GO (国密,标准Https) 单向,双向认证Demo
Posted 小米渣的逆袭
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了GO (国密,标准Https) 单向,双向认证Demo相关的知识,希望对你有一定的参考价值。
最近使用开源项目tjfoc/gmsm 做国密研究,由于他没有具体说怎么生成证书的,期间对于生成他对应的国密证书做了些研究,踩了一些坑
他对国密通信做的demo主要在websvr目录下

下面主要说下生成国密证书步骤
1. 需要装gmssl , 具体编译参见上一篇文章
2. 使用gmssl ecparam -genkey -name sm2p256v1 -noout -out $OUTPUT/$name.key 生成的私钥在他的go代码 gmtls.LoadX509KeyPair 方法会报错,经过研究可以使用x509目录下的go生成私钥
所以使用x509目录下的生成私钥代码
func createPrvateKey(s string)
priv, err := sm2.GenerateKey(nil) // 生成密钥对
if err != nil
return
privPem, err := WritePrivateKeyToPem(priv, nil) // 生成密钥文件
fmt.Printf("privateKey=%s",privPem)
if err != nil
return
os.Remove(s)
os.WriteFile(s,privPem,0666)
其他部分还是使用gmssl生成
3. 开始生成的证书会报keyUsage相关错误,以server签名证书为例
使用./openssl.cnf -extensions v3_req 参数,在openssl.cnf中

server加密证书
-extfile ./openssl.cnf -extensions v3enc_req

4. 如果遇到 x509: cannot validate certificate for x.x.x.x because it doesn't contain any IP SANs 解决: 解决参考
在openssl.cnf中

测试Demo代码
package main
import (
"crypto/tls"
"fmt"
"github.com/tjfoc/gmsm/gmtls"
"github.com/tjfoc/gmsm/x509"
"io/ioutil"
"log"
"net/http"
)
func handler(w http.ResponseWriter, r *http.Request)
fmt.Fprintf(w,
"王家荣")
func httpServerOne()
http.HandleFunc("/", handler)
err := http.ListenAndServeTLS(":50052", "./certs/standard_server_sign.cer",
"./certs/standard_server_sign.key", nil)
if err != nil
fmt.Println(err)
else
fmt.Println("单项httpServer启动成功")
func httpServerTwo()
config,err := newServerConfig()
if err != nil
fmt.Println(err)
return
http.HandleFunc("/", handler)
s := &http.Server
Addr: ":50052",
TLSConfig: config,
log.Fatal(s.ListenAndServeTLS("./certs/standard_server_sign.cer", "./certs/standard_server_sign.key"))
func httpClientOne()
config,err := newClientConfig()
if err != nil
fmt.Println(err)
return
conn, err := tls.Dial("tcp", "127.0.0.1:50052", config)
if err != nil
fmt.Printf("%s\\r\\n",err)
return
defer conn.Close()
req := []byte("GET / HTTP/1.1\\r\\n" +
"Host: 127.0.0.1\\r\\n" +
"Connection: close\\r\\n\\r\\n")
_, _ = conn.Write(req)
buff := make([]byte, 1024)
for
n, _ := conn.Read(buff)
if n <= 0
break
else
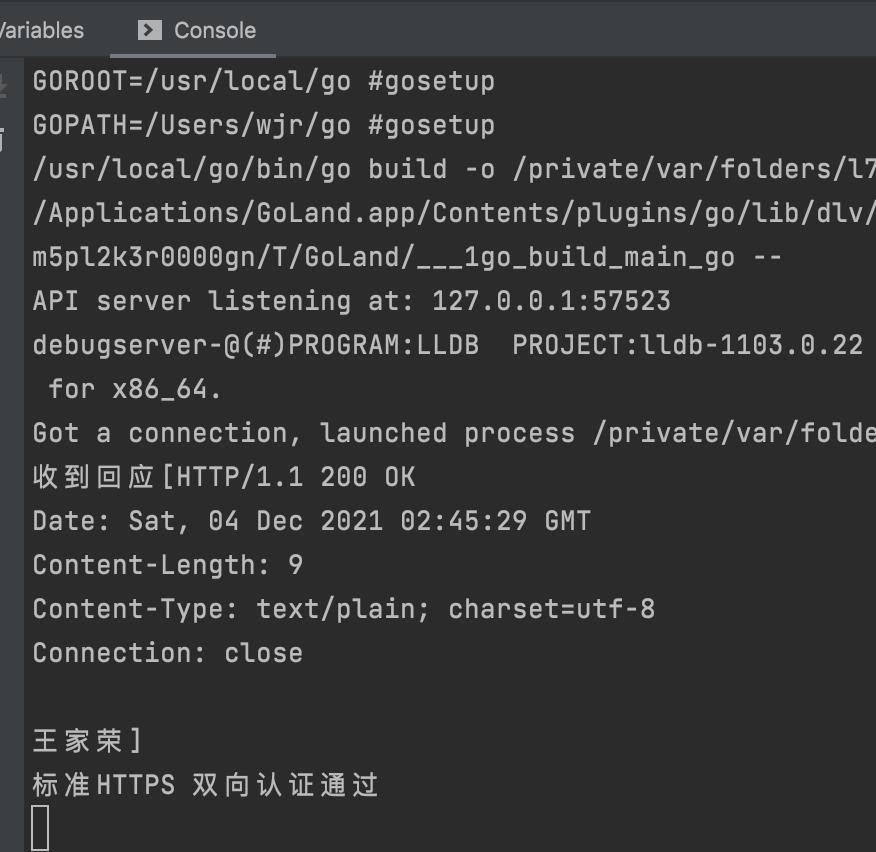
fmt.Printf("收到回应[%s]\\r\\n", buff[0:n])
fmt.Println("标准HTTPS 单向认证通过")
func httpClientTwo()
config,err := newClientConfig()
if err != nil
fmt.Println(err)
return
conn, err := tls.Dial("tcp", "127.0.0.1:50052", config)
if err != nil
fmt.Printf("%s\\r\\n",err)
return
defer conn.Close()
req := []byte("GET / HTTP/1.1\\r\\n" +
"Host: 127.0.0.1\\r\\n" +
"Connection: close\\r\\n\\r\\n")
_, _ = conn.Write(req)
buff := make([]byte, 1024)
for
n, _ := conn.Read(buff)
if n <= 0
break
else
fmt.Printf("收到回应[%s]\\r\\n", buff[0:n])
fmt.Println("标准HTTPS 双向认证通过")
func gmServerTwo()
sigCert, err := gmtls.LoadX509KeyPair(
"./certs/server_sign.cer",
"./certs/server_sign.key")
if err != nil
fmt.Println(err)
encCert, err := gmtls.LoadX509KeyPair(
"./certs/server_encode.cer",
"./certs/server_encode.key")
if err != nil
fmt.Println(err)
certPool := x509.NewCertPool()
cacert, err := ioutil.ReadFile("./certs/ca.cer")
if err != nil
fmt.Println(err)
certPool.AppendCertsFromPEM(cacert)
config := &gmtls.Config
GMSupport: &gmtls.GMSupport,
Certificates: []gmtls.CertificatesigCert, encCert,
ClientAuth: gmtls.RequireAndVerifyClientCert,
ClientCAs: certPool,
if err != nil
fmt.Println(err)
ln, err := gmtls.Listen("tcp", ":50052", config)
if err != nil
fmt.Println(err)
defer ln.Close()
serveMux := http.NewServeMux()
serveMux.HandleFunc("/", handler)
fmt.Println(">> HTTP :50055 [GMSSL] Client Auth running...")
err = http.Serve(ln, serveMux)
if err != nil
fmt.Println(err)
func gmServerOne()
sigCert, err := gmtls.LoadX509KeyPair(
"./certs/server_sign.cer",
"./certs/server_sign.key")
if err != nil
fmt.Println(err)
encCert, err := gmtls.LoadX509KeyPair(
"./certs/server_encode.cer",
"./certs/server_encode.key")
if err != nil
fmt.Println(err)
config := &gmtls.Config
GMSupport: &gmtls.GMSupport,
Certificates: []gmtls.CertificatesigCert, encCert,
if err != nil
fmt.Println(err)
ln, err := gmtls.Listen("tcp", ":50052", config)
if err != nil
fmt.Println(err)
defer ln.Close()
serveMux := http.NewServeMux()
serveMux.HandleFunc("/", handler)
fmt.Println(">> HTTP :50055 [GMSSL] Client Auth running...")
err = http.Serve(ln, serveMux)
if err != nil
fmt.Println(err)
func gmClientOne()
// 信任的根证书
certPool := x509.NewCertPool()
cacert, err := ioutil.ReadFile("./certs/ca.cer")
if err != nil
log.Fatal(err)
ok := certPool.AppendCertsFromPEM(cacert)
if !ok
return
config := &gmtls.Config
GMSupport: &gmtls.GMSupport,
RootCAs: certPool,
InsecureSkipVerify: false,
conn, err := gmtls.Dial("tcp", "127.0.0.1:50052", config)
if err != nil
fmt.Printf("%s\\r\\n",err)
return
defer conn.Close()
req := []byte("GET / HTTP/1.1\\r\\n" +
"Host: 127.0.0.1\\r\\n" +
"Connection: close\\r\\n\\r\\n")
_, _ = conn.Write(req)
buff := make([]byte, 1024)
for
n, _ := conn.Read(buff)
if n <= 0
break
else
fmt.Printf("收到回应[%s]\\r\\n", buff[0:n])
fmt.Println("国密单向校验通过,纯Socket模式")
// 1. 提供根证书链
certPool = x509.NewCertPool()
cacert, err = ioutil.ReadFile("./certs/ca.cer")
if err != nil
panic(err)
certPool.AppendCertsFromPEM(cacert)
// 3. 构造HTTP客户端。
httpClient := gmtls.NewHTTPSClient(certPool)
// 4. 调用API访问HTTPS。
response, err := httpClient.Get("https://127.0.0.1:50052")
if err != nil
fmt.Println(err)
defer response.Body.Close()
// 使用 response 做你需要的事情...
body,err:=ioutil.ReadAll(response.Body)
fmt.Println(string(body))
fmt.Println("国密单向校验通过,httpClient模式")
func gmClientTwo()
// 信任的根证书
certPool := x509.NewCertPool()
cacert, err := ioutil.ReadFile("./certs/ca.cer")
if err != nil
log.Fatal(err)
ok := certPool.AppendCertsFromPEM(cacert)
if !ok
return
cert, err := gmtls.LoadX509KeyPair("./certs/client.cer", "./certs/client.key")
if err != nil
log.Fatal(err)
config := &gmtls.Config
GMSupport: &gmtls.GMSupport,
RootCAs: certPool,
Certificates: []gmtls.Certificatecert,
InsecureSkipVerify: false,
conn, err := gmtls.Dial("tcp", "127.0.0.1:50052", config)
if err != nil
fmt.Printf("%s\\r\\n",err)
return
defer conn.Close()
req := []byte("GET / HTTP/1.1\\r\\n" +
"Host: 127.0.0.1\\r\\n" +
"Connection: close\\r\\n\\r\\n")
_, _ = conn.Write(req)
buff := make([]byte, 1024)
for
n, _ := conn.Read(buff)
if n <= 0
break
else
fmt.Printf("收到回应[%s]\\r\\n", buff[0:n])
fmt.Println("国密双向校验通过,纯Socket模式")
// 1. 提供根证书链
certPool = x509.NewCertPool()
cacert, err = ioutil.ReadFile("./certs/ca.cer")
if err != nil
panic(err)
certPool.AppendCertsFromPEM(cacert)
// 2. 提供客户端认证证书、密钥对。
clientAuthCert, err := gmtls.LoadX509KeyPair("./certs/client.cer", "./certs/client.key")
// 3. 构造HTTP客户端。
httpClient := gmtls.NewAuthHTTPSClient(certPool, &clientAuthCert)
// 4. 调用API访问HTTPS。
response, err := httpClient.Get("https://127.0.0.1:50052")
if err != nil
fmt.Println(err)
defer response.Body.Close()
// 使用 response 做你需要的事情...
body,err:=ioutil.ReadAll(response.Body)
fmt.Println(string(body))
fmt.Println("国密双向校验通过,httpClient模式")
func createPrvateKey(s string)
priv, err := sm2.GenerateKey(nil) // 生成密钥对
if err != nil
return
privPem, err := WritePrivateKeyToPem(priv, nil) // 生成密钥文件
if err != nil
return
os.Remove(s)
os.WriteFile(s,privPem,0666)
func testHttpsOne()
go httpServerOne()
time.Sleep(1 * time.Second)
go httpClientOne()
func testHttpsTwo()
go httpServerTwo()
time.Sleep(1 * time.Second)
go httpClientTwo()
func testGMOne()
go gmServerOne()
time.Sleep(1 * time.Second)
go gmClientOne()
func testGMTwo()
go gmServerTwo()
time.Sleep(1 * time.Second)
go gmClientTwo()
func main()
if len(os.Args) > 1
createPrvateKey(os.Args[1])
wg := sync.WaitGroup
wg.Add(1)
//测试标准Http单向校验,校验服务器信息
//testHttpsOne()
//测试标准http双向校验
//testHttpsTwo()
//测试国密单向校验
//testGMOne()
//测试国密双向校验
testGMTwo()
wg.Wait()
国密生成脚本
rootPath=$(cd "$(dirname "$0")"; pwd)
#删除打包数据目录
OUTPUT=$rootPath/build
rm -drf $OUTPUT
mkdir $OUTPUT
#CreatePrivateKey是由工程 go build main.go utils.go x509.go ber.go pkcs8.go pkcs7.go pkcs1.go
# 生成CA证书
echo "-----------------------------生成CA证书----------------------------------"
name="ca"
./CreatePrivateKey $OUTPUT/$name.key
#gmssl ecparam -genkey -name sm2p256v1 -noout -out $OUTPUT/$name.key
gmssl req -new -SM3 -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -days 3650 -sm3 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3_ca -signkey $OUTPUT/$name.key -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req
echo "-----------------------------Server签名证书----------------------------------"
# Server签名证书
name="server_sign"
./CreatePrivateKey $OUTPUT/$name.key
#gmssl ecparam -name sm2p256v1 -genkey -noout -out $OUTPUT/$name.key
gmssl req -new -SM3 -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -SM3 -days 3650 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3_req -CA $OUTPUT/ca.cer -CAkey $OUTPUT/ca.key -set_serial 1000000001 -extfile $rootPath/openssl.cnf -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req
echo "-----------------------------Server加密证书----------------------------------"
# Server加密证书
name="server_encode"
./CreatePrivateKey $OUTPUT/$name.key
#gmssl ecparam -name sm2p256v1 -genkey -noout -out $OUTPUT/$name.key
gmssl req -new -SM3 -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -SM3 -days 3650 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3enc_req -CA $OUTPUT/ca.cer -CAkey $OUTPUT/ca.key -set_serial 1000000001 -extfile openssl.cnf -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req
echo "-----------------------------客户端证书----------------------------------"
# 客户端证书
name="client"
./CreatePrivateKey $OUTPUT/$name.key
#gmssl ecparam -name sm2p256v1 -genkey -noout -out $OUTPUT/$name.key
gmssl req -new -SM3 -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -SM3 -days 3650 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3_req -CA $OUTPUT/ca.cer -CAkey $OUTPUT/ca.key -set_serial 1000000001 -extfile openssl.cnf -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req标密生成脚本
rootPath=$(cd "$(dirname "$0")"; pwd)
#删除打包数据目录
OUTPUT=$rootPath/build
rm -drf $OUTPUT
mkdir $OUTPUT
#CreatePrivateKey是由工程 go build main.go utils.go x509.go ber.go pkcs8.go pkcs7.go pkcs1.go
# 生成CA证书
echo "-----------------------------生成CA证书----------------------------------"
name="standard_ca"
gmssl genrsa -out $OUTPUT/$name.key 2048
gmssl req -new -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -days 3650 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3_ca -signkey $OUTPUT/$name.key -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req
echo "-----------------------------Server签名证书----------------------------------"
# Server签名证书
name="standard_server_sign"
gmssl genrsa -out $OUTPUT/$name.key 2048
gmssl req -new -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -days 3650 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3_req -CA $OUTPUT/standard_ca.cer -CAkey $OUTPUT/standard_ca.key -set_serial 1000000001 -extfile $rootPath/openssl.cnf -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req
echo "-----------------------------客户端证书----------------------------------"
# 客户端证书
name="standard_client"
gmssl genrsa -out $OUTPUT/$name.key 2048
gmssl req -new -key $OUTPUT/$name.key -out $OUTPUT/$name.req -subj /C=CN/ST=JS/L=NJ/O=NJ/CN="127.0.0.1"
gmssl x509 -req -days 3650 -in $OUTPUT/$name.req -extfile ./openssl.cnf -extensions v3_req -CA $OUTPUT/standard_ca.cer -CAkey $OUTPUT/standard_ca.key -set_serial 1000000001 -extfile $rootPath/openssl.cnf -out $OUTPUT/$name.cer
gmssl x509 -in $OUTPUT/$name.cer -text -noout
rm -f $OUTPUT/$name.req
测试结果

openssl.cnf
#
# OpenSSL example configuration file.
# This is mostly being used for generation of certificate requests.
#
# This definition stops the following lines choking if HOME isn't
# defined.
HOME = .
RANDFILE = $ENV::HOME/.rnd
# Extra OBJECT IDENTIFIER info:
#oid_file = $ENV::HOME/.oid
oid_section = new_oids
# To use this configuration file with the "-extfile" option of the
# "openssl x509" utility, name here the section containing the
# X.509v3 extensions to use:
# extensions =
# (Alternatively, use a configuration file that has only
# X.509v3 extensions in its main [= default] section.)
[ new_oids ]
# We can add new OIDs in here for use by 'ca', 'req' and 'ts'.
# Add a simple OID like this:
# testoid1=1.2.3.4
# Or use config file substitution like this:
# testoid2=$testoid1.5.6
# Policies used by the TSA examples.
tsa_policy1 = 1.2.3.4.1
tsa_policy2 = 1.2.3.4.5.6
tsa_policy3 = 1.2.3.4.5.7
####################################################################
[ ca ]
default_ca = CA_default # The default ca section
####################################################################
[ CA_default ]
dir = /usr/local/gmzs2 # Where everything is kept
certs = $dir/certs # Where the issued certs are kept
crl_dir = $dir/crl # Where the issued crl are kept
database = $dir/index.txt # database index file.
#unique_subject = no # Set to 'no' to allow creation of
# several certs with same subject.
new_certs_dir = $dir/newcerts # default place for new certs.
certificate = $dir/cacert.pem # The CA certificate
serial = $dir/serial # The current serial number
crlnumber = $dir/crlnumber # the current crl number
# must be commented out to leave a V1 CRL
crl = $dir/crl.pem # The current CRL
private_key = $dir/private/cakey.pem # The private key
RANDFILE = $dir/private/.rand # private random number file
x509_extensions = usr_cert # The extensions to add to the cert
# Comment out the following two lines for the "traditional"
# (and highly broken) format.
name_opt = ca_default # Subject Name options
cert_opt = ca_default # Certificate field options
# Extension copying option: use with caution.
# copy_extensions = copy
# Extensions to add to a CRL. Note: Netscape communicator chokes on V2 CRLs
# so this is commented out by default to leave a V1 CRL.
# crlnumber must also be commented out to leave a V1 CRL.
# crl_extensions = crl_ext
default_days = 365 # how long to certify for
default_crl_days= 30 # how long before next CRL
default_md = default # use public key default MD
preserve = no # keep passed DN ordering
# A few difference way of specifying how similar the request should look
# For type CA, the listed attributes must be the same, and the optional
# and supplied fields are just that :-)
policy = policy_match
# For the CA policy
[ policy_match ]
countryName = match
stateOrProvinceName = match
organizationName = match
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
# For the 'anything' policy
# At this point in time, you must list all acceptable 'object'
# types.
[ policy_anything ]
countryName = optional
stateOrProvinceName = optional
localityName = optional
organizationName = optional
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
####################################################################
[ req ]
default_bits = 2048
default_keyfile = privkey.pem
distinguished_name = req_distinguished_name
attributes = req_attributes
x509_extensions = v3_ca # The extensions to add to the self signed cert
# Passwords for private keys if not present they will be prompted for
# input_password = secret
# output_password = secret
# This sets a mask for permitted string types. There are several options.
# default: PrintableString, T61String, BMPString.
# pkix : PrintableString, BMPString (PKIX recommendation before 2004)
# utf8only: only UTF8Strings (PKIX recommendation after 2004).
# nombstr : PrintableString, T61String (no BMPStrings or UTF8Strings).
# MASK:XXXX a literal mask value.
# WARNING: ancient versions of Netscape crash on BMPStrings or UTF8Strings.
string_mask = utf8only
# req_extensions = v3_req # The extensions to add to a certificate request
[ req_distinguished_name ]
countryName = Country Name (2 letter code)
countryName_default = CN
countryName_min = 2
countryName_max = 2
stateOrProvinceName = State or Province Name (full name)
stateOrProvinceName_default = Some-State
localityName = Locality Name (eg, city)
0.organizationName = Organization Name (eg, company)
0.organizationName_default = Internet Widgits Pty Ltd
# we can do this but it is not needed normally :-)
#1.organizationName = Second Organization Name (eg, company)
#1.organizationName_default = World Wide Web Pty Ltd
organizationalUnitName = Organizational Unit Name (eg, section)
#organizationalUnitName_default =
commonName = Common Name (e.g. server FQDN or YOUR name)
commonName_max = 64
emailAddress = Email Address
emailAddress_max = 64
# SET-ex3 = SET extension number 3
[ req_attributes ]
challengePassword = A challenge password
challengePassword_min = 4
challengePassword_max = 20
unstructuredName = An optional company name
[ usr_cert ]
# These extensions are added when 'ca' signs a request.
# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.
# This is OK for an SSL server.
# nsCertType = server
# For an object signing certificate this would be used.
# nsCertType = objsign
# For normal client use this is typical
# nsCertType = client, email
# and for everything including object signing:
# nsCertType = client, email, objsign
# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment
# keyUsage = digitalSignature
keyUsage = keyEncipherment
# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"
# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move
# Copy subject details
# issuerAltName=issuer:copy
#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName
# This is required for TSA certificates.
# extendedKeyUsage = critical,timeStamping
[ v3_req ]
# Extensions to add to a certificate request
basicConstraints = CA:FALSE
keyUsage = nonRepudiation, digitalSignature
subjectAltName = @alt_names
[ v3enc_req ]
# Extensions to add to a certificate request
basicConstraints = CA:FALSE
keyUsage = keyAgreement, keyEncipherment, dataEncipherment
subjectAltName = @alt_names
[ alt_names ]
IP.1 = 127.0.0.1
[ v3_ca ]
# Extensions for a typical CA
subjectAltName = @alt_names
# PKIX recommendation.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid:always,issuer
basicConstraints = critical,CA:true
# Key usage: this is typical for a CA certificate. However since it will
# prevent it being used as an test self-signed certificate it is best
# left out by default.
keyUsage = cRLSign, keyCertSign
# Some might want this also
# nsCertType = sslCA, emailCA
# Include email address in subject alt name: another PKIX recommendation
# subjectAltName=email:copy
# Copy issuer details
# issuerAltName=issuer:copy
# DER hex encoding of an extension: beware experts only!
# obj=DER:02:03
# Where 'obj' is a standard or added object
# You can even override a supported extension:
# basicConstraints= critical, DER:30:03:01:01:FF
[ crl_ext ]
# CRL extensions.
# Only issuerAltName and authorityKeyIdentifier make any sense in a CRL.
# issuerAltName=issuer:copy
authorityKeyIdentifier=keyid:always
[ proxy_cert_ext ]
# These extensions should be added when creating a proxy certificate
# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.
# This is OK for an SSL server.
# nsCertType = server
# For an object signing certificate this would be used.
# nsCertType = objsign
# For normal client use this is typical
# nsCertType = client, email
# and for everything including object signing:
# nsCertType = client, email, objsign
# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment
# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"
# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move
# Copy subject details
# issuerAltName=issuer:copy
#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName
# This really needs to be in place for it to be a proxy certificate.
proxyCertInfo=critical,language:id-ppl-anyLanguage,pathlen:3,policy:foo
####################################################################
[ tsa ]
default_tsa = tsa_config1 # the default TSA section
[ tsa_config1 ]
# These are used by the TSA reply generation only.
dir = ./demoCA # TSA root directory
serial = $dir/tsaserial # The current serial number (mandatory)
crypto_device = builtin # OpenSSL engine to use for signing
signer_cert = $dir/tsacert.pem # The TSA signing certificate
# (optional)
certs = $dir/cacert.pem # Certificate chain to include in reply
# (optional)
signer_key = $dir/private/tsakey.pem # The TSA private key (optional)
signer_digest = sm3 # Signing digest to use. (Optional)
default_policy = tsa_policy1 # Policy if request did not specify it
# (optional)
other_policies = tsa_policy2, tsa_policy3 # acceptable policies (optional)
digests = sm3, sha256, sha384, sha512 # Acceptable message digests (mandatory)
accuracy = secs:1, millisecs:500, microsecs:100 # (optional)
clock_precision_digits = 0 # number of digits after dot. (optional)
ordering = yes # Is ordering defined for timestamps?
# (optional, default: no)
tsa_name = yes # Must the TSA name be included in the reply?
# (optional, default: no)
ess_cert_id_chain = no # Must the ESS cert id chain be included?
# (optional, default: no)以上是关于GO (国密,标准Https) 单向,双向认证Demo的主要内容,如果未能解决你的问题,请参考以下文章