K8S——ETCD部署
Posted
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了K8S——ETCD部署相关的知识,希望对你有一定的参考价值。
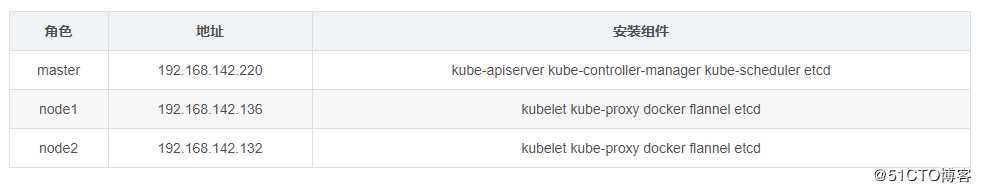
角色分配:
环境部署
所有虚拟机均已关闭防火墙以及selinux核心防护功能
实操
建工作目录存放二进制软件包
[root@master ~]# cd /
[root@master /]# mkdir k8s安装ETCD数据库(三副本机制)
master(下载ca证书创建、管理工具cfssl)
[root@master k8s]# curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
[root@master k8s]# curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
[root@master k8s]# curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
[root@master k8s]# chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo生成ca证书
//定义ca证书,生成ca证书配置文件
[root@master k8s]# cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
//生成证书签名文件
[root@master k8s]# cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
//生成ca证书,ca.pem、ca-key.pem
[root@master k8s]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
[root@master k8s]# ls
ca-config.json ca-csr.json ca.pem ca.csr ca-key.pem
“ca.pem” //ca证书文件
“ca-key.pem” //ca密钥证书文件生成etcd各节点之间通信证书(注意IP地址的变化)
//生成etcd节点之间的通信验证签名
//节点地址必须要更改
[root@master k8s]# cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"192.168.142.220",
"192.168.142.136",
"192.168.142.132"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
//生成ETCD通信证书,用于etcd之间通信验证
[root@master k8s]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
[root@master k8s]# ls
ca-config.json ca-csr.json ca.pem server.csr server-key.pem
ca.csr ca-key.pem etcd-cert.sh server-csr.json server.pem
“server.pem”&“server-key.pem” //etcd之间通信的验证证书配置etcd二进制文件包
//解压安装etcd
[root@master k8s]# tar zxf etcd-v3.3.10-linux-amd64.tar.gz
//建立存放etcd配置文件、命令、证书的目录
[root@master k8s]# mkdir -p /opt/etcd/{cfg,bin,ssl}
[root@master k8s]# ls /opt/etcd/
bin cfg ssl
//将etcd中的文件分门别类存放
[root@master k8s]# mv etcd-v3.3.10-linux-amd64/etcd /opt/etcd/bin/
[root@master k8s]# mv etcd-v3.3.10-linux-amd64/etcdctl /opt/etcd/bin/
[root@master k8s]# cp -p *.pem /opt/etcd/ssl/
//etcd命令文件
[root@master k8s]# ls /opt/etcd/bin/
etcd etcdctl
//etcd证书
[root@master k8s]# ls /opt/etcd/ssl/
ca-key.pem ca.pem server-key.pem server.pem
建立etcd配置文件
[root@master k8s]# cat <<EOF >/opt/etcd/cfg/etcd
//[Member]
ETCD_NAME="etcd01"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.142.220:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.142.220:2379"
//[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.142.220:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.142.220:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.142.220:2380,etcd02=https://192.168.142.136:2380,etcd03=https://192.168.142.132:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
EOF建立etcd启动脚本
[root@master k8s]# cat <<EOF >/usr/lib/systemd/system/etcd.service
[Unit]
Description=Etcd Server
After=network.target
After=network-online.target
Wants=network-online.target
[Service]
Type=notify
EnvironmentFile=/opt/etcd/cfg/etcd
ExecStart=/opt/etcd/bin/etcd --name=etcd01 --data-dir=${ETCD_DATA_DIR} --listen-peer-urls=${ETCD_LISTEN_PEER_URLS} --listen-client-urls=${ETCD_LISTEN_CLIENT_URLS},http://127.0.0.1:2379 --advertise-client-urls=${ETCD_ADVERTISE_CLIENT_URLS} --initial-advertise-peer-urls=${ETCD_INITIAL_ADVERTISE_PEER_URLS} --initial-cluster=${ETCD_INITIAL_CLUSTER} --initial-cluster-token=${ETCD_INITIAL_CLUSTER_TOKEN} --initial-cluster-state=new --cert-file=/opt/etcd/ssl/server.pem --key-file=/opt/etcd/ssl/server-key.pem --peer-cert-file=/opt/etcd/ssl/server.pem --peer-key-file=/opt/etcd/ssl/server-key.pem --trusted-ca-file=/opt/etcd/ssl/ca.pem --peer-trusted-ca-file=/opt/etcd/ssl/ca.pem
Restart=on-failure
LimitNOFILE=65536
[Install]
WantedBy=multi-user.target
EOF推送证书、配置文件、启动脚本至node节点上
//将证书、配置文件推送至其它节点
[root@master ~]# scp -r /opt/etcd/ root@192.168.142.136:/opt/
[root@master ~]# scp -r /opt/etcd/ root@192.168.142.132:/opt/
//推送启动脚本
[root@master ~]# scp /usr/lib/systemd/system/etcd.service root@192.168.142.136:/usr/lib/systemd/system/
[root@master ~]# scp /usr/lib/systemd/system/etcd.service root@192.168.142.132:/usr/lib/systemd/system/node端方面
更改各node节点收到的配置文件
node1
[root@node1 etcd]# vim /opt/etcd/cfg/etcd
//[Member]
ETCD_NAME="etcd02" //节点名称
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.142.136:2380" //节点地址
ETCD_LISTEN_CLIENT_URLS="https://192.168.142.136:2379" //节点地址
//[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.142.136:2380" //节点地址
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.142.136:2379" //节点地址node 2
[root@node2 ~]# vim /opt/etcd/cfg/etcd
//[Member]
ETCD_NAME="etcd03"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.142.132:2380" //节点名称
ETCD_LISTEN_CLIENT_URLS="https://192.168.142.132:2379" //节点名称
//[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.142.132:2380" //节点名称
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.142.132:2379" //节点名称所有节点开启服务
//各节点关防火墙
[root@node1 etcd]# systemctl stop firewalld.service
[root@node1 etcd]# setenforce 0
[root@node1 etcd]# systemctl disable firewalld.service
//开启etcd服务
[root@node1 etcd]# systemctl start etcd
[root@node1 etcd]# systemctl enable etcd群集健康检查,查看群集成员
//群集各节点健康检查
[root@master ~]# /opt/etcd/bin/etcdctl --ca-file=/opt/etcd/ssl/ca.pem --cert-file=/opt/etcd/ssl/server.pem --key-file=/opt/etcd/ssl/server-key.pem --endpoints="https://192.168.142.220:2379,https://192.168.142.136:2379,https://192.168.142.132:2379" cluster-health
//查看etcd群集成员
[root@master ~]# /opt/etcd/bin/etcdctl --ca-file=/opt/etcd/ssl/ca.pem --cert-file=/opt/etcd/ssl/server.pem --key-file=/opt/etcd/ssl/server-key.pem --endpoints="https://192.168.142.220:2379,https://192.168.142.136:2379,https://192.168.142.132:2379" member listetcd群集由此搭建成功!!
以上是关于K8S——ETCD部署的主要内容,如果未能解决你的问题,请参考以下文章