keepalived高可用
Posted rmㅤ-rf *
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了keepalived高可用相关的知识,希望对你有一定的参考价值。
文章目录
keepalived
keepalived是什么?
Keepalived 软件起初是专为LVS负载均衡软件设计的,用来管理并监控LVS集群系统中各个服务节点的状态,后来又加入了可以实现高可用的VRRP功能。因此,Keepalived除了能够管理LVS软件外,还可以作为其他服务(例如:nginx、Haproxy、mysql等)的高可用解决方案软件。
Keepalived软件主要是通过VRRP协议实现高可用功能的。VRRP是Virtual Router RedundancyProtocol(虚拟路由器冗余协议)的缩写,VRRP出现的目的就是为了解决静态路由单点故障问题的,它能够保证当个别节点宕机时,整个网络可以不间断地运行。
所以,Keepalived 一方面具有配置管理LVS的功能,同时还具有对LVS下面节点进行健康检查的功能,另一方面也可实现系统网络服务的高可用功能。
keepalived的重要功能
- 管理LVS负载均衡软件
- 实现LVS集群节点的健康检查
- 作为系统网络服务的高可用性(failover)
keepalived高可用故障转移的原理
Keepalived 高可用服务之间的故障切换转移,是通过 VRRP (Virtual Router Redundancy Protocol ,虚拟路由器冗余协议)来实现的。
在 Keepalived 服务正常工作时,主 Master 节点会不断地向备节点发送(多播的方式)心跳消息,用以告诉备 Backup 节点自己还活看,当主 Master 节点发生故障时,就无法发送心跳消息,备节点也就因此无法继续检测到来自主 Master 节点的心跳了,于是调用自身的接管程序,接管主 Master 节点的 IP 资源及服务。而当主 Master 节点恢复时,备 Backup 节点又会释放主节点故障时自身接管的IP资源及服务,恢复到原来的备用角色。
那么,什么是VRRP呢?
VRRP ,全 称 Virtual Router Redundancy Protocol ,中文名为虚拟路由冗余协议 ,VRRP的出现就是为了解决静态踣甶的单点故障问题,VRRP是通过一种竞选机制来将路由的任务交给某台VRRP路由器的。
keepalived原理
keepalived高可用架构图
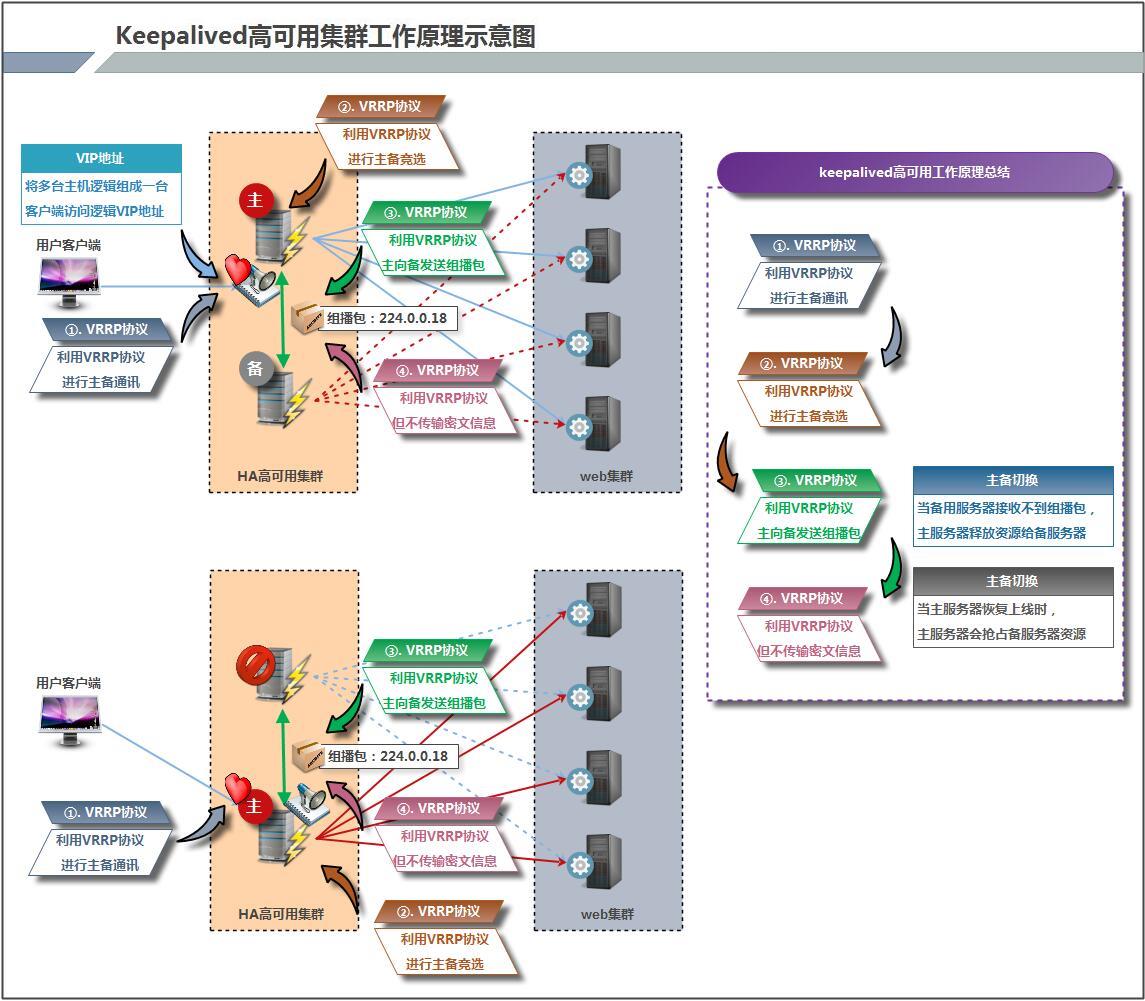
keepalived工作原理描述
keepalived高可用之间是通过VRRP通信的,因此,我们先了解VRRP:
- VRRP,全称Virtual Router Redundant Protocol(虚拟路由冗余协议),VRRP的出现时为了解决静态路由的单点故障。
- VRRP是通过一种竞选协议机制来将路由任务交给某台VRRp路由器的。
- VRRP用IP组播的方式实现高可用之间通信。
- 工作时主节点发包,备节点接包,当备节点接收不到主节点发的数据包的时候,就启动接管程序接管主节点的开源。备节点可有多个,通过优先级竞选,但一般keepalived系统运维工作中都是一对。
- VRRP使用了加密协议加密数据,但keepalived官方目前还是推荐用明文的方式配置认证类型和密码。
keepalived服务的工作原理:
keepalived高可用是通过VRRP进行通信的,VRRP是通过竞选机制来确定主备的,主的优先级高于备,因此,工作时主会优先获得所有的资源,备节点处于等待状态,当主宕了的时候,备节点就会接管主节点的资源,然后顶替主节点对外提供服务。
在keepalived服务之间,只有作为主的服务器会一直发送VRRP组播包,告诉备它还活着,此时备不会抢占主,当主不可用时,即备监听不到主发送的组播包时,就会启动相关服务接管资源,保证业务的连续性,接管速度最快可以小于1秒。
keepalived默认配置文件
keepalived的主配置文件是/etc/keepalived/keepalived.conf
[root@master ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs { //全局配置
notification_email { //定义报警收件人邮件地址
acassen@firewall.loc
failover@firewall.loc
sysadmin@firewall.loc
}
notification_email_from Alexandre.Cassen@firewall.loc //定义报警发件人邮箱
smtp_server 192.168.200.1 //邮箱服务器地址
smtp_connect_timeout 30 //定义邮箱超时时间
router_id LVS_DEVEL //定义路由标识信息,同局域网内唯一
vrrp_skip_check_adv_addr
vrrp_strict
vrrp_garp_interval 0
vrrp_gna_interval 0
}
vrrp_instance VI_1 { //定义实例
state MASTER //指定keepalived节点的初始状态,可选值为MASTER|BACKUP
interface eth0 //VRRP实例绑定的网卡接口,用户发送VRRP包
virtual_router_id 51 //虚拟路由的ID,同一集群要一致
priority 100 //定义优先级,按优先级来决定主备角色,优先级越大越优先
nopreempt //设置不抢占
advert_int 1 //主备通讯时间间隔
authentication { //配置认证
auth_type PASS //认证方式,此处为密码
auth_pass 1111 //同一集群中的keepalived配置里的此处必须一致,推荐使用8位随机数
}
virtual_ipaddress { //配置要使用的VIP地址
192.168.200.16
}
}
virtual_server 192.168.200.16 1358 { //配置虚拟服务器
delay_loop 6 //健康检查的时间间隔
lb_algo rr //lvs调度算法
lb_kind NAT //lvs模式
persistence_timeout 50 //持久化超时时间,单位是秒
protocol TCP //4层协议
sorry_server 192.168.200.200 1358 //定义备用服务器,当所有RS都故障时用sorry_server来响应客户端
real_server 192.168.200.2 1358 { //定义真实处理请求的服务器
weight 1 //给服务器指定权重,默认为1
HTTP_GET {
url {
path /testurl/test.jsp //指定要检查的URL路径
digest 640205b7b0fc66c1ea91c463fac6334d //摘要信息
}
url {
path /testurl2/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334d
}
url {
path /testurl3/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334d
}
connect_timeout 3 //连接超时时间
nb_get_retry 3 //get尝试次数
delay_before_retry 3 //在尝试之前延迟多长时间
}
}
real_server 192.168.200.3 1358 {
weight 1
HTTP_GET {
url {
path /testurl/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334c
}
url {
path /testurl2/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334c
}
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
keepalived实现apache在LVS均衡负载上的高可用实例
| ip类型 | ip地址 |
|---|---|
| VIP | 192.168.74.100 |
| DIP1 | 192.168.74.3 |
| DIP2 | 192.168.74.4 |
| RIP1 | 192.168.74.5 |
| RIP2 | 192.168.74.6 |
配置LVS
关闭防火墙和selinux
[root@R1 ~]# systemctl disable --now firewalld
[root@R1 ~]# setenforce 0
[root@R1 ~]# vim /etc/selinux/config
SELINUX=disabled
SELINUXTYPE=targeted
[root@R2 ~]# systemctl disable --now firewalld
[root@R2 ~]# setenforce 0
[root@R2 ~]# vim /etc/selinux/config
SELINUX=disabled
SELINUXTYPE=targeted
[root@master ~]# systemctl disable --now firewalld
[root@master ~]# setenforce 0
[root@master ~]# vim /etc/selinux/config
SELINUX=disabled
SELINUXTYPE=targeted
[root@slave ~]# systemctl disable --now firewalld
[root@slave ~]# setenforce 0
[root@slave ~]# vim /etc/selinux/config
SELINUX=disabled
SELINUXTYPE=targeted
在调度器上配置VIP和DIP
//配置之前先下载所需要用到的包或者使用本地源
[root@master ~]# dnf -y install ipvsadm
[root@master ~]# dnf -y install keepalived
[root@slave ~]# dnf -y install ipvsadm
[root@slave ~]# dnf -y install keepalived
[root@master ~]# cat /etc/sysconfig/network-scripts/ifcfg-ens33
TYPE=Ethernet
BOOTPROTO=static
NAME=ens33
DEVICE=ens33
ONBOOT=yes
IPADDR=192.168.74.4
PREFIX=24
GATEWAY=192.168.74.2
DNS1=114.114.114.114
[root@slave ~]# cat /etc/sysconfig/network-scripts/ifcfg-ens33
TYPE=Ethernet
BOOTPROTO=static
NAME=ens33
DEVICE=ens33
ONBOOT=yes
IPADDR=192.168.74.3
PREFIX=24
GATEWAY=192.168.74.2
DNS1=114.114.114.114
在RS上先关闭arp包的通告和响应然后配置RIP和VIP
[root@R1 ~]# dnf -y install net-tools
[root@R2 ~]# dnf -y install net-tools
[root@R1 ~]# vim /etc/sysctl.conf
net.ipv4.conf.all.arp_ignore=1
net.ipv4.conf.all.arp_announce=2
[root@R1 ~]# sysctl -p
net.ipv4.conf.all.arp_ignore = 1
net.ipv4.conf.all.arp_announce = 2
[root@R1 ~]# ifconfig lo:0 192.168.74.100/32 broadcast 192.168.74.100 up
[root@R1 ~]# route add -host 192.168.74.100 dev lo:0
[root@R1 ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.74.2 0.0.0.0 UG 100 0 0 ens33
192.168.74.0 0.0.0.0 255.255.255.0 U 100 0 0 ens33
192.168.74.100 0.0.0.0 255.255.255.255 UH 0 0 0 lo
[root@R1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet 192.168.74.100/0 brd 192.168.74.100 scope global lo:0
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:b5:5a:ee brd ff:ff:ff:ff:ff:ff
inet 192.168.74.6/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feb5:5aee/64 scope link
valid_lft forever preferred_lft forever
[root@R2 ~]# vim /etc/sysctl.conf
net.ipv4.conf.all.arp_ignore=1
net.ipv4.conf.all.arp_announce=2
[root@R2 ~]# sysctl -p
net.ipv4.conf.all.arp_ignore = 1
net.ipv4.conf.all.arp_announce = 2
[root@R2 ~]# ifconfig lo:0 192.168.74.100/32 broadcast 192.168.74.100 up
[root@R2 ~]# route add -host 192.168.74.100 dev lo:0
[root@R2 ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.74.2 0.0.0.0 UG 100 0 0 ens33
192.168.74.0 0.0.0.0 255.255.255.0 U 100 0 0 ens33
192.168.74.100 0.0.0.0 255.255.255.255 UH 0 0 0 lo
[root@R2 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet 192.168.74.100/0 brd 192.168.74.100 scope global lo:0
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:32:7e:b4 brd ff:ff:ff:ff:ff:ff
inet 192.168.74.5/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe32:7eb4/64 scope link
valid_lft forever preferred_lft forever
在调度器上添加规则
[root@master ~]# ipvsadm -A -t 192.168.74.100:80 -s rr
[root@master ~]# ipvsadm -a -t 192.168.74.100:80 -r 192.168.74.5:80 -g
[root@master ~]# ipvsadm -a -t 192.168.74.100:80 -r 192.168.74.6:80 -g
[root@master ~]# ipvsadm -Sn > /etc/sysconfig/ipvsadm
[root@master ~]# echo "ipvsadm -Sn > /etc/sysconfig/ipvsadm" >>/etc/rc.d/rc.local
[root@slave ~]# ipvsadm -A -t 192.168.74.100:80 -s rr
[root@slave ~]# ipvsadm -a -t 192.168.74.100:80 -r 192.168.74.5:80 -g
[root@slave ~]# ipvsadm -a -t 192.168.74.100:80 -r 192.168.74.6:80 -g
[root@slave ~]# ipvsadm -Sn > /etc/sysconfig/ipvsadm
[root@slave ~]# echo "ipvsadm -Sn > /etc/sysconfig/ipvsadm" >>/etc/rc.d/rc.local
[root@slave ~]# ipvsadm -C
配置keepalived主配置文件
配置主keepalived
[root@master ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb01
}
vrrp_instance VI_1 {
state MASTER
interface ens33
virtual_router_id 100
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass hahahaha
}
virtual_ipaddress {
192.168.74.100
}
}
virtual_server 192.168.74.100 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.74.5 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.74.6 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@master ~]# systemctl start keepalived
[root@master ~]# systemctl enable keepalived
配置备keepalived
[root@slave ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb02
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 100
priority 90
advert_int 1
authentication {
auth_type PASS
auth_pass hahahaha
}
virtual_ipaddress {
192.168.74.100
}
}
virtual_server 192.168.74.100 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.74.5 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.74.6 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@slave ~]# systemctl start keepalived
[root@slave ~]# systemctl enable keepalived
查看VIP
在MASTER上查看
[root@master ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:00:40:e3 brd ff:ff:ff:ff:ff:ff
inet 192.168.74.3/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet 192.168.74.100/32 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe00:40e3/64 scope link
valid_lft forever preferred_lft forever
在SLAVE上查看
[root@slave ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:9e:17:ec brd ff:ff:ff:ff:ff:ff
inet 192.168.74.4/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe9e:17ec/64 scope link
valid_lft forever preferred_lft forever
让keepalived监控LB
在master上编写脚本
[root@master ~]# mkdir /scripts
[root@master ~]# cat /scripts/notify.sh
#!/bin/bash
case "$1" in
master)
ipvsadm -R < /etc/sysconfig/ipvsadm
;;
backup)
ipvsadm -C
;;
*)
echo "Usage:$0 master|backup"
;;
esac
[root@master ~]# chmod +x /scripts/notify.sh
在SLAVE上编写脚本
[root@slave ~]# mkdir /scripts
[root@slave ~]# cat /scripts/notify.sh
#!/bin/bash
case "$1" in
master)
ipvsadm -R < /etc/sysconfig/ipvsadm
;;
backup)
ipvsadm -C
;;
*)
echo "Usage:$0 master|backup"
;;
esac
[root@slave ~]# chmod +x /scripts/notify.sh
配置keepalived加入故障转移脚本
配置主keepalived
[root@master ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb01
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 100
nopreempt
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass hahahaha
}
virtual_ipaddress {
192.168.74.100
}
notify_master "/scripts/notify.sh master"
notify_backup "/scripts/notify.sh backup"
}
virtual_server 192.168.74.100 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.74.5 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.74.6 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@master ~]# systemctl restart keepalived
[root@master ~]# systemctl enable keepalived
配置备keepalived
[root@slave ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb02
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 100
priority 90
nopreempt
advert_int 1
authentication {
auth_type PASS
auth_pass hahahaha
}
virtual_ipaddress {
192.168.74.100
}
notify_master "/scripts/notify.sh master"
notify_backup "/scripts/notify.sh backup"
}
virtual_server 192.168.74.100 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.74.5 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.74.6 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@slave ~]# systemctl restart keepalived
[root@slave ~]# systemctl enable keepalived
测试验证
因为开启了不抢占,即使master主机宕机恢复了也不会恢复成为主
[root@master ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:00:40:e3 brd ff:ff:ff:ff:ff:ff
inet 192.168.74.4/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet 192.168.74.100/32 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe00:40e3/64 scope link
valid_lft forever preferred_lft forever
[root@master ~]# ipvsadm -Ln
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
-> RemoteAddress:Port Forward Weight ActiveConn InActConn
TCP 192.168.74.100:80 rr
-> 192.168.74.5:80 Route 1 0 0
-> 192.168.74.6:80 Route 1 0 0
[root@slave ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:9e:17:ec brd ff:ff:ff:ff:ff:ff
inet 192.168.74.3/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe9e:17ec/64 scope link
valid_lft forever preferred_lft forever
[root@slave ~]# ipvsadm -Ln
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
-> RemoteAddress:Port Forward Weight ActiveConn InActConn
[root@master ~]# poweroff
[root@master ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:9e:17:ec brd ff:ff:ff:ff:ff:ff
inet 192.168.74.4/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe9e:17ec/64 scope link
valid_lft forever preferred_lft forever
[root@master ~]# ipvsadm -Ln
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
-> RemoteAddress:Port Forward Weight ActiveConn InActConn
[root@slave ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:00:40:e3 brd ff:ff:ff:ff:ff:ff
inet 192.168.74.3/24 brd 192.168.74.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet 192.168.74.100/32 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fe00:40e3/64 scope link
valid_lft forever preferred_lft forever
[root@slave ~]# ipvsadm -Ln
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
-> RemoteAddress:Port Forward Weight ActiveConn InActConn
TCP 192.168.74.100:80 rr
-> 192.168.74.5:80 Route 1 0 0
-> 192.168.74.6:80 Route 1 0 0
以上是关于keepalived高可用的主要内容,如果未能解决你的问题,请参考以下文章