linux命令:DNS域名解析,bind
Posted
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了linux命令:DNS域名解析,bind相关的知识,希望对你有一定的参考价值。
DNS:Domain Name Service 域名服务
DNS服务器的软件bind:berkeley internet name domain
named-checkconf:检查配置文件是否有语法错误命令
named-checkzone:检查区域文件是否有语法错误命令
dig:domain information groper
dig -t NS . 查找根域的所有DNS服务器
bind97:
/etc/named.conf 主配置文件
BIND进程的工作属性
区域的定义
/etc/rndc.key
rndc: Remote Name Domain Controller
密钥文件
配置信息:/etc/rndc.conf
/var/named/ 区域数据文件
/etc/rc.d/init.d/named {start|stop|restart|status|reload}
二进制程序:named
bind-chroot:
默认:named
用户:named
组:named
/var/named/chroot/
etc/named.conf
etc/rdnc.key
sbin/named
var/named/
[[email protected] ~]# yum list all |grep bind
This system is not registered with RHN.
RHN support will be disabled.
bind-libs.i386 30:9.3.6-4.P1.el5 installed
bind-utils.i386 30:9.3.6-4.P1.el5 installed
[[email protected] ~]# rpm -e bind-libs bind-utils #rpm -e 卸载软件包
[[email protected] ~]# yum list all |grep bind
This system is not registered with RHN.
RHN support will be disabled.
bind.i386 30:9.3.6-4.P1.el5 Media
bind-chroot.i386 30:9.3.6-4.P1.el5 Media
一、bind安装
bind97下载地址:http://mirrors.ctyun.cn/centos/5/os/i386/CentOS/
[[email protected] ~]# rpm -ivh bind97-libs-9.7.0-21.P2.el5.i386.rpm
warning: bind97-libs-9.7.0-21.P2.el5.i386.rpm: Header V3 DSA signature: NOKEY, key ID e8562897
Preparing... ################################### [100%]
1:bind97-libs ################################# [100%]
[[email protected] ~]# bind97-utils-9.7.0-21.P2.el5.i386.rpm
warning: bind97-utils-9.7.0-21.P2.el5.i386.rpm: Header V3 DSA signature: NOKEY, key ID e8562897
Preparing... ############################## [100%]
1:bind97-utils ############################ [100%]
[[email protected] ~]# rpm -ivh bind97-9.7.0-21.P2.el5.x86_64.rpm
warning: bind97-9.7.0-21.P2.el5.x86_64.rpm: Header V3 DSA signature: NOKEY, key ID e8562897
Preparing... ########################################### [100%]
1:bind97 ########################################### [100%]
二、语法错误判断、日志查看、服务启动状态
[[email protected] etc]# vi named.conf
options {
directory "/var/named";
};
zone "." IN {
type hint;
file "named.ca";
};
zone "localhost" IN {
type master;
file "named.localhost";
};
zone "0.0.127.in-addr.arpa" IN {
type master;
file "named.loopback";
};
[[email protected] etc]# named-checkconf 检查named.conf配置文件是否有语法错误
[[email protected] etc]# named-checkzone "." /var/named/named.ca 检查区域文件是否有语法错误
zone ./IN: has 0 SOA records
zone ./IN: not loaded due to errors.
[[email protected] etc]# named-checkzone "localhost" /var/named/named.localhost
zone localhost/IN: loaded serial 0
OK
[[email protected] etc]# named-checkzone "0.0.127.in-addr.arpa" /var/named/named.loopback
zone 0.0.127.in-addr.arpa/IN: loaded serial 0
OK
[[email protected] etc]# vim /etc/selinux/config #启动服务器需把selinux关闭才能启动
# enforcing - SELinux security policy is enforced.
# permissive - SELinux prints warnings instead of enforcing.
# disabled - SELinux is fully disabled.
SELINUX=permissive #默认为enforcing 需关闭掉,设置为permissive,否则无法启动
[[email protected] etc]# service named start
Starting named: named: already running [ OK ]
[[email protected] etc]# service named restart
Stopping named: . [ OK ]
Starting named: [ OK ]
[[email protected] etc]# tail /var/log/messages
Dec 13 15:37:16 test named[29856]: command channel listening on 127.0.0.1#953
Dec 13 15:37:16 test named[29856]: zone 0.0.127.in-addr.arpa/IN: loaded serial 0
Dec 13 15:37:16 test named[29856]: zone localhost/IN: loaded serial 0
Dec 13 15:37:16 test named[29856]: running
[[email protected] ~]# vi /etc/resolv.conf
nameserver 110.19.131.131
search localdomain
[[email protected] ~]# dig -t NS .
; <<>> DiG 9.7.0-P2-RedHat-9.7.0-21.P2.el5 <<>> -t NS .
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 6718
;; flags: qr rd ra; QUERY: 1, ANSWER: 13, AUTHORITY: 0, ADDITIONAL: 12
;; QUESTION SECTION:
;. IN NS
;; ANSWER SECTION:
. 16803 IN NS i.root-servers.net.
. 16803 IN NS a.root-servers.net.
. 16803 IN NS e.root-servers.net.
. 16803 IN NS k.root-servers.net.
. 16803 IN NS d.root-servers.net.
. 16803 IN NS b.root-servers.net.
. 16803 IN NS g.root-servers.net.
. 16803 IN NS c.root-servers.net.
. 16803 IN NS l.root-servers.net.
. 16803 IN NS h.root-servers.net.
. 16803 IN NS f.root-servers.net.
. 16803 IN NS j.root-servers.net.
. 16803 IN NS m.root-servers.net.
;; ADDITIONAL SECTION:
i.root-servers.net. 86400 IN A 192.36.148.17
i.root-servers.net. 17019 IN AAAA 2001:7fe::53
a.root-servers.net. 17019 IN A 198.41.0.4
a.root-servers.net. 17019 IN AAAA 2001:503:ba3e::2:30
e.root-servers.net. 29300 IN A 192.203.230.10
e.root-servers.net. 86400 IN AAAA 2001:500:a8::e
k.root-servers.net. 29300 IN A 193.0.14.129
k.root-servers.net. 17019 IN AAAA 2001:7fd::1
d.root-servers.net. 29300 IN A 199.7.91.13
d.root-servers.net. 17019 IN AAAA 2001:500:2d::d
b.root-servers.net. 16803 IN A 192.228.79.201
b.root-servers.net. 17019 IN AAAA 2001:500:84::b
;; Query time: 38 msec
;; SERVER: 10.109.131.131#53(10.109.131.131)
;; WHEN: Wed Dec 14 08:14:20 2016
;; MSG SIZE rcvd: 505
[[email protected] ~]# ping www.163.com
PING 163.xdwscache.ourglb0.com (113.107.57.41) 56(84) bytes of data.
64 bytes from 113.107.57.41: icmp_seq=1 ttl=53 time=39.4 ms
64 bytes from 113.107.57.41: icmp_seq=2 ttl=53 time=38.3 ms
--- 163.xdwscache.ourglb0.com ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1013ms
rtt min/avg/max/mdev = 38.381/38.924/39.468/0.578 ms
[[email protected] ~]# chkconfig --list named
named 0:off 1:off 2:off 3:off 4:off 5:off 6:off
[[email protected] ~]# chkconfig named on
[[email protected] ~]# chkconfig --list named
named 0:off 1:off 2:on 3:on 4:on 5:on 6:off
[[email protected] ~]#
三、创建本地NS正向域
[[email protected] ~]# vi /etc/named.conf
... #新增以下部分
zone "johntest.com" IN {
type master;
file "johntest.com.zone";
};
[[email protected] etc]# chown root:named named.conf #修改用户和组
[[email protected] ~]# named-checkconf /etc/named.conf #检查named.conf配置文件是否有语法错误
/etc/named.conf:24: missing ‘;‘ before end of file
[[email protected] named]# vi johntest.com.zone #正向区域名称
$TTL 600 #宏要加$
johntest.com. IN SOA ns1.johntest.com. admin.johntest.com. (
20161214 #系列号
1H #刷新时间
5M #重试时间
2D #过期时间
6H ) #否定TTL值时间 (需用括号括起来)
johntest.com. IN NS ns1.johntest.com.
IN MX 10 mail #域名可省,10为邮件等级
ns1 IN A 10.109.131.131
mail IN A 10.109.131.120
www IN A 10.109.131.201
www IN A 10.109.131.232
ftp IN CNAME www
[[email protected] named]# chown root:named johntest.com.zone
[[email protected] named]# l
总计 8
-rw-r--r-- 1 root named 471 01-09 04:16 johntest.com.zone
四、语创建本地NS反向域
[[email protected] ~]# vi /etc/named.conf
... #新增以下部分
zone "1.168.192.in-addr.arpa" IN {
type master;
file "192.168.1.zone";
};
[[email protected] named]# cp -p johntest.com.zone 192.168.1.zone #将正向复制为反向区域名称
[[email protected] named]# vi johntest.com.zone #修改反向区域名称
$TTL 600 #宏要加$
@ IN SOA ns1.johntest.com. admin.johntest.com. (
20161214
1H
5M
2D
6H )
IN NS ns1.johntest.com. // 最后一项必须是完整的记录,句尾不可忘记写上" . "
3 IN PTR ns1.johntest.com.
3 IN PTR www.johntest.com.
4 IN PTR mail.johntest.com.
5 IN PTR www.johntest.com.
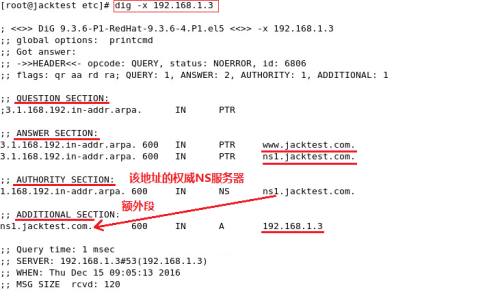
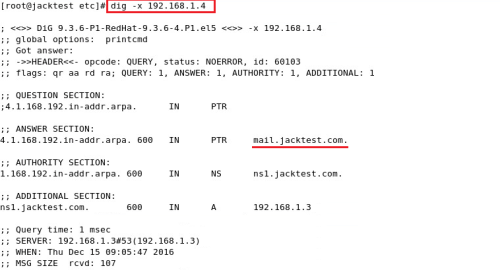
dig -x 192.168.1.3
dig -x 192.168.1.4
dig +norecurse -t A www.163.com @192.168.1.3 #不递归查询
dig +trace -t A www.baidu.com @192.168.1.3 #递归显示查询结果
五、更改配制文件后即可限定查询段
[[email protected] etc]# vi named.conf
options {
directory "/var/named";
allow-recursion { 192.168.1.0/24; }; //只允许此IP段递归查询
};
zone "." IN {
type hint;
file "named.ca";
};
zone "localhost" IN {
type master;
file "named.localhost";
allow-transfer { none; }; //none不允许所有客户端发出传送请求
};
zone "0.0.127.in-addr.arpa" IN {
type master;
file "named.loopback";
allow-transfer { none; };
};
zone "jacktest.com" IN {
type master;
file "jacktest.com.zone";
allow-transfer { 192.168.1.5; }; //只允许此IP发出传送请求
};
zone "1.168.192.in-addr.arpa" IN {
type master;
file "192.168.1.zone";
allow-transfer { 192.168.1.5; };
};
[[email protected] etc]# tail /var/log/messages
Dec 15 14:11:41 test named[7276]: zone 1.168.192.in-addr.arpa/IN: loaded serial 2016121401
Dec 15 14:11:41 test named[7276]: zone jacktest.com/IN: loaded serial 20161214
Dec 15 14:11:41 test named[7276]: zone localhost/IN: loaded serial 0
Dec 15 14:11:41 test named[7276]: running
Dec 15 14:13:31 test named[7276]: client 192.168.1.5#58423: transfer of ‘jacktest.com/IN‘: AXFR started
Dec 15 14:13:31 test named[7276]: client 192.168.1.5#58423: transfer of ‘jacktest.com/IN‘: AXFR ended
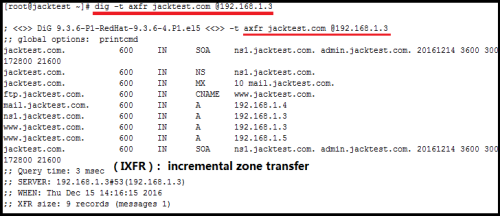
六、设置从DNS服务器
[[email protected] named]# setenforce 0
setenforce: SELinux is disabled
[[email protected] named]# scp 192.168.1.3:/etc/named.conf /etc/
The authenticity of host ‘192.168.1.3 (192.168.1.3)‘ can‘t be established.
RSA key fingerprint is c2:f2:75:5c:ab:4a:43:d3:e1:76:bc:d2:0f:c7:d6:32.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added ‘192.168.1.3‘ (RSA) to the list of known hosts.
[email protected]‘s password:
named.conf
[[email protected] etc]# vi /etc/named.conf
...
zone "jacktest.com" IN {
type slave;
file "slaves/jacktest.com.zone";
allow-transfer { 192.168.1.5; };
};
zone "1.168.192.in-addr.arpa" IN {
type slave;
file "slaves/192.168.1.zone";
allow-transfer { 192.168.1.5; };
};
验证:
[[email protected] slaves]# tail /var/log/messages #192.168.1.3主
Dec 15 15:43:35 test named[7595]: zone 1.168.192.in-addr.arpa/IN: loaded serial 2016121401
Dec 15 15:43:35 test named[7595]: zone jacktest.com/IN: loaded serial 20161214
Dec 15 15:43:35 test named[7595]: zone localhost/IN: loaded serial 0
Dec 15 15:43:35 test named[7595]: running
Dec 15 15:44:12 test named[7595]: client 192.168.1.5#47432: transfer of ‘jacktest.com/IN‘: AXFR started
Dec 15 15:44:12 test named[7595]: client 192.168.1.5#47432: transfer of ‘jacktest.com/IN‘: AXFR ended
Dec 15 17:25:29 test named[7595]: client 192.168.1.5#34268: transfer of ‘jacktest.com/IN‘: AXFR started
Dec 15 17:25:29 test named[7595]: client 192.168.1.5#34268: transfer of ‘jacktest.com/IN‘: AXFR ended
Dec 15 17:25:29 test named[7595]: client 192.168.1.5#59389: transfer of ‘1.168.192.in-addr.arpa/IN‘: AXFR started #传送开始
Dec 15 17:25:29 test named[7595]: client 192.168.1.5#59389: transfer of ‘1.168.192.in-addr.arpa/IN‘: AXFR ended #传送结果
[[email protected] named]# tail /var/log/messages #192.168.1.5
Dec 15 17:28:13 jacktest named[10089]: zone localhost/IN: loaded serial 0
Dec 15 17:28:13 jacktest named[10089]: running
Dec 15 17:28:13 jacktest named[10089]: zone jacktest.com/IN: Transfer started.
Dec 15 17:28:13 jacktest named[10089]: transfer of ‘jacktest.com/IN‘ from 192.168.1.3#53: connected using 192.168.1.5#34268
Dec 15 17:28:13 jacktest named[10089]: zone jacktest.com/IN: transferred serial 20161214
Dec 15 17:28:13 jacktest named[10089]: transfer of ‘jacktest.com/IN‘ from 192.168.1.3#53: Transfer completed: 1 messages, 9 records, 233 bytes, 0.004 secs (58250 bytes/sec)
Dec 15 17:28:13 jacktest named[10089]: zone 1.168.192.in-addr.arpa/IN: Transfer started.
Dec 15 17:28:13 jacktest named[10089]: transfer of ‘1.168.192.in-addr.arpa/IN‘ from 192.168.1.3#53: connected using 192.168.1.5#59389
Dec 15 17:28:13 jacktest named[10089]: zone 1.168.192.in-addr.arpa/IN: transferred serial 2016121401
Dec 15 17:28:13 jacktest named[10089]: transfer of ‘1.168.192.in-addr.arpa/IN‘ from 192.168.1.3#53: Transfer completed: 1 messages, 7 records, 219 bytes, 0.002 secs (109500 bytes/sec)
七、测试NS自动更新到从服务器
[[email protected] named]# vi jacktest.com.zone #192.168.1.3主
$TTL 600
jacktest.com. IN SOA ns1.jacktest.com. admin.jacktest.com. (
2016121404 #3改成4
...
imap IN A 192.168.1.6
haha IN A 192.168.1.7 #新增一条记录
[[email protected] named]# service named reload
Reloading named: [ OK ]
[[email protected] named]# tail /var/log/messages #192.168.1.3主NS
Dec 16 10:05:53 test named[10112]: reloading configuration succeeded
Dec 16 10:05:53 test named[10112]: reloading zones succeeded
Dec 16 10:05:53 test named[10112]: zone jacktest.com/IN: loaded serial 2016121404
Dec 16 10:05:53 test named[10112]: zone jacktest.com/IN: sending notifies (serial 2016121404)
Dec 16 10:05:53 test named[10112]: client 192.168.1.5#50038: transfer of ‘jacktest.com/IN‘: AXFR-style IXFR started
Dec 16 10:05:53 test named[10112]: client 192.168.1.5#50038: transfer of ‘jacktest.com/IN‘: AXFR-style IXFR ended
[[email protected] named]# tail /var/log/messages #192.168.1.5从NS
Dec 16 10:08:38 jacktest named[12536]: client 192.168.1.3#6791: received notify for zone ‘jacktest.com‘
Dec 16 10:08:38 jacktest named[12536]: zone jacktest.com/IN: Transfer started.
Dec 16 10:08:38 jacktest named[12536]: transfer of ‘jacktest.com/IN‘ from 192.168.1.3#53: connected using 192.168.1.5#50038
Dec 16 10:08:38 jacktest named[12536]: zone jacktest.com/IN: transferred serial 2016121404
Dec 16 10:08:38 jacktest named[12536]: transfer of ‘jacktest.com/IN‘ from 192.168.1.3#53: Transfer completed: 1 messages, 13 records, 309 bytes, 0.002 secs (154500 bytes/sec)
Dec 16 10:08:38 jacktest named[12536]: zone jacktest.com/IN: sending notifies (serial 2016121404)
[[email protected] slaves]# cat jacktest.com.zone #192.168.1.5从NS
jacktest.com IN SOA ns1.jacktest.com. admin.jacktest.com. (
2016121404 ; serial
...
ftp CNAME www
haha A 192.168.1.7 #自动学习成功
八、开放远程访问DC
Remote Name Daemon Control # [di:mn]守护进程
[[email protected] ~]# rndc-confgen > /etc/rndc.conf
[[email protected] ~]# cat /etc/rndc.conf
# Start of rndc.conf
key "rndc-key" {
algorithm hmac-md5;
secret "PElKGniJbHk/esQ9zpN+xg==";
};
options {
default-key "rndc-key";
default-server 127.0.0.1;
default-port 953;
};
# End of rndc.conf
# Use with the following in named.conf, adjusting the allow list as needed:
# key "rndc-key" {
# algorithm hmac-md5;
# secret "PElKGniJbHk/esQ9zpN+xg==";
# };
#
# controls {
# inet 127.0.0.1 port 953
# allow { 127.0.0.1; } keys { "rndc-key"; };
# };
# End of named.conf #绿色部分复制添加到named.conf
[[email protected] ~]# rndc -c /etc/rndc.conf status
rndc: connection to remote host closed
This may indicate that
* the remote server is using an older version of the command protocol,
* this host is not authorized to connect,
* the clocks are not synchronized, or
* the key is invalid.
[[email protected] ~]# rm /etc/rndc.key
rm: remove regular file `/etc/rndc.key‘? y
[[email protected] ~]# rndc -c /etc/rndc.conf status
rndc: connection to remote host closed
This may indicate that
* the remote server is using an older version of the command protocol,
* this host is not authorized to connect,
* the clocks are not synchronized, or
* the key is invalid.
[[email protected] ~]# service named restart
Stopping named: . [ OK ]
Generating /etc/rndc.key: [ OK ]
Starting named: [ OK ]
[[email protected] ~]# rndc -c /etc/rndc.conf status
version: 9.7.0-P2-RedHat-9.7.0-21.P2.el5
CPUs found: 8
worker threads: 8
number of zones: 16
debug level: 0
xfers running: 0
xfers deferred: 0
soa queries in progress: 0
query logging is OFF
recursive clients: 0/0/1000
tcp clients: 0/100
server is up and running
[[email protected] ~]# rndc -c /etc/rndc.conf notify "jacktest.com"
zone notify queued
[[email protected] ~]# tail /var/log/messages
Dec 16 10:36:32 test named[10285]: received control channel command ‘notify jacktest.com‘
Dec 16 10:36:32 test named[10285]: zone jacktest.com/IN: sending notifies (serial 2016121404)
[[email protected] ~]# rndc -c /etc/rndc.conf flush
[[email protected] ~]# rndc -c /etc/rndc.conf stop
...
controls {
inet 192.168.1.3 port 953 #监听地址
allow { 192.168.1.5; } keys { "rndc-key"; }; #允许访问192.168.1.3的IP
};
[[email protected] ~]# scp /etc/rndc.conf 192.168.1.5:/root/
[[email protected] ~]# vi /etc/rndc.conf #192.168.1.5从NS
# Start of rndc.conf
key "rndc-key" {
algorithm hmac-md5;
secret "PElKGniJbHk/esQ9zpN+xg==";
};
options {
default-key "rndc-key";
default-server 192.168.1.3;
default-port 953;
};
[[email protected] ~]# rndc -c rndc.conf status #192.168.1.5从NS,已可远程访问
version: 9.7.0-P2-RedHat-9.7.0-21.P2.el5 #一般不开放远程允许访问,非常危险
CPUs found: 8
worker threads: 8
number of zones: 16
debug level: 0
xfers running: 0
xfers deferred: 0
soa queries in progress: 0
query logging is OFF
recursive clients: 0/0/1000
tcp clients: 0/100
server is up and running
[[email protected] ~]#
九、子域及子域转发(forward)
forward {only|first}
forwarders {};
zone "ZONE_NAME" IN {
type forward;
forward first;
forwarders {172.168.1.3};
};
新增子域服务器192.168.1.8
[[email protected] ~]# vi fin.jacktest.com.zone #192.168.1.8 子DNS
$TTL 600 ; 10 minutes
@ IN SOA ns1.fin.jacktest.com. admin.fin.jacktest.com. (
2016121701 ; serial
3600 ; refresh (1 hour)
300 ; retry (5 minutes)
172800 ; expire (2 days)
21600 ; minimum (6 hours)
)
NS ns1.fin.jacktest.com.
MX 10 mail.fin.jacktest.com.
ns1 A 192.168.1.8
mail A 192.168.1.9
www A 192.168.1.10
[[email protected] ~]# service named restart
Stopping named: . [ OK ]
Starting named: [ OK ]
验证子域
[[email protected] named]# dig -t A ns1.fin.jacktest.com @192.168.1.3 #通过主域可解析子域IP
; <<>> DiG 9.7.0-P2-RedHat-9.7.0-21.P2.el5 <<>> -t A ns1.fin.jacktest.com @192.168.1.3
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 57664
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;ns1.fin.jacktest.com. IN A
;; ANSWER SECTION:
ns1.fin.jacktest.com. 600 IN A 192.168.1.8
;; AUTHORITY SECTION:
fin.jacktest.com. 600 IN NS ns1.fin.jacktest.com.
;; Query time: 3 msec
;; SERVER: 192.168.1.3#53(192.168.1.3)
;; WHEN: Sat Dec 17 11:11:13 2016
;; MSG SIZE rcvd: 68
[[email protected] named]# dig -t A ns1.fin.jacktest.com @192.168.1.8 #通过子域可解析子域IP
; <<>> DiG 9.7.0-P2-RedHat-9.7.0-21.P2.el5 <<>> -t A ns1.fin.jacktest.com @192.168.1.8
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 53646
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;ns1.fin.jacktest.com. IN A
;; ANSWER SECTION:
ns1.fin.jacktest.com. 600 IN A 192.168.1.8
;; AUTHORITY SECTION:
fin.jacktest.com. 600 IN NS ns1.fin.jacktest.com.
;; Query time: 2 msec
;; SERVER: 192.168.1.8#53(192.168.1.8)
;; WHEN: Sat Dec 17 11:12:39 2016
;; MSG SIZE rcvd: 68
[[email protected] named]# nslookup
> server 192.168.1.3
Default server: 192.168.1.3
Address: 192.168.1.3#53
> set q=A
> www.jacktest.com
Server: 192.168.1.3 #通过服务器192.168.1.3查找
Address: 192.168.1.3#53
Name: www.jacktest.com #查找出两条记录
Address: 192.168.1.3
Name: www.jacktest.com
Address: 192.168.1.5
> set q=A
> www.fin.jacktest.com
Server: 192.168.1.3 #通过此服务器查找
Address: 192.168.1.3#53
Non-authoritative answer: #查找出一条记录,有为非官方记录
Name: www.fin.jacktest.com
Address: 192.168.1.10
> server 192.168.1.8
Default server: 192.168.1.8
Address: 192.168.1.8#53
> set q=A
> www.fin.jacktest.com
Server: 192.168.1.8 #通过服务器192.168.1.8查找
Address: 192.168.1.8#53
Name: www.fin.jacktest.com #查找出一条记录
Address: 192.168.1.10
> set q=A
> www.jacktest.com #通过子域服务器192.168.1.8查找父域的A记录
Server: 192.168.1.8
Address: 192.168.1.8#53
** server can‘t find www.jacktest.com.localdomain: SERVFAIL #子域无法查找父域的A记录
>
默认子域无法查找父域信息,定义转发即可告诉子域
[[email protected] ~]# vi /etc/rndc.conf #192.168.1.8 子DNS 中新增以下部分
zone "jacktest.com" IN {
type forward;
forward first;
forwarders { 192.168.1.3; };
};
验证:
[[email protected] named]# nslookup
> set q=A
> www.jacktest.com
Server: 192.168.1.8 #通过服务器192.168.1.8查找
Address: 192.168.1.8#53
Non-authoritative answer:
Name: www.jacktest.com #新增forward后查找出两条记录
Address: 192.168.1.5
Name: www.jacktest.com
Address: 192.168.1.3
本文出自 “学linux历程” 博客,请务必保留此出处http://woyaoxuelinux.blog.51cto.com/5663865/1890312
以上是关于linux命令:DNS域名解析,bind的主要内容,如果未能解决你的问题,请参考以下文章