sqlmap参数使用TamperAPI
Posted 鹰潭
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了sqlmap参数使用TamperAPI相关的知识,希望对你有一定的参考价值。
sqlmap
sqlmap is released under the terms of the GPLv2, which means that any derivative work must be distributed without further restrictions on the rights granted by the General Public License itself.
下载&升级
git clone --depth 1 https://github.com/sqlmapproject/sqlmap.git sqlmap-dev
pip install --upgrade sqlmap
python sqlmap.py --update
git pull
获取帮助
python sqlmap.py -h
python sqlmap.py -hh
使用
Usage: python sqlmap.py [options]
Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: 0-6 (default 1)
确定目标
Target:
At least one of these options has to be provided to define the target(s)
至少使用下列一个选项用来确定目标
-u URL, --url=URL Target URL (e.g. "http://www.site.com/vuln.php?id=1")
-d DIRECT Connection string for direct database connection
直接数据库连接的连接字符串
-l LOGFILE Parse target(s) from Burp or WebScarab proxy log file
通过Burp或WebScarab的日志文件确定目标
-m BULKFILE Scan multiple targets given in a textual file
通过给出的txt文件扫描多个目标
-r REQUESTFILE Load HTTP request from a file
从一个文件中加载HTTP请求
-g GOOGLEDORK Process Google dork results as target URLs
将Google Dork结果作为目标URL进行处理
-c CONFIGFILE Load options from a configuration INI file
从配置INI文件中加载选项
请求配置
Request:
These options can be used to specify how to connect to the target URL
-A AGENT, --user.. HTTP User-Agent header value
-H HEADER, --hea.. Extra header (e.g. "X-Forwarded-For: 127.0.0.1")
--method=METHOD Force usage of given HTTP method (e.g. PUT)
--data=DATA Data string to be sent through POST (e.g. "id=1")
--param-del=PARA.. Character used for splitting parameter values (e.g. &)
--cookie=COOKIE HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--cookie-del=COO.. Character used for splitting cookie values (e.g. ;)
--live-cookies=L.. Live cookies file used for loading up-to-date values
--load-cookies=L.. File containing cookies in Netscape/wget format
--drop-set-cookie Ignore Set-Cookie header from response
--mobile Imitate smartphone through HTTP User-Agent header
--random-agent Use randomly selected HTTP User-Agent header value
--host=HOST HTTP Host header value
--referer=REFERER HTTP Referer header value
--headers=HEADERS Extra headers (e.g. "Accept-Language: fr\\nETag: 123")
--auth-type=AUTH.. HTTP authentication type (Basic, Digest, NTLM or PKI)
--auth-cred=AUTH.. HTTP authentication credentials (name:password)
--auth-file=AUTH.. HTTP authentication PEM cert/private key file
--ignore-code=IG.. Ignore (problematic) HTTP error code (e.g. 401)
--ignore-proxy Ignore system default proxy settings
--ignore-redirects Ignore redirection attempts
--ignore-timeouts Ignore connection timeouts
--proxy=PROXY Use a proxy to connect to the target URL
--proxy-cred=PRO.. Proxy authentication credentials (name:password)
--proxy-file=PRO.. Load proxy list from a file
--proxy-freq=PRO.. Requests between change of proxy from a given list
--tor Use Tor anonymity network
--tor-port=TORPORT Set Tor proxy port other than default
--tor-type=TORTYPE Set Tor proxy type (HTTP, SOCKS4 or SOCKS5 (default))
--check-tor Check to see if Tor is used properly
--delay=DELAY Delay in seconds between each HTTP request
--timeout=TIMEOUT Seconds to wait before timeout connection (default 30)
--retries=RETRIES Retries when the connection timeouts (default 3)
--randomize=RPARAM Randomly change value for given parameter(s)
--safe-url=SAFEURL URL address to visit frequently during testing
--safe-post=SAFE.. POST data to send to a safe URL
--safe-req=SAFER.. Load safe HTTP request from a file
--safe-freq=SAFE.. Regular requests between visits to a safe URL
--skip-urlencode Skip URL encoding of payload data
--csrf-token=CSR.. Parameter used to hold anti-CSRF token
--csrf-url=CSRFURL URL address to visit for extraction of anti-CSRF token
--csrf-method=CS.. HTTP method to use during anti-CSRF token page visit
--csrf-retries=C.. Retries for anti-CSRF token retrieval (default 0)
--force-ssl Force usage of SSL/HTTPS
--chunked Use HTTP chunked transfer encoded (POST) requests
--hpp Use HTTP parameter pollution method
--eval=EVALCODE Evaluate provided Python code before the request (e.g.
"import hashlib;id2=hashlib.md5(id).hexdigest()")
优化
Optimization:
These options can be used to optimize the performance of sqlmap
这些选项可以优化sqlmap的性能
-o Turn on all optimization switches
打开所有优化开关
--predict-output Predict common queries output
预测常见的查询输出
--keep-alive Use persistent HTTP(s) connections
--null-connection Retrieve page length without actual HTTP response body
检索页面长度,无需实际HTTP响应正文
--threads=THREADS Max number of concurrent HTTP(s) requests (default 1)
注入
Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts
这些选项可用于指定要测试的参数、提供自定义注入有效负载和可选篡改脚本。
-p TESTPARAMETER Testable parameter(s)
--skip=SKIP Skip testing for given parameter(s)
--skip-static Skip testing parameters that not appear to be dynamic
--param-exclude=.. Regexp to exclude parameters from testing (e.g. "ses")
--param-filter=P.. Select testable parameter(s) by place (e.g. "POST")
--dbms=DBMS Force back-end DBMS to provided value
强制后端的DBMS提供值
--dbms-cred=DBMS.. DBMS authentication credentials (user:password)
--os=OS Force back-end DBMS operating system to provided value
--invalid-bignum Use big numbers for invalidating values
--invalid-logical Use logical operations for invalidating values
--invalid-string Use random strings for invalidating values
--no-cast Turn off payload casting mechanism
--no-escape Turn off string escaping mechanism
--prefix=PREFIX Injection payload prefix string
--suffix=SUFFIX Injection payload suffix string
--tamper=TAMPER Use given script(s) for tampering injection data
检测
Detection:
These options can be used to customize the detection phase
这些选项可用于自定义检测阶段
--level=LEVEL Level of tests to perform (1-5, default 1)
--risk=RISK Risk of tests to perform (1-3, default 1)
--string=STRING String to match when query is evaluated to True
--not-string=NOT.. String to match when query is evaluated to False
--regexp=REGEXP Regexp to match when query is evaluated to True
--code=CODE HTTP code to match when query is evaluated to True
--smart Perform thorough tests only if positive heuristic(s)
--text-only Compare pages based only on the textual content
--titles Compare pages based only on their titles
技术
Techniques:
These options can be used to tweak testing of specific SQL injection
techniques
这些选项可用于调整特定SQL注入的测试技术
--technique=TECH.. SQL injection techniques to use (default "BEUSTQ")
--time-sec=TIMESEC Seconds to delay the DBMS response (default 5)
--union-cols=UCOLS Range of columns to test for UNION query SQL injection
--union-char=UCHAR Character to use for bruteforcing number of columns
--union-from=UFROM Table to use in FROM part of UNION query SQL injection
--dns-domain=DNS.. Domain name used for DNS exfiltration attack
--second-url=SEC.. Resulting page URL searched for second-order response
搜索二阶响应的结果页面URL
--second-req=SEC.. Load second-order HTTP request from file
指纹
Fingerprint:
-f, --fingerprint Perform an extensive DBMS version fingerprint
枚举
Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables
这些选项可用于枚举表中包含的后端数据库管理系统信息、结构和数据
-a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--hostname Retrieve DBMS server hostname
--is-dba Detect if the DBMS current user is DBA
--users Enumerate DBMS users
--passwords Enumerate DBMS users password hashes
--privileges Enumerate DBMS users privileges
--roles Enumerate DBMS users roles
--dbs Enumerate DBMS databases
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--count Retrieve number of entries for table(s)
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
--search Search column(s), table(s) and/or database name(s)
--comments Check for DBMS comments during enumeration
--statements Retrieve SQL statements being run on DBMS
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate
-X EXCLUDE DBMS database identifier(s) to not enumerate
-U USER DBMS user to enumerate
--exclude-sysdbs Exclude DBMS system databases when enumerating tables
--pivot-column=P.. Pivot column name
--where=DUMPWHERE Use WHERE condition while table dumping
--start=LIMITSTART First dump table entry to retrieve
--stop=LIMITSTOP Last dump table entry to retrieve
--first=FIRSTCHAR First query output word character to retrieve
--last=LASTCHAR Last query output word character to retrieve
--sql-query=SQLQ.. SQL statement to be executed
--sql-shell Prompt for an interactive SQL shell
--sql-file=SQLFILE Execute SQL statements from given file(s)
暴力攻击
Brute force:
These options can be used to run brute force checks
这些选项被用于暴力攻击
--common-tables Check existence of common tables
--common-columns Check existence of common columns
--common-files Check existence of common files
用户自定义函数注入
User-defined function injection:
These options can be used to create custom user-defined functions
这些选项可用于创建自定义用户定义的函数
--udf-inject Inject custom user-defined functions
--shared-lib=SHLIB Local path of the shared library
文件系统访问
File system access:
These options can be used to access the back-end database management
system underlying file system
这些选项用于访问数据库管理系统后潜在的文件系统
--file-read=FILE.. Read a file from the back-end DBMS file system
--file-write=FIL.. Write a local file on the back-end DBMS file system
--file-dest=FILE.. Back-end DBMS absolute filepath to write to
操作系统访问
Windows registry access:
These options can be used to access the back-end database management
system Windows registry
--reg-read Read a Windows registry key value
--reg-add Write a Windows registry key value data
--reg-del Delete a Windows registry key value
--reg-key=REGKEY Windows registry key
--reg-value=REGVAL Windows registry key value
--reg-data=REGDATA Windows registry key value data
--reg-type=REGTYPE Windows registry key value type
全局设置
General:
These options can be used to set some general working parameters
-s SESSIONFILE Load session from a stored (.sqlite) file
-t TRAFFICFILE Log all HTTP traffic into a textual file
--answers=ANSWERS Set predefined answers (e.g. "quit=N,follow=N")
--base64=BASE64P.. Parameter(s) containing Base64 encoded data
--base64-safe Use URL and filename safe Base64 alphabet (RFC 4648)
--batch Never ask for user input, use the default behavior
--binary-fields=.. Result fields having binary values (e.g. "digest")
--check-internet Check Internet connection before assessing the target
--cleanup Clean up the DBMS from sqlmap specific UDF and tables
--crawl=CRAWLDEPTH Crawl the website starting from the target URL
--crawl-exclude=.. Regexp to exclude pages from crawling (e.g. "logout")
--csv-del=CSVDEL Delimiting character used in CSV output (default ",")
--charset=CHARSET Blind SQL injection charset (e.g. "0123456789abcdef")
--dump-format=DU.. Format of dumped data (CSV (default), html or SQLITE)
--encoding=ENCOD.. Character encoding used for data retrieval (e.g. GBK)
--eta Display for each output the estimated time of arrival
--flush-session Flush session files for current target
--forms Parse and test forms on target URL
--fresh-queries Ignore query results stored in session file
--gpage=GOOGLEPAGE Use Google dork results from specified page number
--har=HARFILE Log all HTTP traffic into a HAR file
--hex Use hex conversion during data retrieval
--output-dir=OUT.. Custom output directory path
--parse-errors Parse and display DBMS error messages from responses
--preprocess=PRE.. Use given script(s) for preprocessing (request)
--postprocess=PO.. Use given script(s) for postprocessing (response)
--repair Redump entries having unknown character marker (?)
--save=SAVECONFIG Save options to a configuration INI file
--scope=SCOPE Regexp for filtering targets
--skip-heuristics Skip heuristic detection of SQLi/XSS vulnerabilities
--skip-waf Skip heuristic detection of WAF/IPS protection
--table-prefix=T.. Prefix used for temporary tables (default: "sqlmap")
--test-filter=TE.. Select tests by payloads and/or titles (e.g. ROW)
--test-skip=TEST.. Skip tests by payloads and/or titles (e.g. BENCHMARK)
--web-root=WEBROOT Web server document root directory (e.g. "/var/www")
混杂选项
Miscellaneous:
These options do not fit into any other category
-z MNEMONICS Use short mnemonics (e.g. "flu,bat,ban,tec=EU")
--alert=ALERT Run host OS command(s) when SQL injection is found
--beep Beep on question and/or when SQLi/XSS/FI is found
--dependencies Check for missing (optional) sqlmap dependencies
--disable-coloring Disable console output coloring
--list-tampers Display list of available tamper scripts
--offline Work in offline mode (only use session data)
--purge Safely remove all content from sqlmap data directory
--results-file=R.. Location of CSV results file in multiple targets mode
--shell Prompt for an interactive sqlmap shell
--tmp-dir=TMPDIR Local directory for storing temporary files
--unstable Adjust options for unstable connections
--update Update sqlmap
--wizard Simple wizard interface for beginner users
常用命令
python sqlmap.py -u "http://www.target.com/vuln.php" --user -v 2 --method=POST --data="id=1" --param-del=";"
python sqlmap.py --url "http://www.target.com/vuln.php?id=1*" --user -vv
python sqlmap.py --url "http://www.target.com/vuln.php?id=1" -p id
python sqlmap.py --url "http://www.target.com/vuln.php?id=1&username=name" --skip “username,id”
python sqlmap.py -l "log_file" --user
python sqlmap.py -m "multiples_file"
python sqlmap.py -r "request_file"
waybackurls www.target.com | python sqlmap.py # from piped-input
python sqlmap.py -g "inurl:\\".php?id=1\\"" # from Google dork
python sqlmap.py -c sqlmap.conf # from a configuration INI file
# multiples_file
www.target1.com/vuln1.php?q=foobar
www.target2.com/vuln2.asp?id=1
www.target3.com/vuln3/id/1*
# requsetfile
POST /vuln.php HTTP/1.1
Host: www.target.com
User-Agent: Mozilla/4.0
id=1
直连数据库
python sqlmap.py -d "mysql://admin:admin@192.168.21.17:3306/testdb" -f --banner --dbs --user
cookie
--cookie, --cookie-del, --live-cookies, --load-cookies and --drop-set-cookie
user-agent
--user-agent, --random-agent
--host
--referer
--headers
HTTP认证
The three supported HTTP protocol authentication mechanisms are:
-
Basic -
Digest -
NTLM
python sqlmap.py -u "http://192.168.136.131/sqlmap/mysql/basic/get_int.php?id=1"、
--auth-type Basic --auth-cred "testuser:testpass"
HTTP协议私钥身份验证
–auth-file=key_file.txt
使用代理
--proxy, --proxy-cred, --proxy-file and --ignore-proxy
Tor 匿名网络
--tor, --tor-port, --tor-type and --check-tor
网络延迟设置
Option: --delay 默认没有延迟设置
在超时之前等待的秒数
Option: --timeout=30
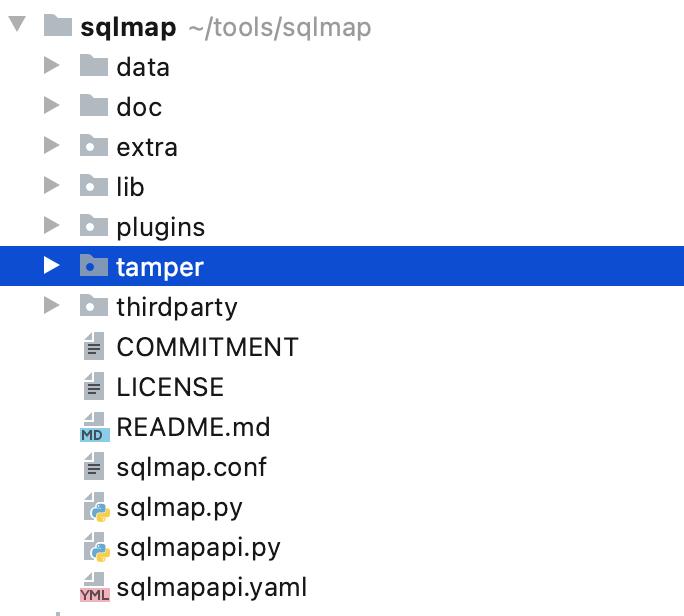
tamper脚本
tamper 脚本在sqlmap的tamper目录之下,写tamper脚本需要定义一个优先级和两个函数
tamper脚本实例:
#!/usr/bin/env python
"""
Copyright (c) 2006-2021 sqlmap developers (http://sqlmap.org/)
See the file 'LICENSE' for copying permission
"""
from lib.core.convert import encodeBase64
from lib.core.enums import PRIORITY
# 这两个库的位置在sqlmap主目录下lib目录中,可以调用其他第三方库
__priority__ = PRIORITY.LOW
# 七个等级:LOWEST、LOWER、LOW、NORMAL、HIGH、HIGHER、HIGHEST
# 加载多个tamper,谁的优先级高,谁被优先使用
def dependencies():
pass # dependencies函数声明该脚本适用/不适用的范围,可以为空。
def tamper(payload, **kwargs):
"""
Base64-encodes all characters in a given payload
>>> tamper("1' AND SLEEP(5)#")
'MScgQU5EIFNMRUVQKDUpIw=='
"""
return encodeBase64(payload, binary=False) if payload else payload
# 传入值为原payload字符串,返回值值为经过加工后的payload
使用tamper脚本
python sqlmap.py --url "http://www.target.com/vuln.php?id=1*" --tamper "space2commet,versionedmorekeywords.py"
sqlmap API
sqlmap API 本质是sqlmap打开一个web服务器,然后通过使用http协议与客户端进行交互
开启sqlmap API
python sqlmapapi.py -s
python sqlmapapi.py -s -H "0.0.0.0" -p 8775
sqlmap 客户端命令行模式
python sqlmapapi.py -c
python sqlmapapi.py -c -H "192.168.1.101" -p 8775
命令行接口模式命令
api> help
help 显示帮助信息
new ARGS 开启一个新的扫描任务
use TASKID 切换taskid
data 获取当前任务返回的数据
log 获取当前任务的扫描日志
status 获取当前任务的扫描状态
option OPTION 获取当前任务的选项
options 获取当前任务的所有配置信息
stop 停止当前任务
kill 杀死当前任务
list 显示所有任务列表
flush 清空所有任务
exit 退出客户端
基于HTTP协议的接口模式:
## “@get”就说明需要通过GET请求的,“@post”就说明需要通过POST请求的;
## POST请求需要修改HTTP头中的Content-Type字段为application/json
#辅助
@get('/error/401')
@get("/task/new")
@get("/task/<taskid>/delete")
#Admin 命令
@get("/admin/list")
@get("/admin/<token>/list")
@get("/admin/flush")
@get("/admin/<token>/flush")
#sqlmap 核心交互命令
@get("/option/<taskid>/list")
@post("/option/<taskid>/get")
@post("/option/<taskid>/set")
@post("/scan/<taskid>/start")
@get("/scan/<taskid>/stop")
@get("/scan/<taskid>/kill")
@get("/scan/<taskid>/status")
@get("/scan/<taskid>/data")
@get("/scan/<taskid>/log/<start>/<end>")
@get("/scan/<taskid>/log")
@get("/download/<taskid>/<target>/<filename:path>")
脚本实例:
import requsets
r = requests.get("http://ip:port/task/new") # 创建新任务
print(r.json()) # {"success": True, "taskid": taskid}
r = requests.post("http://ip:port/task/taskid/start", data=json.dump{"url":"http://host:port/target.php","data":"keyword=1"})
# 开启新任务
剩下的,大家自行摸索吧
以上是关于sqlmap参数使用TamperAPI的主要内容,如果未能解决你的问题,请参考以下文章