Ansible 安全 之ssh登录二次验证
Posted 我的紫霞辣辣
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Ansible 安全 之ssh登录二次验证相关的知识,希望对你有一定的参考价值。
Ansible 安全 之【ssh登录二次验证】
本次二次认证方式使用 Google 身份验证器
配置ssh二次登陆验证
同步时间
# 下载同步时间命令
yum -y install ntpdate
# 同步时间
/usr/sbin/ntpdate asia.pool.ntp.org >>/var/log/ntpdate.log
安装依赖包
yum install pam-devel make gcc-c++ wget -y
下载谷歌身份验证器包
wget https://github.com/google/google-authenticator-libpam/archive/1.03.tar.gz
编译安装
tar zxf 1.03.tar.gz
cd google-authenticator-libpam-1.03
./bootstrap.sh
./configure
make
make install
复制google 身份验证器pam模块到系统下
cp /usr/local/lib/security/pam_google_authenticator.so /lib64/security/
修改ssh的pam登录模块为pam_google_authenticator.so
vim /etc/pam.d/sshd
#%PAM-1.0
#auth required pam_sepermit.so
auth required pam_google_authenticator.so
auth substack password-auth
auth include postlogin
# Used with polkit to reauthorize users in remote sessions
-auth optional pam_reauthorize.so prepare
account required pam_nologin.so
account include password-auth
password include password-auth
# pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
# pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open env_params
session required pam_namespace.so
session optional pam_keyinit.so force revoke
session include password-auth
session include postlogin
# Used with polkit to reauthorize users in remote sessions
-session optional pam_reauthorize.so prepare
修改ChallengeResponseAuthentication 为yes
sed -i 's#^ChallengeResponseAuthentication no#ChallengeResponseAuthentication yes#' /etc/ssh/sshd_config
生成key,手机app上添加账户所需要的
./google-authenticator
Do you want authentication tokens to be time-based (y/n) y
https://www.google.com/chart?chs=200x200&chld=M|0&cht=qr&chl=otpauth://totp/root@k8s-master-01%3Fsecret%3DTFWWGTCAKGXDDTBPJXDXK24ORY%26issuer%3Dk8s-master-01
# 此处为二维码
Your new secret key is: TFWWGTCAKGXDDTBPJXDXK24ORY
Your verification code is 991953
Your emergency scratch codes are:
76049739
45229095
97222624
43385798
68589293
Do you want me to update your "/root/.google_authenticator" file? (y/n) y
Do you want to disallow multiple uses of the same authentication
token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) y
By default, tokens are good for 30 seconds. In order to compensate for
possible time-skew between the client and the server, we allow an extra
token before and after the current time. If you experience problems with
poor time synchronization, you can increase the window from its default
size of +-1min (window size of 3) to about +-4min (window size of
17 acceptable tokens).
Do you want to do so? (y/n) y
If the computer that you are logging into isn't hardened against brute-force
login attempts, you can enable rate-limiting for the authentication module.
By default, this limits attackers to no more than 3 login attempts every 30s.
Do you want to enable rate-limiting (y/n) y
重启ssh服务(重启后,不要关闭当前窗口,以免配置错误出现登录不了服务器)
service sshd restart
手机端配置:本次使用安卓手机,下载app(google authenticator)并安装。
添加帐号
添加完成后,可以看到每30秒变换一次验证码
登陆验证
ssh 192.168.15.11
Verification code: # 先输入手机端的验证码
Password: # 在输入root密码
Last failed login: Wed Oct 27 15:10:19 CST 2021 from k8s-master-01 on ssh:notty
There was 1 failed login attempt since the last successful login.
Last login: Wed Oct 27 14:56:35 2021 from 192.168.15.1
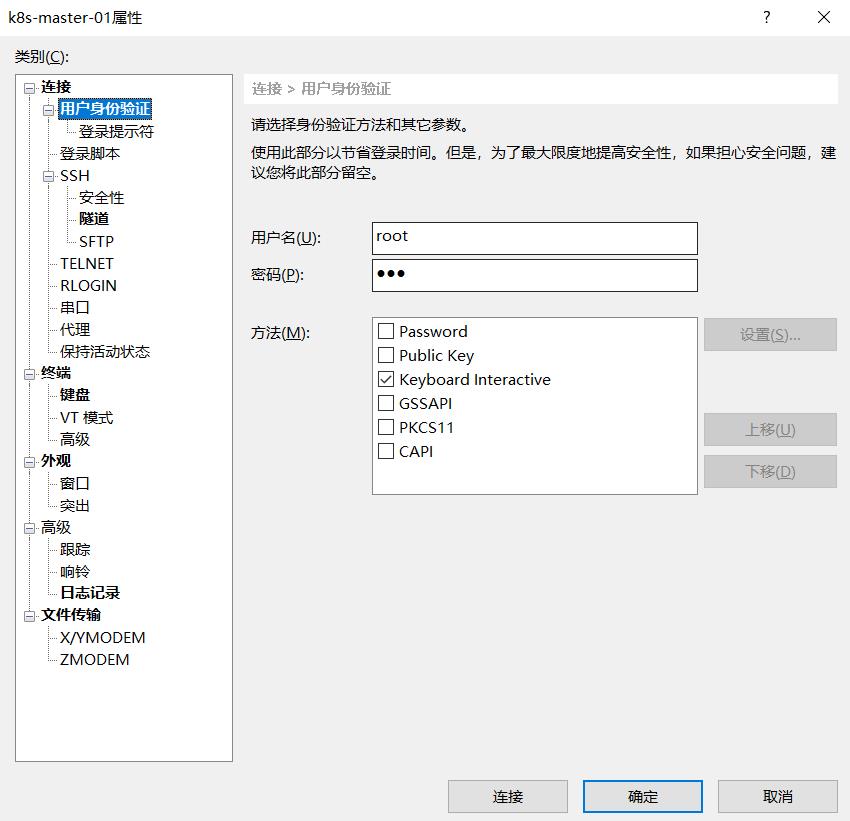
xshell客户端登录
修改用户身份验证方式
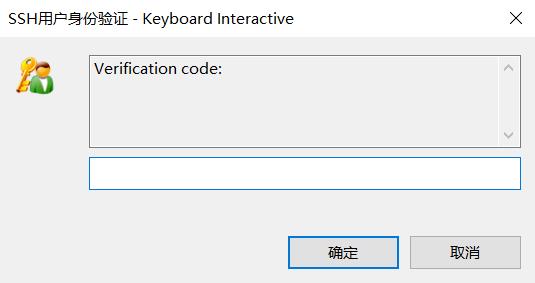
先输入谷歌验证码
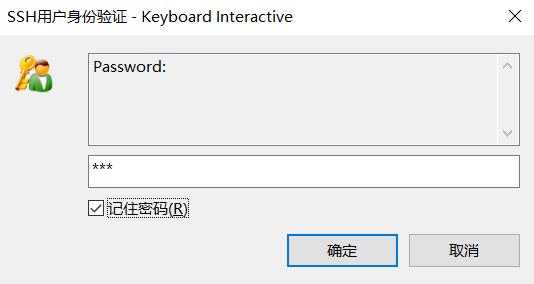
再输入root密码
登陆成功

以上是关于Ansible 安全 之ssh登录二次验证的主要内容,如果未能解决你的问题,请参考以下文章
