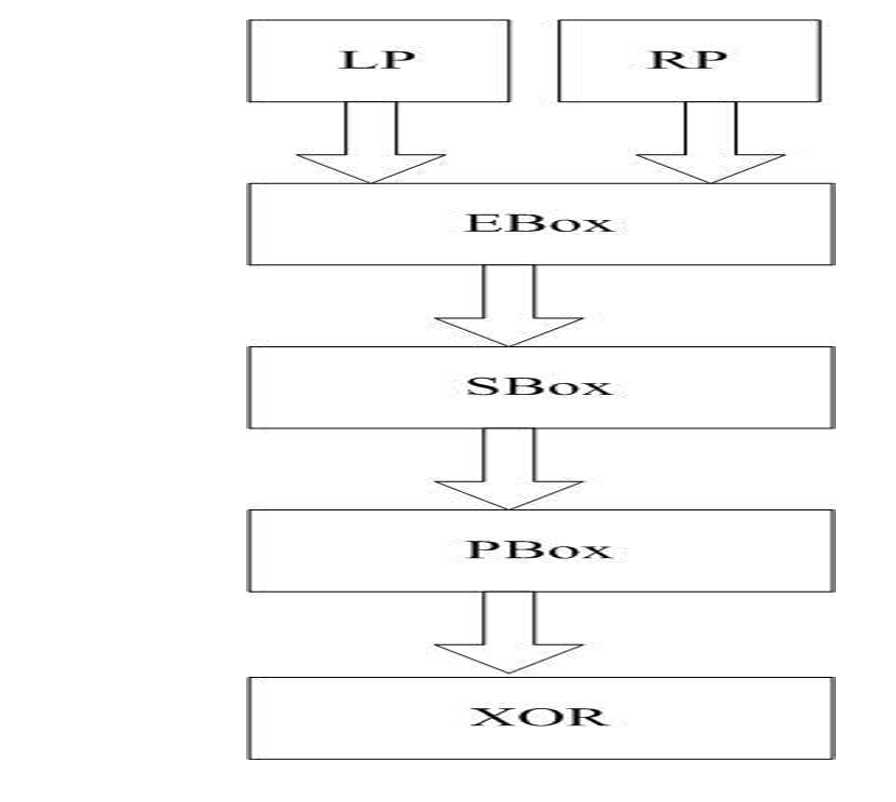
经过了初始置换之后,R0会进依次进入E-box,S-box,P-box三个置换盒,进行下一步的处理。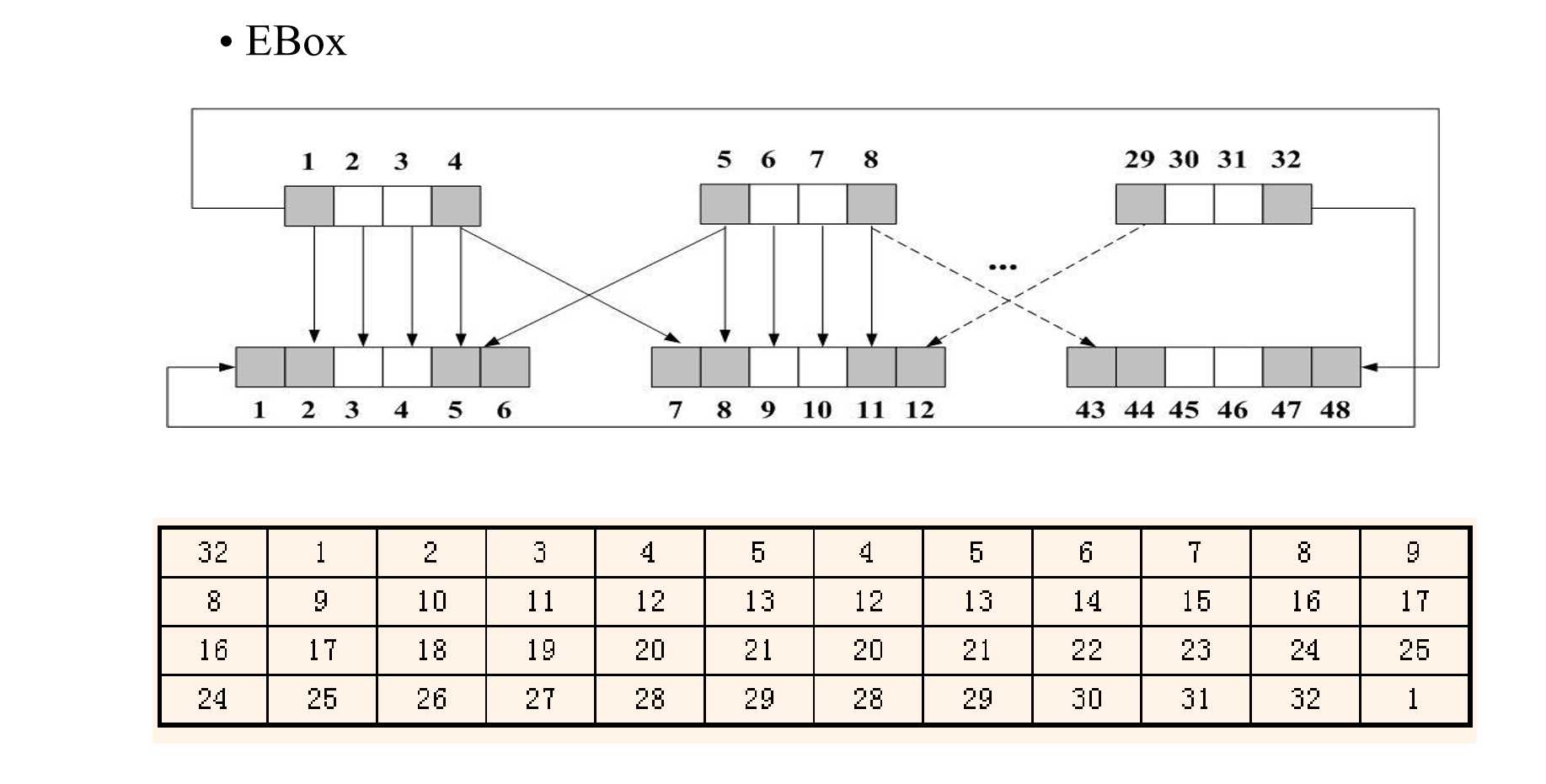
E-box的处理过程如图示
E-box本质上是将原来32位的数据变为了48位,原理是将原来的32位输入以四位为一个单元分开,然后这个单元的第1位会复制到上一个单元的最后一位,这个单元的最后一位会变为下一个单元的第1位。看图可知,1234分块的第一位复制到了最后一块成为了第48位,第32位复制到了第1位成为了新数据组的第1位,具体过程如果还不明晰的话可以仔细看图解决。
在经过了E-box后,新的R0变为了48位,刚好与生成的密钥位数一致。这个时候,需要使用k1和新R0执行一次异或(相同记为0,不同记为1)操作,在异或操作结束后新的数据块会进入S-Box进行替代。
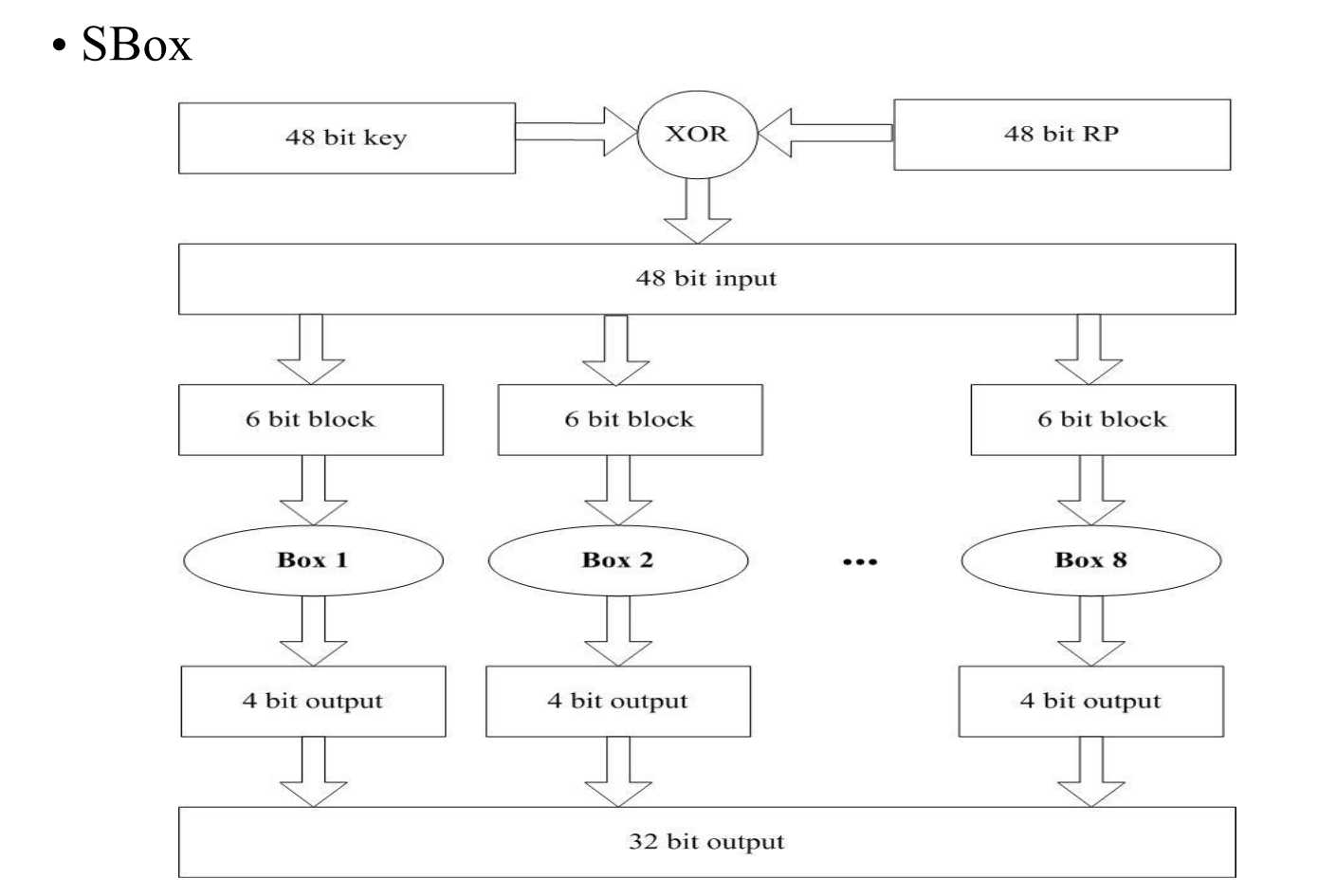
S-box会将48位的输入按照次序分为8组,分别进入8个子盒进行替代,每个盒的输入是6位,输出是4位。8个子盒原理如下:
S-box1
1 14,4,13,1,2,15,11,8,3,10,6,12,5,9,0,7, 2 0,15,7,4,14,2,13,1,10,6,12,11,9,5,3,8, 3 4,1,14,8,13,6,2,11,15,12,9,7,3,10,5,0, 4 15,12,8,2,4,9,1,7,5,11,3,14,10,0,6,13
S-box2
1 15,1,8,14,6,11,3,4,9,7,2,13,12,0,5,10, 2 3,13,4,7,15,2,8,14,12,0,1,10,6,9,11,5, 3 0,14,7,11,10,4,13,1,5,8,12,6,9,3,2,15, 4 13,8,10,1,3,15,4,2,11,6,7,12,0,5,14,9
S-box3
1 10,0,9,14,6,3,15,5,1,13,12,7,11,4,2,8, 2 13,7,0,9,3,4,6,10,2,8,5,14,12,11,15,1, 3 13,6,4,9,8,15,3,0,11,1,2,12,5,10,14,7, 4 1,10,13,0,6,9,8,7,4,15,14,3,11,5,2,12
S-box4
1 7,13,14,3,0,6,9,10,1,2,8,5,11,12,4,15, 2 13,8,11,5,6,15,0,3,4,7,2,12,1,10,14,9, 3 10,6,9,0,12,11,7,13,15,1,3,14,5,2,8,4, 4 3,15,0,6,10,1,13,8,9,4,5,11,12,7,2,14
S-box5
1 2,12,4,1,7,10,11,6,8,5,3,15,13,0,14,9, 2 14,11,2,12,4,7,13,1,5,0,15,10,3,9,8,6, 3 4,2,1,11,10,13,7,8,15,9,12,5,6,3,0,14, 4 11,8,12,7,1,14,2,13,6,15,0,9,10,4,5,3
S-box6
1 12,1,10,15,9,2,6,8,0,13,3,4,14,7,5,11, 2 10,15,4,2,7,12,9,5,6,1,13,14,0,11,3,8, 3 9,14,15,5,2,8,12,3,7,0,4,10,1,13,11,6, 4 4,3,2,12,9,5,15,10,11,14,1,7,6,0,8,13
S-box7
1 4,11,2,14,15,0,8,13,3,12,9,7,5,10,6,1, 2 13,0,11,7,4,9,1,10,14,3,5,12,2,15,8,6, 3 1,4,11,13,12,3,7,14,10,15,6,8,0,5,9,2, 4 6,11,13,8,1,4,10,7,9,5,0,15,14,2,3,12
S-box8
1 13,2,8,4,6,15,11,1,10,9,3,14,5,0,12,7, 2 1,15,13,8,10,3,7,4,12,5,6,11,0,14,9,2, 3 7,11,4,1,9,12,14,2,0,6,10,13,15,3,5,8, 4 2,1,14,7,4,10,8,13,15,12,9,0,3,5,6,11
S-box的计算规则:
以S-box8为例,如果该盒输入为六位011100。取第一位和最后一位组成二进制数00,转化为十进制为0,对应该盒第1行。中间四位组成1110,十进制化为14,对应该盒第15列(考试的时候这个地方错了,,,1551)寻找该盒第1行第15列的元素,是12,转化为2进制是1100,这也就是该盒的输出。
在经过了S-box置换后,数据块还需一步处理,P-box
P-box很简单,类似于pc-1,就是简单的置换,32位的输入置换为32位的输出。置换表如下:
1 16,7,20,21,29,12,28,17,1,15,23,26,5,18,31,10, 2 2,8,24,14,32,27,3,9,19,13,30,6,22,11,4,25
在经过了这些处理后,原来32位的R0变为了新的32位数据块,这个时候,使用这32位数据块和原来的L0进行异或,变为新的32位R1,这时候,原来的R0成为新的L1。R1再经过E-box扩展,和k2(第二个子密钥)异或,S-box替代,P-box置换的过程。再与L1进行异或,直到使用完所有的16个子密钥(也是16轮)。
明文经过了这16轮变换之后已经面目全非,这个时候把L和R组合成为64位经过最后的置换,即成为密文。最终置换如下:
1 40,8,48,16,56,24,64,32,39,7,47,15,55,23,63,31, 2 38,6,46,14,54,22,62,30,37,5,45,13,53,21,61,29, 3 36,4,44,12,52,20,60,28,35,3,43,11,51,19,59,27, 4 34,2,42,10,50,18,58 26,33,1,41, 9,49,17,57,25
下面附上从别的老哥那抄来的介绍:
DES的特点:
优点:
效率高,算法简单,系统开销小(真的简单吗,,,,)
适合加密大量数据
明文长度和密文长度相等
缺点:
需要以安全方式进行秘钥交换
秘钥管理复杂
最后是JAVA实现的代码,我已上传至我的GitHub,地址为:https://github.com/jason-ralston各位自行前去食用。
以上是关于80分求DES加密解密算法实现的PHP源代码的主要内容,如果未能解决你的问题,请参考以下文章