RPC漏洞挖掘案例研究(下)
Posted 嘶吼专业版
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了RPC漏洞挖掘案例研究(下)相关的知识,希望对你有一定的参考价值。
在《》一文中,我们向你展示了如何使用不同的可用工具和在线资源,在Windows RPC服务器中发现潜在的安全风险(微软通用遥测客户端漏洞)。另外,我们还演示了对RPC服务器进行反向汇编所需的一些基本知识。不过,我们坚信RPC服务器中还有其他潜在的安全漏洞。所以,在本篇文章中,我们将继续研究并改进强化Windows RPC服务器的方法,以便发现其他RPC服务器漏洞。
 前言
前言
在本博客系列的第一部分中,我们讨论了我们在FortiGuard实验室中使用的方法,以使用RPCView查找RPC服务器上的逻辑漏洞。因此,我们发现了Microsoft Universal Telemetry服务中的潜在漏洞。
如果你仔细阅读了上篇文章,就会知道我们的分析步骤如下:
1.首先将所有RPC接口从RpcView GUI导出到文本文件,生成的文本文件包含可从RPC服务器调用的所有RPC API。
2.我们从输出文本文件中查找接受宽字符串作为输入的RPC API,直到发现来自diagtrack.dll的一个更有趣的RPC接口。
但是,我们本文的目的不是将所有RPC信息反编译并导出到文本文件中。幸运的是,在阅读源代码时,我们发现其中已经包含了我们需要的功能,但是默认情况下它不会被启用,只能在调试模式下使用特定的命令行参数被触发。由于此限制,RPCView(识别运行在Windows操作系统上的RPC服务的一个非常方便的工具)不会显示默认情况下在Windows上没有自动启动的RPC服务——例如数据共享服务。我们会在本文中,采用一些办法来识别此服务。事实证明,RPC服务还会遇到一些权限升级漏洞,这些漏洞我们都会在下面一一解答。
去年12月,Google安全研究员James Forshaw使用RPCView报告了由MSRC(Microsoft Security Response Center)修复的四个漏洞。因此,虽然使用RPCView仍然有用,但它也很耗时,因为你必须逐字审核所有接受字符串的API。所以我们想找到其他节省时间的方法。
首先,我们分析了一组以前发现的非常相似的漏洞。确定它们之间有一个共同点,因为它们都调用SetNamedSecurityInfo Windows API,该API允许程序通过对象名称在指定对象的安全描述符中设置指定的安全信息。例如,如果文件名是file对象,程序可以指定文件名。
我们想强调的是,虽然这个Windows API不构成任何安全漏洞。但是,当我们使用我们编写的静态分析工具来搜索我们想要查看的RPC服务时,它可以作为过滤器。有了这些知识,我们可以创建了一个简单的工具,静态解析所有RPC服务可执行文件,试图寻找感兴趣的Windows API,以缩小我们需要进一步挖掘的RPC服务的范围。
不出所料,我们果然发现了一些有趣的RPC服务。臭名昭着的存储服务,也称为StorSvc,具有以前未被其他研究人员发现的多个权限提升漏洞。另外还有AppX部署服务器器,它容易受到最终可能导致权限提升的竞争条件的影响。最终,我们将这些漏洞报告给微软安全响应中心(MSRC),现在它们已经分别被修复,并编号为CVE-2019-0569 和CVE-2019-0766 。
现在,我们将讨论我们是如何发现这些漏洞的。
[+] Target: appidsvc.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: appidsvc.dll
[+] Target: AppVEntSubsystemController.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: AppVEntSubsystemController.dll
[+] Target: AppXDeploymentServer.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: AppXDeploymentServer.dll
[*] Potential DLL with arbitrary deletion: AppXDeploymentServer.dll
[*] Potential executable with arbitrary file modification with move: AppXDeploymentServer.dll
[*] Potential DLL with arbitrary DACL modification: AppXDeploymentServer.dll
[+] Target: bdesvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: bdesvc.dll
[+] Target: bisrv.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: bisrv.dll
[+] Target: combase.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: combase.dll
[*] Potential executable arbitrary deletion: combase.dll
[+] Target: cryptcatsvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: cryptcatsvc.dll
[*] Potential executable with arbitrary file modification with move: cryptcatsvc.dll
[+] Target: cryptsvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: cryptsvc.dll
[+] Target: dhcpcore.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: dhcpcore.dll
[+] Target: dhcpcore6.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: dhcpcore6.dll
[+] Target: DiagSvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: DiagSvc.dll
[+] Target: diagtrack.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: diagtrack.dll
[*] Potential executable arbitrary deletion: diagtrack.dll
[*] Potential executable with arbitrary file modification with move: diagtrack.dll
[*] Potential DLL with arbitrary DACL modification: diagtrack.dll
[+] Target: DmApiSetExtImplDesktop.dll
[*] Is RPC server file
[+] Target: dot3svc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: dot3svc.dll
[+] Target: dpapisrv.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: dpapisrv.dll
[+] Target: dssvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: dssvc.dll
[*] Potential DLL with arbitrary deletion: dssvc.dll
[*] Potential executable with arbitrary file modification with move: dssvc.dll
[*] Potential DLL with arbitrary DACL modification: dssvc.dll
[+] Target: dusmsvc.dll
[*] Is RPC server file
[+] Target: edgehtml.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: edgehtml.dll
[*] Potential DLL with arbitrary deletion: edgehtml.dll
[*] Potential executable with arbitrary file modification with move: edgehtml.dll
[*] Potential DLL with arbitrary DACL modification: edgehtml.dll
[+] Target: eeprov.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: eeprov.dll
[+] Target: efslsaext.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: efslsaext.dll
[*] Potential executable arbitrary deletion: efslsaext.dll
[+] Target: FXSAPI.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: FXSAPI.dll
[+] Target: FXSSVC.exe
[*] Is RPC server file
[*] Potential executable arbitrary deletion: FXSSVC.exe
[*] Potential DLL with arbitrary deletion: FXSSVC.exe
[*] Potential executable with arbitrary file modification with move: FXSSVC.exe
[+] Target: iphlpsvc.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: iphlpsvc.dll
[+] Target: LogonController.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: LogonController.dll
[+] Target: lsasrv.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: lsasrv.dll
[*] Potential executable with arbitrary file modification with move: lsasrv.dll
[+] Target: mispace.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: mispace.dll
[*] Potential executable arbitrary deletion: mispace.dll
[+] Target: modernexecserver.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: modernexecserver.dll
[+] Target: msdtcprx.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: msdtcprx.dll
[*] Potential executable with arbitrary file modification with move: msdtcprx.dll
[*] Potential DLL with arbitrary DACL modification: msdtcprx.dll
[*] Potential executable with arbitrary file modification with move: msdtcprx.dll
[+] Target: netlogon.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: netlogon.dll
[*] Potential executable with arbitrary file modification with move: netlogon.dll
[+] Target: p2psvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: p2psvc.dll
[+] Target: PackageStateRoaming.dll
[*] Is RPC server file
[+] Target: pcasvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: pcasvc.dll
[*] Potential executable with arbitrary file modification with move: pcasvc.dll
[+] Target: PeerDistSvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: PeerDistSvc.dll
[*] Potential DLL with arbitrary deletion: PeerDistSvc.dll
[*] Potential executable with arbitrary file modification with move: PeerDistSvc.dll
[+] Target: PhoneProviders.dll
[*] Is RPC server file
[+] Target: pla.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: pla.dll
[*] Potential executable arbitrary deletion: pla.dll
[*] Potential DLL with arbitrary deletion: pla.dll
[+] Target: pnrpsvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: pnrpsvc.dll
[+] Target: profsvc.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: profsvc.dll
[*] Potential executable arbitrary deletion: profsvc.dll
[*] Potential DLL with arbitrary DACL modification: profsvc.dll
[+] Target: rasmans.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: rasmans.dll
[*] Potential executable with arbitrary file modification with move: rasmans.dll
[*] Potential DLL with arbitrary DACL modification: rasmans.dll
[+] Target: rdpclip.exe
[*] Is RPC server file
[*] Potential executable arbitrary deletion: rdpclip.exe
[+] Target: scesrv.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: scesrv.dll
[*] Potential DLL with arbitrary DACL modification: scesrv.dll
[+] Target: schedsvc.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: schedsvc.dll
[*] Potential executable arbitrary deletion: schedsvc.dll
[*] Potential DLL with arbitrary DACL modification: schedsvc.dll
[+] Target: SessEnv.dll
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: SessEnv.dll
[*] Potential executable arbitrary deletion: SessEnv.dll
[*] Potential DLL with arbitrary deletion: SessEnv.dll
[+] Target: Spectrum.exe
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: Spectrum.exe
[+] Target: spoolsv.exe
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: spoolsv.exe
[*] Potential executable arbitrary deletion: spoolsv.exe
[+] Target: sstpsvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: sstpsvc.dll
[+] Target: StorSvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: StorSvc.dll
[*] Potential DLL with arbitrary deletion: StorSvc.dll
[*] Potential DLL with arbitrary DACL modification: StorSvc.dll
[+] Target: sysmain.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: sysmain.dll
[*] Potential executable with arbitrary file modification with move: sysmain.dll
[*] Potential DLL with arbitrary DACL modification: sysmain.dll
[+] Target: SystemEventsBrokerServer.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: SystemEventsBrokerServer.dll
[*] Potential executable with arbitrary file modification with move:
[+] Target: tapisrv.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: tapisrv.dll
[+] Target: taskcomp.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: taskcomp.dll
[*] Potential DLL with arbitrary DACL modification: taskcomp.dll
[+] Target: tellib.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: tellib.dll
[*] Potential executable arbitrary deletion: tellib.dll
[*] Potential executable with arbitrary file modification with move: tellib.dll
[*] Potential DLL with arbitrary DACL modification: tellib.dll
[+] Target: termsrv.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: termsrv.dll
[+] Target: trkwks.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: trkwks.dll
[*] Potential executable with arbitrary file modification with move: trkwks.dll
[+] Target: tttracer.exe
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: tttracer.exe
[*] Potential DLL with arbitrary DACL modification: tttracer.exe
[+] Target: uireng.dll
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: uireng.dll
[*] Potential DLL with arbitrary deletion: uireng.dll
[*] Potential executable arbitrary deletion: uireng.dll
[+] Target: usermgr.dll
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: usermgr.dll
[*] Potential DLL with arbitrary DACL modification: usermgr.dll
[+] Target: vaultsvc.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: vaultsvc.dll
[*] Potential executable arbitrary deletion: vaultsvc.dll
[*] Potential executable with arbitrary file modification with move: vaultsvc.dll
[+] Target: vmrdvcore.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: vmrdvcore.dll
[*] Potential executable arbitrary deletion: vmrdvcore.dll
[*] Potential executable with arbitrary file modification with move: vmrdvcore.dll
[+] Target: w32time.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary DACL modification: w32time.dll
[+] Target: wevtsvc.dll
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: wevtsvc.dll
[*] Potential executable arbitrary deletion: wevtsvc.dll
[*] Potential DLL with arbitrary DACL modification: wevtsvc.dll
[+] Target: wiaservc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: wiaservc.dll
[+] Target: wifinetworkmanager.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: wifinetworkmanager.dll
[*] Potential DLL with arbitrary deletion: wifinetworkmanager.dll
[+] Target: wimserv.exe
[*] Is RPC server file
[*] Potential executable arbitrary deletion: wimserv.exe
[*] Potential DLL with arbitrary deletion: wimserv.exe
[+] Target: Windows.Internal.Bluetooth.dll
[*] Is RPC server file
[+] Target: wininit.exe
[*] Is RPC server file
[*] Potential executable arbitrary deletion: wininit.exe
[*] Potential executable with arbitrary file modification with move: wininit.exe
[+] Target: winlogon.exe
[*] Is RPC server file
[*] Potential executable with arbitrary file modification with move: winlogon.exe
[+] Target: wlansvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: wlansvc.dll
[*] Potential executable with arbitrary file modification with move: wlansvc.dll
[+] Target: wwansvc.dll
[*] Is RPC server file
[*] Potential executable arbitrary deletion: wwansvc.dll
[*] Potential executable with arbitrary file modification with move: wwansvc.dll
[+] Target: XblGameSave.dll
[*] Is RPC server file
[*] Potential DLL with arbitrary deletion: XblGameSave.dll
[*] Potential executable arbitrary deletion: XblGameSave.dll
[*] Potential executable with arbitrary file modification with move: XblGameSave.dll
由静态解析器过滤的RPC可执行文件
 CVE-2019-0569——任意文件覆盖Microsoft Windows存储服务
CVE-2019-0569——任意文件覆盖Microsoft Windows存储服务
如上图所示,在分析由静态解析器过滤的RPC可执行文件时,它指出了包含我们所需的导入API的StorSvc.dll。在反汇编DLL组件时,我们发现了这个接口:BE7F785E-0E3A-4AB7-91DE-7E46E443BE29,当反汇编其中一个公开的RPC API时,我们发现了一个名为SvcSetStorageSettings的有趣RPC API。这引起了我们的注意,因为这个API涉及创建两个具有可预测文件夹名称的Windows目录。将正确的参数传递给这个API时,将在外部存储驱动器卷的根目录上创建以下文件夹:
· 文件
· 影片
· 图片
· 下载
· 音乐
你可能已经注意到,这些是在用户帐户配置文件根目录下找到的相同默认文件夹(%USERPROFILE%)。但是,漏洞是,如果存在外部硬盘驱动器卷,这些文件夹将仅由RPC API创建。当RPC API被触发时,你可以看到Process Monitor(一款系统进程监视软件)输出类似于下面屏幕截图中显示的输出:
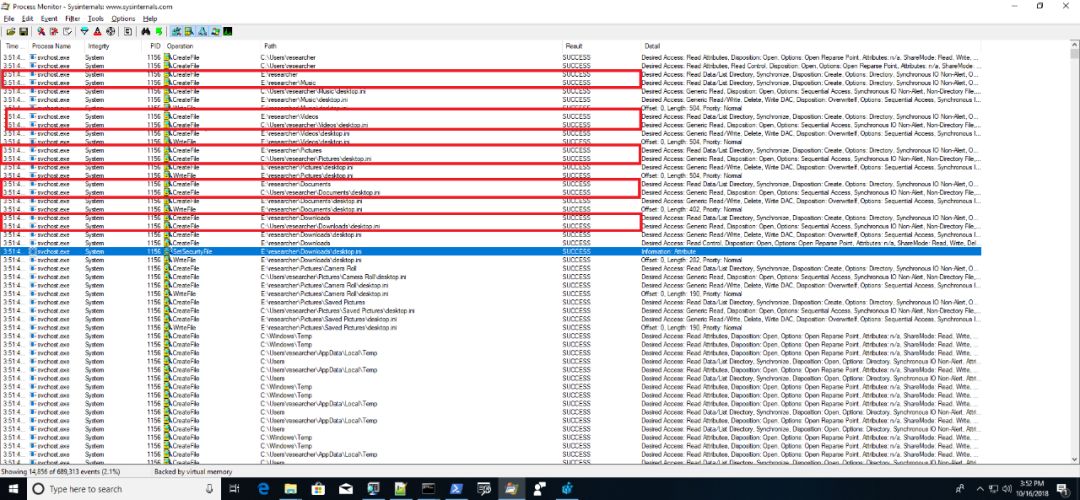
SvcSetStorageSettings创建的多个硬编码文件夹
查看Process Monitor输出的内容,我们可以看到此RPC API容易受到符号链接攻击(一次完美的符号链接攻击,除了必须有符号链接外,更重要的是要有提权的渠道。)因为它会创建一些可预测的目录。从Process Monitor调用堆栈信息中,我们可以确定特定CreateFile事件中涉及的函数例程。在查看相关函数例程时,我们很快在StorageService::CreateStorageCardDirectory中发现了漏洞,在创建经过身份验证的用户可以访问的文件和文件夹时,这个目录缺少模拟过程,以至于它允许攻击者修改通过符号链接指定的任意文件对象的ACL。
我们来看下面的代码片段:
StorageService::CreateStorageCardDirectory()
{
dwFileAttributes = GetFileAttributesW(&FileName);
if ( dwFileAttributes != -1 && !(dwFileAttributes & FILE_ATTRIBUTE_DIRECTORY) ) // -- (1)
{
DeleteFileW(&FileName);
dwFileAttributes = -1;
}
if (CreateDirectoryW(&FileName, lpSecurityAttributes) ) // -- (2)
{
if (dwFileAttributes != -1 && (ExistingFileAttributes | 0x10) != (dwFileAttributes & 0xFFFFFFDF) )
SetFileAttributesW(&FileName, ExistingFileAttributes | 0x10)
}
else if (GetLastError() == ERROR_ALREADY_EXISTS)
{
result = SetNamedSecurityInfoW(&FileName, SE_FILE_OBJECT, SECURITY_DACL_INFORMATION, 0, 0, NewAcl, 0); // -- (3)
boolSetNameddSecInfo = result < 0;
if ( result > 0 )
{
result = (unsigned __int16)result | 0x80070000;
boolSetNameddSecInfo = result < 0;
}
if (!boolSetNameddSecInfo)
{
dwFileAttributes = GetFileAttributesW(&FileName);
SetFileAttributesW(&FileName, ExistingFileAttributes | 0x10)
}
}
}
有漏洞的StorageService::CreateStorageCardDirectory缺少模拟过程
如果攻击者成功地创建了一个符号链接,将文件名重定向到攻击者想要的文件对象,则可以使用NewAcl(即当前登录用户的ACL)在label(3)中的代码路径上修改重定向文件对象的ACL。
符号链接攻击发生之前,我们需要处理标签(1)和(2)中的条件检查。简而言之,我们确定(1)和(2)中的条件检查将删除文件并尝试在发生文件名冲突时创建具有相同名称的目录。需要注意的是,在创建目录之前,它会执行DeleteFileW,删除指向目标文件的符号链接。那么,我们如何防止符号链接被删除呢?
事实证明,如果文件名具有调用者进程打开的独占文件句柄,则可以很容易地绕过它。即使DeleteFileW调用失败并且漏洞访问被拒绝,执行进程仍将继续,因为从API调用返回时没有漏洞检查。
在我们设置指向目标文件的符号链接并在目标文件上创建了独占句柄之后,我们可以触发SvcSetStorageSettings来修改任意文件对象的ACL。以下屏幕截图中的PoC结果说明了SvcSetStorageSettings中的漏洞如何允许我们修改位于Windows目录中的文件的ACL。实际上,该ACL应禁止非权限用户修改:
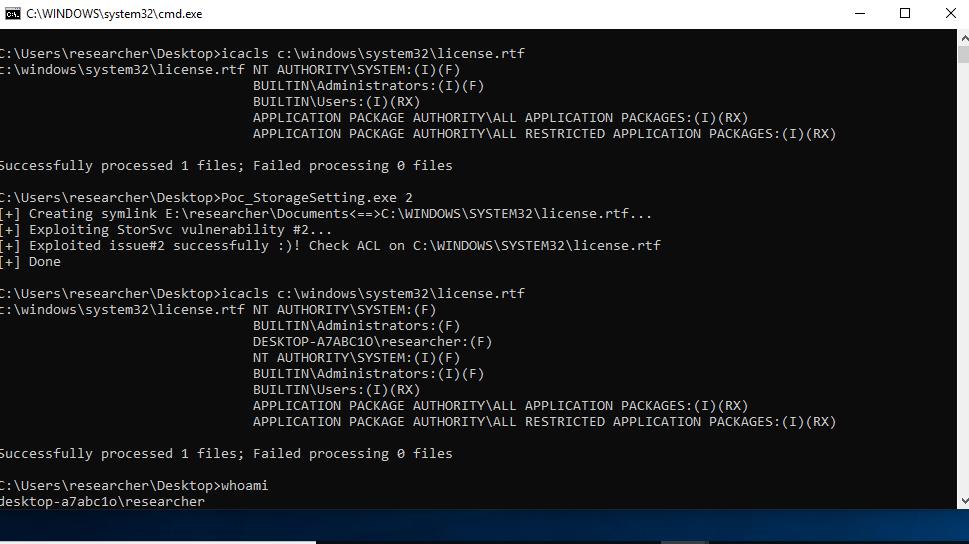
使用svcsetstoragesetings RPC API的结果
 CVE-2019-0766——Microsoft AppX 部署服务器通过竞争条件创建任意文件
CVE-2019-0766——Microsoft AppX 部署服务器通过竞争条件创建任意文件
继续进行解析器的输出内容,我们发现另一个Windows AppX部署服务器也是由于缺乏模拟过程,出现了同样的符号链接攻击漏洞。
在安装可从Microsoft Store下载的AppX软件包时,我们意识到AppX部署服务器将AppX软件包可执行文件及其相应资源保存在以下可预测文件路径中:
E:WpSystem<current_logged_in_user_sid>AppDataLocalPackagesMicrosoft.AppX.Package.Name
如果部署服务器要修改同时删除的文件上的ACL,则可能会发生相同的符号链接攻击。注意:E: drive 是我们测试系统上的外部驱动器。你可能已经注意到,这与上一节描述的漏洞有点类似。但是,我们首先需要确定这个文件路径的可访问性。
我们可以使用icacls命令确定文件和文件夹的可访问性,事实证明,当前登录的用户具有对此目录的完全访问权限。
C:>icacls E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppDataLocalPackagesMicrosoft.MicrosoftMahjong_8wekyb3d8bbwe
E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppDataLocalPackagesMicrosoft.MicrosoftMahjong_8wekyb3d8bbwe
NT AUTHORITYSYSTEM:(CR)(F)
NT AUTHORITYSYSTEM:(OI)(CI)(IO)(CR)(F)
DESKTOP-A7ABC1O esearcher:(CR)(F)
DESKTOP-A7ABC1O esearcher:(OI)(CI)(IO)(CR)(F)
BUILTINAdministrators:(CR)(F)
BUILTINAdministrators:(OI)(CI)(IO)(CR)(F)
NT AUTHORITYSYSTEM:(I)(OI)(CI)(F)
BUILTINAdministrators:(I)(OI)(CI)(F)
DESKTOP-A7ABC1O esearcher:(I)(OI)(CI)(F)
C:>icacls E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppDataLocalPackages
E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppDataLocalPackages
NT AUTHORITYSYSTEM:(I)(OI)(CI)(F)
BUILTINAdministrators:(I)(OI)(CI)(F)
DESKTOP-A7ABC1O esearcher:(I)(OI)(CI)(F)
C:>icacls E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppDataLocal
E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppDataLocal
NT AUTHORITYSYSTEM:(I)(OI)(CI)(F)
BUILTINAdministrators:(I)(OI)(CI)(F)
DESKTOP-A7ABC1O esearcher:(I)(OI)(CI)(F)
C:>icacls E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppData
E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001AppData
NT AUTHORITYSYSTEM:(I)(OI)(CI)(F)
BUILTINAdministrators:(I)(OI)(CI)(F)
DESKTOP-A7ABC1O esearcher:(I)(OI)(CI)(F)
C:>icacls E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001
E:WpSystemS-1-5-21-2264505789-2271452246-4192020221-1001
NT AUTHORITYSYSTEM:(OI)(CI)(F)
BUILTINAdministrators:(OI)(CI)(F)
DESKTOP-A7ABC1O esearcher:(OI)(CI)(F)
显然,普通用户帐户可以任意操纵具有较高权限服务共享的资源。有两种方法可以验证此漏洞:如前一篇文章中所述,你可以使用Process Monitor在AppX软件包安装期间捕获事件,并从那里通过查找SetSecurityFile事件来查明代码路径。而另一种方法就是对DLL组件AppXDeploymentServer.dll执行静态分析,该组件包含服务逻辑的实现。
我们最终得到了以下代码片段:
// After created its parent directories, try to create E:WpSystem<SID>AppDataLocalPackages<AppX.PackageName>
if ( CreateDirectoryW(*(LPCWSTR *)(this - 28), 0) ) // -- (1)
v16 = 0;
else
v16 = getlasterror();
v15 = *(void **)(this + 4);
if ( v16 < 0 )
{
v17 = 0x4C8;
goto exit;
}
}
v15 = *(void **)(this + 4);
if ( v16 >= 0 )
{
if ( v13 == 1
|| sub_102335C9(v15)
// Set security descriptor on e:WPSystem and its sub-directories to allow Administrator and System user access only
|| (v19 = wpsystem_setnamedsecurityinfo((int)v12, *(WCHAR **)(this - 16)),
v15 = *(void **)(this + 4),
v16 = v19,
v19 >= 0) )
{
// Encrypt and compress the files in Appx.Package
v20 = EncryptFile((int)v12, *(WCHAR **)(this - 16)); // -- (2)
v15 = *(void **)(this + 4);
v16 = v20;
if ( v20 >= 0 )
{
// Reset security descriptor on \?E:WpSystem<SID>AppDataLocalPackages<AppX.PackageName> to allow full access
// however, neither no verification is done on the assigned object name therefore it can be replaced with file object instead of directory object and impersonation here
v21 = SetNamedSecurityInfoW(*(LPWSTR *)(this - 28), SE_FILE_OBJECT, DACL_SECURITY_INFORMATION, 0, 0, *(PACL *)(this - 20), 0); // -- (3)
AppXDeploymentServer.dll缺少用户模拟
正如你在上面的代码片段中所看到的,在(1)中标记的AppX包目录与通过(3)中标记的SetNamedSecurityInfoW设置其安全描述符之间存在潜在的竞争条件,这可能允许攻击者修改任意文件对象的ACL。
为了验证这一点,我们的目标是通过符号链接将AppX文件夹名称,SetNamedSecurityInfoW的第一个参数(由label(3)中的代码指示)重定向到感兴趣的任意文件对象。
但是,在此之前,请务必注意默认保存位置需要设置为外部驱动器。在Windows 10中,这可以在“控制面板”中的“默认保存位置”设置下完成,但我们希望以编程方式执行此操作。如前一个案例研究中所述,找到了SvcSetStorageSettings RPC API后,它可以用来直接更改默认的保存位置。但是在程序中定义RPC接口是一个非常繁琐的步骤,所以我们需要一种更方便的方法来实现这一点。
事实证明,大多数RPC API都是通过单个DLL组件进行封装和导出的。因为大多数封装的RPC API导出函数都是未记录的,并由Windows系统组件实现,我们需要做的是通过在%WINDIR SYSTEM32目录中搜索其RPC UUID来查找此DLL。在我们使用其UUID(即BE7F785E-0E3A-4AB7-91DE-7E46E443BE29)搜索SvcSetStorageSettings接口后,会发现StorageUsage.dll,我们在其中发现了SetStorageSettings未记录的API。因此,我们可以使用常规LoadLibrary()和GetProcAddress()动态调用这个API。
最后,我们准备了PoC,并使用Process Monitor运行它来说明竞争条件,如下面的屏幕截图所示:
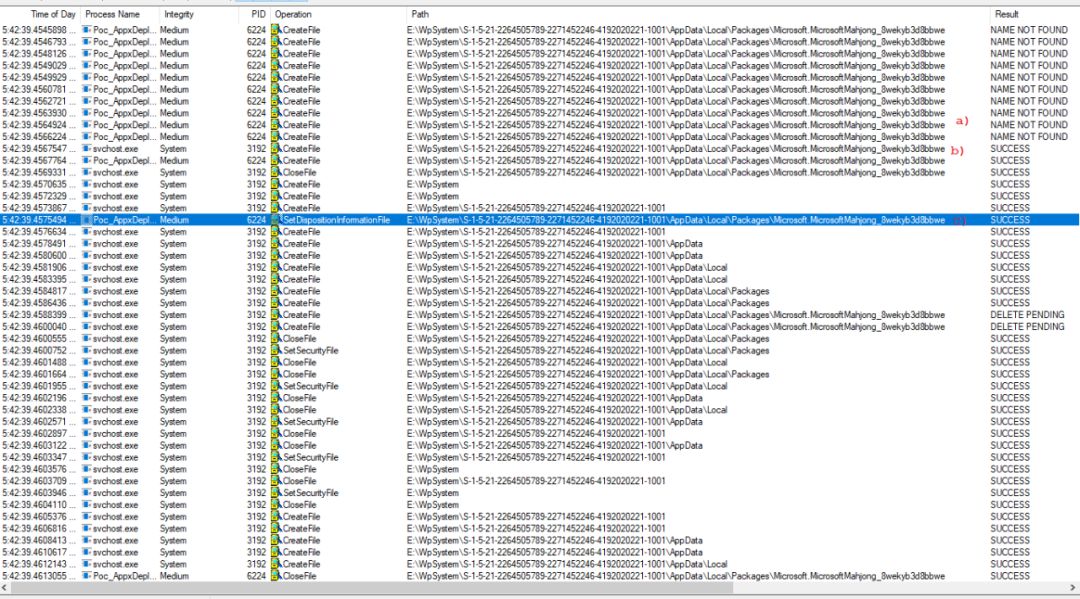
演示无限循环线程的PoC屏幕截图
1.表示我们的PoC正在执行无限循环线程操作,试图删除列表3中label(1)中的代码创建的AppX文件夹;
2.表示AppX部署服务器成功创建的AppX文件夹;
3.线程会立即成功删除该文件夹;
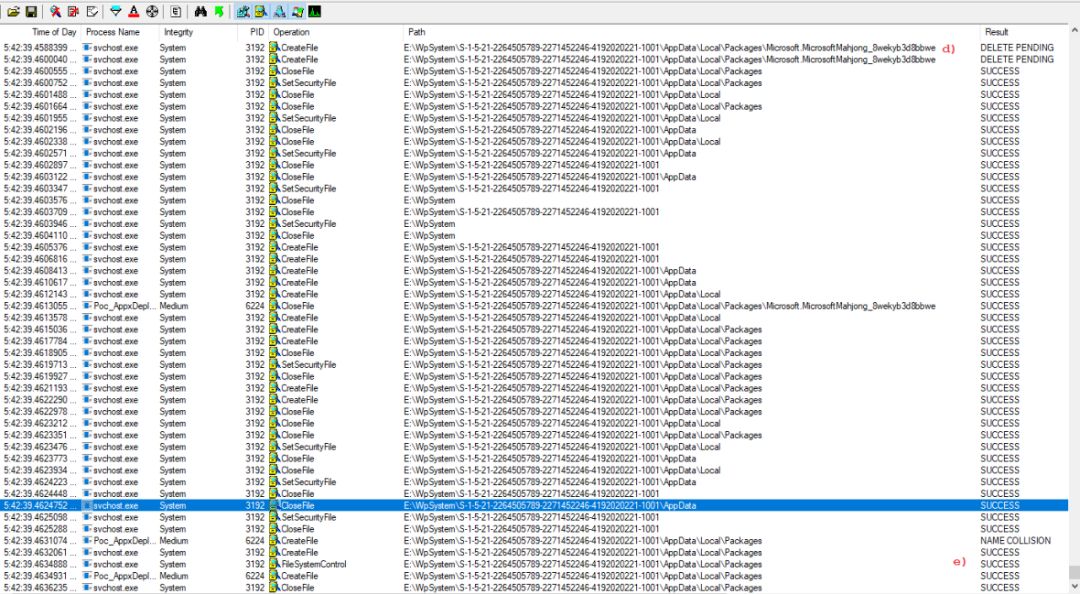
修改ACL操作的PoC屏幕截图
4.此时,AppX 部署服务器尝试通过执行wpsystem_setnamedsecurityinfo例程来修改目录及其子目录的安全描述符。然而,由于(a)处的操作导致文件即将被删除,所以操作没有成功。
5. 列表3中的代码标签(2)中提到的操作将在此时执行;
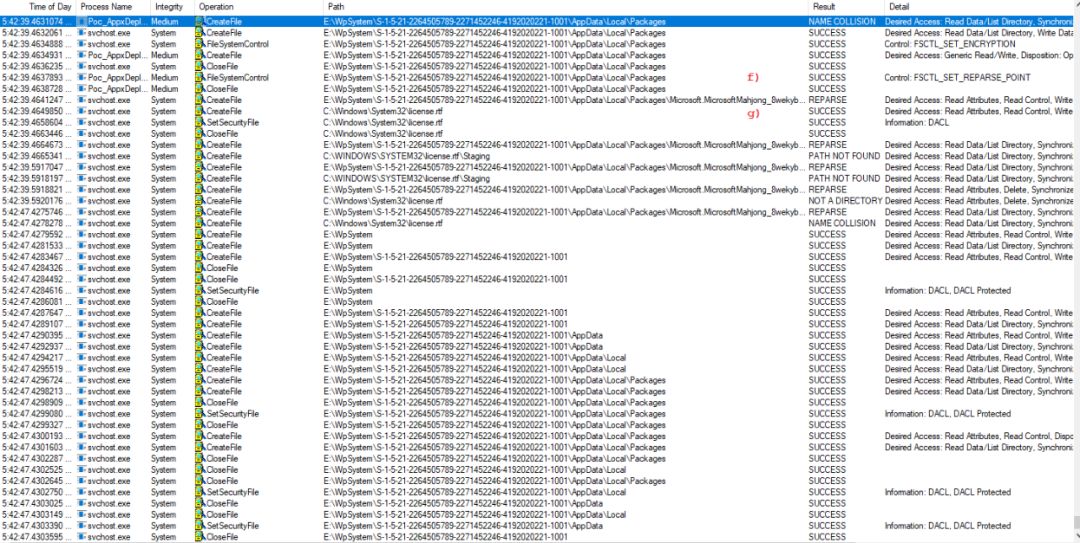
PoC屏幕截图,用于说明竞争条件的成功利用
6.竞争条件成功利用后,我们的PoC将能够在执行列表3中的代码标签(3)之前,在PoC中创建任意文件C:Windowssystem32 license.rtf的符号链接;
7.最后,权限服务成功修改了目标文件的安全描述符
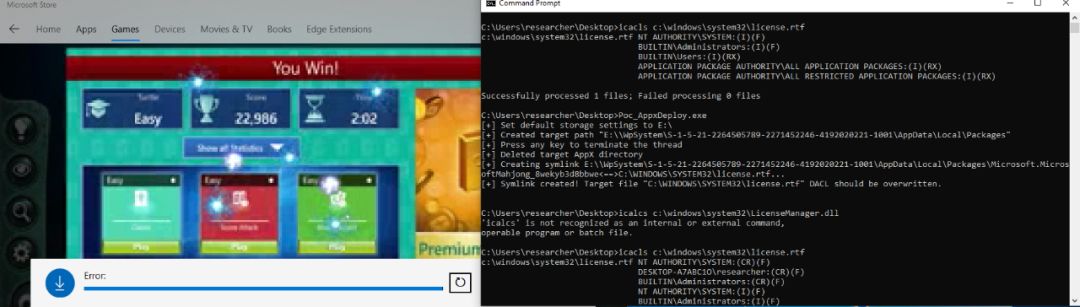
成功利用竞争条件覆盖任意文件对象的PoC
 总结
总结
本文,我们介绍了在寻找本地权限提升漏洞时,如何缩小搜寻的RPC服务范围。目前,这种方法已被证明非常有效,如上所述,我们发现了CVE-2019-0569 和 CVE-2019-0766漏洞,但是在不同的组件中。
以上是关于RPC漏洞挖掘案例研究(下)的主要内容,如果未能解决你的问题,请参考以下文章