GKCTF X DASCTF应急挑战杯Misc-Writeup
Posted 末 初
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了GKCTF X DASCTF应急挑战杯Misc-Writeup相关的知识,希望对你有一定的参考价值。
Misc
签到

tcp.stream eq 5发现cat /f14g操作
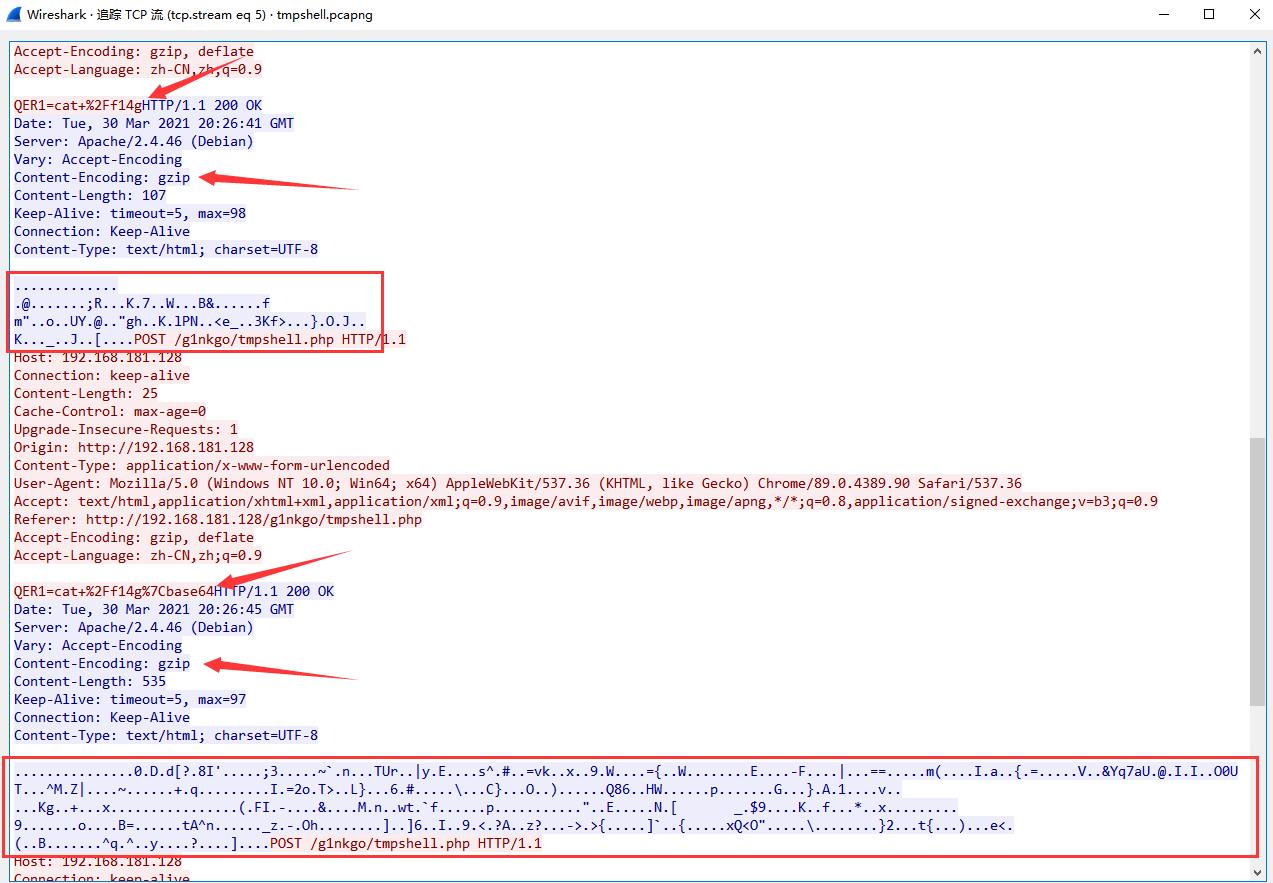
尝试直接foremost分离无果,只能切换为显示Hex数据,然后手动复制出Hex数据,转存为gzip
gzip的文件开头Hex为:1f 8b
from binascii import *
hexdata = '1f8b0800000000000003c5d1cb0d80400884e196dcccbf3b528ecffe4b10379e8c57f5f405422601a096b6b3a1660d6d221cac6fcb0c55599b4094bb226768bbc74be76c504e1d1a3c655fe9d8334b663ee69cda7dbf4ff64afb1d0d4bd5cfe65fb51e4ac6d45be0010000'
with open('flag.gz', 'wb') as f:
f.write(unhexlify(hexdata))
解压出来还hex数据,转换为字符串是base64,解码base64得到
#######################################
# 80:10:02 03-30-1202 #
#######################################
--------------------------------------------------
没啥发现,继续看另外一串Hex数据
from binascii import *
hexdata = '1f8b0800000000000003cd940b8ae4300c44af645b3fe7384927b9ff11f6953b33b0b00c03cb7e609a6e8fe492545572bab57c798445a5fb88ae735ed123fcf23d766b9ea6789415398a570f8fc9bd3d7b1ed657bcaaf99511f197e245dcc3f3b42d460cefd5fe7cdd1cd63d3d14e7dbbfe06d280c9ec7ee497f61cdc87be33dbca6ea11bb561c0c265971376155d140ab49ee49b5cb4f30550d549fff2e5e4df35a7c93b7c30f7ec1d7a31b08192baf710ecdbfb8ca07c71f9c49fd3d326f1b543e89174c7dfab0bc36c123c7ceb9c3f35c9f8ddf437d81df974fe81c29e4e3ddabcad0513836defa4857a716b8f4cd9f70e9eb97bce0b3ff478fb0da7d9041d331b2c7869f76e8b90ae6ca994b67fbd02bf2f1e178f32e9fe5cddc1cd1c31edca5dba317fc28d346498f2de1ba0cfe262ed7def14dad6ef0927774b6606607c7f1058be270cabdb51ff09fabeeeea7f422bee5459dc40fdae34ecf5b095ff32439eadbbfc94bf9916696130e2acf9a780ed7e087e0db99eaa539c8df14cf89e6036fa97fceb8423dc1a7eaaffe1b74415e6eefbe16b7bf175f7a992d9f4f68cfb5f7f0a9ddffe05def1a5d36bd1f49fee239de3c883f41d2f77a3fc4b7ee2d3ef03e7bc2bce89eae5d60cfb87b7fdedfa49b78513c4f2219dab6c1fd5cf7aff59e910ff2c17d32f191b9747ba5deaf29ffe4f1653cf328d59342bc86f88c17cfd65e71ef5effff79aece9e9f3f000ce1e95d90060000'
with open('flag1.gz', 'wb') as f:
f.write(unhexlify(hexdata))
一样的操作,Hex->base64得到
wIDIgACIgACIgAyIK0wIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMiCNoQD
jMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjoQDjACIgACIgACIggDM6EDM6AjMgAzMtMDMtEjM
t0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0iCNMyIjMyIjMyIjMyI
6AjMgAzMtMDMtEjMwIjO0eZ62ep5K0wKrQWYwVGdv5EItAiM1Aydl5mK6M6jlfpqnrQDt0SLt0SL
t0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLK0AIdZavo75mlvlCNMTM6EDM
z0yMw0SMyAjM6Q7lpb7lmrQDrsCZhBXZ09mTg0CIyUDI3VmbqozoPW+lqeuCN0SLt0SLt0SLt0SL
sxWZld1V913e7d2ZhFGbsZmZg0lp9iunbW+Wg0lp9iunbW+Wg0lp9iunbW+WK0wMxoTMwoDMyACM
DN0QDN0QDlWazNXMx0Wbf9lRGRDNDN0ard0Rf9VZl1WbwADIdRampDKilvFIdRampDKilvVKpM2Y
==wIDIgACIgACIgAyIK0wIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMiCNoQD
jMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjMyIjoQDjACIgACIgACIggDM6EDM6AjMgAzMtMDMtEjM
t0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0iCNMyIjMyIjMyIjMyI
6AjMgAzMtMDMtEjMwIjO0eZ62ep5K0wKrQWYwVGdv5EItAiM1Aydl5mK6M6jlfpqnrQDt0SLt0SL
t0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLt0SLK0AIdZavo75mlvlCNMTM6EDM
z0yMw0SMyAjM6Q7lpb7lmrQDrsCZhBXZ09mTg0CIyUDI3VmbqozoPW+lqeuCN0SLt0SLt0SLt0SL
sxWZld1V913e7d2ZhFGbsZmZg0lp9iunbW+Wg0lp9iunbW+Wg0lp9iunbW+WK0wMxoTMwoDMyACM
DN0QDN0QDlWazNXMx0Wbf9lRGRDNDN0ard0Rf9VZl1WbwADIdRampDKilvFIdRampDKilvVKpM2Y
==QIhM0QDN0Q
从base64的填充符位置来看,猜测分了三部分,然后逆序了字符串,所以最终得到
第一部分:
Q0NDQ0MhIQ==
解码后得到:
CCCCC!!
第二部分:
Y2MpKVvliKDpmaRdIFvliKDpmaRdIDAwbW1lZV9fR0dra0NDNDRGRl9fbW0xMXNzaWlDQ0NDQ0ND
MCAyMDowMToxMw0KW+Wbnui9pl0gW+Wbnui9pl0gW+Wbnui9pl0gZmZsbGFhZ2d7e319V1dlZWxs
LS0tLS0tLS0tLS0NCueql+WPozoqbmV3IDUyIC0gTm90ZXBhZCsrDQrml7bpl7Q6MjAyMS0wMy0z
MDE6MTMNClvlm57ovaZdIA0KLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0t
LS0tLS0tDQrnqpflj6M6Km5ldyA1MiAtIE5vdGVwYWQrKw0K5pe26Ze0OjIwMjEtMDMtMzAgMjA6
IyMjIyMjIyMjIyMNCi0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0t
MjEtMDMtMzAgMjA6MDE6MDggICAgICAgICAjDQojIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMj
DQoNCiMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIw0KIyAgICAgICAgIDIw==
解码后得到:
cc))[删除] [删除] 00mmee__GGkkCC44FF__mm11ssiiCCCCCCC0 20:01:13
[回车] [回车] [回车] ffllaagg{{}}WWeell-----------
窗口:*new 52 - Notepad++
时间:2021-03-301:13
[回车]
---------------------------------------------
窗口:*new 52 - Notepad++
时间:2021-03-30 20:###########
--------------------------------------------21-03-30 20:01:08 #
############################
#######################################
# 20
第三部分:
Y2MpKVvliKDpmaRdIFvliKDpmaRdIDAwbW1lZV9fR0dra0NDNDRGRl9fbW0xMXNzaWlDQ0NDQ0ND
MCAyMDowMToxMw0KW+Wbnui9pl0gW+Wbnui9pl0gW+Wbnui9pl0gZmZsbGFhZ2d7e319V1dlZWxs
LS0tLS0tLS0tLS0NCueql+WPozoqbmV3IDUyIC0gTm90ZXBhZCsrDQrml7bpl7Q6MjAyMS0wMy0z
MDE6MTMNClvlm57ovaZdIA0KLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0t
LS0tLS0tDQrnqpflj6M6Km5ldyA1MiAtIE5vdGVwYWQrKw0K5pe26Ze0OjIwMjEtMDMtMzAgMjA6
IyMjIyMjIyMjIyMNCi0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0tLS0t
MjEtMDMtMzAgMjA6MDE6MDggICAgICAgICAjDQojIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMj
DQoNCiMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIw0KIyAgICAgICAgIDIw
解码后得到:
cc))[删除] [删除] 00mmee__GGkkCC44FF__mm11ssiiCCCCCCC0 20:01:13
[回车] [回车] [回车] ffllaagg{{}}WWeell-----------
窗口:*new 52 - Notepad++
时间:2021-03-301:13
[回车]
---------------------------------------------
窗口:*new 52 - Notepad++
时间:2021-03-30 20:###########
--------------------------------------------21-03-30 20:01:08 #
############################
#######################################
# 20
这里感觉有坑点,flag靠猜测
flag{Welc0me_GkC4F_m1siCCCCCC!}
你知道apng吗


改为png只能显示第一帧,wiki上说Firefox支持apng,尝试直接拖入Firefox发现可以显示(我用Chrome也行)
我用ScreenToGif直接截成Gif,然后放入Stegsolve一帧一帧看

-0327-288a235370ea}
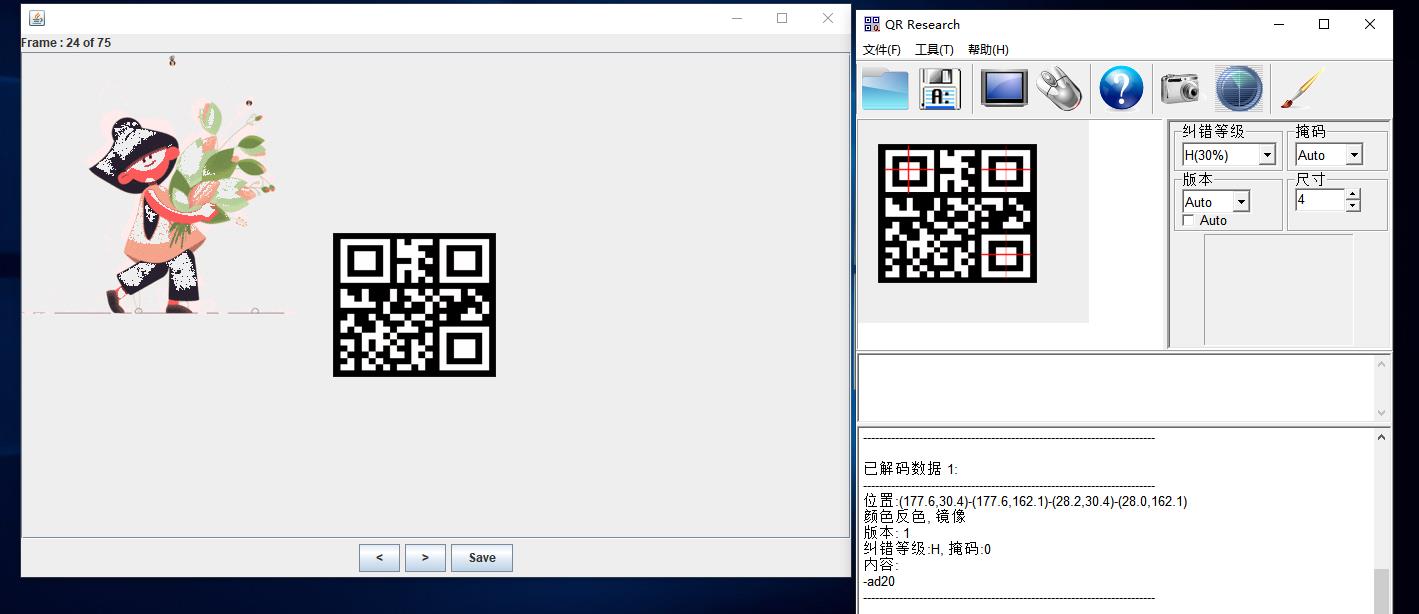
-ad20
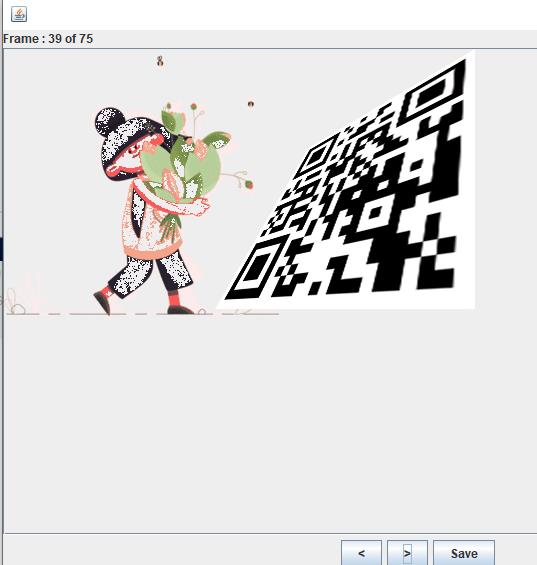
这张导出来,用PS打开,拉一下就行
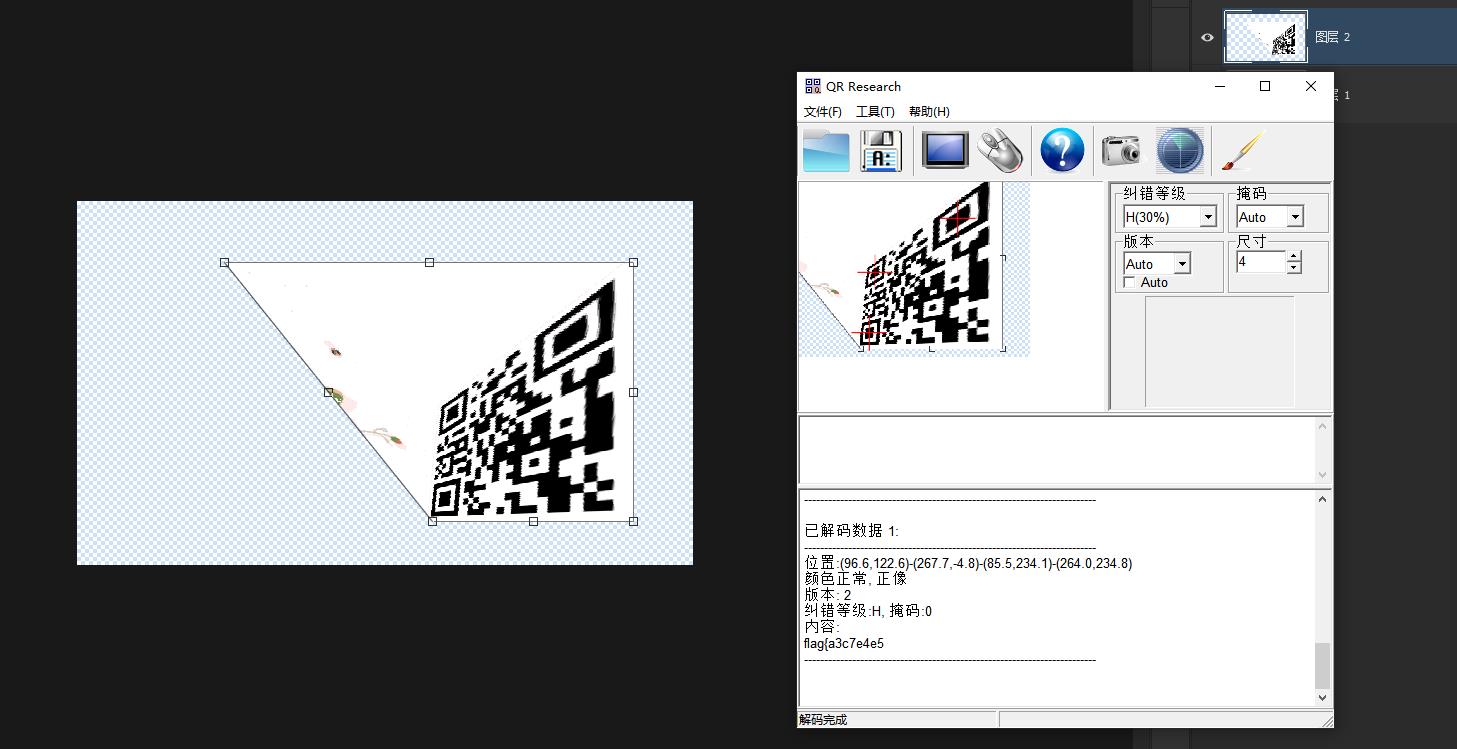
flag{a3c7e4e5
还有一张隐藏的比较深
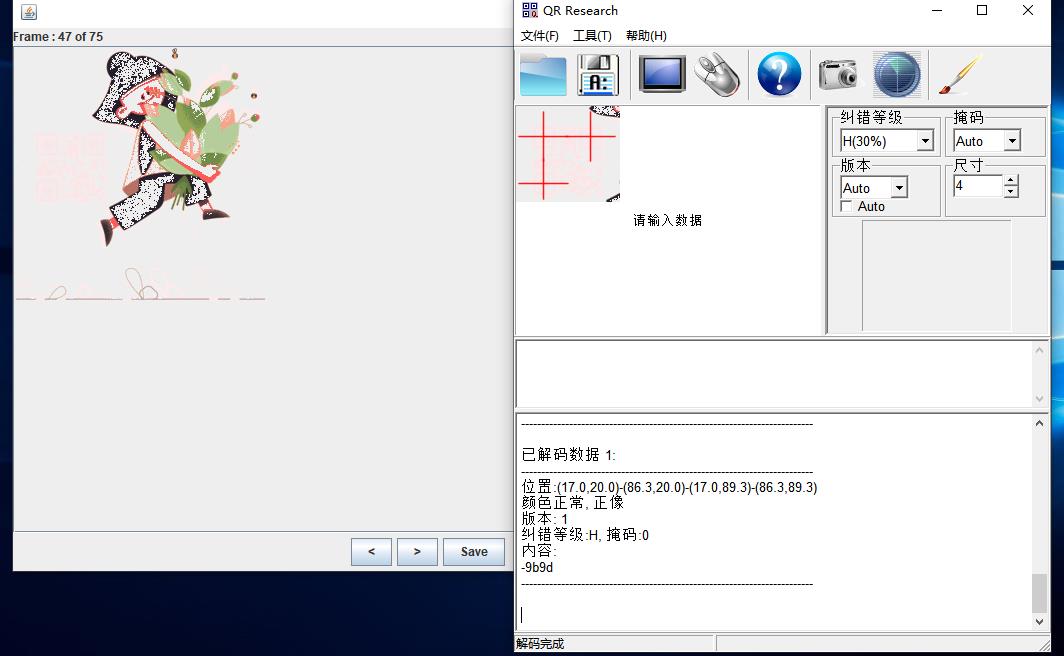
-9b9d
最终flag为
flag{a3c7e4e5-9b9d-ad20-0327-288a235370ea}
另外也可以使用APNG Disassembler来分离出apng图片的每一帧
APNG Disassembler:http://apngdis.sourceforge.net
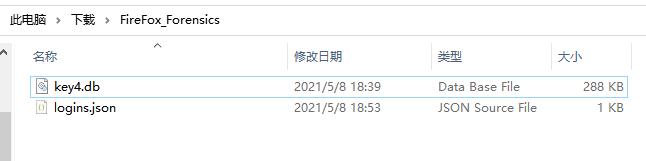
FireFox Forensics

从文件内容上看应该是Firefox的网页登录密码保存加密文件,给了key
Google找一下有没有工具
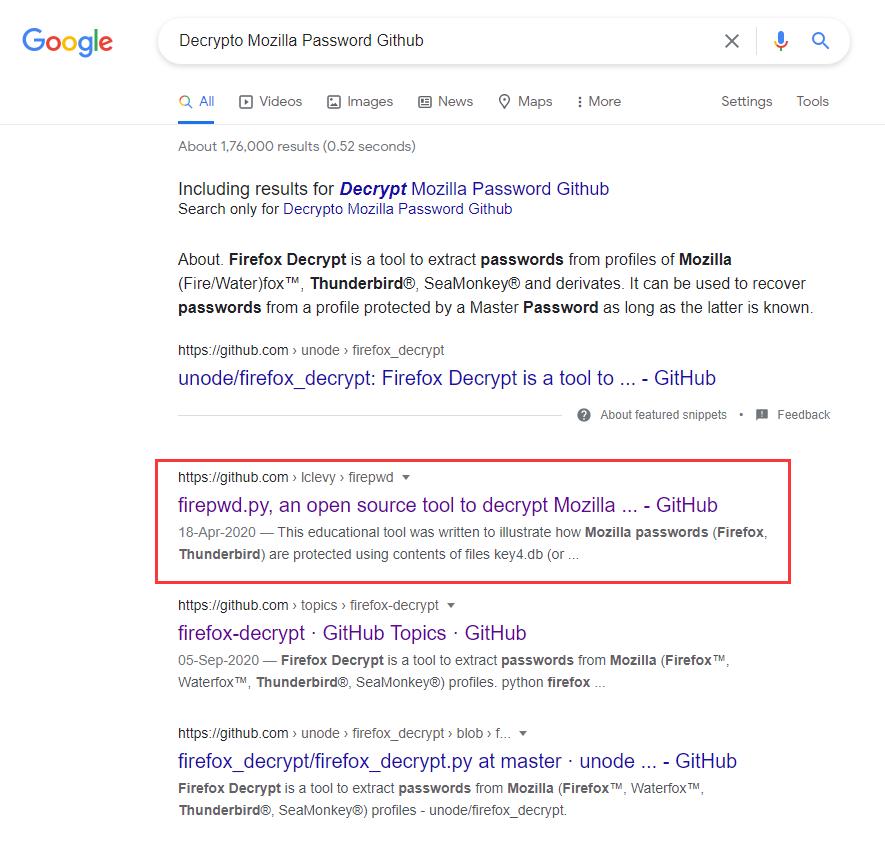
https://github.com/lclevy/firepwd
PS D:\\Tools\\Misc\\firepwd-master> python .\\firepwd.py -d C:\\Users\\Administrator\\Downloads\\FireFox_Forensics
globalSalt: b'1e26e84b2f01da28d865e7258f9003d16b9c43f2'
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.13 pkcs5 pbes2
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.12 pkcs5 PBKDF2
SEQUENCE {
OCTETSTRING b'66a735e17767b37d83d464126b36d4269243f9e0c99405ccd68f442798f83129'
INTEGER b'01'
INTEGER b'20'
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.2.9 hmacWithSHA256
}
}
}
SEQUENCE {
OBJECTIDENTIFIER 2.16.840.1.101.3.4.1.42 aes256-CBC
OCTETSTRING b'24eb241594de7ab37ec379d9ba06'
}
}
}
OCTETSTRING b'946322a2b2978db6601e449e1bdf7c4d'
}
clearText b'70617373776f72642d636865636b0202'
password check? True
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.13 pkcs5 pbes2
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.12 pkcs5 PBKDF2
SEQUENCE {
OCTETSTRING b'56722302469f529a29dc73f28d6af3ed0ee483cceff05772e96e2313336816fd'
INTEGER b'01'
INTEGER b'20'
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.2.9 hmacWithSHA256
}
}
}
SEQUENCE {
OBJECTIDENTIFIER 2.16.840.1.101.3.4.1.42 aes256-CBC
OCTETSTRING b'ef6a4df3e5fd7608c97df9e22092'
}
}
}
OCTETSTRING b'51b24cd6a2672c312255d7f2dddeb67336fd56973b4302bb2eacf2270c251d41'
}
clearText b'673dec57458fb95bd50bdc9198541038970e5b3d518973a40808080808080808'
decrypting login/password pairs
https://ctf.g1nkg0.com:b'admin',b'GKCTF{9cf21dda-34be-4f6c-a629-9c4647981ad7}'
PS D:\\Tools\\Misc\\firepwd-master>
GKCTF{9cf21dda-34be-4f6c-a629-9c4647981ad7}
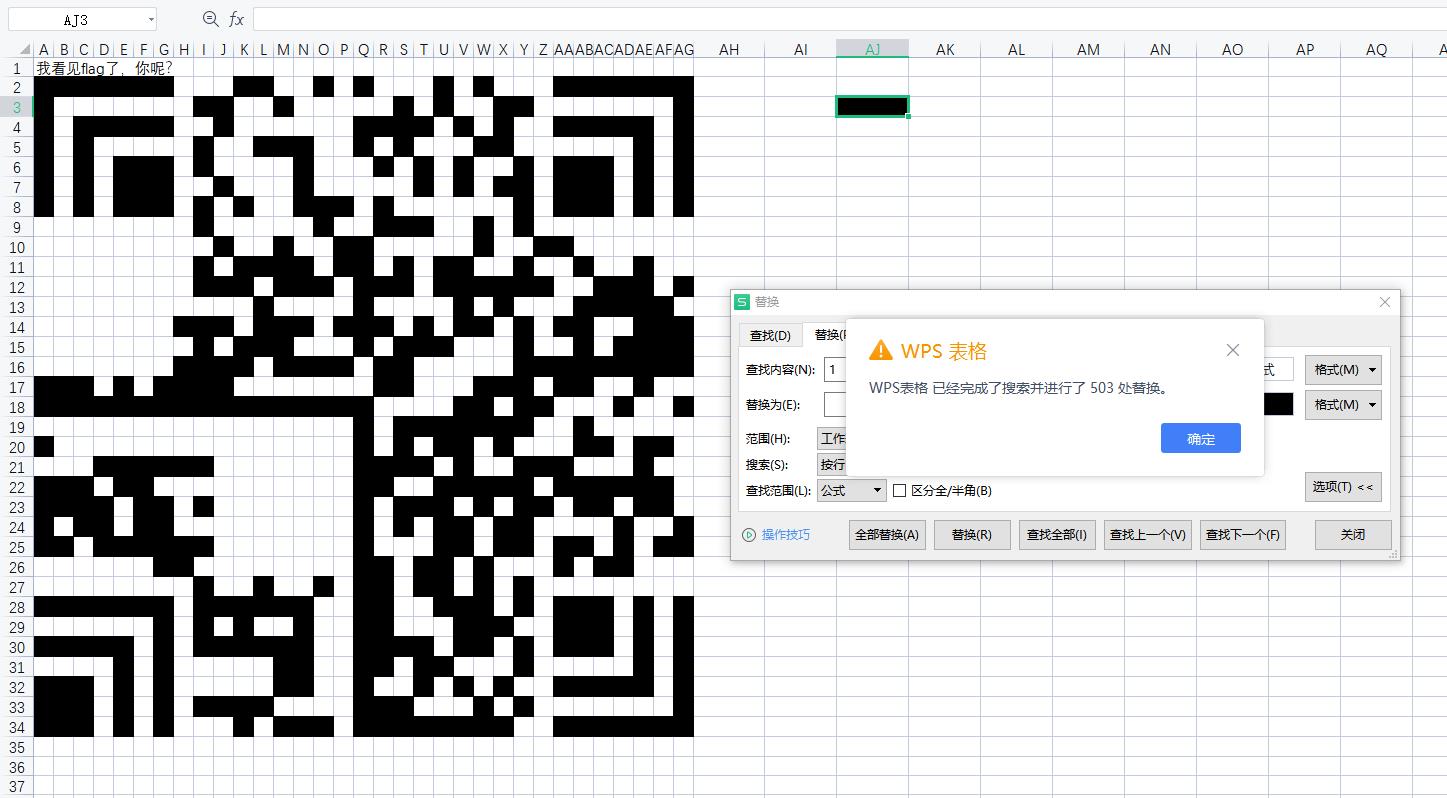
excel 骚操作

某些单元格设置了只有双击击才能显示内容的格式,Ctrl+A全选然后右键,选择清楚内容->格式
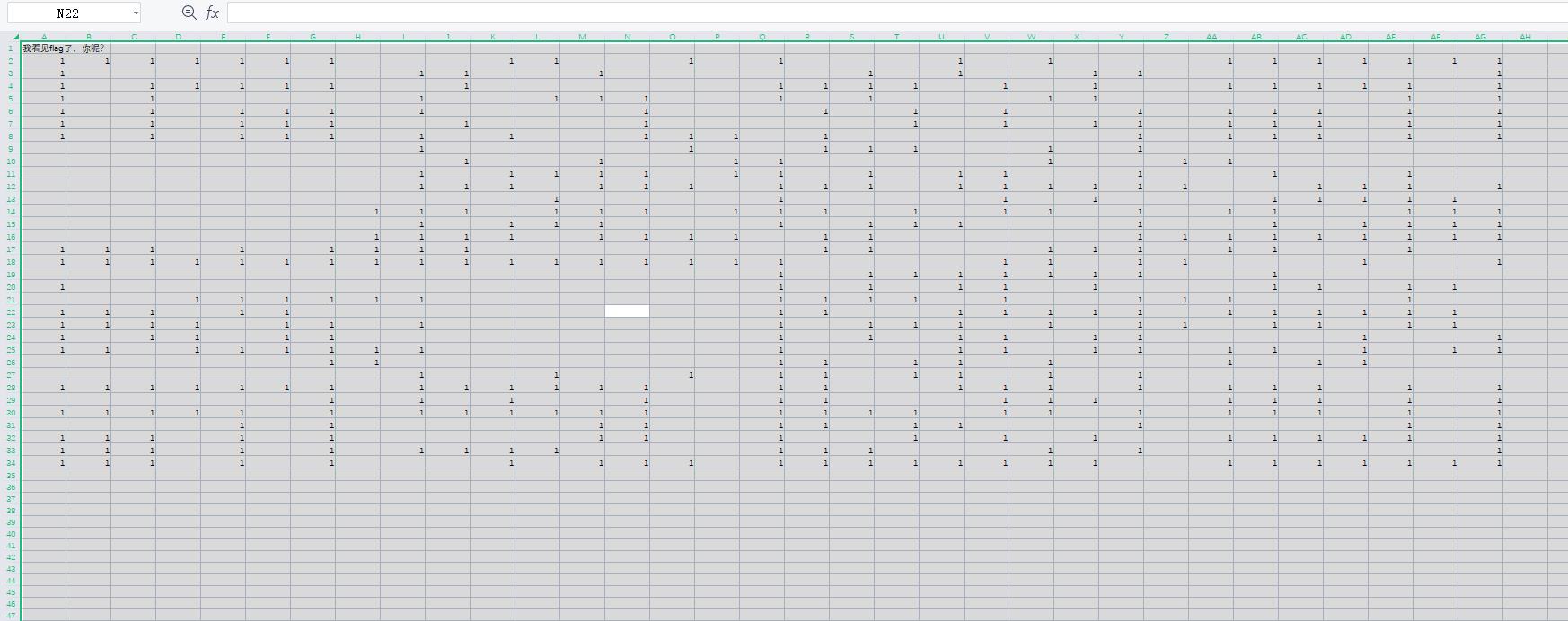
只有空单元格和内容为1的单元格,猜测为二维码,修改行高列宽相等
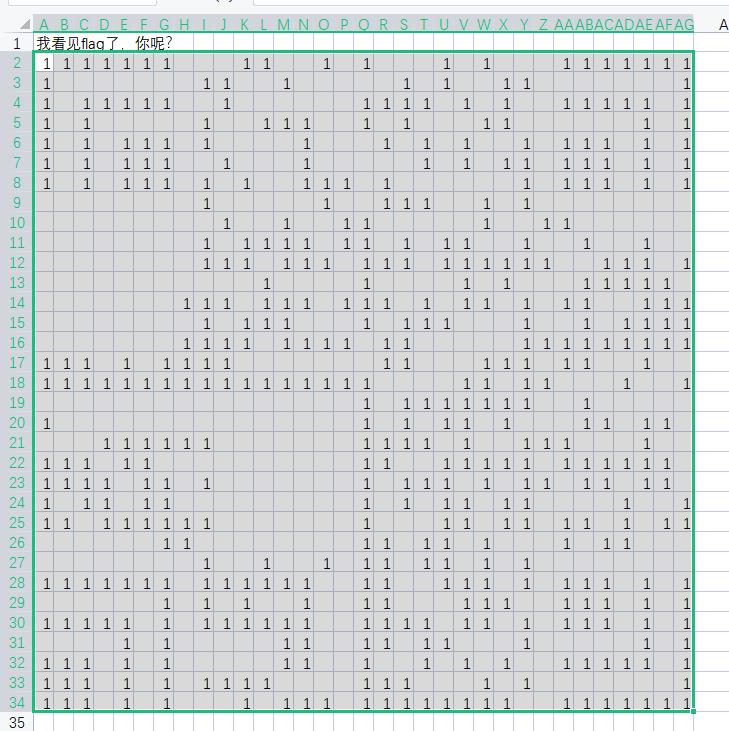
选中该范围Ctrl+H替换,替换为框点击格式,选择背景颜色选择一个黑色单元格
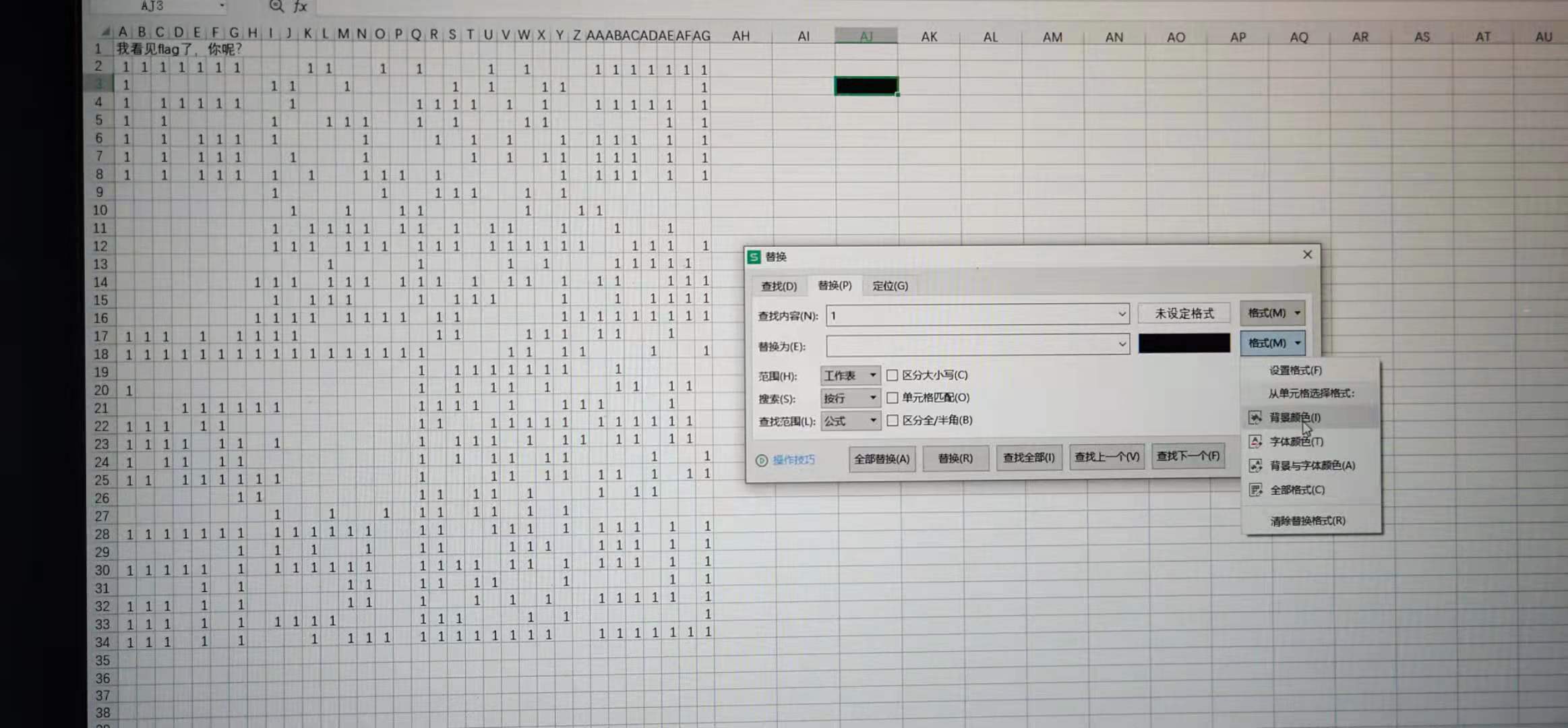
替换之后发现为汉信码
在线的汉信码站用不了了:http://www.efittech.com/hxdec.html
但是在网上看到有一个叫中国物品编码中心的APP可以扫描识别
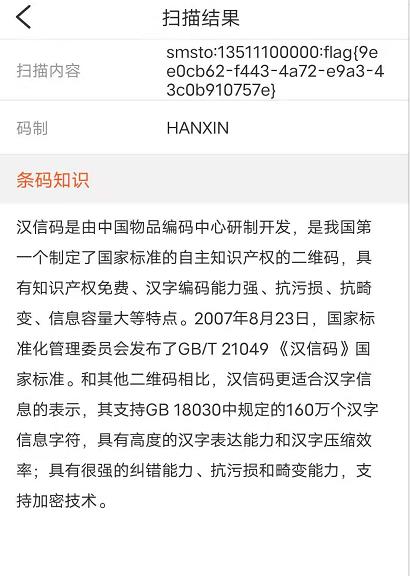
flag{9ee0cb62-f443-4a72-e9a3-43c0b910757e}
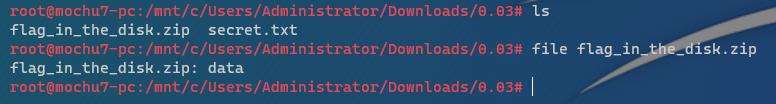
0.03

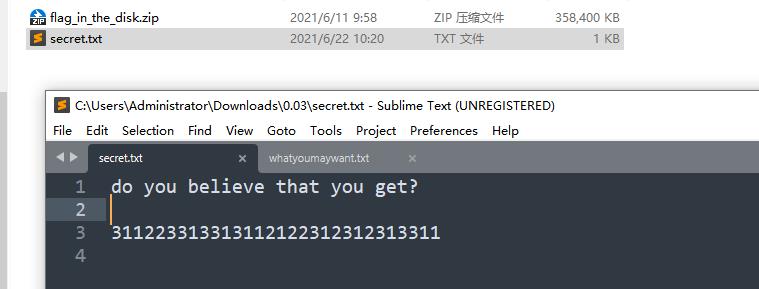
flag_in_the_disk.zip并非zip文件,也没识别出来是什么
但是看大小猜测可能为虚拟系统文件,可能需要挂载,经过多次尝试发现当密码为:311223313313112122312312313311时VeraCrypt可以挂载。
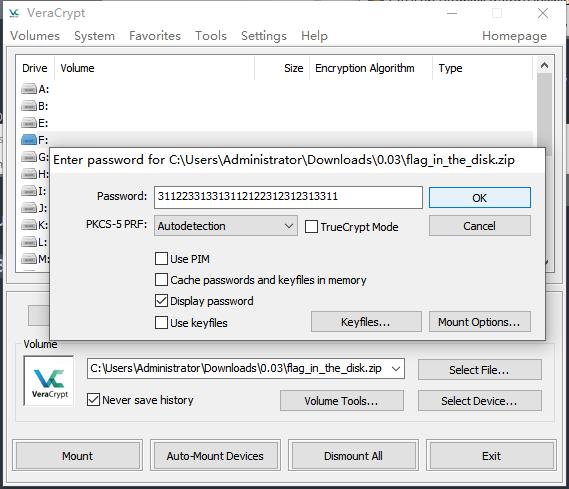
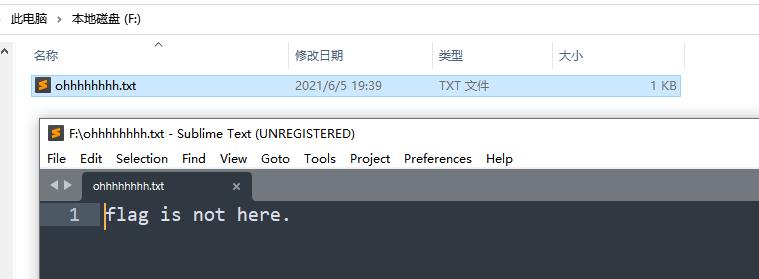
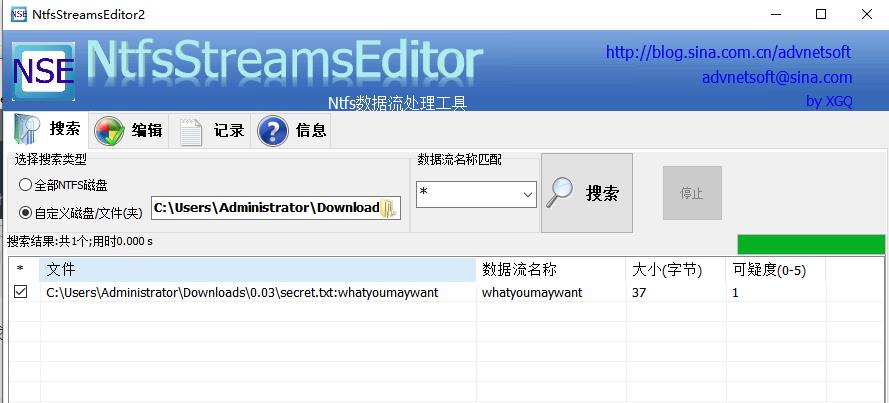
VeraCrypt对于同一个文件可以用不同密码挂载,得到不同内容。需要找到真的密码,secret.txt中的信息都试了不行,当看到0.03.rar是RAR的压缩包时猜测可能存在NTFS文件流隐写。
扫描一下发现确实存在NTFS文件流隐写
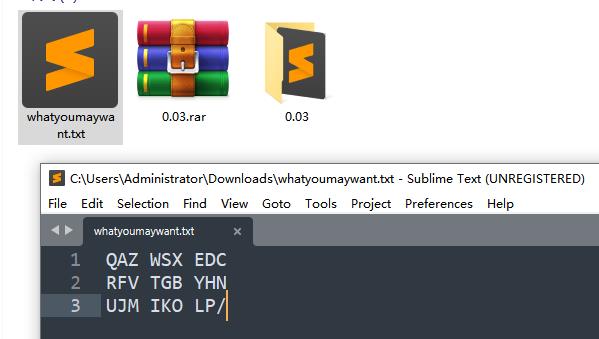
0 1 2 3 (x)
1 QAZ WSX EDC
2 RFV TGB YHN
3 UJM IKO LP/
(y)
看着有点像敲击码,联合secret.txt中的那串数字确实类似敲击码中的坐标,但是如果只有x,y,那只能定位到三个一组的字符串,经过尝试发现这样得到字符串并不是正确的密码。所以怀疑是x,y,z三位一组的坐标,一组坐标定位一个字符串。最后一位数字定位x,y坐标得到的三个字符串中的前后顺序。密码的真实坐标如下:
311 223 313 313 112 122 312 312 313 311
E B C C A F D D C E
得到密码:EBCCAFDDCE
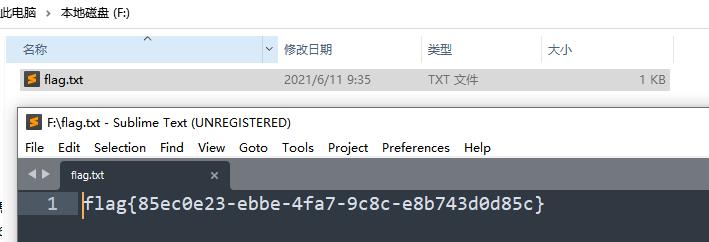
flag{85ec0e23-ebbe-4fa7-9c8c-e8b743d0d85c}
以上是关于GKCTF X DASCTF应急挑战杯Misc-Writeup的主要内容,如果未能解决你的问题,请参考以下文章